Navigating the Path to CyberPeace: Insights and Strategies
Featured Blogs
.jpeg)
Introduction
Quantum mechanics is not a new field. It finds its roots in the works of physicists such as Niels Bohr in the 1920s, and has informed the development of technologies like nuclear power in the past. But with developments in science and engineering, we are at the cusp of harnessing quantum mechanics for a new wave of real-world uses in sensing and metrology, computing, networking, security, and more. While at different stages of development, quantum technologies have the potential to revolutionise global security, economic systems, and digital infrastructure. The science is dazzling, but it is equally urgent to start preparing for its broader impact on society, especially regarding privacy and digital security. This article explores quantum computing, its threat to information integrity, and global interdependencies as they exist today, and discusses policy areas that should be addressed.
What Is Quantum Computing?
Classical computers use binary bits (0 or 1) to represent and process information. This binary system forms the base of modern computing. But quantum computers use qubits (quantum bits) as a basic unit, which can exist in multiple states ( 0, 1, both, or with other qubits) simultaneously due to quantum principles like superposition and entanglement. This creates an infinite range of possibilities in information processing and allows quantum machines to perform complex computations at speeds impossible for traditional computers. While still in their early stages, large-scale quantum computers could eventually:
- Break modern encryption systems
- Model complex molecules for drug discovery
- Optimise global logistics and financial systems
- Accelerate AI and machine learning
While this could eventually present significant opportunities in fields such as health innovation, material sciences, climate modelling, and cybersecurity, challenges will continue to arise even before the technology is ready for commercial application. Policymakers must start anticipating their impact.
Threats
Policy solutions surrounding quantum technologies will depend on the pace of development of the elements of the quantum ecosystem. However, the most urgent concerns regarding quantum computing applications are the risk to encryption and the impact on market competition.
1. Cybersecurity Threat: Digital infrastructure today (e.g., cloud services, networks, servers, etc.) across sectors such as government, banking and finance, healthcare, energy, etc., depends on encryption for secure data handling and communications. Threat actors can utilise quantum computers to break this encryption. Widely used asymmetric encryption keys, such as RSA or ECC, are particularly susceptible to being broken. Threat actors could "harvest now, decrypt later”- steal encrypted data now and decrypt it later when quantum capabilities mature. Although AES-256, a symmetric encryption standard, is currently considered resistant to quantum decryption, it only protects data after a secure connection is established through a process that today relies on RSA or ECC. This is why governments and companies are racing to adopt Post- Quantum Cryptography (PQC) and quantum key distribution (QKD) to protect security and privacy in digital infrastructure.
2. Market Monopoly: Quantum computing demands significant investments in infrastructure, talent, and research, which only a handful of countries and companies currently possess. As a result, firms that develop early quantum advantage may gain unprecedented competitive leverage through offerings such as quantum-as-a-service, disrupting encryption-dependent industries, or accelerating innovation in pharmaceuticals, finance, and logistics. This could reinforce the existing power asymmetries in the global digital economy. Given these challenges, proactive and forward-looking policy frameworks are critical.
What Should Quantum Computing Policy Cover?
Commercial quantum computing will transform many industries. Policy will have to be flexible and be developed in iterations to account for fast-paced developments in the field. It will also require enduring international collaboration to effectively address a broad range of concerns, including ethics, security, privacy, competition, and workforce implications.
1. Cybersecurity and Encryption: Quantum policy should prioritise the development and standardisation of quantum-resistant encryption methods. This includes ongoing research into Post-Quantum Cryptography (PQC) algorithms and their integration into digital infrastructure. Global policy will need to align national efforts with international standards to create unified quantum-safe encryption protocols.
2. Market Competition and Access: Given the high barriers to entry, regulatory frameworks should promote fair competition, enabling smaller players like startups and developing economies to participate meaningfully in the quantum economy. Frameworks to ensure equitable access, interoperability, and fair competition will become imperative as the quantum ecosystem matures so that society can reap its benefits as a whole.
4. Ethical Considerations: Policymakers will have to consider the impact on privacy and security, and push for the responsible use of quantum capabilities. This includes ensuring that quantum advances do not contribute to cybercrime, disproportionate surveillance, or human rights violations.
5. International Standard-Setting: Setting benchmarks, shared terminologies, and measurement standards will ensure interoperability and security across diverse stakeholders and facilitate global collaboration in quantum research and infrastructure.
6. Military and Defence Implications: Militarisation of quantum technologies is a growing concern, and national security affairs related to quantum espionage are being urgently explored. Nations will have to develop regulations to protect sensitive data and intellectual property from quantum-enabled attacks.
7. Workforce Development and Education: Policies should encourage quantum computing education at various levels to ensure a steady pipeline of talent and foster cross-disciplinary programs that blend quantum computing with fields like machine learning, AI, and engineering.
8. Environmental and Societal Impact: Quantum computing hardware requires specialised conditions such as extreme cooling. Policy will have to address the environmental footprint of the infrastructure and energy consumption of large-scale quantum systems. Broader societal impacts of quantum computing, including potential job displacement, accessibility issues, and the equitable distribution of quantum computing benefits, will have to be explored.
Conclusion
Like nuclear power and AI, the new wave of quantum technologies is expected to be an exciting paradigm shift for society. While they can bring numerous benefits to commercial operations and address societal challenges, they also pose significant risks to global information security. Quantum policy will require regulatory, strategic, and ethical frameworks to govern the rise of these technologies, especially as they intersect with national security, global competition, and privacy. Policymakers must act in collaboration to mitigate unethical use of these technologies and the entrenchment of digital divides across countries. The OECD’s Anticipatory Governance of Emerging Technologies provides a framework of essential values like respect for human rights, privacy, and sustainable development, which can be used to set a baseline, so that quantum computing and related technologies benefit society as a whole.
References
- https://www.weforum.org/stories/2024/07/explainer-what-is-quantum-technology/
- https://www.paconsulting.com/insights/what-is-quantum-technology
- https://delinea.com/blog/quantum-safe-encryption#:~:text=This%20can%20result%20in%20AES,%2D128%20to%20AES%2D256.
- https://www.oecd.org/en/publications/a-quantum-technologies-policy-primer_fd1153c3-en.html

Introduction
As our experiments with Generative Artificial Intelligence (AI) continue, companies and individuals look for new ways to incorporate and capitalise on it. This also includes big tech companies betting on their potential through investments. This process also sheds light on how such innovations are being carried out, used, and affect other stakeholders. Google’s AI overview feature has raised concerns from various website publishers and regulators. Recently, Chegg, a US-based tech education company that provides online resources for high school and college students, has filed a lawsuit against Google alleging abuse of monopoly over the searching mechanism.
Legal Background
Google’s AI Overview/Search Generative Experience (SGE) is a feature that incorporates AI into its standard search tool and helps summarise search results. This is then presented at the top, over the other published websites, when one looks for the search result. Although the sources of the information present are linked, they are half-covered, and it is ambiguous to tell which claims made by the AI come from which link. This creates an additional step for the searcher as, to find out the latter, their user interface requires the searcher to click on a drop-down box. Individual publishers and companies like Chegg have argued that such summaries deter their potential traffic and lead to losses as they continue to bid higher for advertisement services that Google offers, only to have their target audience discouraged from visiting their websites. What is unique about the lawsuit that has been filed by Chegg, is that it is based on anti-trust law rather than copyright law, which it has dealt with previously. In August 2024, a US Federal Judge had ruled that Google had an illegal monopoly over internet search and search text advertising markets, and by November, the US Department of Justice (DOJ) filed its proposed remedy. Some of them were giving advertisers and publishers more control of their data flowing through Google’s products, opening Google’s search index to the rest of the market, and imposing public oversight over Google’s AI investments. Currently, the DOJ has emphasised its stand on dismantling the search monopoly through structural separations, i.e., divesting Google of Chrome. The company is slated to defend itself before the DC District Court Judge Amit Mehta starting April 20, 2025.
CyberPeace Insights
As per a report by Statista (Global market share of leading search engines 2015-2025), Google, as the market leader, held a search traffic share of around 89.62 per cent. It is also stated that its advertising services account for the majority of its revenue, which amounted to a total of 305.63 billion U.S. dollars in 2023. The inclusion of the AI feature is undoubtedly changing how we search for things online. Benefits for users include an immediate, convenient scan of general information pertaining to the looked-up subject, but it may also raise concerns on the part of the website publishers and their loss of ad revenue owing to fewer impressions/clicks. Even though links (sources) are mentioned, they are usually buried. Such a searching mechanism questions the incentive on both ends- the user to explore various viewpoints, as people are now satisfied with the first few results that pop up, and the incentive for a creator/publisher to create new content as well as generate an income out of it. There might be a shift to more passive consumption rather than an active one, where one looks up/or is genuinely searching for information.
Conclusion
AI might make life more convenient, but in this case, it might also take away from small businesses, their finances, and the results of their hard work. It is also necessary for regulators, publishers, and users to continue asking such critical questions to keep the accountability of big tech giants in check, whilst not compromising their creations and publications.
References
- https://www.washingtonpost.com/technology/2024/05/13/google-ai-search-io-sge/
- https://www.theverge.com/news/619051/chegg-google-ai-overviews-monopoly
- https://economictimes.indiatimes.com/tech/technology/google-leans-further-into-ai-generated-overviews-for-its-search-engine/articleshow/118742139.cms?from=mdr
- https://www.nytimes.com/2024/12/03/technology/google-search-antitrust-judge.html
- https://www.odinhalvorson.com/monopoly-and-misuse-googles-strategic-ai-narrative/
- https://cio.economictimes.indiatimes.com/news/artificial-intelligence/google-leans-further-into-ai-generated-overviews-for-its-search-engine/118748621
- https://www.techpolicy.press/the-elephant-in-the-room-in-the-google-search-case-generative-ai/
- https://www.karooya.com/blog/proposed-remedies-break-googles-monopoly-antitrust/
- https://getellipsis.com/blog/googles-monopoly-and-the-hidden-brake-on-ai-innovation/
- https://www.statista.com/statistics/266249/advertising-revenue-of-google/#:~:text=Google:%20annual%20advertising%20revenue%202001,local%20products%20are%20more%20preferred.
- https://www.statista.com/statistics/1381664/worldwide-all-devices-market-share-of-search-engines/
- https://www.techpolicy.press/doj-sets-record-straight-of-whats-needed-to-dismantle-googles-search-monopoly/

Executive Summary:
Apple has quickly responded to two severe zero-day threats, CVE-2024-44308 and CVE-2024-44309 in iOS, macOS, visionOS, and Safari. These defects, actively used in more focused attacks presumably by state actors, allow for code execution and cross-site scripting (XSS). In a report shared by Google’s Threat Analysis Group, the existing gaps prove that modern attacks are highly developed. Apple’s mitigation comprises memory management, especially state management to strengthen device security. Users are encouraged to update their devices as soon as possible, turn on automatic updates and be careful in the internet space to avoid these new threats.
Introduction
Apple has proved its devotion to the security issue releasing the updates fixing two zero-day bugs actively exploited by hackers. The bugs, with the IDs CVE-2024-44308 and CVE-2024-44309, are dangerous and can lead to code execution and cross-site scripting attacks. The vulnerabilities have been employed in attack and the significance of quick patch release for the safety of the users.
Vulnerabilities in Detail
The discovery of vulnerabilities (CVE-2024-44308, CVE-2024-44309) is credited to Clément Lecigne and Benoît Sevens of Google's Threat Analysis Group (TAG). These vulnerabilities were found in JavaScriptCore and WebKit, integral components of Apple’s web rendering framework. The details of these vulnerabilities are mentioned below:
CVE-2024-44308
- Severity: High (CVSS score: 8.8)
- Description: A flaw in the JavaScriptCore component of WebKit. Malicious web content could cause code to be executed on the target system and make the system vulnerable to the full control of the attacker.
- Technical Finding: This vulnerability involves bad handling of memory in the course of executing JavaScript, allowing the use of injected payloads remotely by the attackers.
CVE-2024-44309
- Severity: Moderate (CVSS score: 6.1)
- Description: A cookie management flaw in WebKit which might result in cross site scripting (XSS). This vulnerability enables the attackers to embed unauthorized scripts into genuine websites and endanger the privacy of users as well as their identities.
- Technical Finding: This issue arises because of wrong handling of cookies at the state level while processing the maliciously crafted web content and provides an unauthorized route to session data.
Affected Systems
These vulnerabilities impact a wide range of Apple devices and software versions:
- iOS 18.1.1 and iPadOS 18.1.1: For devices including iPhone XS and later, iPad Pro (13-inch), and iPad mini 5th generation onwards.
- iOS 17.7.2 and iPadOS 17.7.2: Supports earlier models such as iPad Pro (10.5-inch) and iPad Air 3rd generation.
- macOS Sequoia 15.1.1: Specifically targets systems running macOS Sequoia.
- visionOS 2.1.1: Exclusively for Apple Vision Pro.
- Safari 18.1.1: For Macs running macOS Ventura and Sonoma.
Apple's Mitigation Approach
Apple has implemented the following fixes:
- CVE-2024-44308: Enhanced input validation and robust memory checks to prevent arbitrary code execution.
- CVE-2024-44309: Improved state management to eliminate cookie mismanagement vulnerabilities.
These measures ensure stronger protection against exploitation and bolster the underlying security architecture of affected components.
Broader Implications
The exploitation of these zero-days highlights the evolving nature of threat landscapes:
- Increasing Sophistication: Attackers are refining techniques to target niche vulnerabilities, bypassing traditional defenses.
- Spyware Concerns: These flaws align with the modus operandi of spyware tools, potentially impacting privacy and national security.
- Call for Timely Updates: Users delaying updates inadvertently increase their risk exposure
Technical Recommendations for Users
To mitigate potential risks:
- Update Devices Promptly: Install the latest patches for iOS, macOS, visionOS, and Safari.
- Enable Automatic Updates: Ensures timely application of future patches.
- Restrict WebKit Access: Avoid visiting untrusted websites until updates are installed.
- Monitor System Behavior: Look for anomalies that could indicate exploitation.
Conclusion
The exploitation of CVE-2024-44308 and CVE-2024-44309 targeting Apple devices highlight the importance of timely software updates to protect users from potential exploitation. The swift action of Apple by providing immediate improved checks, state management and security patches. Users are therefore encouraged to install updates as soon as possible to guard against these zero day flaws.
References:
- https://support.apple.com/en-us/121752
- https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2024-44308
- https://securityonline.info/cve-2024-44308-and-cve-2024-44309-apple-addresses-zero-day-vulnerabilities/

Introduction
Election misinformation poses a major threat to democratic processes all over the world. The rampant spread of misleading information intentionally (disinformation) and unintentionally (misinformation) during the election cycle can not only create grounds for voter confusion with ramifications on election results but also incite harassment, bullying, and even physical violence. The attack on the United States Capitol Building in Washington D.C., in 2021, is a classic example of this phenomenon, where the spread of dis/misinformation snowballed into riots.
Election Dis/Misinformation
Election dis/misinformation is false or misleading information that affects/influences public understanding of voting, candidates, and election integrity. The internet, particularly social media, is the foremost source of false information during elections. It hosts fabricated news articles, posts or messages containing incorrectly-captioned pictures and videos, fabricated websites, synthetic media and memes, and distorted truths or lies. In a recent example during the 2024 US elections, fake videos using the Federal Bureau of Investigation’s (FBI) insignia alleging voter fraud in collusion with a political party and claiming the threat of terrorist attacks were circulated. According to polling data collected by Brookings, false claims influenced how voters saw candidates and shaped opinions on major issues like the economy, immigration, and crime. It also impacted how they viewed the news media’s coverage of the candidates’ campaign. The shaping of public perceptions can thus, directly influence election outcomes. It can increase polarisation, affect the quality of democratic discourse, and cause disenfranchisement. From a broader perspective, pervasive and persistent misinformation during the electoral process also has the potential to erode public trust in democratic government institutions and destabilise social order in the long run.
Challenges In Combating Dis/Misinformation
- Platform Limitations: Current content moderation practices by social media companies struggle to identify and flag misinformation effectively. To address this, further adjustments are needed, including platform design improvements, algorithm changes, enhanced content moderation, and stronger regulations.
- Speed and Spread: Due to increasingly powerful algorithms, the speed and scale at which misinformation can spread is unprecedented. In contrast, content moderation and fact-checking are reactive and are more time-consuming. Further, incendiary material, which is often the subject of fake news, tends to command higher emotional engagement and thus, spreads faster (virality).
- Geopolitical influences: Foreign actors seeking to benefit from the erosion of public trust in the USA present a challenge to the country's governance, administration and security machinery. In 2018, the federal jury indicted 11 Russian military officials for alleged computer hacking to gain access to files during the 2016 elections. Similarly, Russian involvement in the 2024 federal elections has been alleged by high-ranking officials such as White House national security spokesman John Kirby, and Attorney General Merrick Garland.
- Lack of Targeted Plan to Combat Election Dis/Misinformation: In the USA, dis/misinformation is indirectly addressed through laws on commercial advertising, fraud, defamation, etc. At the state level, some laws such as Bills AB 730, AB 2655, AB 2839, and AB 2355 in California target election dis/misinformation. The federal and state governments criminalize false claims about election procedures, but the Constitution mandates “breathing space” for protection from false statements within election speech. This makes it difficult for the government to regulate election-related falsities.
CyberPeace Recommendations
- Strengthening Election Cybersecurity Infrastructure: To build public trust in the electoral process and its institutions, security measures such as updated data protection protocols, publicized audits of election results, encryption of voter data, etc. can be taken. In 2022, the federal legislative body of the USA passed the Electoral Count Reform and Presidential Transition Improvement Act (ECRA), pushing reforms allowing only a state’s governor or designated executive official to submit official election results, preventing state legislatures from altering elector appointment rules after Election Day and making it more difficult for federal legislators to overturn election results. More investments can be made in training, scenario planning, and fact-checking for more robust mitigation of election-related malpractices online.
- Regulating Transparency on Social Media Platforms: Measures such as transparent labeling of election-related content and clear disclosure of political advertising to increase accountability can make it easier for voters to identify potential misinformation. This type of transparency is a necessary first step in the regulation of content on social media and is useful in providing disclosures, public reporting, and access to data for researchers. Regulatory support is also required in cases where popular platforms actively promote election misinformation.
- Increasing focus on ‘Prebunking’ and Debunking Information: Rather than addressing misinformation after it spreads, ‘prebunking’ should serve as the primary defence to strengthen public resilience ahead of time. On the other hand, misinformation needs to be debunked repeatedly through trusted channels. Psychological inoculation techniques against dis/misinformation can be scaled to reach millions on social media through short videos or messages.
- Focused Interventions On Contentious Themes By Social Media Platforms: As platforms prioritize user growth, the burden of verifying the accuracy of posts largely rests with users. To shoulder the responsibility of tackling false information, social media platforms can outline critical themes with large-scale impact such as anti-vax content, and either censor, ban, or tweak the recommendations algorithm to reduce exposure and weaken online echo chambers.
- Addressing Dis/Information through a Socio-Psychological Lens: Dis/misinformation and its impact on domains like health, education, economy, politics, etc. need to be understood through a psychological and sociological lens, apart from the technological one. A holistic understanding of the propagation of false information should inform digital literacy training in schools and public awareness campaigns to empower citizens to evaluate online information critically.
Conclusion
According to the World Economic Forum’s Global Risks Report 2024, the link between misleading or false information and societal unrest will be a focal point during elections in several major economies over the next two years. Democracies must employ a mixed approach of immediate tactical solutions, such as large-scale fact-checking and content labelling, and long-term evidence-backed countermeasures, such as digital literacy, to curb the spread and impact of dis/misinformation.
Sources
- https://www.cbsnews.com/news/2024-election-misinformation-fbi-fake-videos/
- https://www.brookings.edu/articles/how-disinformation-defined-the-2024-election-narrative/
- https://www.fbi.gov/wanted/cyber/russian-interference-in-2016-u-s-elections
- https://indianexpress.com/article/world/misinformation-spreads-fear-distrust-ahead-us-election-9652111/
- https://academic.oup.com/ajcl/article/70/Supplement_1/i278/6597032#377629256
- https://www.brennancenter.org/our-work/policy-solutions/how-states-can-prevent-election-subversion-2024-and-beyond
- https://www.bbc.com/news/articles/cx2dpj485nno
- https://msutoday.msu.edu/news/2022/how-misinformation-and-disinformation-influence-elections
- https://misinforeview.hks.harvard.edu/article/a-survey-of-expert-views-on-misinformation-definitions-determinants-solutions-and-future-of-the-field/
- https://reutersinstitute.politics.ox.ac.uk/sites/default/files/2023-06/Digital_News_Report_2023.pdf
- https://www.weforum.org/stories/2024/03/disinformation-trust-ecosystem-experts-curb-it/
- https://www.apa.org/topics/journalism-facts/misinformation-recommendations
- https://mythvsreality.eci.gov.in/
- https://www.brookings.edu/articles/transparency-is-essential-for-effective-social-media-regulation/
- https://www.brookings.edu/articles/how-should-social-media-platforms-combat-misinformation-and-hate-speech/

Executive Summary:
A viral post on X (formerly twitter) shared with misleading captions about Gautam Adani being arrested in public for fraud, bribery and corruption. The charges accuse him, his nephew Sagar Adani and 6 others of his group allegedly defrauding American investors and orchestrating a bribery scheme to secure a multi-billion-dollar solar energy project awarded by the Indian government. Always verify claims before sharing posts/photos as this came out to be AI-generated.

Claim:
An image circulating of public arrest after a US court accused Gautam Adani and executives of bribery.
Fact Check:
There are multiple anomalies as we can see in the picture attached below, (highlighted in red circle) the police officer grabbing Adani’s arm has six fingers. Adani’s other hand is completely absent. The left eye of an officer (marked in blue) is inconsistent with the right. The faces of officers (marked in yellow and green circles) appear distorted, and another officer (shown in pink circle) appears to have a fully covered face. With all this evidence the picture is too distorted for an image to be clicked by a camera.


A thorough examination utilizing AI detection software concluded that the image was synthetically produced.
Conclusion:
A viral image circulating of the public arrest of Gautam Adani after a US court accused of bribery. After analysing the image, it is proved to be an AI-Generated image and there is no authentic information in any news articles. Such misinformation spreads fast and can confuse and harm public perception. Always verify the image by checking for visual inconsistency and using trusted sources to confirm authenticity.
- Claim: Gautam Adani arrested in public by law enforcement agencies
- Claimed On: Instagram and X (Formerly Known As Twitter)
- Fact Check: False and Misleading

Introduction:
The National Security Council Secretariat, in strategic partnership with the Rashtriya Raksha University, Gujarat, conducted a 12-day Bharat National Cyber Security Exercise in 2024 (from 18th November to 29th November). This exercise included landmark events such as a CISO (Chief Information Security Officers) Conclave and a Cyber Security Start-up exhibition, which were inaugurated on 27 November 2024. Other key features of the exercise include cyber defense training, live-fire simulations, and strategic decision-making simulations. The aim of the exercise was to equip senior government officials and personnel in critical sector organisations with skills to deal with cybersecurity issues. The event also consisted of speeches, panel discussions, and initiatives such as the release of the National Cyber Reference Framework (NCRF)- which provides a structured approach to cyber governance, and the launch of the National Cyber Range(NCR) 1.0., a cutting-edge facility for cyber security research training.
The Deputy National Security Advisor, Shri T.V. Ravichandran (IPS) reiterated, through his speech, the importance of the inclusion of technology in challenges with respect to cyber security and shaping India’s cyber strategy in a manner that is proactive. The CISOs of both government and private entities were encouraged to take up multidimensional efforts which included technological upkeep but also soft skills for awareness.
CyberPeace Outlook
The Bharat National Cybersecurity Exercise (Bharat NCX) 2024 underscores India’s commitment to a comprehensive and inclusive approach to strengthening its cybersecurity ecosystem. By fostering collaboration between startups, government bodies, and private organizations, the initiative facilitates dialogue among CISOs and promotes a unified strategy toward cyber resilience. Platforms like Bharat NCX encourage exploration in the Indian entrepreneurial space, enabling startups to innovate and contribute to critical domains like cybersecurity. Developments such as IIT Indore’s intelligent receivers (useful for both telecommunications and military operations) and the Bangalore Metro Rail Corporation Limited’s plans to establish a dedicated Security Operations Centre (SOC) to counter cyber threats are prime examples of technological strides fostering national cyber resilience.
Cybersecurity cannot be understood in isolation: it is an integral aspect of national security, impacting the broader digital infrastructure supporting Digital India initiatives. The exercise emphasises skills training, creating a workforce adept in cyber hygiene, incident response, and resilience-building techniques. Such efforts bolster proficiency across sectors, aligning with the government’s Atmanirbhar Bharat vision. By integrating cybersecurity into workplace technologies and fostering a culture of awareness, Bharat NCX 2024 is a platform that encourages innovation and is a testament to the government’s resolve to fortify India’s digital landscape against evolving threats.
References
- https://ciso.economictimes.indiatimes.com/news/cybercrime-fraud/bharat-cisos-conclave-cybersecurity-startup-exhibition-inaugurated-under-bharat-ncx-2024/115755679
- https://pib.gov.in/PressReleasePage.aspx?PRID=2078093
- https://timesofindia.indiatimes.com/city/indore/iit-indore-unveils-groundbreaking-intelligent-receivers-for-enhanced-6g-and-military-communication-security/articleshow/115265902.cms
- https://www.thehindu.com/news/cities/bangalore/defence-system-to-be-set-up-to-protect-metro-rail-from-cyber-threats/article68841318.ece
- https://rru.ac.in/wp-content/uploads/2021/04/Brochure12-min.pdf

Introduction
The Australian Parliament has passed the world’s first legislation regarding a ban on social media for children under 16. This was done citing risks to the mental and physical well-being of children and the need to contain misogynistic influence on them. The debate surrounding the legislation is raging strong, as it is the first proposal of its kind and would set precedence for how other countries can assess their laws regarding children and social media platforms and their priorities.
The Legislation
Currently trailing an age-verification system (such as biometrics or government identification), the legislation mandates a complete ban on underage children using social media, setting the age limit to 16 or above. Further, the law does not provide exemptions of any kind, be it for pre-existing accounts or parental consent. With federal elections approaching, the law seeks to address parental concerns regarding measures to protect their children from threats lurking on social media platforms. Every step in this regard is being observed with keen interest.
The Australian Prime Minister, Anthony Albanese, emphasised that the onus of taking responsible steps toward preventing access falls on the social media platforms, absolving parents and their children of the same. Social media platforms like TikTok, X, and Meta Platforms’ Facebook and Instagram all come under the purview of this legislation.
CyberPeace Overview
The issue of a complete age-based ban raises a few concerns:
- It is challenging to enforce digitally as children might find a way to circumnavigate such restrictions. An example would be the Cinderella Law, formally known as the Shutdown Law, which the Government of South Korea had implemented back in 2011 to reduce online gaming and promote healthy sleeping habits among children. The law mandated the prohibition of access to online gaming for children under the age of 16 between 12 A.M. to 6 A.M. However, a few drawbacks rendered it less effective over time. Children were able to use the login IDs of adults, switch to VPN, and even switch to offline gaming. In addition, parents also felt the government was infringing on the right to privacy and the restrictions were only for online PC games and did not extend to mobile phones. Consequently, the law lost relevance and was repealed in 2021.
- The concept of age verification inherently requires collecting more personal data and inadvertently opens up concerns regarding individual privacy.
- A ban is likely to reduce the pressure on tech and social media companies to develop and work on areas that would make their services a safe child-friendly environment.
Conclusion
Social media platforms can opt for an approach that focuses on how to create a safe environment online for children as they continue to deliberate on restrictions. An example of an impactful-yet-balanced step towards the protection of children on social media while respecting privacy is the U.K.'s Age-Appropriate Design Code (UK AADC). It is the U.K.’s implementation of the European Union’s General Data Protection Regulation (GDPR), prepared by the ICO (Information Commissioner's Office), the U.K. data protection regulator. It follows a safety-by-design approach for children. As we move towards a future that is predominantly online, we must continue to strive and create a safe space for children and address issues in innovative ways.
References
- https://indianexpress.com/article/technology/social/australia-proposes-ban-on-social-media-for-children-under-16-9657544/
- https://www.thehindu.com/opinion/op-ed/should-children-be-barred-from-social-media/article68661342.ece
- https://forumias.com/blog/debates-on-whether-children-should-be-banned-from-social-media/
- https://timesofindia.indiatimes.com/education/news/why-banning-kids-from-social-media-wont-solve-the-youth-mental-health-crisis/articleshow/113328111.cms
- https://iapp.org/news/a/childrens-privacy-laws-and-freedom-of-expression-lessons-from-the-uk-age-appropriate-design-code
- https://www.techinasia.com/s-koreas-cinderella-law-finally-growing-up-teens-may-soon-be-able-to-play-online-after-midnight-again
- https://wp.towson.edu/iajournal/2021/12/13/video-gaming-addiction-a-case-study-of-china-and-south-korea/
- https://www.dailysabah.com/world/asia-pacific/australia-passes-worlds-1st-total-social-media-ban-for-children

Executive Summary:
A viral online video claims visuals of a massive rally organised in Manipur for stopping the violence in Manipur. However, the CyberPeace Research Team has confirmed that the video is a deep fake, created using AI technology to manipulate the crowd into existence. There is no original footage in connection to any similar protest. The claim that promotes the same is therefore, false and misleading.
Claims:
A viral post falsely claims of a massive rally held in Manipur.


Fact Check:
Upon receiving the viral posts, we conducted a Google Lens search on the keyframes of the video. We could not locate any authentic sources mentioning such event held recently or previously. The viral video exhibited signs of digital manipulation, prompting a deeper investigation.
We used AI detection tools, such as TrueMedia and Hive AI Detection tool, to analyze the video. The analysis confirmed with 99.7% confidence that the video was a deepfake. The tools identified "substantial evidence of manipulation," particularly in the crowd and colour gradience , which were found to be artificially generated.



Additionally, an extensive review of official statements and interviews with Manipur State officials revealed no mention of any such rally. No credible reports were found linking to such protests, further confirming the video’s inauthenticity.
Conclusion:
The viral video claims visuals of a massive rally held in Manipur. The research using various tools such as truemedia.org and other AI detection tools confirms that the video is manipulated using AI technology. Additionally, there is no information in any official sources. Thus, the CyberPeace Research Team confirms that the video was manipulated using AI technology, making the claim false and misleading.
- Claim: Massive rally held in Manipur against the ongoing violence viral on social media.
- Claimed on: Instagram and X(Formerly Twitter)
- Fact Check: False & Misleading

Introduction
Digital Public Infrastructure (DPI) serves as the backbone of e-governance, enabling governments to deliver services more efficiently, transparently, and inclusively. By leveraging information and communication technology (ICT), digital governance systems reconfigure traditional administrative processes, making them more accessible and citizen-centric. However, the successful implementation of such systems hinges on overcoming several challenges, from ensuring data security to fostering digital literacy and addressing infrastructural gaps.
This article delves into the key enablers that drive effective DPI and outlines the measures already undertaken by the government to enhance its functionality. Furthermore, it outlines strategies for their enhancement, emphasizing the need for a collaborative, secure, and adaptive approach to building robust e-governance systems.
Key Enablers of DPI
Digital Public Infrastructure (DPI), the foundation for e-governance, relies on common design, robust governance, and private sector participation for efficiency and inclusivity. This requires common principles, frameworks for collaboration, capacity building, and the development of common standards. Some of the key measures undertaken by the government in this regard include:
- Data Protection Framework: The Digital Personal Data Protection (DPDP) Act of 2023 establishes a framework to ensure consent-based data sharing and regulate the processing of digital personal data. It delineates the responsibilities of data fiduciaries in safeguarding users' digital personal data.
- Increasing Public-Private Partnerships: Refining collaboration between the government and the private sector has accelerated the development, maintenance, expansion, and trust of the infrastructure of DPIs, such as the AADHAR, UPI, and Data Empowerment and Protection Architecture (DEPA). For example, the Asian Development Bank attributes the success of UPI to its “consortium ownership structure”, which enables the wide participation of major financial stakeholders in the country.
- Coordinated Planning: The PM-Gati Shakti establishes a clear coordination framework involving various inter-governmental stakeholders at the state and union levels. This aims to significantly reduce project duplications, delays, and cost escalations by streamlining communication, harmonizing project appraisal and approval processes, and providing a comprehensive database of major infrastructure projects in the country. This database called the National Master Plan, is jointly accessible by various government stakeholders through APIs.
- Capacity Building for Government Employees: The National e-Governance Division of the Ministry of Electronics and Information Technology routinely rolls out multiple training programs to build the technological and managerial skills required by government employees to manage Digital Public Goods (DPGs). For instance, it recently held a program on “Managing Large Digital Transformative Projects”. Additionally, the Ministry of Personnel, Public Grievances, and Pensions has launched the Integrated Government Online Training platform (iGOT) Karmayogi for the continuous learning of civil servants across various domains.
Digital Governance; Way Forward
E-governance utilizes information and communication technology (ICT) such as Wide Area Networks, the Internet, and mobile computing to implement existing government activities, reconfiguring the structures and processes of governance systems. This warrants addressing certain inter-related challenges such as :
- Data Security: The dynamic and ever-changing landscape of cyber threats necessitates regular advancements in data and information security technologies, policy frameworks, and legal provisions. Consequently, the digital public ecosystem must incorporate robust data cybersecurity measures, advanced encryption technologies, and stringent privacy compliance standards to safeguard against data breaches.
- Creating Feedback Loops: Regular feedback surveys will help government agencies improve the quality, efficiency, and accessibility of digital governance services by tailoring them to be more user-friendly and enhancing administrative design. This is necessary to build trust in government services and improve their uptake among beneficiaries. Conducting the decennial census is essential to gather updated data that can serve as a foundation for more informed and effective decision-making.
- Capacity Building for End-Users: The beneficiaries of key e-governance projects like Aadhar and UPI may have inadequate technological skills, especially in regions with weak internet network infrastructure like hilly or rural areas. This can present challenges in the access to and usage of technological solutions. Robust capacity-building campaigns for beneficiaries can provide an impetus to the digital inclusion efforts of the government.
- Increasing the Availability of Real-Time Data: By prioritizing the availability of up-to-date information, governments and third-party enterprises can enable quick and informed decision-making. They can effectively track service usage, assess quality, and monitor key metrics by leveraging real-time data. This approach is essential for enhancing operational efficiency and delivering improved user experience.
- Resistance to Change: Any resistance among beneficiaries or government employees to adopt digital governance goods may stem from a limited understanding of digital processes and a lack of experience with transitioning from legacy systems. Hand-holding employees during the transitionary phase can help create more trust in the process and strengthen the new systems.
Conclusion
Digital governance is crucial to transforming public services, ensuring transparency, and fostering inclusivity in a rapidly digitizing world. The successful implementation of such projects requires addressing challenges like data security, skill gaps, infrastructural limitations, feedback mechanisms, and resistance to change. Addressing these challenges with a strategic, multi-stakeholder approach can ensure the successful execution and long-term impact of large digital governance projects. By adopting robust cybersecurity frameworks, fostering public-private partnerships, and emphasizing capacity building, governments can create efficient and resilient systems that are user-centric, secure, and accessible to all.
References
- https://www.adb.org/sites/default/files/publication/865106/adbi-wp1363.pdf
- https://www.jotform.com/blog/government-digital-transformation-challenges/
- https://aapti.in/wp-content/uploads/2024/06/AaptixONI-DPIGovernancePlaybook_compressed.pdf
- https://community.nasscom.in/sites/default/files/publicreport/Digital%20Public%20Infrastructure%2022-2-2024_compressed.pdf
- https://proteantech.in/articles/Decoding-Digital-Public-Infrastructure-in-India/

Introduction
According to the Finance Ministry's data, the incidence of domestic Unified Payment Interface (UPI) fraud rose by 85% in FY 2023-24 compared to FY 2022-23. Further, as of September of FY 2024-25, 6.32 lakh fraud cases had been already reported, amounting to Rs 485 crore. The data was shared on 25th November 2024, by the Finance Ministry in response to a question in Lok Sabha’s winter session about the fraud in UPI transactions during the past three fiscal years.
Statistics

UPI Frauds and Government's Countermeasures
On the query as to measures taken by the government for safe and secure UPI transactions and prevention of fraud in the transactions, the ministry has highlighted the measures as follows:
- The Reserve Bank of India (RBI) has launched the Central Payment Fraud Information Registry (CPFIR), a web-based tool for reporting payment-related frauds, operational since March 2020, and it requires requiring all Regulated Entities (RE) to report payment-related frauds to the said CPFIR.
- The Government, RBI, and National Payments Corporation of India (NPCI) have implemented various measures to prevent payment-related frauds, including UPI transaction frauds. These include device binding, two-factor authentication through PIN, daily transaction limits, and limits on use cases.
- Further, NPCI offers a fraud monitoring solution for banks, enabling them to alert and decline transactions using AI/ML models. RBI and banks are also promoting awareness through SMS, radio, and publicity on 'cyber-crime prevention'.
- The Ministry of Home Affairs has launched a National Cybercrime Reporting Portal (NCRP) (www.cybercrime.gov.in) and a National Cybercrime Helpline Number 1930 to help citizens report cyber incidents, including financial fraud. Customers can also report fraud on the official websites of their bank or bank branches.
- The Department of Telecommunications has introduced the Digital Intelligence Platform (DIP) and 'Chakshu' facility on the Sanchar Saathi portal, enabling citizens to report suspected fraud messages via call, SMS, or WhatsApp.
Conclusion
UPI is India's most popular digital payment method. As of June 2024, there are around 350 million active users of the UPI in India. The Indian Cyber Crime Coordination Centre (I4C) report indicates that ‘Online Financial Fraud’, a cyber crime category under NCRP, is the most prevalent among others. The rise of financial fraud, particularly UPI fraud is cause for alarm, the scammers use sophisticated strategies to deceive victims. It is high time for netizens to exercise caution and care with their personal and financial information, stay aware of common tactics used by fraudsters, and adhere to best security practices for secure transactions and the safe use of UPI services.
References

Introduction
26th November 2024 marked a historical milestone for India as a Hyderabad-based space technology firm TakeMe2Space, announced the forthcoming launch of MOI-TD “(My Orbital Infrastructure - Technology Demonstrator)”, India's first AI lab in space. The mission will demonstrate real-time data processing in orbit, making space research more affordable and accessible according to the Company. The launch is scheduled for mid-December 2024 aboard the ISRO's PSLV C60 launch vehicle. It represents a transformative phase for innovation and exploration in India's AI and space technology integration space.
The Vision Behind the Initiative
The AI Laboratory in orbit is designed to enable autonomous decision-making, revolutionising satellite exploration and advancing cutting-edge space research. It signifies a major step toward establishing space-based data centres, paving the way for computing capabilities that will support a variety of applications.
While space-based data centres currently cost 10–15 times more than terrestrial alternatives, this initiative leverages high-intensity solar power in orbit to significantly reduce energy consumption. Training AI models in space could lower energy costs by up to 95% and cut carbon emissions by at least tenfold, even when factoring in launch emissions. It positions MOI-TD as an eco-friendly and cost-efficient solution.
Technological Innovations and Future Impact of AI in Space
This AI Laboratory, MOI-TD includes control software and hardware components, including reaction wheels, magnetometers, an advanced onboard computer, and an AI accelerator. The satellite also features flexible solar cells that could power future satellites. It will enable the processing of real-time space data, pattern recognition, and autonomous decision-making and address the latency issues, ensuring faster and more efficient data analysis, while the robust hardware designs tackle the challenges posed by radiation and extreme space environments. Advanced sensor integration will further enhance data collection, facilitating AI model training and validation.
These innovations drive key applications with transformative potential. It will allow users to access the satellite platform through OrbitLaw, a web-based console that will allow users to upload AI models to aid climate monitoring, disaster prediction, urban growth analysis and custom Earth observation use cases. TakeMe2Space has already partnered with a leading Malaysian university and an Indian school (grades 9 and 10) to showcase the satellite’s potential for democratizing space research.
Future Prospects and India’s Global Leadership in AI and Space Research
As per Stanford’s HAI Global AI Vibrancy rankings, India secured 4th place due to its R&D leadership, vibrant AI ecosystem, and public engagement for AI. This AI laboratory is a step further in advancing India’s role in the development of regulatory frameworks for ethical AI use, fostering robust public-private partnerships, and promoting international cooperation to establish global standards for AI applications.
Cost-effectiveness and technological exercise are some of India’s unique strengths and could position the country as a key player in the global AI and space research arena and draw favourable comparisons with initiatives by NASA, ESA, and private entities like SpaceX. By prioritising ethical and sustainable practices and fostering collaboration, India can lead in shaping the future of AI-driven space exploration.
Conclusion
India’s first AI laboratory in space, MOI-TD, represents a transformative milestone in integrating AI with space technology. This ambitious project promises to advance autonomous decision-making, enhance satellite exploration, and democratise space research. Additionally, factors such as data security, fostering international collaboration and ensuring sustainability should be taken into account while fostering such innovations. With this, India can establish itself as a leader in space research and AI innovation, setting new global standards while inspiring a future where technology expands humanity’s frontiers and enriches life on Earth.
References
- https://www.ptinews.com/story/national/start-up-to-launch-ai-lab-in-space-in-december/2017534
- https://economictimes.indiatimes.com/tech/startups/spacetech-startup-takeme2space-to-launch-ai-lab-in-space-in-december/articleshow/115701888.cms?from=mdr
- https://www.ibm.com/think/news/data-centers-space
- https://cio.economictimes.indiatimes.com/amp/news/next-gen-technologies/spacetech-startup-takeme2space-to-launch-ai-lab-in-space-in-december/115718230

Introduction
Misinformation spreads differently with respect to different host environments, making localised cultural narratives and practices major factors in how an individual deals with it when presented in a certain place and to a certain group. In the digital age, with time-sensitive data, an overload of information creates a lot of noise which makes it harder to make informed decisions. There are also cases where customary beliefs, biases, and cultural narratives are presented in ways that are untrue. These instances often include misinformation related to health and superstitions, historical distortions, and natural disasters and myths. Such narratives, when shared on social media, can lead to widespread misconceptions and even harmful behaviours. For example, it may also include misinformation that goes against scientific consensus or misinformation that contradicts simple, objectively true facts. In such ambiguous situations, there is a higher probability of people falling back on patterns in determining what information is right or wrong. Here, cultural narratives and cognitive biases come into play.
Misinformation and Cultural Narratives
Cultural narratives include deep-seated cultural beliefs, folklore, and national myths. These narratives can also be used to manipulate public opinion as political and social groups often leverage them to proceed with their agenda. Lack of digital literacy and increasing information online along with social media platforms and their focus on generating algorithms for engagement aids this process. The consequences can even prove to be fatal.
During COVID-19, false claims targeted certain groups as being virus spreaders fueled stigmatisation and eroded trust. Similarly, vaccine misinformation, rooted in cultural fears, spurred hesitancy and outbreaks. Beyond health, manipulated narratives about parts of history are spread depending on the sentiments of the people. These instances exploit emotional and cultural sensitivities, emphasizing the urgent need for media literacy and awareness to counter their harmful effects.
CyberPeace Recommendations
As cultural narratives may lead to knowingly or unknowingly spreading misinformation on social media platforms, netizens must consider preventive measures that can help them build resilience against any biased misinformation they may encounter. The social media platforms must also develop strategies to counter such types of misinformation.
- Digital and Information Literacy: Netizens must encourage developing digital and information literacy in a time of information overload on social media platforms.
- The Role Of Media: The media outlets can play an active role, by strictly providing fact-based information and not feeding into narratives to garner eyeballs. Social media platforms also need to be careful while creating algorithms focused on consistent engagement.
- Community Fact-Checking: As localised information prevails in such cases, owing to the time-sensitive nature, immediate debunking of precarious information by authorities at the ground level is encouraged.
- Scientifically Correct Information: Starting early and addressing myths and biases through factual and scientifically correct information is also encouraged.
Conclusion
Cultural narratives are an ingrained part of society, and they might affect how misinformation spreads and what we end up believing. Acknowledging this process and taking counter measures will allow us to move further and take steps for intervention regarding tackling the spread of misinformation specifically aided by cultural narratives. Efforts to raise awareness and educate the public to seek sound information, practice verification checks, and visit official channels are of the utmost importance.
References
- https://www.icf.com/insights/cybersecurity/developing-effective-responses-to-fake-new
- https://www.dw.com/en/india-fake-news-problem-fueled-by-digital-illiteracy/a-56746776
- https://www.apa.org/topics/journalism-facts/how-why-misinformation-spreads

Executive Summary:
BrazenBamboo’s DEEPDATA malware represents a new wave of advanced cyber espionage tools, exploiting a zero-day vulnerability in Fortinet FortiClient to extract VPN credentials and sensitive data through fileless malware techniques and secure C2 communications. With its modular design, DEEPDATA targets browsers, messaging apps, and password stores, while leveraging reflective DLL injection and encrypted DNS to evade detection. Cross-platform compatibility with tools like DEEPPOST and LightSpy highlights a coordinated development effort, enhancing its espionage capabilities. To mitigate such threats, organizations must enforce network segmentation, deploy advanced monitoring tools, patch vulnerabilities promptly, and implement robust endpoint protection. Vendors are urged to adopt security-by-design practices and incentivize vulnerability reporting, as vigilance and proactive planning are critical to combating this sophisticated threat landscape.
Introduction
The increased use of zero-day vulnerabilities by more complex threat actors reinforces the importance of more developed countermeasures. One of the threat actors identified is BrazenBamboo uses a zero-day vulnerability in Fortinet FortiClient for Windows through the DEEPDATA advanced malware framework. This research explores technical details about DEEPDATA, the tricks used in its operations, and its other effects.
Technical Findings
1. Vulnerability Exploitation Mechanism
The vulnerability in Fortinet’s FortiClient lies in its failure to securely handle sensitive information in memory. DEEPDATA capitalises on this flaw via a specialised plugin, which:
- Accesses the VPN client’s process memory.
- Extracts unencrypted VPN credentials from memory, bypassing typical security protections.
- Transfers credentials to a remote C2 server via encrypted communication channels.
2. Modular Architecture
DEEPDATA exhibits a highly modular design, with its core components comprising:
- Loader Module (data.dll): Decrypts and executes other payloads.
- Orchestrator Module (frame.dll): Manages the execution of multiple plugins.
- FortiClient Plugin: Specifically designed to target Fortinet’s VPN client.
Each plugin operates independently, allowing flexibility in attack strategies depending on the target system.
3. Command-and-Control (C2) Communication
DEEPDATA establishes secure channels to its C2 infrastructure using WebSocket and HTTPS protocols, enabling stealthy exfiltration of harvested data. Technical analysis of network traffic revealed:
- Dynamic IP switching for C2 servers to evade detection.
- Use of Domain Fronting, hiding C2 communication within legitimate HTTPS traffic.
- Time-based communication intervals to minimise anomalies in network behavior.
4. Advanced Credential Harvesting Techniques
Beyond VPN credentials, DEEPDATA is capable of:
- Dumping password stores from popular browsers, such as Chrome, Firefox, and Edge.
- Extracting application-level credentials from messaging apps like WhatsApp, Telegram, and Skype.
- Intercepting credentials stored in local databases used by apps like KeePass and Microsoft Outlook.
5. Persistence Mechanisms
To maintain long-term access, DEEPDATA employs sophisticated persistence techniques:
- Registry-based persistence: Modifies Windows registry keys to reload itself upon system reboot.
- DLL Hijacking: Substitutes legitimate DLLs with malicious ones to execute during normal application operations.
- Scheduled Tasks and Services: Configures scheduled tasks to periodically execute the malware, ensuring continuous operation even if detected and partially removed.
Additional Tools in BrazenBamboo’s Arsenal
1. DEEPPOST
A complementary tool used for data exfiltration, DEEPPOST facilitates the transfer of sensitive files, including system logs, captured credentials, and recorded user activities, to remote endpoints.
2. LightSpy Variants
- The Windows variant includes a lightweight installer that downloads orchestrators and plugins, expanding espionage capabilities across platforms.
- Shellcode-based execution ensures that LightSpy’s payload operates entirely in memory, minimising artifacts on the disk.
3. Cross-Platform Overlaps
BrazenBamboo’s shared codebase across DEEPDATA, DEEPPOST, and LightSpy points to a centralised development effort, possibly linked to a Digital Quartermaster framework. This shared ecosystem enhances their ability to operate efficiently across macOS, iOS, and Windows systems.
Notable Attack Techniques
1. Memory Injection and Data Extraction
Using Reflective DLL Injection, DEEPDATA injects itself into legitimate processes, avoiding detection by traditional antivirus solutions.
- Memory Scraping: Captures credentials and sensitive information in real-time.
- Volatile Data Extraction: Extracts transient data that only exists in memory during specific application states.
2. Fileless Malware Techniques
DEEPDATA leverages fileless infection methods, where its payload operates exclusively in memory, leaving minimal traces on the system. This complicates post-incident forensic investigations.
3. Network Layer Evasion
By utilising encrypted DNS queries and certificate pinning, DEEPDATA ensures that network-level defenses like intrusion detection systems (IDS) and firewalls are ineffective in blocking its communications.
Recommendations
1. For Organisations
- Apply Network Segmentation: Isolate VPN servers from critical assets.
- Enhance Monitoring Tools: Deploy behavioral analysis tools that detect anomalous processes and memory scraping activities.
- Regularly Update and Patch Software: Although Fortinet has yet to patch this vulnerability, organisations must remain vigilant and apply fixes as soon as they are released.
2. For Security Teams
- Harden Endpoint Protections: Implement tools like Memory Integrity Protection to prevent unauthorised memory access.
- Use Network Sandboxing: Monitor and analyse outgoing network traffic for unusual behaviors.
- Threat Hunting: Proactively search for indicators of compromise (IOCs) such as unauthorised DLLs (data.dll, frame.dll) or C2 communications over non-standard intervals.
3. For Vendors
- Implement Security by Design: Adopt advanced memory protection mechanisms to prevent credential leakage.
- Bug Bounty Programs: Encourage researchers to report vulnerabilities, accelerating patch development.
Conclusion
DEEPDATA is a form of cyber espionage and represents the next generation of tools that are more advanced and tunned for stealth, modularity and persistence. While Brazen Bamboo is in the process of fine-tuning its strategies, the organisations and vendors have to be more careful and be ready to respond to these tricks. The continuous updating, the ability to detect the threats and a proper plan on how to deal with incidents are crucial in combating the attacks.
References:

Introduction
The first activity one engages in while using social media is scrolling through their feed and liking or reacting to posts. Social media users' online activity is passive, involving merely reading and observing, while active use occurs when a user consciously decides to share information or comment after actively analysing it. We often "like" photos, posts, and tweets reflexively, hardly stopping to think about why we do it and what information it contains. This act of "liking" or "reacting" is a passive activity that can spark an active discourse. Frequently, we encounter misinformation on social media in various forms, which could be identified as false at first glance if we exercise caution and avoid validating it with our likes.
Passive engagement, such as liking or reacting to a post, triggers social media algorithms to amplify its reach, exposing it to a broader audience. This amplification increases the likelihood of misinformation spreading quickly as more people interact with it. As the content circulates, it gains credibility through repeated exposure, reinforcing false narratives and expanding its impact.
Social media platforms are designed to facilitate communication and conversations for various purposes. However, this design also enables the sharing, exchange, distribution, and reception of content, including misinformation. This can lead to the widespread spread of false information, influencing public opinion and behaviour. Misinformation has been identified as a contributing factor in various contentious events, ranging from elections and referenda to political or religious persecution, as well as the global response to the COVID-19 pandemic.
The Mechanics of Passive Sharing
Sharing a post without checking the facts mentioned or sharing it without providing any context can create situations where misinformation can be knowingly or unknowingly spread. The problem with sharing and forwarding information on social media without fact-checking is that it usually starts in small, trusted networks before going on to be widely seen across the internet. This web which begins is infinite and cutting it from the roots is necessary. The rapid spread of information on social media is driven by algorithms that prioritise engagement and often they amplify misleading or false content and contribute to the spread of misinformation. The algorithm optimises the feed and ensures that the posts that are most likely to engage with appear at the top of the timeline, thus encouraging a cycle of liking and posting that keeps users active and scrolling.
The internet reaches billions of individuals and enables them to tailor persuasive messages to the specific profiles of individual users. The internet because of its reach is an ideal medium for the fast spread of falsehoods at the expense of accurate information.
Recommendations for Combating Passive Sharing
The need to combat passive sharing that we indulge in is important and some ways in which we can do so are as follows:
- We need to critically evaluate the sources before sharing any content. This will ensure that the information source is not corrupted and used as a means to cause disruptions. The medium should not be used to spread misinformation due to the source's ulterior motives. Tools such as crowdsourcing and AI methods have been used in the past to evaluate the sources and have been successful to an extent.
- Engaging with fact-checking tools and verifying the information is also crucial. The information that has been shared on the post needs to be verified through authenticated sources before indulging in the practice of sharing.
- Being mindful of the potential impact of online activity, including likes and shares is important. The kind of reach that social media users have today is due to several reasons ranging from the content they create, the rate at which they engage with other users etc. Liking and sharing content might not seem much for an individual user but the impact it has collectively is huge.
Conclusion
Passive sharing of misinformation, like liking or sharing without verification, amplifies false information, erodes trust in legitimate sources, and deepens social and political divides. It can lead to real-world harm and ethical dilemmas. To combat this, critical evaluation, fact-checking, and mindful online engagement are essential to mitigating this passive spread of misinformation. The small act of “like” or “share” has a much more far-reaching effect than we anticipate and we should be mindful of all our activities on the digital platform.
References
- https://www.tandfonline.com/doi/full/10.1080/00049530.2022.2113340#summary-abstract
- https://timesofindia.indiatimes.com/city/thane/badlapur-protest-police-warn-against-spreading-fake-news/articleshow/112750638.cms
Executive Summary:
New Linux malware has been discovered by a cybersecurity firm Volexity, and this new strain of malware is being referred to as DISGOMOJI. A Pakistan-based threat actor alias ‘UTA0137’ has been identified as having espionage aims, with its primary focus on Indian government entities. Like other common forms of backdoors and botnets involved in different types of cyberattacks, DISGOMOJI, the malware allows the use of commands to capture screenshots, search for files to steal, spread additional payloads, and transfer files. DISGOMOJI uses Discord (messaging service) for Command & Control (C2) and uses emojis for C2 communication. This malware targets Linux operating systems.
The DISCOMOJI Malware:
- The DISGOMOJI malware opens a specific channel in a Discord server and every new channel corresponds to a new victim. This means that the attacker can communicate with the victim one at a time.
- This particular malware connects with the attacker-controlled Discord server using Emoji, a form of relay protocol. The attacker provides unique emojis as instructions, and the malware uses emojis as a feedback to the subsequent command status.
- For instance, the ‘camera with flash’ emoji is used to screenshots the device of the victim or to steal, the ‘fox’ emoji cracks all Firefox profiles, and the ‘skull’ emoji kills the malware process.
- This C2 communication is done using emojis to ensure messaging between infected contacts, and it is almost impossible for Discord to shut down the malware as it can always change the account details of Discord it is using once the maliciou server is blocked.
- The malware also has capabilities aside from the emoji-based C2 such as network probing, tunneling, and data theft that are needed to help the UTA0137 threat actor in achieving its espionage goals.
Specific emojis used for different commands by UTA0137:
- Camera with Flash (📸): Captures a picture of the target device’s screen as per the victim’s directions.
- Backhand Index Pointing Down (👇): Extracts files from the targeted device and sends them to the command channel in the form of attachments.
- Backhand Index Pointing Right (👉): This process involves sending a file found on the victim’s device to another web-hosted file storage service known as Oshi or oshi[. ]at.
- Backhand Index Pointing Left (👈): Sends a file from the victim’s device to transfer[. ]sh, which is an online service for sharing files on the Internet.
- Fire (🔥): Finds and transmits all files with certain extensions that exist on the victim’s device, such as *. txt, *. doc, *. xls, *. pdf, *. ppt, *. rtf, *. log, *. cfg, *. dat, *. db, *. mdb, *. odb, *. sql, *. json, *. xml, *. php, *. asp, *. pl, *. sh, *. py, *. ino, *. cpp, *. java,
- Fox (🦊): This works by compressing all Firefox related profiles in the affected device.
- Skull (💀): Kills the malware process in windows using ‘os. Exit()’
- Man Running (🏃♂️): Execute a command on a victim’s device. This command receives an argument, which is the command to execute.
- Index Pointing up (👆) : Upload a file to the victim's device. The file to upload is attached along with this emoji
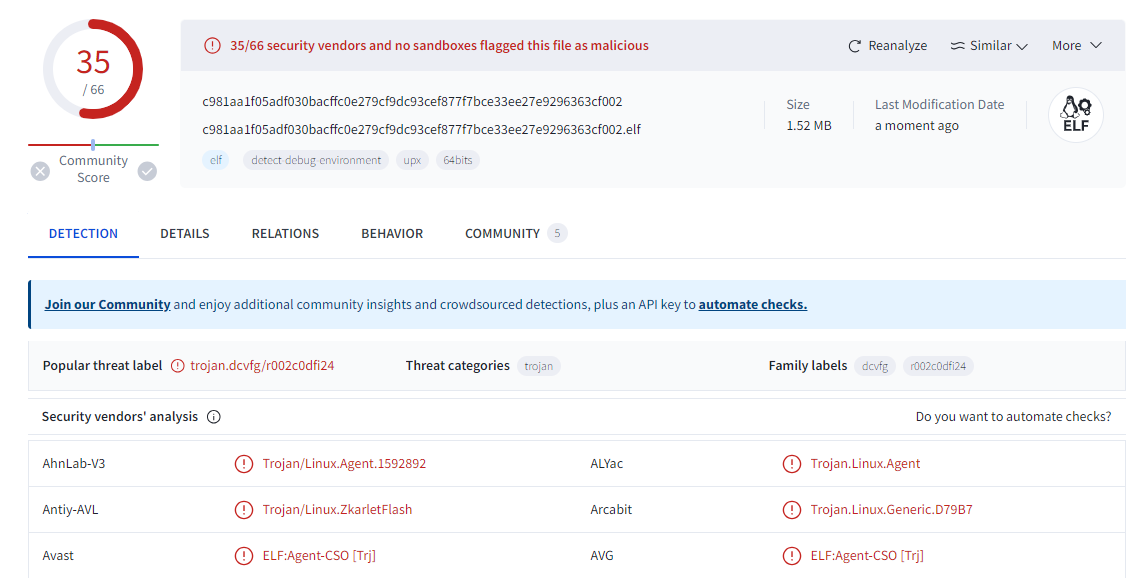
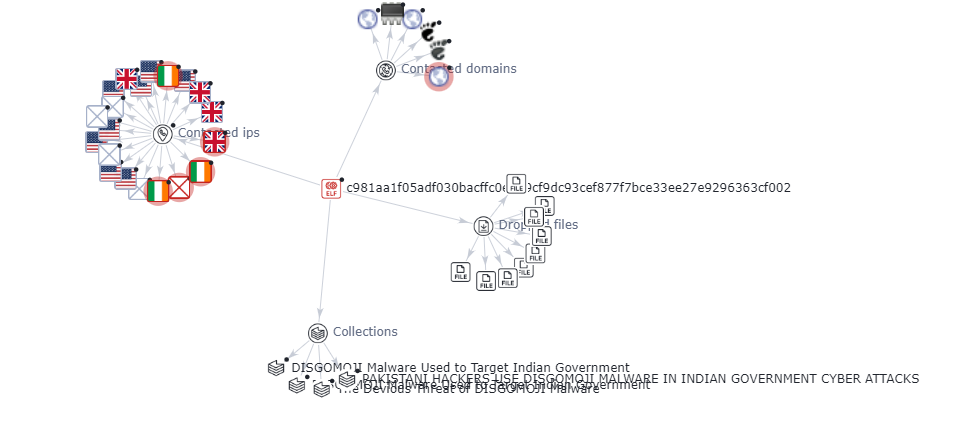
Analysis:
The analysis was carried out for one of the indicator of compromised SHA-256 hash file- C981aa1f05adf030bacffc0e279cf9dc93cef877f7bce33ee27e9296363cf002.
It is found that most of the vendors have marked the file as trojan in virustotal and the graph explains the malicious nature of the contacted domains and IPs.
Discord & C2 Communication for UTA0137:
- Stealthiness: Discord is a well-known messaging platform used for different purposes, which means that sending any messages or files on the server should not attract suspicion. Such stealthiness makes it possible for UTA0137 to remain dormant for greater periods before launching an attack.
- Customization: UTA0137 connected to Discord is able to create specific channels for distinct victims on the server. Such a framework allows the attackers to communicate with each of the victims individually to make a process more accurate and efficient.
- Emoji-based protocol: For C2 communication, emojis really complicates the attempt that Discord might make to interfere with the operations of the malware. In case the malicious server gets banned, malware could easily be recovered, especially by using the Discord credentials from the C2 server.
- Persistence: The malware, as stated above, has the ability to perpetually exist to hack the system and withstand rebooting of systems so that the virus can continue to operate without being detected by the owner of the hacked system.
- Advanced capabilities: Other features of DISGOMOJI are the Network Map using Nmap scanner, network tunneling through Chisel and Ligolo and Data Exfiltration by File Sharing services. These capabilities thus help in aiding the espionage goals of UTA0137.
- Social engineering: The virus and the trojan can show the pop-up windows and prompt messages, for example the fake update for firefox and similar applications, where the user can be tricked into inputting the password.
- Dynamic credential fetching: The malware does not write the hardcoded values of the credentials in order to connect it to the discord server. This also inconveniences analysts as they are unable to easily locate the position of the C2 server.
- Bogus informational and error messages: They never show any real information or errors because they do not want one to decipher the malicious behavior easily.
Recommendations to mitigate the risk of UTA0137:
- Regularly Update Software and Firmware: It is essential to regularly update all the application software and firmware of different devices, particularly, routers, to prevent hackers from exploiting the discovered and disclosed flaws. This includes fixing bugs such as CVE-2024-3080 and CVE-2024-3912 on ASUS routers, which basically entails solving a set of problems.
- Implement Multi-Factor Authentication: There are statistics that show how often user accounts are attacked, it is important to incorporate multi-factor authentication to further secure the accounts.
- Deploy Advanced Malware Protection: Provide robust guard that will help the user recognize and prevent the execution of the DISGOMOJI malware and similar threats.
- Enhance Network Segmentation: Utilize stringent network isolation mechanisms that seek to compartmentalize the key systems and data from the rest of the network in order to minimize the attack exposure.
- Monitor Network Activity: Scanning Network hour to hour for identifying and handling the security breach and the tools such as Nmap, Chisel, Ligolo etc can be used.
- Utilize Threat Intelligence: To leverage advanced threats intelligence which will help you acquire knowledge on previous threats and vulnerabilities and take informed actions.
- Secure Communication Channels: Mitigate the problem of the leakage of developers’ credentials and ways of engaging with the discord through loss of contact to prevent abusing attacks or gaining control over Discord as an attack vector.
- Enforce Access Control: Regularly review and update the user authentication processes by adopting stricter access control measures that will allow only the right personnel to access the right systems and information.
- Conduct Regular Security Audits: It is important to engage in security audits periodically in an effort to check some of the weaknesses present within the network or systems.
- Implement Incident Response Plan: Conduct a risk assessment, based on that design and establish an efficient incident response kit that helps in the early identification, isolation, and management of security breaches.
- Educate Users: Educate users on cybersecurity hygiene, opportunities to strengthen affinity with the University, and conduct retraining on threats like phishing and social engineering.
Conclusion:
The new threat actor named UTA0137 from Pakistan who was utilizing DISGOMOJI malware to attack Indian government institutions using embedded emojis with a command line through the Discord app was discovered by Volexity. It has the capability to exfiltrate and aims to steal the data of government entities. The UTA0137 was continuously improved over time to permanently communicate with victims. It underlines the necessity of having strong protection from viruses and hacker attacks, using secure passwords and unique codes every time, updating the software more often and having high-level anti-malware tools. Organizations can minimize advanced threats, the likes of DISGOMOJI and protect sensitive data by improving network segmentation, continuous monitoring of activities, and users’ awareness.
References:
https://otx.alienvault.com/pulse/66712446e23b1d14e4f293eb
https://thehackernews.com/2024/06/pakistani-hackers-use-disgomoji-malware.html?m=1
https://cybernews.com/news/hackers-using-emojis-to-command-malware/
https://www.volexity.com/blog/2024/06/13/disgomoji-malware-used-to-target-indian-government/

Introduction
The ‘Barbie’ fever is going high in India, and it’s hype to launch online scams in India. The cybercriminals attacking the ‘Barbie’ fans in India, as the popular malware and antivirus protection MacAfee has recently reported that India is in the top 3rd number among countries facing major malware attacks. After the release of ‘barbie’ in theatres, the Scams started spreading across India through the free download of the ‘Barbie’ movie from the link and other viruses. The scammers trick the victims by selling free ‘Barbie’ tickets and, after the movie’s hit, search for the free download links on websites which leads to the Scams.
What is the ‘Barbie’ malware?
After the release of the ‘Barbie’ movie, trying to keep up with the trend, Barbie fans started to search the links for free movie downloads from anonymous sources. And after downloading the movie, there was malware in the downloaded zip files. The online scam includes not genuine dubbed downloads of the movie that install malware, barbie-related viruses, and fake videos that point to free tickets, and also clicking on unverified links for the movie access resulted in Scam. It is important not to get stuck in these trends just because to keep up with them, as it could land you in trouble.
Case: As per the report of McAfee, several cases of malware trick victims into downloading the ‘ Barbie’ movie in different languages. By clicking the link, it prompts the user to download a Zip file, which is packed with malware
Countries-wise malware distribution
Cyber Scams witnessed a significant surge in just a few weeks, with hundreds of incidents of new malware cases. And The USA is on the top No. Among all the countries, In the USA there was 37 % of ‘Barbie’ malware attacks held per the, while Australia, the UK, and India suffered 6 % of malware attacks. And other countries like Japan, Ireland, and France faced 3% of Malware attacks.
What are the precautions?
Cyber scams are evolving everywhere, users must remain vigilant and take necessary precautions to protect their personal information. The user shall avoid clicking on suspicious links, also those which are related to unauthorised movie downloads or fake ticket offers. The people shall use legitimate and official platforms to access movie-related content. Keeping anti-malware and antivirus will add an extra layer of protection.
Here are some following precautions against Malware:
- Use security software.
- Use strong passwords and authentication.
- Enforce safe browsing and email.
- Data backup.
- Implement Anti-lateral Movement.
Conclusion
Cyberspace is evolving, and with that, Scams are also evolving. With the new trend of ‘Barbie’ Scams going on the rise everywhere, India is on top 3rd No. In India, McAfee reported several malicious attacks that attempted to trick the victims into downloading the free version of ‘Barbie’ movie in dubbed languages. This resulted in a Scam. People usually try to keep up with trends that land them in trouble. The users shall beware of these kinds of cyber-attacks. These scams result in huge losses. Technology should be used with proper precautions as per the incidents happening around.

Introduction
A famous quote, “Half knowledge is always dangerous”, but “Too much knowledge of anything can lead to destruction”. Recently very infamous spyware and malware named WyrmSpy and Dragon Egg were invented by a Chinese group of hackers APT41. The APT41 is a state-endorsed Clandstein active group based in the People’s Republic of China that has been active since 2012. In contrast to numerous countries-government supported, APT has a footprint record jeopardising both government organisations for clandestine activities as well as different private organisations or enterprises for their financial gain. APT41 group aims at Android devices through spyware wyrmspy and dragon egg, which masquerades as a legitimate application. According to the U.S. jury legal accusation from 2019 to 2020, the group was entangled in threatening over more than 100 public and private individuals and organisations in the United States and around the world.Moreover, a detailed analysis report was shared by the Lookout Threat Researchers, that has been actively monitoring and tracking both spyware and malware.
Briefing about how spyware attacks on Android devices take place
To begin with, this malware imitates a real source Android application to show some sort of notification. Once it is successfully installed on the user’s machine, proclaims multiple device’s permission to enable data filtration.
Wyrmspy complies with log files, photos, device locations, SMS(read and write), and audio recordings. It has also authenticated that there are no detection malware activities found on google play even after running multiple security levels. These malicious things are made with the intent to obtain rooting access privileges to the device and monitor activities to the specified commands received from the C2 servers.
Similarly, Dragon Egg can collect data files, contacts, locations, and audio recordings, and it also accesses camera photos once it successfully trade-off the device. Dragon egg receives a payload that is also known as “smallmload.jar”, which is either from APK(Android Packet Kit).
WyrmSpy initially masquerades as a default operation system application, and Dragon Egg simulates a third-party keyboard/ messaging application.
Overview of APT41 Chinese group background
APT41 is a Chinese-based stealth activity-carrying group that is said to be active since mid-2006. Rumours about APT41 that it was also a part of the 2nd Bureau of the People’s Liberation Army (PLA) General Staff Department’s (GSD) 3rd Department. Owning to that fact, 2006 has seen 140+ organisations’ security getting compromised, ranging from 20 strategically crucial companies.APT is also recognised for rationally plundering hundreds of terabytes of data from at least 141 organisations between 2006 and 2013. It typically begins with spear-phishing emails to the targeted victims. These sent emails contain official templates along with language pretending to be from a legitimate real source, carrying a malicious attachment. As the victim opens the attached file, the backdoor bestows the control of the targeted machine to the APT groups machine. Once there is an unauthorised gain of access, the attacker visits and revisits the victim’s machine. The group remains dormant for lengthy durations, more likely for months or even for years.
Advisory points need to adhere to while using Android devices
- The security patch update is necessary at least once a week
- Clearing up unwanted junk files.
- Cache files of every frequently used application need to clear out.
- Install only required applications from
Google play store. - Download only necessary APK files only it comes from trusted resources.
- Before giving device permission, it is advisable to run your files or URLs on VirusTotal.com this website will give a good closure to the malicious intent.
- Install good antivirus software.
- Individuals need to check the source of the email before opening an attachment to it.
- Never collect or add any randomly found device to your system
- Moreover, the user needs to keep track of their device activity. Rather than using devices just for entertainment purposes, it is more important to look for data protection on that device.
Conclusion
Network Crack Program Hacker Group (NCPH), which grew as an APT41 group with malicious intent, earlier performed the role of grey hat hacker, this group somehow grew up greedy to enhance more money laundering by hacking networks, devices, etc. As this group conducts a supply chain of attacks to gain unauthorised access to the network throughout the world, targeting hundreds of companies, including an extensive selection of industries such as social media, telecommunications, government, defence, education, and manufacturing. Last but not least, many more fraud-making groups with malicious intent will be forming and implementing in the future. It is on individuals and organisations to secure themselves but practise basic security levels to safeguard themselves against such threats and attacks.

Pretext
The Army Welfare Education Society has informed the Parents and students that a Scam is targeting the Army schools Students. The Scamster approaches the students by faking the voice of a female and a male. The scamster asks for the personal information and photos of the students by telling them they are taking details for the event, which is being organised by the Army welfare education society for the celebration of independence day. The Army welfare education society intimated that Parents to beware of these calls from scammers.
The students of Army Schools of Jammu & Kashmir, Noida, are getting calls from the scamster. The students were asked to share sensitive information. Students across the country are getting calls and WhatsApp messages from two numbers, which end with 1715 and 2167. The Scamster are posing to be teachers and asking for the students’ names on the pretext of adding them to the WhatsApp Groups. The scamster then sends forms links to the WhatsApp groups and asking students to fill out the form to seek more sensitive information.
Do’s
- Do Make sure to verify the caller.
- Do block the caller while finding it suspicious.
- Do be careful while sharing personal Information.
- Do inform the School Authorities while receiving these types of calls and messages posing to be teachers.
- Do Check the legitimacy of any agency and organisation while telling the details
- Do Record Calls asking for personal information.
- Do inform parents about scam calling.
- Do cross-check the caller and ask for crucial information.
- Do make others aware of the scam.
Don’ts
- Don’t answer anonymous calls or unknown calls from anyone.
- Don’t share personal information with anyone.
- Don’t Share OTP with anyone.
- Don’t open suspicious links.
- Don’t fill any forms, asking for personal information
- Don’t confirm your identity until you know the caller.
- Don’t Reply to messages asking for financial information.
- Don’t go to a fake website by following a prompt call.
- Don’t share bank Details and passwords.
- Don’t Make payment over a prompt fake call.

Introduction
Discussions took place focused on cybersecurity measures, specifically addressing cybercrime in the context of emerging technologies such as Non-Fungible Tokens (NFTs), Artificial Intelligence (AI), and the Metaverse. Session 5 of the conference focused on the interconnectedness between the darknet and cryptocurrency and the challenges it poses for law enforcement agencies and regulators. They discussed that Understanding AI is necessary for enterprises. AI models have difficulties, but we are looking forward to trustworthy AIs. and AI technology must be transparent.
Darknet and Cryptocurrency
The darknet refers to the hidden part of the internet where illicit activities have proliferated in recent years. It was initially developed to provide anonymity, privacy, and protection to specific individuals such as journalists, activists, and whistleblowers. However, it has now become a playground for criminal activities. Cryptocurrency, particularly Bitcoin, has been widely adopted on the darknet due to its anonymous nature, enabling anti-money laundering and unlawful transactions.
Three major points emerge from this relationship: the integrated nature of the darknet and cryptocurrency, the need for regulations to prevent darknet-based crimes, and the importance of striking a balance between privacy and security.
Key Challenges:
- Integrated Relations: The darknet and cryptocurrency have evolved independently, with different motives and purposes. It is crucial to understand the integrated relationship between them and how criminals exploit this connection.
- Regulatory Frameworks: There is a need for effective regulations to prevent crimes facilitated through the darknet and cryptocurrency while striking a balance between privacy and security.
- Privacy and Security: Privacy is a fundamental right, and any measures taken to enhance security should not infringe upon individual privacy. A multistakeholder approach involving tech companies and regulators is necessary to find this delicate balance.
Challenges Associated with Cryptocurrency Use:
The use of cryptocurrency on the darknet poses several challenges. The risks associated with darknet-based cryptocurrency crimes are a significant concern. Additionally, regulatory challenges arise due to the decentralised and borderless nature of cryptocurrencies. Mitigating these challenges requires innovative approaches utilising emerging technologies.
Preventing Misuse of Technologies:
The discussion emphasised that we can step ahead of the people who wish to use these beautiful technologies meant and developed for a different purpose, to prevent from using them for crime.
Monitoring the Darknet:
The darknet, as explained, is an elusive part of the internet that necessitates the use of a special browser for access. Initially designed for secure communication by the US government, its purpose has drastically changed over time. The darknet’s evolution has given rise to significant challenges for law enforcement agencies striving to monitor its activities.
Around 95% of the activities carried out on the dark net are associated with criminal acts. Estimates suggest that over 50% of the global cybercrime revenue originates from the dark net. This implies that approximately half of all cybercrimes are facilitated through the darknet.
The exploitation of the darknet has raised concerns regarding the need for effective regulation. Monitoring the darknet is crucial for law enforcement, national agencies, and cybersecurity companies. The challenges associated with the darknet’s exploitation and the criminal activities facilitated by cryptocurrency emphasise the pressing need for regulations to ensure a secure digital landscape.
Use of Cryptocurrency on the Darknet
Cryptocurrency plays a central role in the activities taking place on the darknet. The discussion highlighted its involvement in various illicit practices, including ransomware attacks, terrorist financing, extortion, theft, and the operation of darknet marketplaces. These applications leverage cryptocurrency’s anonymous features to enable illegal transactions and maintain anonymity.
AI's Role in De-Anonymizing the Darknet and Monitoring Challenges:
- 1.AI’s Potential in De-Anonymizing the Darknet
During the discussion, it was highlighted how AI could be utilised to help in de-anonymizing the darknet. AI’s pattern recognition capabilities can aid in identifying and analysing patterns of behaviour within the darknet, enabling law enforcement agencies and cybersecurity experts to gain insights into its operations. However, there are limitations to what AI can accomplish in this context. AI cannot break encryption or directly associate patterns with specific users, but it can assist in identifying illegal marketplaces and facilitating their takedown. The dynamic nature of the darknet, with new marketplaces quickly emerging, adds further complexity to monitoring efforts.
- 2.Challenges in Darknet Monitoring
Monitoring the darknet poses various challenges due to its vast amount of data, anonymous and encrypted nature, dynamically evolving landscape, and the need for specialised access. These challenges make it difficult for law enforcement agencies and cybersecurity professionals to effectively track and prevent illicit activities.
- 3.Possible Ways Forward
To address the challenges, several potential avenues were discussed. Ethical considerations, striking a balance between privacy and security, must be taken into account. Cross-border collaboration, involving the development of relevant laws and policies, can enhance efforts to combat darknet-related crimes. Additionally, education and awareness initiatives, driven by collaboration among law enforcement, government entities, and academia, can play a crucial role in combating darknet activities.
The panel also addressed the questions from the audience
- How law enforcement agencies and regulators can use AI to detect and prevent crimes on the darknet and cryptocurrency? The panel answered that- Law enforcement officers should also be AI and technology ready, and that kind of upskilling program should be there in place.
- How should lawyers and the judiciary understand the problem and regulate it? The panel answered that AI should only be applied by looking at the outcomes. And Law has to be clear as to what is acceptable and what is not.
- Aligning AI with human intention? Whether it’s possible? Whether can we create an ethical AI instead of talking about using AI ethically? The panel answered that we have to understand how to behave ethically. AI can beat any human. We have to learn AI. Step one is to focus on our ethical behaviour. And step two is bringing the ethical aspect to the software and technologies. Aligning AI with human intention and creating ethical AI is a challenge. The focus should be on ethical behaviour both in humans and in the development of AI technologies.
Conclusion
The G20 Conference on Crime and Security shed light on the intertwined relationship between the darknet and cryptocurrency and the challenges it presents to cybersecurity. The discussions emphasised the need for effective regulations, privacy-security balance, AI integration, and cross-border collaboration to tackle the rising cybercrime activities associated with the darknet and cryptocurrency. Addressing these challenges will require the combined efforts of governments, law enforcement agencies, technology companies, and individuals committed to building a safer digital landscape.

Introduction
According to a shocking report, there are multiple scam loan apps on the App Store in India that charge excessive interest rates and force users to pay by blackmailing and harassing them. Apple has prohibited and removed these apps from the App Store, but they may still be installed on your iPhone and running. You must delete any of these apps if you have downloaded them. Learn the names of these apps and how they operated the fraud.
Why Apple banned these apps?
- Apple has taken action to remove certain apps from the Indian App Store. These apps were engaging in unethical behaviour, such as impersonating financial institutions, demanding high fees, and threatening borrowers. Here are the titles of these apps, as well as what Apple has said about their suspension.
- Following user concerns, Apple removed six loan apps from the Indian App Store. Loan apps include White Kash, Pocket Kash, Golden Kash, Ok Rupee, and others.
- According to multiple user reviews, certain apps seek unjustified access to users’ contact lists and media. These apps also charge exorbitant fees that are not necessitated. Furthermore, companies have been found to engage in unethical tactics such as charging high-interest rates and “processing fees” equal to half the loan amount.
- Some lending app users have reported being harassed and threatened for failing to return their loans on time. In some circumstances, the apps threatened the user’s contacts if payment was not completed by the deadline. According to one user, the app company threatened to produce and send false photographs of her to her contacts.
- These loan apps were removed from the App Store, according to Apple, because they broke the norms and standards of the Apple Developer Program License Agreement. These apps were discovered to be falsely claiming financial institution connections.
Issue of Fake loan apps on the App Store
- The App Store and our App Review Guidelines are designed to ensure we provide our users with the safest experience possible,” Apple explained. “We do not tolerate fraudulent activity on the App Store and have strict rules against apps and developers who attempt to game the system.
- In 2022, Apple blocked nearly $2 billion in fraudulent App Store sales. Furthermore, it rejected nearly 1.7 million software submissions that did not match Apple’s quality and safety criteria and cancelled 428,000 developer accounts due to suspected fraudulent activities.
- The scammers also used heinous tactics to force the loanees to pay. According to reports, the scammers behind the apps gained access to the user’s contact list as well as their images. They would morph the images and then scare the individual by sharing their fake nude photos with their whole contact list.
Dangerous financial fraud apps have surfaced on the App Store
- TechCrunch acquired a user review from one of these apps. “I borrowed an amount in a helpless situation, and a day before the repayment due date, I got some messages with my picture and my contacts in my phone saying that repay your loan or they will inform our contacts that you are not paying the loan,” it said.
- Sandhya Ramesh, a journalist from The Print, recently tweeted a screenshot of a direct message she got. A victim’s friend told a similar story in the message.
- TechCrunch contacted Apple, who confirmed that the apps had been removed from the App Store for breaking the Apple Developer Program License Agreement and guidelines.
Conclusion
Recently, some users have claimed that some quick-loan applications, such as White Kash, Pocket Kash, and Golden Kash, have appeared on the Top Finance applications chart in recent days. These apps necessitate unauthorised and intrusive access to users’ contact lists and media. According to hundreds of user evaluations, these apps charged exorbitantly high and useless fees. They used unscrupulous techniques such as demanding “processing fees” equal to half the loan amount and charging high-interest rates. Users were also harassed and threatened with restitution. If payments were not made by the due date, the lending applications threatened to notify users’ contacts. According to one user, the app provider even threatened to generate phoney nude images of her and send them to her contacts.

Introduction
In a distressing incident that highlights the growing threat of cyber fraud, a software engineer in Bangalore fell victim to fraudsters who posed as police officials. These miscreants, operating under the guise of a fake courier service and law enforcement, employed a sophisticated scam to dupe unsuspecting individuals out of their hard-earned money. Unfortunately, this is not an isolated incident, as several cases of similar fraud have been reported recently in Bangalore and other cities. It is crucial for everyone to be aware of these scams and adopt preventive measures to protect themselves.
Bangalore Techie Falls Victim to ₹33 Lakh
The software engineer received a call from someone claiming to be from FedEx courier service, informing him that a parcel sent in his name to Taiwan had been seized by the Mumbai police for containing illegal items. The call was then transferred to an impersonator posing as a Mumbai Deputy Commissioner of Police (DCP), who alleged that a money laundering case had been registered against him. The fraudsters then coerced him into joining a Skype call for verification purposes, during which they obtained his personal details, including bank account information.
Under the guise of verifying his credentials, the fraudsters manipulated him into transferring a significant amount of money to various accounts. They assured him that the funds would be returned after the completion of the procedure. However, once the money was transferred, the fraudsters disappeared, leaving the victim devastated and financially drained.
Best Practices to Stay Safe
- Be vigilant and skeptical: Maintain a healthy level of skepticism when receiving unsolicited calls or messages, especially if they involve sensitive information or financial matters. Be cautious of callers pressuring you to disclose personal details or engage in immediate financial transactions.
- Verify the caller’s authenticity: If someone claims to represent a legitimate organisation or law enforcement agency, independently verify their credentials. Look up the official contact details of the organization or agency and reach out to them directly to confirm the authenticity of the communication.
- Never share sensitive information: Avoid sharing personal information, such as bank account details, passwords, or Aadhaar numbers, over the phone or through unfamiliar online platforms. Legitimate organizations will not ask for such information without proper authentication protocols.
- Use secure communication channels: When communicating sensitive information, prefer secure platforms or official channels that provide end-to-end encryption. Avoid switching to alternative platforms or applications suggested by unknown callers, as fraudsters can exploit these.
- Educate yourself and others: Stay informed about the latest cyber fraud techniques and scams prevalent in your region. Share this knowledge with family, friends, and colleagues to create awareness and prevent them from falling victim to similar schemes.
- Implement robust security measures: Keep your devices and software updated with the latest security patches. Utilize robust anti-virus software, firewalls, and spam filters to safeguard against malicious activities. Regularly review your financial statements and account activity to detect any unauthorized transactions promptly.
Conclusion:
The incident involving the Bangalore techie and other victims of cyber fraud highlights the importance of remaining vigilant and adopting preventive measures to safeguard oneself from such scams. It is disheartening to see individuals falling prey to impersonators who exploit their trust and manipulate them into sharing sensitive information. By staying informed, exercising caution, and following best practices, we can collectively minimize the risk and protect ourselves from these fraudulent activities. Remember, the best defense against cyber fraud is a well-informed and alert individual.

Introduction
Deepfakes are artificial intelligence (AI) technology that employs deep learning to generate realistic-looking but phoney films or images. Algorithms use large volumes of data to analyse and discover patterns in order to provide compelling and realistic results. Deepfakes use this technology to modify movies or photos to make them appear as if they involve events or persons that never happened or existed.The procedure begins with gathering large volumes of visual and auditory data about the target individual, which is usually obtained from publicly accessible sources such as social media or public appearances. This data is then utilised for training a deep-learning model to resemble the target of deep fakes.
Recent Cases of Deepfakes-
In an unusual turn of events, a man from northern China became the victim of a sophisticated deep fake technology. This incident has heightened concerns about using artificial intelligence (AI) tools to aid financial crimes, putting authorities and the general public on high alert.
During a video conversation, a scammer successfully impersonated the victim’s close friend using AI-powered face-swapping technology. The scammer duped the unwary victim into transferring 4.3 million yuan (nearly Rs 5 crore). The fraud occurred in Baotou, China.
AI ‘deep fakes’ of innocent images fuel spike in sextortion scams
Artificial intelligence-generated “deepfakes” are fuelling sextortion frauds like a dry brush in a raging wildfire. According to the FBI, the number of nationally reported sextortion instances came to 322% between February 2022 and February 2023, with a notable spike since April due to AI-doctored photographs. And as per the FBI, innocent photographs or videos posted on social media or sent in communications can be distorted into sexually explicit, AI-generated visuals that are “true-to-life” and practically hard to distinguish. According to the FBI, predators often located in other countries use doctored AI photographs against juveniles to compel money from them or their families or to obtain actual sexually graphic images.
Deepfake Applications
- Lensa AI.
- Deepfakes Web.
- Reface.
- MyHeritage.
- DeepFaceLab.
- Deep Art.
- Face Swap Live.
- FaceApp.
Deepfake examples
There are numerous high-profile Deepfake examples available. Deepfake films include one released by actor Jordan Peele, who used actual footage of Barack Obama and his own imitation of Obama to convey a warning about Deepfake videos.
A video shows Facebook CEO Mark Zuckerberg discussing how Facebook ‘controls the future’ with stolen user data, most notably on Instagram. The original video is from a speech he delivered on Russian election meddling; only 21 seconds of that address were used to create the new version. However, the vocal impersonation fell short of Jordan Peele’s Obama and revealed the truth.
The dark side of AI-Generated Misinformation
- Misinformation generated by AI-generated the truth, making it difficult to distinguish fact from fiction.
- People can unmask AI content by looking for discrepancies and lacking the human touch.
- AI content detection technologies can detect and neutralise disinformation, preventing it from spreading.
Safeguards against Deepfakes-
Technology is not the only way to guard against Deepfake videos. Good fundamental security methods are incredibly effective for combating Deepfake.For example, incorporating automatic checks into any mechanism for disbursing payments might have prevented numerous Deepfake and related frauds. You might also:
- Regular backups safeguard your data from ransomware and allow you to restore damaged data.
- Using different, strong passwords for different accounts ensures that just because one network or service has been compromised, it does not imply that others have been compromised as well. You do not want someone to be able to access your other accounts if they get into your Facebook account.
- To secure your home network, laptop, and smartphone against cyber dangers, use a good security package such as Kaspersky Total Security. This bundle includes anti-virus software, a VPN to prevent compromised Wi-Fi connections, and webcam security.
What is the future of Deepfake –
Deepfake is constantly growing. Deepfake films were easy to spot two years ago because of the clumsy movement and the fact that the simulated figure never looked to blink. However, the most recent generation of bogus videos has evolved and adapted.
There are currently approximately 15,000 Deepfake videos available online. Some are just for fun, while others attempt to sway your opinion. But now that it only takes a day or two to make a new Deepfake, that number could rise rapidly.
Conclusion-
The distinction between authentic and fake content will undoubtedly become more challenging to identify as technology advances. As a result, experts feel it should not be up to individuals to discover deep fakes in the wild. “The responsibility should be on the developers, toolmakers, and tech companies to create invisible watermarks and signal what the source of that image is,” they stated. Several startups are also working on approaches for detecting deep fakes.

Introduction
In recent years, the city of Hyderabad/Cyberabad has emerged as a technology hub, a place with the strong presence of multi corporations, Startups, and research institutions, Hyderabad has become a hub of innovations and technological advancement. However, this growing land of cyber opportunities has also become a hub for cybercriminals as well. In this blog post, we shall explore the reasons why professionals are being targeted and the effects of cyber fraud on techies. Through this investigation, we hope to raise awareness about the seriousness of the problem as well as give vital insights and techniques for Cyberabad’s computer workers to defend themselves against cyber theft. We can work together to make Cyberabad’s technology ecosystem safer and more secure.
Defining Cyber Fraud
In today’s age, where everything has an interconnected digital world, cyber fraud cases are increasing daily. Cyber fraud encompasses a wide range of threats and techniques employed by bad actors, such as Phishing, Ransomware, identity theft, online scams, data breaches, and fake websites designed for users. The sophistication of cyber fraud techniques is constantly evolving, making it challenging for individuals and organisations to stay ahead. Cybercriminals use software vulnerabilities, social engineering tactics, and flaws in cybersecurity defences to carry out their harmful operations. Individuals and organisations must grasp these dangers and tactics to protect themselves against cyber fraud.
Impact of Cyber Frauds
The consequences of Falling victim to cyber fraud can be devastating, both personally and professionally. The emotional and financial toll on individuals may be a challenge. Identity theft may lead to damaged credit scores, fraudulent transactions, and years of recovery work to rehabilitate one’s image. Financial fraud can result in depleted bank accounts, unauthorised charges, and substantial monetary losses. Furthermore, being tricked and violated in the digital environment can generate anxiety, tension, and a lack of confidence.
The impact of cyber fraud goes beyond immediate financial losses and can have long-term consequences for individuals’ and organisations’ entire well-being and stability. As the threat environment evolves, it is critical for people and organisations to recognise the gravity of these repercussions and take proactive actions to protect themselves against cyber theft.

Why are Cyberabad Tech Professionals Targeted?
Tech professionals in Cyberabad are particularly vulnerable to cyber due to various factors. Firstly, their expertise and knowledge in technology make them attractive targets for cybercrooks. These professionals possess valuable coding, Software, and administration skills, making them attractive to cybercriminals.
Secondly, the nature of work often involves enormous use of technology, including regular internet contacts, email exchanges, and access to private information. This expanded digital presence exposes them to possible cyber dangers and makes them more vulnerable to fraudsters’ social engineering efforts. Furthermore, the fast-moving nature of the tech industry, with many deadlines and work pressure to deliver, can create a distraction. This can let them click on some malicious links or share sensitive information unknowingly all these factors let the cyber criminals exploit vulnerabilities.
Unveiling the Statistics
According to various reports, 80% of cyber fraud victims in Hyderabad are techies; the rest are the public targeted by cyber crooks. This surprising number emphasises the critical need to address the vulnerabilities and threats this specific segment within the IT community faces.
Going further into the data, we can acquire insights into the many forms of cyber fraud targeting tech workers, the strategies used by cybercriminals, and the impact these occurrences have on individuals and organisations. Examining precise features and patterns within data might give important information for developing successful preventative and protection methods.
Factors Contributing
Several reasons contribute to the elevated risk of cyber fraud among ICT professionals in Cyberabad. Understanding these aspects helps explain why this group is specifically targeted and may be more vulnerable to such assaults.
Technical Expertise: Tech workers frequently have specialised technical knowledge, but this knowledge may only sometimes extend to cybersecurity. Their primary concentration is writing software, designing systems, or implementing technologies, which may result in missing possible vulnerabilities or a lack of overall cybersecurity understanding.
Confidence in Technology: IT workers have a higher level of confidence in technology because of their knowledge and dependence on technology. This trust can sometimes make individuals more vulnerable to sophisticated frauds or social engineering approaches that prey on their faith in the services they utilise.
Time Constraints and Pressure: Tech workers frequently operate under tight deadlines and tremendous pressure to reach project milestones. This may result in hurried decision-making or disregarding possible warning signals of cyber fraud, rendering them more exposed to assaults that prey on time-sensitive circumstances.
Cybercriminals know that technology workers have valuable knowledge, trade secrets, and intellectual property that may be economically profitable. As a result, they are attractive targets for attacks aiming at stealing sensitive data or gaining unauthorised access to critical systems.
The best practices that cyber techies can apply to safeguard their personal and professional data by following these simple tips:
Strong Passwords: create a strong password, using passwords for all your online accounts and changing them regularly. Remember to use unique combinations!
MFA (Multi-Factor Authentication): Enable MFA wherever possible. This provides an extra degree of protection by requiring a second form of verification, such as a code texted to your mobile device and your password.
Use Secured WiFi: Use secure and encrypted Wi-Fi networks, especially while viewing sensitive information. Avoid connecting to public or unprotected networks, as they can be readily exploited. Recognising Red Flags and Staying Ahead
Social Engineering: Be sceptical of unwanted solicitations or offers, both online and offline. Cybercriminals may try to persuade or fool you using social engineering tactics. Before revealing any personal or private information, think critically and confirm the veracity of the request.
Secure Web Browsing: Only browse trustworthy websites with valid SSL certificates (look for “https://” in the URL). Avoid clicking on strange links or downloading files from unknown sources since they may contain malware or ransomware.
Report Suspicious actions: If you encounter any suspicious or fraudulent actions, report them to the relevant authorities, such as the Cyber Crime Police or your organisation’s IT department. Reporting events can assist in avoiding additional harm and aid in identifying and apprehending hackers.
Stay Current on Security Practises: Stay up to speed on the newest cybersecurity risks and best practices. Follow credible sources, participate in cybersecurity forums or seminars, and remain current on new threats and preventative measures.

Conclusion
The rise in cybercrimes and fraud cases among tech experts in Cyberabad is a disturbing trend that requires prompt intervention. We can establish a safer tech cluster that lives on creativity, trust, and resilience by adopting proactive actions, raising awareness, and encouraging cooperation. Let us work together to prevent cybercrime and ensure the future of Cyberabad’s IT ecosystem.
Introduction
The information of hundreds of thousands of Indians who received the COVID vaccine was Leaked in a significant data breach and posted on a Telegram channel. Numerous reports claim that sensitive information, including a person’s phone number, gender, ID card details, and date of birth, leaked over Telegram. It could be obtained by typing a person’s name into a Telegram bot.
What really happened?
The records pertaining to the mobile number registered in the CoWin portal are accessible on the Malayalam news website channel. It is also feasible to determine which vaccination was given and where it was given.
According to The Report, the list of individuals whose data was exposed includes BJP Tamil Nadu president K Annamalai, Congress MP Karti Chidambaram, and former BJP union minister for health Harsh Vardhan. Telangana’s minister of information and communication technology, Kalvakuntla Taraka Rama Rao, is also on the list.
MEITY stated in response to the data leak, “It is old data, we are still confirming it. We have requested a report on the matter.
After the media Report, the bot was disabled, but experts said the incident raised severe issues because the information might be used for identity theft, phishing emails, con games, and extortion calls. The Indian Computer Emergency Response Team (CERT-In), the government’s nodal body, has opened an investigation into the situation
The central government declared the data breach reports regarding the repository of beneficiaries against Covid to be “mischievous in nature” on Monday and claimed the ‘bot’ that purportedly accessed the confidential data was not directly accessing the CoWIN database.
According to the first complaint by CERT-In, the government’s cybersecurity division, the government claimed the bot might be displaying information from “previously stolen data.” Reports.
The health ministry refuted the claim, asserting that no bots could access the information without first verifying with a one-time password.
“It is made clear that all of these rumours are false and malicious. The health ministry’s CoWIN interface is entirely secure and has sufficient data privacy protections. The security of the data on the CoWIN portal is being ensured in every way possible, according to a statement from the health ministry.
Meity said the CoWin program or database was not directly compromised, and the shared information appeared to be taken from a previous intrusion. But the hack again highlights the growing danger of cyber assaults, particularly on official websites.

Recent cases of data leak
Dominos India 2021– Dominos India, a division of Jubilant FoodWorks, faced a cyberattack on May 22, 2021, which led to the disclosure of information from 180 million orders. The breach exposed order information, email addresses, phone numbers, and credit card information. Although Jubilant FoodWorks acknowledged a security breach, it refuted any illegal access to financial data.
Air India – A cyberattack that affected Air India in May 2021 exposed the personal information of about 4.5 million customers globally. Personal information recorded between August 26, 2011, and February 3, 2021, including names, dates of birth, contact information, passport information, ticket details, frequent flyer information from Star Alliance and Air India, and credit card information, were exposed in the breach.
Bigbasket – BigBasket, an online supermarket, had a data breach in November 2020, compromising the personal information of approximately 20 million consumers. Email IDs, password hashes, PINs, phone numbers, addresses, dates of birth, localities, and IP addresses were among the information released from an insecure database containing over 15 GB of customer data. BigBasket admitted to the incident and reported it to the Bengaluru Cyber Crime Department.
Unacademy – Unacademy, an online learning platform, experienced a data breach in May 2020, compromising the email addresses of approximately 11 million subscribers. While no sensitive information, such as financial data or passwords, was compromised, user data, including IDs, passwords, date joined, last login date, email IDs, names, and user credentials, was. The breach was detected when user accounts were uncovered for sale on the dark web.
2022 Card Data- Cybersecurity researchers from AI-driven Singapore-based CloudSEK found a threat actor offering a database of 1.2 million cards for free on a Dark Web forum for crimes on October 12, 2022. This came after a second problem involving 7.9 million cardholder records that were reported on the BidenCash website. This comprised information pertaining to State Bank of India (SBI) clients. And other well-known companies were among those targeted in high-profile data breach cases that have surfaced in recent years.

Conclusion
Data breach cases are increasing daily, and attackers are mainly attacking the healthcare sectors and health details as they can easily find personal details. This recent CoWIN case has compromised thousands of people’s data. The All-India Institute of Medical Sciences’ systems were compromised by hackers a few months ago. Over 95% of adults have had their vaccinations, according to the most recent data, even if the precise number of persons impacted by the CoWin privacy breach could not be determined.

Introduction
The advent of AI-driven deepfake technology has facilitated the creation of explicit counterfeit videos for sextortion purposes. There has been an alarming increase in the use of Artificial Intelligence to create fake explicit images or videos for sextortion.
What is AI Sextortion and Deepfake Technology
AI sextortion refers to the use of artificial intelligence (AI) technology, particularly deepfake algorithms, to create counterfeit explicit videos or images for the purpose of harassing, extorting, or blackmailing individuals. Deepfake technology utilises AI algorithms to manipulate or replace faces and bodies in videos, making them appear realistic and often indistinguishable from genuine footage. This enables malicious actors to create explicit content that falsely portrays individuals engaging in sexual activities, even if they never participated in such actions.
Background on the Alarming Increase in AI Sextortion Cases
Recently there has been a significant increase in AI sextortion cases. Advancements in AI and deepfake technology have made it easier for perpetrators to create highly convincing fake explicit videos or images. The algorithms behind these technologies have become more sophisticated, allowing for more seamless and realistic manipulations. And the accessibility of AI tools and resources has increased, with open-source software and cloud-based services readily available to anyone. This accessibility has lowered the barrier to entry, enabling individuals with malicious intent to exploit these technologies for sextortion purposes.

The proliferation of sharing content on social media
The proliferation of social media platforms and the widespread sharing of personal content online have provided perpetrators with a vast pool of potential victims’ images and videos. By utilising these readily available resources, perpetrators can create deepfake explicit content that closely resembles the victims, increasing the likelihood of success in their extortion schemes.
Furthermore, the anonymity and wide reach of the internet and social media platforms allow perpetrators to distribute manipulated content quickly and easily. They can target individuals specifically or upload the content to public forums and pornographic websites, amplifying the impact and humiliation experienced by victims.
What are law agencies doing?
The alarming increase in AI sextortion cases has prompted concern among law enforcement agencies, advocacy groups, and technology companies. This is high time to make strong Efforts to raise awareness about the risks of AI sextortion, develop detection and prevention tools, and strengthen legal frameworks to address these emerging threats to individuals’ privacy, safety, and well-being.
There is a need for Technological Solutions, which develops and deploys advanced AI-based detection tools to identify and flag AI-generated deepfake content on platforms and services. And collaboration with technology companies to integrate such solutions.
Collaboration with Social Media Platforms is also needed. Social media platforms and technology companies can reframe and enforce community guidelines and policies against disseminating AI-generated explicit content. And can ensure foster cooperation in developing robust content moderation systems and reporting mechanisms.
There is a need to strengthen the legal frameworks to address AI sextortion, including laws that specifically criminalise the creation, distribution, and possession of AI-generated explicit content. Ensure adequate penalties for offenders and provisions for cross-border cooperation.
Proactive measures to combat AI-driven sextortion
Prevention and Awareness: Proactive measures raise awareness about AI sextortion, helping individuals recognise risks and take precautions.
Early Detection and Reporting: Proactive measures employ advanced detection tools to identify AI-generated deepfake content early, enabling prompt intervention and support for victims.
Legal Frameworks and Regulations: Proactive measures strengthen legal frameworks to criminalise AI sextortion, facilitate cross-border cooperation, and impose offender penalties.
Technological Solutions: Proactive measures focus on developing tools and algorithms to detect and remove AI-generated explicit content, making it harder for perpetrators to carry out their schemes.
International Cooperation: Proactive measures foster collaboration among law enforcement agencies, governments, and technology companies to combat AI sextortion globally.
Support for Victims: Proactive measures provide comprehensive support services, including counselling and legal assistance, to help victims recover from emotional and psychological trauma.
Implementing these proactive measures will help create a safer digital environment for all.
Misuse of Technology
Misusing technology, particularly AI-driven deepfake technology, in the context of sextortion raises serious concerns.
Exploitation of Personal Data: Perpetrators exploit personal data and images available online, such as social media posts or captured video chats, to create AI- manipulation violates privacy rights and exploits the vulnerability of individuals who trust that their personal information will be used responsibly.
Facilitation of Extortion: AI sextortion often involves perpetrators demanding monetary payments, sexually themed images or videos, or other favours under the threat of releasing manipulated content to the public or to the victims’ friends and family. The realistic nature of deepfake technology increases the effectiveness of these extortion attempts, placing victims under significant emotional and financial pressure.
Amplification of Harm: Perpetrators use deepfake technology to create explicit videos or images that appear realistic, thereby increasing the potential for humiliation, harassment, and psychological trauma suffered by victims. The wide distribution of such content on social media platforms and pornographic websites can perpetuate victimisation and cause lasting damage to their reputation and well-being.
Targeting teenagers– Targeting teenagers and extortion demands in AI sextortion cases is a particularly alarming aspect of this issue. Teenagers are particularly vulnerable to AI sextortion due to their increased use of social media platforms for sharing personal information and images. Perpetrators exploit to manipulate and coerce them.
Erosion of Trust: Misusing AI-driven deepfake technology erodes trust in digital media and online interactions. As deepfake content becomes more convincing, it becomes increasingly challenging to distinguish between real and manipulated videos or images.
Proliferation of Pornographic Content: The misuse of AI technology in sextortion contributes to the proliferation of non-consensual pornography (also known as “revenge porn”) and the availability of explicit content featuring unsuspecting individuals. This perpetuates a culture of objectification, exploitation, and non-consensual sharing of intimate material.
Conclusion
Addressing the concern of AI sextortion requires a multi-faceted approach, including technological advancements in detection and prevention, legal frameworks to hold offenders accountable, awareness about the risks, and collaboration between technology companies, law enforcement agencies, and advocacy groups to combat this emerging threat and protect the well-being of individuals online.

Introduction
In an alarming event, one of India’s premier healthcare institutes, AIIMS Delhi, has fallen victim to a malicious cyberattack for the second time in the year. The Incident serves as a clear-cut reminder of the escalating threat landscape faced by the healthcare organisation in this digital age. In the attack, which unfolded with grave implications, the attackers not only explored the vulnerabilities present in the healthcare sector, but this also raised the concern about the security of patient data and the uninterrupted delivery of critical healthcare services. In this blog post, we will explore the incident, what happened, and what safety measures can be taken.
Backdrop
The cyber-security systems deployed in AIIMS, New Delhi, recently detected a malware attack. The nature and scope of the attack were both sophisticated and targeted. This second hack acts as a wake-up call for healthcare organisations nationwide. As the healthcare business increasingly depends on digital technology to improve patient care and operational efficiency, cybersecurity must be prioritised to protect sensitive data. To minimise cyber-attack dangers, healthcare organisations must invest in robust defences such as multi-factor authentication, network security, frequent system upgrades, and employee training.
The attempt was successfully prevented, and the deployed cyber-security systems neutralised the threat. The e-Hospital services remain to be fully secure and are functioning normally.
Impact on AIIMS
Healthcare services have been under hackers’ radar worldwide, and the healthcare sector has been impacted badly. The attack on AIIMS Delhi’s effects has been both immediate and far-reaching. The organisation, which is recognised for delivering excellent healthcare services and performing breakthrough medical research, faced significant interruptions in its everyday operations. Patient care and treatment processes were considerably impeded, resulting in delays, cancellations, and the inability to access essential medical documents. The stolen data raises serious concerns about patient privacy and confidentiality, raising doubts about the institution’s capacity to protect sensitive information. Furthermore, the financial ramifications of the assault, such as the cost of recovery, deploying more robust cybersecurity measures, and potential legal penalties and forensic analyses, contribute to the scale of the effect. The event has also generated public concerns about the institution’s ability to preserve personal information, undermining confidence and degrading AIIMS Delhi’s image.
Impact on Patients: The attacks not only impact the institutes but also have serious implications for the patients and here are some key highlights:
Healthcare Service Disruption: The hack has affected the seamless delivery of healthcare services at AIIMS Delhi. Appointments, surgeries, and other medical treatments may be delayed, cancelled, or rescheduled. This disturbance can result in longer wait times, longer treatment periods, and potential problems from delayed or interrupted therapy.

Patient Privacy and Confidentiality are jeopardised because of the breach of sensitive patient data. Medical data, test findings, and treatment plans may have been compromised. This breach may diminish patient faith in the institution’s capacity to safeguard their personal information, discouraging them from seeking care or submitting sensitive information in the future.
As a result of the cyberattack, patients may endure mental anguish and worry. Fear of possible exploitation of personal health information, confusion about the scope of the breach, and concerns about the security of their healthcare data can all have a negative impact on their mental health. This stress might aggravate pre-existing medical issues and impede total recovery.
Trust at stake: A data breach may harm patients’ faith and confidence in AIIMS Delhi and the healthcare system. Patients rely on healthcare facilities to keep their information secure and confidential while providing safe, high-quality care. A hack can doubt the institution’s ability to safeguard patient data, affecting patients’ overall faith in the organisation and potentially leading to patients seeking care elsewhere.
Cybersecurity Measures
To avoid future hacks and protect patient data, AIIMS Delhi must prioritize enhancing its cybersecurity procedures. The institution can strengthen its resistance to changing threats by establishing strong security practices. The following steps can be considered.
Using Multi-factor Authentication: By forcing users to submit several forms of identity to access systems and data, multi-factor authentication offers an extra layer of protection. AIIMS Delhi may considerably lower the danger of unauthorised access by applying this precaution, even in the case of leaked passwords or credentials. Biometrics and one-time passwords, for example, should be integrated into the institution’s authentication systems.
Improving Network Security and Firewalls: AIIMS Delhi should improve network security by implementing strong firewalls, intrusion detection and prevention systems, and network segmentation. These techniques serve to construct barriers between internal systems and external threats, reducing attackers’ lateral movement within the network. Regular network traffic monitoring and analysis can assist in recognising and mitigating any security breaches.
Risk Assessment: Regular penetration testing and vulnerability assessments are required to uncover possible flaws and vulnerabilities in AIIMS Delhi’s systems and infrastructure. Security professionals can detect vulnerabilities and offer remedial solutions by carrying out controlled simulated assaults. This proactive strategy assists in identifying and addressing any security flaws before attackers exploit them.
Educating and training Healthcare Professionals: Education and training have a crucial role in enhancing cybersecurity practices in healthcare facilities. Healthcare workers, including physicians, nurses, administrators, and support staff, must be well-informed about the importance of cybersecurity and trained in risk-mitigation best practices. This will empower healthcare professionals to actively contribute to protecting the patient’s data and maintaining the trust and confidence of patients.
Learnings from Incidents
AIIMS Delhi should embrace cyber-attacks as learning opportunities to strengthen its security posture. Following each event, a detailed post-incident study should be performed to identify areas for improvement, update security policies and procedures, and improve employee training programs. This iterative strategy contributes to the institution’s overall resilience and preparation for future cyber-attacks. AIIMS Delhi can effectively respond to cyber incidents, minimise the impact on operations, and protect patient data by establishing an effective incident response and recovery plan, implementing data backup and recovery mechanisms, conducting forensic analysis, and promoting open communication. Proactive measures, constant review, and regular revisions to incident response plans are critical for staying ahead of developing cyber threats and ensuring the institution’s resilience in the face of potential future assaults.

Conclusion
To summarise, developing robust healthcare systems in the digital era is a key challenge that healthcare organisations must prioritise. Healthcare organisations can secure patient data, assure the continuation of key services, and maintain patients’ trust and confidence by adopting comprehensive cybersecurity measures, building incident response plans, training healthcare personnel, and cultivating a security culture. Adopting a proactive and holistic strategy for cybersecurity is critical to developing a healthcare system capable of withstanding and successfully responding to digital-age problems.

Introduction
The two-day Apple’s Worldwide Developer Conference (WWDC) 2023, which was held on the 6th & 7th of June, has become an essential and highly anticipated part of our calendar as frequently as the trend. This year’s keynote announcements will include all of the usual enhancements for iOS, iPadOS, watchOS, macOS, and more. However, this year is also unique due to the unveiling of the Vision Pro headset, a brand-new Apple product.
In this blog, we will examine the exciting announcements made at Apple WWDC 2023, which was a ground-breaking event.
macOS Sonoma
macOS Sonoma, the new presentation of macOS disclosed at the WWDC full of exciting features. It comes with stunning video screensavers that show stunning scenes from all over the world. Gadgets can now be added genuinely to the work area and adjusted totally based on the client’s action. Also, it changes variety and blurring out of the spotlight while utilising applications. In addition, Death Stranding: Directors Cut for Mac announced that the Game Mode is added to make Macs more suitable for gaming. A presenter overlay enhances video presentations, and viewers can respond to them with interactive responses. Updated Safari is also included in the WebApp feature that turns frequently used websites into dedicated windows, a new Profile system for separating browsing history, and secure password sharing. Currently, the developer beta is available and the public beta will be available in July, and the final release is anticipated for the fall.
ios 16
Apple WWDC 2023 shows the following iOS, and iOS 16 replication, offering plenty of energising highlights for iPhone and iPad clients. Apple maintains its commitment to privacy with iOS 16, which introduces enhanced privacy settings that give users even more control over their data and online privacy. Users can also personalise their devices according to their preferences thanks to the new operating system’s refinement and customisable user interface.Improved multitasking capabilities like redesigned Files app and advanced note-taking features are just a few of the productivity enhancements included in the iOS 16. With iOS 16, Apple also improves its AR capabilities, allowing developers to develop even more immersive and interactive AR experiences.

WatchOS 9
Apple WWDC 2023 carried energising updates to the Apple Watch with the presentation of watchOS 9. The Apple Watch is an essential companion for sustaining a healthy lifestyle because the most recent version of the operating system includes cutting-edge health and fitness features. WatchOS 9 gives users unprecedented control over their health, offering personalised fitness recommendations and advanced sleep tracking.
Additionally, new watch faces were added, enhancing communication capabilities and improving app performance in watchOS 9, making the Apple Watch even easier to use daily.
ios 17
Rather than focusing on major features, Apple focused on quality-of-life enhancements when it announced iOS 17 at WWDC 2023. Live Voicemail with real-time transcripts of voicemails, personalised personal contact “posters,” and video voicemails for FaceTime are all part of the update. Search filters, a catch-up arrow, live location sharing, and a safety feature called Check-In are all available in Messages. AirDrop now supports NameDrop for transferring contact information; stickers have been expanded. The autocorrect and recording features on the keyboard have been improved for accuracy. Standby in the lock screen is an intelligent home display that shows the weather, upcoming appointments, and notifications. Siri works on Standby and adjusts itself for the night. The developer beta is currently available now, and a public beta will take place next month before the full release is in the fall.
Vision Pro VR Headset
Apple unveiled the Vision Pro AR headset, their first foray into virtual reality (VR), during the WWDC keynote. The Vision Pro is a virtual reality headset that competes with PlayStation VR2 and Meta Quest 3. This is in contrast to the long-awaited Apple smart glasses. Apple put a lot of effort into making a thin and light headset by using premium materials when needed. Voice, hand, and eye commands are all used to operate the Digital Crown-equipped device. The showcases offer extraordinary clarity, which is fueled by Apple’s M2 processor with a committed R1 chip. The Vision Pro combines virtual reality (VR) and augmented reality (AR), enabling users to interact with Apple apps and gain access to the company’s existing ecosystem. The expanded reality space created by the headset’s sensors and cameras allows users to place apps in real-world environments and adjust their level of concentration. Optic ID is a security and unlocking eye-tracking technology that is incorporated into the Vision Pro. It allows for a more immersive screen experience because it is compatible with Apple accessories like Magic Keyboard and Mac. At launch, the Vision Pro supports over a hundred Apple game galleries. Disney gave a hint that Apple and Disney might work together in the future by announcing support for the Vision Pro and making the Disney Plus app available immediately. The show highlighted the headset’s lightweight plan and recommended Apple clients wear it for extended periods. However, widespread adoption may be difficult due to the high price of $3,499 (₹289,093.01 approx). Apple is expected to release the Vision Pro for public use in 2024.

15-inch MacBook Air
At the WWDC event, Apple revealed a new MacBook Air with a larger 15-inch model instead of the standard 13-inch model. The 15-inch MacBook Air features a powerful Apple M2 processor, a thin, light, and long-lasting design, and a stunning 15.3-inch Retina display. It comes in four colours and has a headphone jack, two USB-C ports, and MagSafe charging. The display has six spatial speakers, a 1080p webcam, and 500 nits of brightness. Apple claims a battery life of up to 18 hours.
Conclusion
At Apple’s 2023 WWDC, the company demonstrated its commitment to developing technology that is user-friendly and accessible to all. Apple’s commitment to improving the user experience across all of its products is demonstrated in the updates to operating systems, improvements of Siri, breakthroughs in augmented reality, and enhancements to health and fitness.By making complex innovations more like-minded and easy to understand, Apple is enabling people to use the maximum capacity of their gadgets. Apple’s innovations at WWDC 2023 are expected to shape the future of technology, simplifying everyday tasks and revolutionising how we interact with the digital world.As we push ahead, it is exciting to guess what these advancements will proceed to develop and decidedly mean for our lives. The future holds even more incredible possibilities for all of us because of Apple’s focus on privacy, user-centric design, and pushing the boundaries of innovation. Thus, prepare to embrace a future where innovation flawlessly incorporates into our lives because of the endeavours displayed at Apple WWDC 2023.

Introduction
In recent years, India has witnessed a significant rise in the popularity and recognition of esports, which refers to online gaming. Esports has emerged as a mainstream phenomenon, influencing players and youngsters worldwide. In India, with the penetration of the internet at 52%, the youth has got its attracted to Esports. In this blog post, we will look at how the government is booting the players, establishing professional leagues, and supporting gaming companies and sponsors in the best possible manner. As the ecosystem continues to rise in prominence and establish itself as a mainstream sporting phenomenon in India.
Factors Shaping Esports in India: A few factors are shaping and growing the love for esports in India here. Let’s have a look.
Technological Advances: The availability and affordability of high-speed internet connections and smart gaming equipment have played an important part in making esports more accessible to a broader audience in India. With the development of smartphones and low-cost gaming PCs, many people may now easily participate in and watch esports tournaments.
Youth Demographic: India has a large population of young people who are enthusiastic gamers and tech-savvy. The youth demographic’s enthusiasm for gaming has spurred the expansion of esports in the country, as they actively participate in competitive gaming and watch major esports competitions.
Increase in the Gaming community: Gaming has been deeply established in Indian society, with many people using it for enjoyment and social contact. As the competitive component of gaming, esports has naturally gained popularity among gamers looking for a more competitive and immersive experience.
Esports Infrastructure and Events: The creation of specialised esports infrastructure, such as esports arenas, gaming cafés, and tournament venues, has considerably aided esports growth in India. Major national and international esports competitions and leagues have also been staged in India, offering exposure and possibilities for prospective esports players. Also supports various platforms such as YouTube, Twitch, and Facebook gaming, which has played a vital role in showcasing and popularising Esports in India.
Government support: Corporate and government sectors in India have recognised the potential of esports and are actively supporting its growth. Major corporate investments, sponsorships, and collaborations with esports organisations have supplied the financial backing and resources required for the country’s esports development. Government attempts to promote esports have also been initiated, such as forming esports governing organisations and including esports in official sporting events.
Growing Popularity and Recognition: Esports in India has witnessed a significant surge in viewership and fanbase, all thanks to online streaming platforms such as Twitch, YouTube which have provided a convenient way for fans to watch live esports events at home and at high-definition quality social media platforms let the fans to interact with their favourite players and stay updated on the latest esports news and events.

Esports Leagues in India
The organisation of esports tournaments and leagues in India has increased, with the IGL being one of the largest and most popular. The ESL India Premiership is a major esports event the Electronic Sports League organised in collaboration with NODWIN Gaming. Viacom18, a well-known Indian media business, established UCypher, an esports league. It focuses on a range of gaming games such as CS: GO, Dota 2, and Tekken in order to promote esports as a professional sport in India. All of these platforms provide professional players with a venue to compete and establish their profile in the esports industry.
India’s Performance in Esports to Date
Indian esports players have achieved remarkable global success, including outstanding results in prominent events and leagues. Individual Indian esports players’ success stories illustrate their talent, determination, and India’s ability to flourish in the esports sphere. These accomplishments contribute to the worldwide esports landscape’s awareness and growth of Indian esports. To add the name of the players and their success stories that have bought pride to India, they are Tirth Metha, Known as “Ritr”, a CS:GO player, Abhijeet “Ghatak”, Ankit “V3nom”, Saloni “Meow16K”.Apart from this Indian women’s team has also done exceptionally well in CS:GO and has made it to the finale.
Government and Corporate Sectors support: The Indian esports business has received backing from the government and corporate sectors, contributing to its growth and acceptance as a genuine sport.
Government Initiatives: The Indian government has expressed increased support for esports through different initiatives. This involves recognising esports as an official sport, establishing esports regulating organisations, and incorporating esports into national sports federations. The government has also announced steps to give financial assistance, subsidies, and infrastructure development for esports, therefore providing a favourable environment for the industry’s growth. Recently, Kalyan Chaubey, joint secretary and acting CEO of the IOA, personally gave the athletes cutting-edge training gear during this occasion, providing kits to the players. The kit includes the following:
Advanced gaming mouse.
Keyboard built for quick responses.
A smooth mousepad
A headphone for crystal-clear communication
An eSports bag to carry the equipment.
Corporate Sponsorship and Partnerships
Indian corporations have recognised esports’ promise and actively sponsored and collaborated with esports organisations, tournaments, and individual players. Companies from various industries, including technology, telecommunications, and entertainment, have invested in esports to capitalise on its success and connect with the esports community. These sponsorships and collaborations give financial support, resources, and visibility to esports in India. The leagues and championships provide opportunities for young players to showcase their talent.
Challenges and future
While esports provides great job opportunities, several obstacles must be overcome in order for the industry to expand and gain recognition:
Infrastructure & Training Facilities: Ensuring the availability of high-quality training facilities and infrastructure is critical for developing talent and allowing players to realise their maximum potential. Continued investment in esports venues, training facilities, and academies is critical for the industry’s long-term success.
Fostering a culture of skill development and giving outlets for formal education in esports would improve the professionalism and competitiveness of Indian esports players. Collaborations between educational institutions and esports organisations can result in the development of specialised programs in areas such as game analysis, team management, and sports psychology.
Establishing a thorough legal framework and governance structure for esports will help it gain legitimacy as a professional sport. Clear standards on player contracts, player rights, anti-doping procedures, and fair competition policies are all part of this.
Conclusion
Esports in India provide massive professional opportunities and growth possibilities for aspiring esports athletes. The sector’s prospects are based on overcoming infrastructure, perception, talent development, and regulatory barriers. Esports may establish itself as a viable and acceptable career alternative in India with continued support, investment, and stakeholder collaboration

BharOS’s successful testing grabbed massive online attention after Ashwini Vaishnaw, Minister of Communications and Electronics & IT, and Union Education Minister Dharmendra Pradhan unveiled the new mobile operating system. On Data Privacy Day, January 28, it’s appropriate to discuss the safety factors.
The OS is developed by JandKops, which has been incubated by IIT Madras Pravartak Technologies Foundation. It is claimed that BharOS will ensure the prevention of the “execution of any malware” and “execution of any malicious application”.
Even though it is called a Made in India OS, there are many people who disagree with this. It is because the OS is based on an AOSP (Android Open Source Project). It includes similar methodologies, functionalities, and basics used in Google Android.
Global safety factor
Security and data safety has been worldwide issue. A few years ago, Alphabet CEO Sundar Pichai also testified in front of US Congress while facing questions related to privacy, data collection, and location tracking.
While experts say that Android’s app ecosystem is a privacy and security disaster, a study that examined 82,501 apps pre-installed on 1,742 Android smartphones sold by 214 vendors concluded that users are woefully unaware of the significant security and privacy risks posed by pre-installed applications.
Even Apple, which takes cybersafety issues as a top priority, sometimes finds itself in a vulnerable situation. For example, last year Apple users were advised to update their devices to protect against a pair of security flaws that could allow attackers to take complete control.
It was said that one of the software flaws affected the kernel, the deepest layer of the OS shared by all Apple devices, while the other had an impact on WebKit, the technology that powers the Safari web browser.
Security researchers, including NordVPN, said that Apple’s closed development OS makes it more difficult for hackers to develop exploits, while Android raises the threat level since anyone can see its source code to develop exploits.
BharOS is not like iOS but it is kind of similar to Android and based on AOSP. So the question is, how safe would this OS be?
‘Security blanket’
Sandip Kumar Panda, Co-founder and CEO of InstaSafe, told News18: “BharOS acts as a security blanket for devices. The framework is designed in a manner that it prevents the execution of any malicious app and verifies each app on the devices before making it live on the BharOS platform.”
There are no apps without any vulnerabilities, he said. “As the app development progresses, vulnerabilities get introduced either in the form of insecure coding practices or third-party software vulnerabilities integrated with the platform. Since several Android vulnerabilities were discovered over the years, all those bugs would have been fixed now and updates would already have been for AOSP, which will be much more mature now,” he added.
Vineet Kumar, Founder and President of CyberPeace Foundation, believes that “the use of AOSP as the foundation for BharOS is a positive step” as it is a robust platform.
But according to him, it is important to note that no OS can be completely immune to all forms of cyber threats. “The key to staying safe online is to stay vigilant, use security software, keep your software updated, and be mindful of the apps you install and the websites you visit,” he said,
Furthermore, the expert stated that it is possible to make an OS more secure by implementing a variety of security features and technologies such as sandboxing, whitelisting, and application control, as well as rigorous testing and code review processes.
Kumar said: “It would be important for an independent, reputable security firm to evaluate BharOS and test its security features before it can be stated with certainty that it is more secure than other OSs.”
It is difficult to say whether the BharOS will be free of cybersecurity issues without more information about the specific features and security measures that have been implemented, he noted while adding that this OS has to go through a rigorous testing and certification process.
“It will be important to see how it measures up against established security standards and how well it can withstand real-world attacks,” the expert stated.
Reference Link : https://www.news18.com/amp/news/tech/data-privacy-day-how-safe-is-bharos-what-do-cybersecurity-experts-say-you-are-about-to-find-out-6932521.html

Introduction
The world has been surfing the wave of technological advancements and innovations for the past decade, and it all pins down to one device – our mobile phone. For all mobile users, the primary choices of operating systems are Android and iOS. Android is an OS created by google in 2008 and is supported by most brands like – One+, Mi, OPPO, VIVO, Motorola, and many more and is one of the most used operating systems. iOS is an OS that was developed by Apple and was introduced in their first phone – The iPhone, in 2007. Both OS came into existence when mobile phone penetration was slow globally, and so the scope of expansion and advancements was always in favor of such operating systems.
The Evolution
iOS
Ever since the advent of the iPhone, iOS has seen many changes since 2007. The current version of iOs is iOS 16. However, in the course of creating new iOS and updating the old ones, Apple has come out with various advancements like the App Store, Touch ID & Face ID, Apple Music, Podcasts, Augmented reality, Contact exposure, and many more, which have later become part of features of Android phone as well. Apple is one of the oldest tech and gadget developers in the world, most of the devices manufactured by Apple have received global recognition, and hence Apple enjoys providing services to a huge global user base.
Android
The OS has been famous for using the software version names on the food items like – Pie, Oreo, Nougat, KitKat, Eclairs, etc. From Android 10 onwards, the new versions were demoted by number. The most recent Android OS is Android 13; this OS is known for its practicality and flexibility. In 2012 Android became the most popular operating system for mobile devices, surpassing Apple’s iOS, and as of 2020, about 75 percent of mobile devices run Android.
Android vs. iOS
1. USER INTERFACE
One of the most noticeable differences between Android and iPhone is their user interface. Android devices have a more customizable interface, with options to change the home screen, app icons, and overall theme. The iPhone, on the other hand, has a more uniform interface with less room for customization. Android allows users to customize their home screen by adding widgets and changing the layout of their app icons. This can be useful for people who want quick access to certain functions or information on their home screen. IOS does not have this feature, but it does allow users to organize their app icons into folders for easier navigation.
2. APP SELECTION
Another factor to consider when choosing between Android and iOS is the app selection. Both platforms have a wide range of apps available, but there are some differences to consider. Android has a larger selection of apps overall, including a larger selection of free apps. However, some popular apps, such as certain music streaming apps and games, may be released first or only available on iPhone. iOS also has a more curated app store, meaning that all apps must go through a review process before being accepted for download. This can result in a higher quality of apps overall, but it can also mean that it takes longer for new apps to become available on the platform. iPhone devices tend to have less processing power and RAM. But they are generally more efficient in their use of resources. This can result in longer battery life, but it may also mean that iPhones are slower at handling multiple tasks or running resource-intensive apps.
3. PERFORMANCE
When it comes to performance, both Android and iPhone have their own strengths and weaknesses. Android devices tend to have more processing power and RAM. This can make them faster and more capable of handling multiple tasks simultaneously. However, this can also lead to Android devices having shorter battery life compared to iPhones.
4. SECURITY
Security is an important consideration for any smartphone user, and Android and iPhone have their own measures to protect user data. Android devices are generally seen as being less secure than iPhones due to their open nature. Android allows users to install apps from sources other than the Google Play Store, which can increase the risk of downloading malicious apps. However, Android has made improvements in recent years to address this issue. Including the introduction of Google Play Protect, which scans apps for malware before they are downloaded. On the other hand, iPhone devices have a more closed ecosystem, with all apps required to go through Apple‘s review process before being available for download. This helps reduce the risk of downloading malicious apps, but it can also limit the platform’s flexibility.
Conclusion
The debate about the better OS has been going on for some time now, and it looks like it will get more comprehensive in the times to come, as netizens go deeper into cyberspace, they will get more aware and critical of their uses and demands, which will allow them to opt for the best OS for their convenience. Although the Andriod OS, due to its integration, stands more vulnerable to security threats as compared to iOS, no software is secure in today’s time, what is secure is its use and application hence the netizen and the platforms need to increase their awareness and knowledge to safeguard themselves and the wholesome cyberspace.

Introduction
Established in the US, one of the world’s largest cab networks came into existence in 2010 and, since its inception, has expanded all over the globe with operations in 10,000 cities across 71 countries. It made a remarkable start in India in 2017 and, since then, has seen a rise in the customers and drivers for the company. India is among the largest markets for Uber, with 600,000 monthly drivers and 8.5 million monthly riders.
GeM
Government e-Marketplace (GeM) is a one-stop portal to facilitate online procurement of common-use Goods & Services required by various Government Departments / Organizations / PSUs. GeM aims to enhance transparency, efficiency and speed in public procurement. It provides the tools of e-bidding, reverses e-auction and demand aggregation to facilitate government users achieve the best value for their money. Government e-Marketplace owes its genesis to the recommendations of two Groups of Secretaries to the Prime Minister in January 2016. They recommended setting up a dedicated e-market for different goods & services procured or sold by Government/PSUs besides reforming DGS&D. Subsequently, the Finance Minister, in his Budget speech for FY 2016-17, announced setting up of a technology-driven platform to facilitate procurement of goods and services by various Ministries and agencies of the Government. The portal was launched on 9th August 2016 by the Commerce & Industry Minister.
Uber-GeM collaboration
The cab network giant has registered on the portal of the Government E-marketplace and has declared that it will offer its services to Government officials from Ministries and PSUs. The project is currently in its pilot phase and shall be executed systematically to cover all the ministries and PSUs in the nation. The officials can book cabs at a fixed price with no cancellation or surge fees on the rides. The authorised officials will be able to book a cab from the portal and select from the list of drivers available. It will be a cashless/cardless ride for the officials; additional vehicle categories for government riders have been added, namely, GeM Yatraa Hatch and GeM Yatraa Sedan, and there will be hourly rentals for multiple-stops, allowing the government officials to enjoy the flexible and easily accessible network of cabs in major cities.
Advantages
Such collaboration between Government institutions and corporates will go a long way to secure a stable equilibrium in the market. Uber, a US-based company, enjoys a vast user base in India and has created new job avenues. The advantages of the collaboration between GeM and Uber are as follows-
Easy accessibility
This will undoubtedly provide ease in accessibility in terms of being in a new place, and language barriers will no longer exist with such options for Government officials.
Increased jobs for drivers
With more cabs being engaged with ministries and PSUs, it is pertinent that the requirement for drivers will grow, thus increasing the employability rate in India and allowing the user to have an uninterrupted experience.
Ease of travel and commuting
This move will provide flexibility, thus leading to more ease in travel in cases of emergencies or places inaccessible by trains or other modes of transport.
Rise in travel and tourism
Coupled with the other factors, the opportunities for the users to visit different places will be an added advantage which will help boost the tourism industry, thus creating a balance in the market.
Sustainable Government corporate relationship

Such collaborations between the government and corporates will be substantial, signifying the ease of doing business in India. They will also act as a beacon of example for compliance with opportunities for the other companies and stakeholders.
Opportunities for collaboration with ingenious start-ups
With such major corporate joining hands with the government, the indigenous start-ups will have various opportunities to engage with companies and recreate similar businesses rooted in India, thus transforming the economy.
Conclusion
Transportation and communication play a vital role in our lives, thus, such collaboration will go a long way in creating a better and more uniform user experience in the country. This also goes a long way to showcase that the Governmental platforms also offer services of a global standard. Such portals exist in South Korea, Singapore, the US and Europe. The network of cabs can only be sustained using the locals as drivers, hence these collaborations are win-win for all as the market dynamics are improving, employability will increase, and improved user experience will be seen.

THREE CENTRES OF EXCELLENCE IN ARTIFICIAL INTELLIGENCE:
India’s Finance Minister, Mrs. Nirmala Sitharaman, with a vision of ‘Make AI for India’ and ‘Make AI work for India, ’ announced during the presentation of Union Budget 2023 that the Indian Government is planning to set up three ‘Centre of Excellence’ for Artificial Intelligence in top Educational Institutions to revolutionise fields such as health, agriculture, etc.
Under the ‘Amirt Kaal,’ i.e., the budget of 2023 is a stepping stone by the government to have a technology-driven knowledge-based economy and the seven priorities that have been set up by the government called ‘Saptarishi’ such as inclusive development, reaching the last mile, infrastructure investment, unleashing potential, green growth, youth power, and financial sector will guide the nation in this endeavor along with leading industry players that will partner in conducting interdisciplinary research, developing cutting edge applications and scalable problem solutions in such areas.
The government has already formed the roadmap for AI in the nation through MeitY, NASSCOM, and DRDO, indicating that the government has already started this AI revolution. For AI-related research and development, the Centre for Artificial Intelligence and Robotics (CAIR) has already been formed, and biometric identification, facial recognition, criminal investigation, crowd and traffic management, agriculture, healthcare, education, and other applications of AI are currently being used.
Even a task force on artificial intelligence (AI) was established on August 24, 2017. The government had promised to set up Centers of Excellence (CoEs) for research, education, and skill development in robotics, artificial intelligence (AI), digital manufacturing, big data analytics, quantum communication, and the Internet of Things (IoT) and by announcing the same in the current Union budget has planned to fulfill the same.
The government has also announced the development of 100 labs in engineering institutions for developing applications using 5G services that will collaborate with various authorities, regulators, banks, and other businesses.
Developing such labs aims to create new business models and employment opportunities. Among others, it will also create smart classrooms, precision farming, intelligent transport systems, and healthcare applications, as well as new pedagogy, curriculum, continual professional development dipstick survey, and ICT implementation will be introduced for training the teachers.
POSSIBLE ROLES OF AI:
The use of AI in top educational institutions will help students to learn at their own pace, using AI algorithms providing customised feedback and recommendations based on their performance, as it can also help students identify their strengths and weaknesses, allowing them to focus their study efforts more effectively and efficiently and will help train students in AI and make the country future-ready.
The main area of AI in healthcare, agriculture, and sustainable cities would be researching and developing practical AI applications in these sectors. In healthcare, AI can be effective by helping medical professionals diagnose diseases faster and more accurately by analysing medical images and patient data. It can also be used to identify the most effective treatments for specific patients based on their genetic and medical history.
Artificial Intelligence (AI) has the potential to revolutionise the agriculture industry by improving yields, reducing costs, and increasing efficiency. AI algorithms can collect and analyse data on soil moisture, crop health, and weather patterns to optimise crop management practices, improve yields and the health and well-being of livestock, predict potential health issues, and increase productivity. These algorithms can identify and target weeds and pests, reducing the need for harmful chemicals and increasing sustainability.
ROLE OF AI IN CYBERSPACE:
Artificial Intelligence (AI) plays a crucial role in cyberspace. AI technology can enhance security in cyberspace, prevent cyber-attacks, detect and respond to security threats, and improve overall cybersecurity. Some of the specific applications of AI in cyberspace include:
- Intrusion Detection: AI-powered systems can analyse large amounts of data and detect signs of potential cyber-attacks.
- Threat Analysis: AI algorithms can help identify patterns of behaviour that may indicate a potential threat and then take appropriate action.
- Fraud Detection: AI can identify and prevent fraudulent activities, such as identity theft and phishing, by analysing large amounts of data and detecting unusual behaviour patterns.
- Network Security: AI can monitor and secure networks against potential cyber-attacks by detecting and blocking malicious traffic.
- Data Security: AI can be used to protect sensitive data and ensure that it is only accessible to authorised personnel.
CONCLUSION:
Introducing AI in top educational institutions and partnering it with leading industries will prove to be a stepping stone to revolutionise the development of the country, as Artificial Intelligence (AI) has the potential to play a significant role in the development of a country by improving various sectors and addressing societal challenges. Overall, we hope to see an increase in efficiency and productivity across various industries, leading to increased economic growth and job creation, improved delivery of healthcare services by increasing access to care and, improving patient outcomes, making education more accessible and effective as AI has the potential to improve various sectors of a country and contribute to its overall development and progress. However, it’s important to ensure that AI is developed and used ethically, considering its potential consequences and impact on society.
References:

Introduction
It’s a proud moment for Indians that India will host the G- 20 administration, which will bring the world’s 20 largest profitable nations together on a single platform during the post-economic recovery and the Russia- Ukraine conflict, which has increased geopolitical pressures among nations over the last many times and made the G- 20 a precedence of nations. With this administration, India has to make cybersecurity precedence, as the security and integrity of the critical structure and digital platforms are top precedence in 2023. The necessity for a secure cyberspace is pivotal given the exponential increase in the volume and kind of cyber-attacks, particularly to crucial structures the most recent illustration is the ongoing interruption at New Delhi’s All India Institute of Medical lores caused by a ransomware assault. It has been observed that the mode of attacks are more sophisticated and targets communication structure, critical structure, transport systems, and especially the information technology sector and fiscal system.
The structure that enables the delivery of government services to be more effective. As a result,cyber-secured critical structures and digital public forums are necessary for public security, bettered governance, and, most importantly, maintaining people’s trust. The G20 can be enhanced and contribute towards securing digital public platforms and the integrity of the critical structure. This time, in 2023, digital security is the top precedence.
G20 cybersecurity enterprises and politic sweat
The emphasis on cybersecurity was maintained throughout the Italian and Indonesian regulations in 2021 and 2022, independently, by emphasizing the significance of cyberspace during Digital Economy Working Group addresses. Specifically, under the Indonesian Presidency, the prominent cybersecurity focus was clear in the recent Bali Leaders’ protestation, which noted, among other effects, the significance of fighting misinformation juggernauts and cyber attacks, as well as guaranteeing connectivity structure security. The cyber incident report by the Financial Stability Board on carrying further uniformity in cyber incident reporting In 2016, a G20 digital task force was created under the Chinese administration to understand digital technology issues. Under the Saudi administration, the cybersecurity gap at the G20 was bridged by addressing the issues of MSMs. India has also refocused on the significance of creating secure, secure, and stronger-friendly digital platforms.
G20- India’s digital invention alliance( G-20-DIA) a cyber-secure Bharat
- Under India’s administration, the G20’s Digital Economy Working Group is led by the Ministry of Electronics and Information Technology( MeitY, DEWG).
- The Ministry concentrated on three major areas during India’s G20 administration digital skill development, digital public structure, and cyber security.
- The EWG’s DIA and Stay Safe Online enterprise further the ideal of lesser digital metamorphosis by guaranteeing a safe and creative cyber terrain. They want to offer a smooth and secure delivery of public services.

The G20 Digital Innovation Alliance
(G20- DIA) strives to find, admit, and encourage the relinquishment of innovative and poignant digital technologies produced by invited G20 startups and-member governments.
- These technologies must meet humanity’s conditions in six crucial areas husbandry, health, education, finance, secure digital structure, and indirect frugality.
- The inventions created around these motifs will be supported by the Digital Public Goods structure, allowing them to be espoused encyclopedically, closing the digital gap and icing sustainable and indifferent growth.
- The G20 Digital Innovation Alliance( G20- DIA) conference will be held on the perimeters of the Digital Economy Working Group( DEWG) meeting in Bengaluru.
- Top-nominated entrepreneurs from each order will present their ideas to a worldwide community of investors, instructors, pots, and other stakeholders at this event.
India’s” Stay Safe Online crusade”
The” Stay Safe Online” crusade attempts to raise mindfulness about the significance of remaining safe in the online world amid our adding reliance on it. With the fast expansion of the technical terrain and the growing number of internet druggies in India, new difficulties are arising. The Stay Safe Online crusade aims to educate individuals about cyber pitfalls and how to avoid them. The time-long crusade will target children, women, scholars, and aged citizens, as well as individuals with disabilities, preceptors, and government officers in particular. It’ll be done in Hindi, English, and indigenous languages to reach a larger followership. It’ll distribute mindfulness information in infographics, short pictures, cartoon stories, and so on through extensively employed social media platforms and other channels. The primary stakeholders will be government agencies, civil societies, and NGOs.
Conclusion
To wind up, it can be said that cyber security has become the most essential part of transnational affairs. As India hosts the G20 administration in 2023, the docket relating to cybersecurity gains a global stage, where cyber-related issues are addressed and honored encyclopedically, and nations can combat these issues; also, India aims to raise cyber mindfulness among its citizens.

Introduction
The year, 2022 has been a year of transition and change for the gaming industry. This year esports and gaming including the industry’s greater increased acceptance by the sports authorities and higher prize pools for top players, has been more commercial than ever, according to research by the year 2025 the industry will witness growth by 5 million dollars and around 420 million active gamers from India. Since, India is on the way to become world’s largest gaming market, with revenue earned in 2021 increasing by up to 28%, or 1.2 billion dollars, and predicted to reach 2 billion dollars by 2024 as a result of the COVID-19 expanding internet access throughout the country.
After a lengthy debate, the government has finally decided to bring online gaming under the purview of the law. The President of India has changed the rules governing e-sports and requested that the Sports Ministry and the Ministry of Electronics and Information Technology (MeitY) include e-sports in multi-sport competitions. India’s gaming sector has reached new heights this year, with the country winning its first bronze medal in the first esports event organized by this year’s Commonwealth Games, and this is only the beginning.
Indian government takes on E-sports
The Indian government has given esports a huge boost. It has been introduced into the traditional sports disciplines of the nation. Droupadi Murmu, the President of India, changed the regulations governing eSports using the authority “conferred by clause (3) of Article 77 of the Constitution,” and requested that “e-Sports be included as part of multi-sports events” from the Ministries of Electronics and Information Technology and Sports. Some crucial points will clarify the government’s position on e-sports.
- E-sports were added as a demonstration sport to the 2018 Asian Games in Jakarta, which meant that medals earned in the sport were not counted in the official total of medals.
- There is a greater desire for Esports to be integrated with school curricula.
- E-Sports (Electronic Sports) have been acknowledged by the Indian government as a component of multi-sport tournaments.

Why is e-sports important?
The Indian Esports Industry has worked hard to distinguish Esports from the broader category of “Gaming.” Esports is a competitive sport in which esports athletes compete in specific video game genres in a virtual, electronic environment using their physical and mental prowess, according to the industry.
According to studies, as individuals have gotten more screen aware and online gaming has become a part of their life, internet gaming not only improves fine motor skills but also sharpens the mind. The industry has the most users and stakeholders, and it has become critical to governing it; consequently, legislation is required to regulate it.
The online regulation bill 2022
The Online Gaming (Regulations) Bill, 2022, was recently filed in the Lok Sabha to create an effective regulatory mechanism for the online gaming business to prevent fraud and misuse of things related to or incidental to it. There are 20 sections spread throughout three chapters. It intends to establish an Online Gaming Commission, the authority, mandate, and jurisdiction of which will be specified by the Bill. An online gaming server will be licensed, relinquished, revoked, or suspended by the Commission’s key highlights of the bill to make it more clear
- The Bill establishes a regulating agency, the Online Gaming Commission (“OGC”), comprised of five members chosen by the Central Government, each with at least one specialist in the fields of law, cyber technology, and law enforcement experience.
- The OGC will be able to oversee the functions of online gaming websites, issue periodic or special reports on Online Gaming issues, recommend appropriate measures to control and curb illegal Online Gaming, grant, suspend, and revoke licenses for online gaming websites, and set fees for license applications and renewals.
- Without a website and a non-transferable and non-assignable license, the Bill proposes to make online gambling illegal. Anyone operating an online gaming server or website without a license risks up to three years in prison and a fine. The permission will be good for a six-year term.
- The license intended to be given under the Bill may be terminated or canceled if the licensee violates any of the license’s requirements or any of Bill’s provisions. However, the Bill does not apply to anybody providing backend services in India, including hosting and maintenance for any international gaming website situated outside of India.
- The bill also mentions the Foreign Direct Investment and Technology Collaboration in Online Gaming

Few misses in the bill that can be addressed to make it stronger and a better version
- The law does not address Know Your Customer (KYC) requirements, customer complaint procedures, advertising and marketing restrictions, user data protection, responsible gaming guidelines, and other concerns.
- In the bill, there is no clear distinction between money involved in the game. This is a matter of concern and needs to be addressed so the money laundering aspect can be determined.
- The distinction between “games of chance” and “games of skill” is not addressed in the Bill. Furthermore, the Bill does not specify whether its prohibitions apply only to for-real-money games or to free games.
Conclusion
Despite the bill’s flaws, it has offered optimism to the burgeoning gaming sector, which desperately needs a robust regulatory and legal framework free of ambiguity, allowing players to play safely, and encouraging entrepreneurs to enter the field with safety and security. An improved regulatory framework will increase job prospects while also assisting the government. A transparent framework will also aid in the protection of the rights of actors and stakeholders.

Introduction
With the increasing reliance on digital technologies in the banking industry, cyber threats have become a significant concern. Cyberlaw plays a crucial role in safeguarding the banking sector from cybercrimes and ensuring the security and integrity of financial systems.
The banking industry has witnessed a rapid digital transformation, enabling convenient services and greater access to financial resources. However, this digitalisation also exposes the industry to cyber threats, necessitating the formulation and implementation of effective cyber law frameworks.
Recent Trends in the Banking Industry
Digital Transformation: The banking industry has embraced digital technologies, such as mobile banking, internet banking, and financial apps, to enhance customer experience and operational efficiency.
Open Banking: The concept of open banking has gained prominence, enabling data sharing between banks and third-party service providers, which introduces new cyber risks.

How Cyber Law Helps the Banking Sector
The banking sector and cyber crime share an unspoken synergy due to the mass digitisation of banking services. Thanks to QR codes, UPI and online banking payments, India is now home to 40% of global online banking transactions. Some critical aspects of the cyber law and banking sector are as follows:
Data Protection: Cyberlaw mandates banks to implement robust data protection measures, including encryption, access controls, and regular security audits, to safeguard customer data.
Incident Response and Reporting: Cyberlaw requires banks to establish incident response plans, promptly report cyber incidents to regulatory authorities, and cooperate in investigations.
Customer Protection: Cyberlaw enforces regulations related to online banking fraud, identity theft, and unauthorised transactions, ensuring that customers are protected from cybercrimes.
Legal Framework: Cyberlaw provides a legal foundation for digitalisation in the banking sector, assuring customers that regulations protect their digital transactions and data.
Cybersecurity Training and Awareness: Cyberlaw encourages banks to conduct regular training programs and create awareness among employees and customers about cyber threats, safe digital practices, and reporting procedures.

RBI Guidelines
The RBI, as India’s central banking institution, has issued comprehensive guidelines to enhance cyber resilience in the banking industry. These guidelines address various aspects, including:
Technology Risk Management
Cyber Security Framework
IT Governance
Cyber Crisis Management Plan
Incident Reporting and Response
Recent Trends in Banking Sector Frauds and the Role of Cyber Law
Phishing Attacks: Cyberlaw helps banks combat phishing attacks by imposing penalties on perpetrators and mandating preventive measures like two-factor authentication.
Insider Threats: Cyberlaw regulations emphasise the need for stringent access controls, employee background checks, and legal consequences for insiders involved in fraudulent activities.
Ransomware Attacks: Cyberlaw frameworks assist banks in dealing with ransomware attacks by enabling legal actions against hackers and promoting preventive measures, such as regular software updates and data backups.
Master Directions on Cyber Resilience and Digital Payment Security Controls for Payment System Operators (PSOs)
Draft of Master Directions on Cyber Resilience and Digital Payment Security Controls for Payment System Operators (PSOs) issued by the Reserve Bank of India (RBI). The directions provide guidelines and requirements for PSOs to improve the safety and security of their payment systems, with a focus on cyber resilience. These guidelines for PSOs include mobile payment service providers like Paytm or digital wallet payment platforms.
Here are the highlights-
The Directions aim to improve the safety and security of payment systems operated by PSOs by providing a framework for overall information security preparedness, with an emphasis on cyber resilience.
The Directions apply to all authorised non-bank PSOs.
PSOs must ensure adherence to these Directions by unregulated entities in their digital payments ecosystem, such as payment gateways, third-party service providers, vendors, and merchants.
The PSO’s Board of Directors is responsible for ensuring adequate oversight over information security risks, including cyber risk and cyber resilience. A sub-committee of the Board may be delegated with primary oversight responsibilities.
PSOs must formulate a Board-approved Information Security (IS) policy that covers roles and responsibilities, measures to identify and manage cyber security risks, training and awareness programs, and more.
PSOs should have a distinct Board-approved Cyber Crisis Management Plan (CCMP) to detect, contain, respond, and recover from cyber threats and attacks.
A senior-level executive, such as a Chief Information Security Officer (CISO), should be responsible for implementing the IS policy and the cyber resilience framework and assessing the overall information security posture of the PSO.
PSOs need to define Key Risk Indicators (KRIs) and Key Performance Indicators (KPIs) to identify potential risk events and assess the effectiveness of security controls. The sub-committee of the Board is responsible for monitoring these indicators.
PSOs should conduct a cyber risk assessment when launching new products, services, technologies, or significant changes to existing infrastructure or processes.
PSOs, including inventory management, identity and access management, network security, application security life cycle, security testing, vendor risk management, data security, patch and change management life cycle, incident response, business continuity planning, API security, employee awareness and training, and other security measures should implement various baseline information security measures and controls.
PSOs should ensure that payment transactions involving debit to accounts conducted electronically are permitted only through multi-factor authentication, except where explicitly permitted/relaxed.

Conclusion
The relationship between cyber law and the banking industry is crucial in ensuring a secure and trusted digital environment. Recent trends indicate that cyber threats are evolving and becoming more sophisticated. Compliance with cyber law provisions and adherence to guidelines such as those provided by the RBI is essential for banks to protect themselves and their customers from cybercrimes. By embracing robust cyber law frameworks, the banking industry can foster a resilient ecosystem that enables innovation while safeguarding the interests of all stakeholders or users.

Introduction
The insurance industry is a target for cybercriminals due to the sensitive nature of the information it holds. This makes it essential for insurance companies to have robust cybersecurity measures to protect their data and customers’ personal information.
Cyber fraud in India’s insurance industry is increasing. It is reported that the Indian insurance sector has witnessed a surge in cyber-attacks, with several instances of data breaches, identity thefts, and financial fraud being reported. These cybercrimes not only pose a significant threat to the financial stability of the insurance industry but also to the privacy and security of policyholders.
Cyber Frauds in the Insurance Industry
The insurance industry in India has been the target of increasing cyber fraud in recent years. With the growing digital transformation trend, insurance companies have become increasingly vulnerable to cyber-attacks. Cyber frauds in the insurance industry are initiated by hackers who use various techniques such as phishing, malware, ransomware, and social engineering to gain unauthorised access to policyholders’ personal data and sensitive information
Kinds of cyber frauds in the insurance industry
It is essential for insurers and policyholders alike to be aware of these kinds of cyber-attacks on insurance companies in today’s digital age. Staying educated about these threats can help prevent them from happening in the future.
Identity theft– One common type of cyber fraud that occurs in the insurance industry is identity theft. In this type of fraud, criminals steal personal information such as name, address, date of birth and social security numbers through phishing emails or fraudulent websites. They then use this information to open fraudulent policies or access existing ones.
Payment fraud- Another type of cyber fraud that is on the rise is payment fraud. In this type of fraud, hackers intercept electronic payments made by policyholders or agents using fake bank accounts or compromised payment gateways. The money is then siphoned into untraceable accounts, making it difficult for law enforcement agencies to identify and arrest the perpetrators.
Phishing attacks- Where the fraudsters posed as company officials and sent emails to policyholders requesting their account details. The unsuspecting customers fell for this scam and shared their sensitive information, which was then used to access their accounts and steal funds.
Hacking- Where hackers breach the company’s system to gain access to policyholder data. The hackers’ stoles personal records, including names, addresses, phone numbers, social security numbers, and financial information, which they later sell on the dark web.
Fake policies scam- Fraudsters create fake policies using stolen identities and collect premiums from innocent customers. The insurer then voided these policies due to fraudulent activity leaving those people without valid coverage when they needed it most. The victims suffer significant financial losses due to this scam.
Fake Insurance Websites- Discuss the creation of deceptive websites that imitate well-known insurance companies, where unsuspecting individuals provide their personal details, leading to identity theft or financial losses.

Prevention of Cyber Frauds in the Insurance Industry- Best practices to follow
Prevention is better than cure, which also holds true in the case of cyber fraud in the insurance industry. The industry must take proactive steps to prevent such frauds from occurring in the first place. One of the most effective ways to do so is by investing in cybersecurity measures that are specifically designed for the insurance sector.
Insurance companies must conduct regular employee training programs on cybersecurity best practices. This includes educating employees on how to identify and avoid phishing emails, create strong passwords, and recognise potential cyber threats. Companies should also establish a reporting mechanism for employees to report suspicious activity or incidents immediately.
Having proper access controls in place is also necessary. This means limiting access to sensitive data only to those employees who need it, implementing two-factor authentication, and regularly monitoring user activity logs. Regular audits can also provide an extra layer of protection against potential threats by identifying vulnerabilities that may have been overlooked during routine security checks.
Another essential step is encrypting all data transmitted between different systems and devices. Encryption scrambles data into unreadable codes that can only be deciphered using a decryption key, making it difficult for hackers to intercept or steal information in transit.
Legal Framework for Cyber Frauds in the Insurance Industry
The legal framework for cyber fraud in the insurance industry is critical to preventing such crimes. The Insurance Regulatory and Development Authority of India (IRDAI) has issued guidelines for insurers to establish a cybersecurity framework. The guidelines require insurers to conduct regular risk assessments, implement security measures, and ensure compliance with data privacy laws.
The Information Technology Act 2000, is another significant piece of legislation dealing with cyber fraud in India. The act defines offences such as unauthorised access to a computer system, hacking, and tampering with data. It also provides for stringent penalties and imprisonment for those found guilty of such offences.
The IRDAI’s guidelines provide insurers with a roadmap to establish robust cybersecurity measures to help prevent cyber fraud in the insurance industry. Stringent implementation of these guidelines will go a long way in safeguarding sensitive customer information from falling into the wrong hands.
Best Practices for Insurers and Policyholders
Insurers:
Implementing Strong Authentication: Encouraging the use of multi-factor authentication and secure login processes to safeguard customer accounts and prevent unauthorised access.
Regular Employee Training: Conduct cybersecurity awareness programs to educate employees about the latest threats and preventive measures.
Investing in Advanced Technologies: Utilizing robust cybersecurity tools and systems to promptly detect and mitigate potential cyber threats.
Policyholders:
Vigilance and Awareness: Policyholders must stay vigilant while sharing personal information online and verify the authenticity of insurance websites and communication channels.
Regular Updates and Patches: Advising individuals to keep their devices and software up to date to minimise vulnerabilities that cybercriminals can exploit.
Secure Online Practices: Encouraging the use of strong and unique passwords, avoiding sharing sensitive information on unsecured networks, and exercising caution when clicking on suspicious links or attachments.

Conclusion
As the Indian insurance industry embraces digitisation, the risk of cyber scams and data breaches becomes a significant concern. Insurers and policyholders must collaborate to ensure robust cybersecurity measures are in place to protect sensitive information and financial interests.
It is essential for insurance companies to invest in robust cybersecurity measures that can detect and prevent fraud attempts. Additionally, educating employees on the dangers of cyber fraud and implementing strict compliance measures can go a long way in mitigating risks. With these efforts, the insurance industry can continue to provide trustworthy and reliable services to its customers while protecting against cyber threats. As technology continues to evolve, it is imperative that the insurance industry adapts accordingly and remains vigilant against emerging threats.

Introduction
The European Union has fined the meta $ 1.3 billion for infringing the EU privacy laws by transferring the personal data of Facebook users to the United States. The EU fined Meta’s business in Ireland. As per the European Union, transferring Personal data to the US is a breach of the General data protection Regulation or European Union law on data protection and privacy.
GDPR Compliance
The terms of GDPR promise to gather users’ personal information legally and under strict conditions. And those who collect and manage personal data must protect users’ personal data from exploitation. The GDPR restricts an organisation’s capacity to transfer personal data outside the EU if the transfer is solely based on that body’s evaluation of the sufficiency of the personal data’s protection. Transfers should only be made where European authorities have determined that a third country, a territory within that third country, or an international organisation provides acceptable protection for data protection.
Violation by Meta
The punishment, announced by Ireland’s Data Protection Commission, might be one of the most significant in the five years since the European Union passed the landmark General Data Protection Regulation. According to regulators, Facebook failed to comply with a 2020 judgment by the European Union’s top court that Facebook data transferred over the Atlantic was not sufficiently safeguarded from American espionage agencies. However, whether Meta will ever need to encrypt Facebook users’ data in Europe is still being determined. Meta announced it would appeal the ruling, launching a potentially legal procedure.
Simultaneously, European Union and American officials are negotiating a new data-sharing pact that would provide legal protections for Meta and scores of other companies to continue moving information between the US and Europe. This pact could overturn much of the European Union’s Monday ruling.
Article 46(1) GDPR Has been violated by the meta, And as per the Irish privacy.
What is required by the GDPR before transferring personal information across national boundaries?

Personal data transfers to countries outside the European Economic Area are generally permitted if these nations are regarded to provide a sufficient degree of data protection. According to Article 45 of the GDPR, the European Commission evaluates the degree of personal data protection in third countries.
The European Union judgment demonstrates how government rules are upending the borderless way data has traditionally migrated. Companies are increasingly being pressed to store data within the country where it is acquired rather than allowing it to transfer freely to data centres around the world as a result of data-protection requirements, national security laws, and other regulations.
The US internet giant had previously warned that if forced to stop using SCCs (standard contractual clauses) without a proper alternative data transfer agreement in place, it would be compelled to shut down services such as Facebook and Instagram in Europe.
What will happen next for Facebook in Europe?
The ruling includes a six-month transition period before it must halt data flows, meaning the service will continue to operate in the meantime. (More specifically, Meta has been given a five-month transition period to freeze any future transfer of personal data to the United States and a six-month deadline to terminate the unlawful processing and/or storage of European user data it has previously transferred without a legitimate legal basis. Meta has also stated that it will appeal and appears to seek a stay of execution while it pursues its legal arguments in court.
Conclusion
The GDPR places restrictions on transferring personal data outside the European Union to third-party nations or international bodies to ensure that the GDPR’s level of protection for individuals is not jeopardised. But the meta violated the European Union’s privacy laws by the user’s personal information to the US. Under the compliance of GDPR, transferring and sending personal information to users intentionally is an offence. and presently, the personal data of Facebook users has been breached by the Meta, as they shared the information with the US.

Introduction
Recent advances in space exploration and technology have increased the need for space laws to control the actions of governments and corporate organisations. India has been attempting to create a robust legal framework to oversee its space activities because it is a prominent player in the international space business. In this article, we’ll examine India’s current space regulations and compare them to the situation elsewhere in the world.
Space Laws in India
India started space exploration with Aryabhtta, the first satellite, and Rakesh Sharma, the first Indian astronaut, and now has a prominent presence in space as many international satellites are now launched by India. NASA and ISRO work closely on various projects
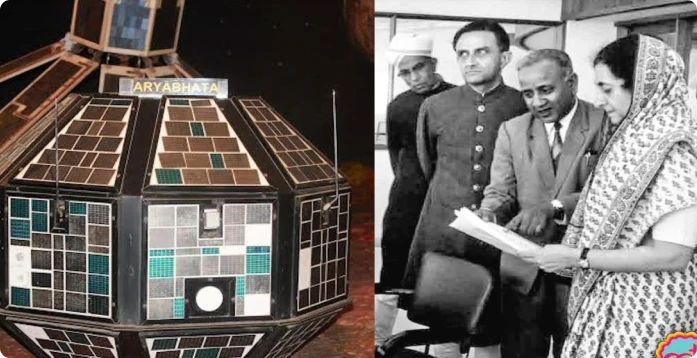
India currently lacks any space-related legislation. Only a few laws and regulations, such as the Indian Space Research Organisation (ISRO) Act of 1969 and the National Remote Sensing Centre (NRSC) Guidelines of 2011, regulate space-related operations. However, more than these rules and regulations are essential to control India’s expanding space sector. India is starting to gain traction as a prospective player in the global commercial space sector. Authorisation, contracts, dispute resolution, licencing, data processing and distribution related to earth observation services, certification of space technology, insurance, legal difficulties related to launch services, and stamp duty are just a few of the topics that need to be discussed. The necessary statute and laws need to be updated to incorporate space law-related matters into domestic laws.
India’s Space Presence
Space research activities were initiated in India during the early 1960s when satellite applications were in experimental stages, even in the United States. With the live transmission of the Tokyo Olympic Games across the Pacific by the American Satellite ‘Syncom-3’ demonstrating the power of communication satellites, Dr Vikram Sarabhai, the founding father of the Indian space programme, quickly recognised the benefits of space technologies for India.
As a first step, the Department of Atomic Energy formed the INCOSPAR (Indian National Committee for Space Research) under the leadership of Dr Sarabhai and Dr Ramanathan in 1962. The Indian Space Research Organisation (ISRO) was formed on August 15, 1969. The prime objective of ISRO is to develop space technology and its application to various national needs. It is one of the six largest space agencies in the world. The Department of Space (DOS) and the Space Commission were set up in 1972, and ISRO was brought under DOS on June 1, 1972.

Since its inception, the Indian space programme has been orchestrated well. It has three distinct elements: satellites for communication and remote sensing, the space transportation system and application programmes. Two major operational systems have been established – the Indian National Satellite (INSAT) for telecommunication, television broadcasting, and meteorological services and the Indian Remote Sensing Satellite (IRS) for monitoring and managing natural resources and Disaster Management Support.
Global Scenario
The global space race has been on and ever since the moon landing in 1969, and it has now transformed into the new cold war among developed and developing nations. The interests and assets of a nation in space need to be safeguarded by the help of effective and efficient policies and internationally ratified laws. All nations with a presence in space do not believe in good for all policy, thus, preventive measures need to be incorporated into the legal system. A thorough legal framework for space activities is being developed by the United Nations Office for Outer Space Affairs (UNOOSA). The “Outer Space Treaty,” a collection of five international agreements on space law, establishes the foundation of international space law. The agreements address topics such as the peaceful use of space, preventing space from becoming militarised, and who is responsible for damage caused by space objects. Well-established space laws govern both the United States and the United Kingdom. The National Aeronautics and Space Act, which was passed in the US in 1958 and established the National Aeronautics and Space Administration (NASA) to oversee national space programmes, is in place there. The Outer Space Act of 1986 governs how UK citizens and businesses can engage in space activity.

Conclusion
India must create a thorough legal system to govern its space endeavours. In the space sector, there needs to be a legal framework to avoid ambiguity and confusion, which may have detrimental effects. The Pacific use of space for the benefit of humanity should be covered by domestic space legislation in India. The overall scenario demonstrates the requirement for a clearly defined legal framework for the international acknowledgement of a nation’s space activities. India is fifth in the world for space technology, which is an impressive accomplishment, and a strong legal system will help India maintain its place in the space business.

Pretext
On 20th October 2022, the Competition Commission of India (CCI) imposed a penalty of Rs. 1,337.76 crores on Google for abusing its dominant position in multiple markets in the Android Mobile device ecosystem, apart from issuing cease and desist orders. The CCI also directed Google to modify its conduct within a defined timeline. Smart mobile devices need an operating system (OS) to run applications (apps) and programs. Android is one such mobile operating system that Google acquired in 2005. In the instant matter, the CCI examined various practices of Google w.r.t. licensing of this Android mobile operating system and various proprietary mobile applications of Google (e.g., Play Store, Google Search, Google Chrome, YouTube, etc.).
The Issue
Google was found to be misusing its dominant position in the tech market, and the same was the reason behind the penalty. Google argued about the competitive constraints being faced from Apple. In relation to understanding the extent of competition between Google’s Android ecosystem and Apple’s iOS ecosystem, the CCI noted the differences in the two business models, which affect the underlying incentives of business decisions. Apple’s business is primarily based on a vertically integrated smart device ecosystem that focuses on the sale of high-end smart devices with state-of-the-art software components. In contrast, Google’s business was found to be driven by the ultimate intent of increasing users on its platforms so that they interact with its revenue-earning service, i.e., online searches, which directly affects the sale of online advertising services by Google. It was seen that google had created a dominant position among the android phone manufacturers as they were made to have a set of google apps preinstalled in the device to increase the user’s dependency on google services. The CCI felt that Google had created a dominant position to which they replied that the same operations are done by Apple as well, to which the commission responded that apple is a phone and app manufacturer and they have Apple-owned apps in Apple devices only, but Google here in had made a pseudo mandate for android manufactures to have the google apps pre-installed which is, in turn, a possible way of disrupting the market equilibrium and violative of market practices. The CCI imposed a penalty of Rs. 1,337.76 for abusing its dominant position in multiple markets in India, CCI delineated the following five relevant markets in the present matter –

- The market for licensable OS for smart mobile devices in India
- The market for app store for Android smart mobile OS in India
- The market for general web search services in India
- The market for non-OS specific mobile web browsers in India
- The market for online video hosting platforms (OVHP) in India.
Supreme Courts Opinion
In October 2022, the Competition Commission of India (CCI) ruled that Google, owned by Alphabet Inc, exploited its dominant position in Android and told it to remove restrictions on device makers, including those related to the pre-installation of apps and ensuring exclusivity of its search. Google lost a challenge in the Supreme Court to block the directives, as the learned court refused to put a stay on the imposed penalty, further giving seven days to comply. The Supreme Court has said a lower tribunal—where Google first challenged the Android directives—can continue to hear the company’s appeal and must rule by March 31.
Counterpoint Research estimates that about 97% of 600 million smartphones in India run on Android. Apple has just a 3% share. Hoping to block the implementation of the CCI directives, Google challenged the CCI order in the Supreme Court by warning it could stall the growth of the Android ecosystem. It also said it would be forced to alter arrangements with more than 1,100 device manufacturers and thousands of app developers if the directives kick in. Google has been concerned about India’s decision as the steps are seen as more sweeping than those imposed in the European Commission’s 2018 ruling. There it was fined for putting in place what the Commission called unlawful restrictions on Android mobile device makers. Google is still challenging the record $4.3 billion fine in that case. In Europe, Google made changes later, including letting Android device users pick their default search engine, and said device makers would be able to license the Google mobile application suite separately from the Google Search App or the Chrome browser.
Conclusion
As the world goes deeper into cyberspace, the big tech companies have more control over the industry and the markets, but the same should not turn into anarchy in the global markets. The Tech giants need to be made aware that compliance is the utmost duty for all companies, and enforcement of the law of the land will be maintained no matter what. Earlier India lacked policies and legislation to govern cyberspace, but in the recent proactive stance by the govt, a lot of new bills have been tabled, one of them being the Intermediary Rules 2021, which has laid down the obligations nand duties of the companies by setting up an intermediary in the country. Such bills coupled with such crucial judgments on tech giants will act as a test and barrier for other tech companies who try to flaunt the rules and avoid compliance.

What are Wi-Fi attacks?
Wi-fi is an important area of cyber security and there is no need for physical cable for the network. Wi-Fi has access to a network signal radius everywhere. The devices and systems can have a network without physical access due to Wi-fi. But everything comes with cons and pros, and if we talk about cybersecurity, it has been established that Wi-fi networks are extremely vulnerable to security breaches and it is very easy to be hacked by hackers. Wi-Fi can be accessed by almost every device in the modern day: it can be smartphones, tablets, computers, and laptops. To know whether someone has been tampering with your personal Wi-Fi there are certain signs that can prove it. The first and most important sign is that your internet speed gets slower, as someone else is using your Wi-Fi surf.
Why would anyone hack someone’s Wi-Fi network?
Usually, hackers hack the network because they want access to the confidential data of someone and they can observe all the online activities and data that have been sent through a network. An unauthorize hacker will pretty much be able to see everything you do online. Wi-Fi allows hackers o view information on sites. Any financial information which is saved in the browser can be accessed by hackers and they can alter it and can alter the content you see online. And all the information saved in Wi-fi networks can be used by hackers for their own benefit, they can sell it, impersonate you, or even take money out of your bank through Wi-Fi.
Avoiding vulnerable Wi-Fi networks
The first and foremost rule of protection is that you should not use public networks if that network is easily open to you then that is also available to others and from others, and someone can who wishes to use your confidential and sensitive information, can access that. If you really need to access the public network in an urgent situation, then you must make sure to limit your activities while connected. And avoid accessing your online banking or pages that require login information. Also, a good measure to take as well is to always delete your cookies after using public WIFI.
How To Secure Your Home Wi-Fi Network
Your home’s wireless internet connection is your Wi-Fi network. Typically, a wireless router is used, which broadcasts a signal into the atmosphere. You can connect to the internet using that signal. However, if your network is not password-protected, any nearby device can grab the signal off the air and connect to your internet. The benefit of Wi-Fi? Wireless access to the internet is possible. The negative? Your internet activity, including your personal information, may be visible to neighboring users who connect to your unprotected network. Furthermore, if someone uses your network to conduct a crime or send out unauthorized spam, you might be held accountable.
Wi-Fi or Li-Fi? –
The common consensus is that Li-Fi technology is more secure than Wi-Fi. Li-Fi systems can be made more secure by integrating a variety of security features. Although these qualities might appear when Li-Fi is widely used in the near future, it is already thought to be safer because of a number of security features. Since the connection’s characteristics make it simpler to lock connections, limit access, and track users even in the absence of encryption and other security features, Li-Fi is seen as being safer. Li-Fi systems will be able to support new security protocols, which will not only enable high-speed networking but also open the door for innovative security techniques to strengthen connections.
Conclusion
A hacker can sniff the network packets without having to be in the same building where the network is located. As wireless networks communicate through radio waves, a hacker can easily sniff the network from a nearby location. Most attackers use network sniffing to find the SSID and hack a wireless network.
Any wireless network can theoretically be attacked in a number of different ways. Use of the default SSID or password, WPS pin authentication, insufficient access control, and leaving the access point available in open locations are all examples of potential vulnerabilities that could allow for the theft of sensitive data. Kismet’s architecture in WIDS mode may guard against DOS, MiTM, and MAC spoofing attacks. routine software updates on the other hand, the use of firewalls may help defend the network against outside intrusion. The act of finding infrastructure issues that could allow harmful code to be injected into a service, system, or organization is known as ethical hacking. They use this technique to prevent invasions by lawfully breaking into networks and looking for weak spots.

Introduction
Google Play has announced its new policy which will ensure trust and transparency on google play by providing a new framework for developer verification and app details. The new policy requires that new developer accounts on Google Play will have to provide a D-U-N-S number to verify the business. So when an organisation will create a new Play Console developer account the organisation will need to provide a D-U-N-S number. Which is a nine-digit unique identifier which will be used to verify their business. The new google play policy aims to enhance user trust. And the developer will provide detailed developer details on the app’s listing page. Users will get to know who is behind the app which they are installing.
Verifying Developer Identity with D-U-N-S Numbers
To boost security the google play new policy requires the developer account to provide the D-U-N-S number when creating a new Play Console developer account. The D-U-N-S number assigned by Dun & Bradstreet will be used to verify the business. Once the developer creates his new Play Console developer account by providing a D-U-N-S number, Google Play will verify the developer’s details, and he will be able to start publishing the apps. Through this step, Google Play aims to validate the business information in a more authentic way.
If your organisation does not have a D-U-N-S number, you may check on or request for it for free on this website (https://www.dnb.com/duns-number/lookup.html). The request process for D-U-N-S can take up to 30 days. Developers are also required to keep the information up to date.
Building User Trust with Enhanced App Details
In addition to verifying developer identities in a more efficient way, google play also requires that developer provides sufficient app details to the users. There will be an “App Support” section on the app’s store listing page, where the developer will display the app’s support email address and even can include their website and phone number for support.
The new section “About the developer” will also be introduced to provide users with verified identity information, including the developer’s name, address, and contact details. Which will make the users more informed about the valuable information of the app developers.
Key highlights of the Google Play Polic
- Google Play came up with the policy to keep the platform safe by verifying the developers’ identity and it will also help to reduce the spread of malware apps and help the users to make confident informed decisions about the apps they download. Google Play announced the policy by expanding its developer verification requirement to strengthen Google Play as a platform and build user trust. When you create a new Play Console Developer account and choose organisation as your account type you will now need to provide a D-U-N-S number.
- Users will get detailed information about the developers’ identities and contact information, building more transparency and encouraging responsible app development practices.
- This policy will enable the users to make informed choices about the apps they download.
- The new “App support” section will provide enhanced communication between users and developers by displaying support email addresses, website and support phone numbers, streamlining the support process and user satisfaction.
Timeline and Implementation
The new policy requirements for D-U-N-S numbers will start rolling out on 31 August 2023 for all new Play Console developer accounts. The “About the developer” section will be visible to users as soon as a new app is published. and In October 2023, existing developers will also be required to update and verify their existing accounts to comply with the new verification policy.
Conclusion
Google Play’s new policy will aim to enhance the more transparent app ecosystem. This new policy will provide the users with more information about the developers. Google Play aims to establish a platform where users can confidently discover and download apps. This new policy will enhance the user experience on google play in terms of a reliable and trustworthy platform.

Introduction
Recently, a Consultation Paper on Regulatory Mechanisms for Over-The-Top (OTT) Communication Services was published by the Telecom Regulatory Authority of India (TRAI). The paper explores several OTT regulation-related challenges and solicits input from stakeholders on a suggested regulatory framework. We’ll summarise the paper’s main conclusions in this blog.
Structure of the Paper
The Telecom Regulatory Authority of India’s Consultation Paper on Regulatory Mechanism for Over-The-Top (OTT) Communication Services and Selective Banning of OTT Services intends to solicit comments and recommendations from stakeholders about the regulation of OTT services in India. The paper is broken up into five chapters that cover the introduction and background, issues with regulatory mechanisms for OTT communication services, issues with the selective banning of OTT services, a summary of the issues for consultation, and an overview of international practices on the topic. Written comments from interested parties are requested and may be sent electronically to the Advisor (Networks, Spectrum and Licencing) at TRAI. These comments will also be posted on the TRAI website.
Overview of the Paper
- Chapter 1: Introduction and Background
- The first chapter of the essay introduces the subject of OTT communication services and argues why regulatory frameworks are necessary. The chapter also gives a general outline of the topics and the paper’s organisation that will be covered in the following chapters.
- Chapter 2: Examination of the Issues Related to Regulatory Mechanism for Over-The-Top Communication Services
- The second chapter of the essay looks at the problems with OTT communication service regulation. It talks about the many kinds of OTT services and how they affect the conventional telecom sector. The chapter also looks at the regulatory issues raised by OTT services and the various strategies used by various nations to address them.
- Chapter 3: Examination of the Issues Related to Selective Banning of OTT Services
- The final chapter of the essay looks at the problems of selectively outlawing OTT services. It analyses the justifications for government restrictions on OTT services as well as the possible effects of such restrictions on consumers and the telecom sector. The chapter also looks at the legal and regulatory structures that determine how OTT services are prohibited in various nations.
- Chapter 4: International Practices
- An overview of global OTT communication service best practices is given in the paper’s fourth chapter. It talks about the various regulatory strategies used by nations throughout the world and how they affect consumers and the telecom sector. The chapter also looks at the difficulties regulators encounter when trying to create efficient regulatory frameworks for OTT services.
- Chapter 5: Issues for Consultation
- This chapter is the spirit of the consultation paper as it covers the points and questions for consultation. This chapter has been classified into two sub-sections – Issues Related to Regulatory Mechanisms for OTT Communication Services and Issues Related to the Selective Banning of OTT Services. The inputs will be entirely focused on these sub headers, and the scope, extent, and ambit of the consultation paper rests on these questions and necessary inputs.
Conclusion
An important publication that aims to address the regulatory issues raised by OTT services is the Consultation Paper on Regulatory Mechanisms for Over-The-Top Communication Services. The paper offers a thorough analysis of the problems with OTT service regulation and requests input from stakeholders on the suggested regulatory structure. In order to make sure that the regulatory framework is efficient and advantageous for everyone, it is crucial for all stakeholders to offer their opinion on the document.

Introduction
Twitter Inc.’s appeal against barring orders for specific accounts issued by the Ministry of Electronics and Information Technology was denied by a single judge on the Karnataka High Court. Twitter Inc. was also given an Rs. 50 lakh fine by Justice Krishna Dixit, who claimed the social media corporation had approached the court defying government directives.
As a foreign corporation, Twitter’s locus standi had been called into doubt by the government, which said they were ineligible to apply Articles 19 and 21 to their situation. Additionally, the government claimed that because Twitter was only designed to serve as an intermediary, there was no “jural relationship” between Twitter and its users.
The Issue
In accordance with Section 69A of the Information Technology Act, the Ministry issued the directives. Nevertheless, Twitter had argued in its appeal that the orders “fall foul of Section 69A both substantially and procedurally.” Twitter argued that in accordance with 69A, account holders were to be notified before having their tweets and accounts deleted. However, the Ministry failed to provide these account holders with any notices.
On June 4, 2022, and again on June 6, 2022, the government sent letters to Twitter’s compliance officer requesting that they come before them and provide an explanation for why the Blocking Orders were not followed and why no action should be taken against them.
Twitter replied on June 9 that the content against which it had not followed the blocking orders does not seem to be a violation of Section 69A. On June 27, 2022, the Government issued another notice stating Twitter was violating its directions. On June 29, Twitter replied, asking the Government to reconsider the direction on the basis of the doctrine of proportionality. On June 30, 2022, the Government withdrew blocking orders on ten account-level URLs but gave an additional list of 27 URLs to be blocked. On July 10, more accounts were blocked. Compiling the orders “under protest,” Twitter approached the HC with the petition challenging the orders.
Legality
Additionally, the government claimed that because Twitter was only designed to serve as an intermediary, there was no “jural relationship” between Twitter and its users.
Government attorney Additional Solicitor General R Sankaranarayanan argued that tweets mentioning “Indian Occupied Kashmir” and the survival of LTTE commander Velupillai Prabhakaran were serious enough to undermine the integrity of the nation.
Twitter, on the other hand, claimed that its users have pushed for these rights. Additionally, Twitter maintained that under Article 14 of the Constitution, even as a foreign company, they were entitled to certain rights, such as the right to equality. They also argued that the reason for the account blocking in each case was not stated and that Section 69a’s provision for blocking a URL should only apply to the offending URL rather than the entire account because blocking the entire account would prevent the creation of information while blocking the offending tweet only applied to already-created information.
Conclusion
The evolution of cyberspace has been substantiated by big tech companies like Facebook, Google, Twitter, Amazon and many more. These companies have been instrumental in leading the spectrum of emerging technologies and creating a blanket of ease and accessibility for users. Compliance with laws and policies is of utmost priority for the government, and the new bills and policies are empowering the Indian cyberspace. Non Compliance will be taken very seriously, and the same is legalised under the Intermediary Guidelines 2021 and 2022 by Meity. Referring to Section 79 of the Information Technology Act, which pertains to an exemption from liability of intermediary in some instances, it was said, “Intermediary is bound to obey the orders which the designate authority/agency which the government fixes from time to time.”

Introduction
Cert-In (Indian Computer Emergency Response Team) has recently issued the “Guidelines on Information Security Practices” for Government Entities for Safe & Trusted Internet. The guideline has come at a critical time when the Draft Digital India Bill is about to be released, which is aimed at revamping the legal aspects of Indian cyberspace. These guidelines lay down the policy framework and the requirements for critical infrastructure for all government organisations and institutions to improve the overall cyber security of the nation.
What is Cert-In?
A Computer Emergency Response Team (CERT) is a group of information security experts responsible for the protection against, detection of and response to an organisation’s cybersecurity incidents. A CERT may focus on resolving data breaches and denial-of-service attacks and providing alerts and incident handling guidelines. CERTs also conduct ongoing public awareness campaigns and engage in research aimed at improving security systems. The Ministry of Electronics and Information Technology (MeitY) oversees CERT-In. It regularly releases alerts to help individuals and companies safeguard their data, information, and ICT (Information and Communications Technology) infrastructure.
Indian Computer Emergency Response Team (CERT-In) has been established and appointed as national agency in respect of cyber incidents and cyber security incidents in terms of the provisions of section 70B of Information Technology (IT) Act, 2000.
CERT-In requests information from service providers, intermediaries, data centres, and body corporates to coordinate reaction actions and emergency procedures regarding cyber security incidents. It is a focal point for incident reporting and offers round-the-clock security services. It manages cyber occurrences that are tracked and reported while continuously analysing cyber risks. It strengthens the security barriers for the Indian Internet domain.
Background
India is fast becoming one of the world’s largest connected nations – with over 80 Crore Indians (Digital Nagriks) presently connected and using the Internet and cyberspace – and with this number is expected to touch 120 Crores in the coming few years. The Digital Nagriks of the country are using the Internet for business, education, finance and various applications and services including Digital Government services. Internet provides growth and innovation and at the same time it has seen rise in cybercrimes, user harm and other challenges to online safety. The policies of the Government are aimed at ensuring an Open, Safe & Trusted and Accountable Internet for its users. Government is fully cognizant and aware of the growing cyber security threats and attacks.
It is the Government of India’s objective to ensure that Digital Nagriks experience a Safe & Trusted Internet. Along with ubiquitous applications of Information & Communication Technologies (ICT) in almost all facets of service delivery and operations, continuously evolving cyber threats have become a concern for the Government. Cyber-attacks can come in the form of malware, ransomware, phishing, data breach etc., that adversely affect an organisation’s information and systems. Cyber threats leading to cyber-attacks or incidents can compromise the confidentiality, integrity, and availability of an organisation’s information and systems and can have far reaching impact on essential services and national interests. To protect against cyber threats, it is important for government entities to implement strong cybersecurity measures and follow best practices. As ICT infrastructure of the Government entities is one of the preferred targets of the malicious actors, responsibility of implementing good cyber security practices for protecting computers, servers, applications, electronic systems, networks, and data from digital attacks, also remain with the ICT assets’ owner i.e. Government entity.
What are the new Guidelines about?
The Government of India (distribution of business) Rules, 1961’s First Schedule lists a number of Ministries, Departments, Secretariats, and Offices, along with their affiliated and subordinate offices, which are all subject to the rules. They also comprise all governmental organisations, businesses operating in the public sector, and other governmental entities under their administrative control.
“The government has launched a number of steps to guarantee an accessible, trustworthy, and accountable digital environment. With a focus on capabilities, systems, human resources, and awareness, we are extending and speeding our work in the area of cyber security, according to Rajeev Chandrasekhar, Minister of State for Electronics, Information Technology, Skill Development, and Entrepreneurship.
The Recommendations
- Various security domains are covered in the standards, including network security, identity and access management, application security, data security, third-party outsourcing, hardening procedures, security monitoring, incident management, and security audits.
- For instance, the rules advise using only a Standard User (non-administrator) account to use computers and laptops for regular work regarding desktop, laptop, and printer security in the workplace. Users may only be granted administrative access with the CISO’s consent.
- The usage of lengthy passwords containing at least eight characters that combine capital letters, tiny letters, numerals, and special characters; Never save any usernames or passwords in your web browser. Likewise, never save any payment-related data there.
- They include guidelines created by the National Informatics Centre for Chief Information Security Officers (CISOs) and staff members of Central government Ministries/Departments to improve cyber security and cyber hygiene in addition to adhering to industry best practises.
Conclusion
The government has been proactive in the contemporary times to eradicate the menace of cybercrimes and therreats from the Indian cyberspace and hence now we have seen a series of new bills and polices introduced by the Ministry of Electronics and Information Technology, and various other government organisations like Cert-In and TRAI. These policies have been aimed towards being relevant to time and current technologies. The threats from emerging technologies like web 3.0 cannot be ignored and hence with active netizen participation and synergy between government and corporates will lead to a better and improved cyber ecosystem in India.

Introduction
The Telecom Regulatory Authority of India (TRAI) issued a consultation paper titled “Encouraging Innovative Technologies, Services, Use Cases, and Business Models through Regulatory Sandbox in Digital Communication Sector. The paper presents a draft sandbox structure for live testing of new digital communication products or services in a regulated environment. TRAI seeks comments from stakeholders on several parts of the framework.
What is digital communication?
Digital communication is the use of internet tools such as email, social media messaging, and texting to communicate with other people or a specific audience. Even something as easy as viewing the content on this webpage qualifies as digital communication.
Aim of Paper
- Frameworks are intended to support regulators’ desire for innovation while also ensuring economic resilience and consumer protection. Considering this, the Department of Telecom (DoT) asked TRAI to offer recommendations on a regulatory sandbox framework. TRAI approaches the issue with the goal of encouraging creativity and hastening the adoption of cutting-edge digital communications technologies.
- Artificial intelligence, the Internet of Things, edge computing, and other emerging technologies are revolutionizing how we connect, communicate, and access information, driving the digital communication sector to rapidly expand. To keep up with this dynamic environment, an enabling environment for the development and deployment of novel technologies, services, use cases, and business models is required.
- The regulatory sandbox concept is becoming increasingly popular around the world as a means of encouraging innovation in a range of industries. A regulatory sandbox is a regulated environment in which businesses and innovators can test their concepts, commodities, and services while operating under changing restrictions.
- Regulatory Sandbox will benefit the telecom startup ecosystem by providing access to a real-time network environment and other data, allowing them to evaluate the reliability of new applications before releasing them to the market. Regulatory Sandbox also attempts to stimulate cross-sectoral collaboration for carrying out such testing by engaging the assistance of other ministries and departments in order to give the starting company with a single window for acquiring all clearances.
What is regulatory sandbox?
- A regulatory sandbox is a controlled regulatory environment in which new products or services are tested in real-time.
- It serves as a “safe space” for businesses because authorities may or may not allow certain relaxations for the sole purpose of testing.
- The sandbox enables the regulator, innovators, financial service providers, and clients to perform field testing in order to gather evidence on the benefits and hazards of new financial innovations, while closely monitoring and mitigating their risks.
What are the advantages of having a regulatory sandbox?
- Firstly, regulators obtain first-hand empirical evidence on the benefits and risks of emerging technologies and their implications, allowing them to form an informed opinion on the regulatory changes or new regulations that may be required to support useful innovation while mitigating the associated risks.
- Second, sandbox customers can evaluate the viability of a product without the need for a wider and more expensive roll-out. If the product appears to have a high chance of success, it may be authorized and delivered to a wider market more quickly.
Digital communication sector and Regulatory Sandbox
- Many countries’ regulatory organizations have built sandbox settings for telecom tech innovation.
- These frameworks are intended to encourage regulators’ desire for innovation while also promoting economic resilience and consumer protection.
- In this context, the Department of Telecom (DoT) had asked TRAI to give recommendations on a regulatory sandbox framework.
- Written comments on the drafting framework will be received until July 17, 2023, and counter-comments will be taken until August 1, 2023. The Authority’s goal in the digital communication industry is to foster creativity and expedite the use of emerging technologies such as artificial intelligence (AI), the Internet of Things (IoT), and edge computing. These technologies are changing the way individuals connect, engage, and access information, causing rapid changes in the industry.
Conclusion
According to TRAI, these technologies are changing how individuals connect, engage, and obtain information, resulting in significant changes in the sector.
The regulatory sandbox also wants to stimulate cross-sectoral collaboration for carrying out such testing by engaging the assistance of other ministries and departments in order to give the starting company with a single window for acquiring all clearances. The consultation paper covers some of the worldwide regulatory sandbox frameworks in use in the digital communication industry, as well as some of the frameworks in use inside the country in other sectors.

Introduction
The Telecom Regulatory Authority of India (TRAI) has directed all telcos to set up detection systems based on Artificial Intelligence and Machine Learning (AI/ML) technologies in order to identify and control spam calls and text messages from unregistered telemarketers (UTMs).
The TRAI Directed telcos
The telecom regulator, TRAI, has directed all Access Providers to detect Unsolicited commercial communication (UCC)by systems, which is based on Artificial Intelligence and Machine Learning to detect, identify, and act against senders of Commercial Communication who are not registered in accordance with the provisions of the Telecom Commercial Communication Customer Preference Regulations, 2018 (TCCCPR-2018). Unregistered Telemarketers (UTMs) are entities that do not register with Access Providers and use 10-digit mobile numbers to send commercial communications via SMS or calls.
TRAI steps to curb Unsolicited commercial communication
TRAI has taken several initiatives to reduce Unsolicited Commercial Communication (UCC), which is a major source of annoyance for the public. It has resulted in fewer complaints filed against Registered Telemarketers (RTMs). Despite the TSPs’ efforts, UCC from Unregistered Telemarketers (UTMs) continues. Sometimes, these UTMs use messages with bogus URLs and phone numbers to trick clients into revealing crucial information, leading to financial loss.
To detect, identify, and prosecute all Unregistered Telemarketers (UTMs), the TRAI has mandated that Access Service Providers implement the UCC.
Detect the System with the necessary functionalities within the TRAI’s Telecom Commercial Communication Customer Preference Regulations, 2018 framework.
Access service providers have implemented such detection systems based on their applicability and practicality. However, because UTMs are constantly creating new strategies for sending unwanted communications, the present UCC detection systems provided by Access Service providers cannot detect such UCC.
TRAI also Directs Telecom Providers to Set Up Digital Platform for Customer Consent to Curb Promotional Calls and Messages.
Unregistered Telemarketers (UTMs) sometimes use messages with fake URLs and phone numbers to trick customers into revealing essential information, resulting in financial loss.

TRAI has urged businesses like banks, insurance companies, financial institutions, and others to re-verify their SMS content templates with telcos within two weeks. It also directed telecom companies to stop misusing commercial messaging templates within the next 45 days.
The telecom regulator has also instructed operators to limit the number of variables in a content template to three. However, if any business intends to utilise more than three variables in a content template for communicating with their users, this should be permitted only after examining the example message, as well as adequate justifications and justification.
In order to ensure consistency in UCC Detect System implementations, TRAI has directed all Access Providers to deploy UCC and detect systems based on artificial intelligence and Machine Learning that are capable of constantly evolving to deal with new signatures, patterns, and techniques used by UTMs.
Access Providers have also been directed to use the DLT platform to share intelligence with others. Access Providers have also been asked to ensure that such UCC Detect System detects senders that send unsolicited commercial communications in bulk and do not comply with the requirements. All Access Providers are directed to follow the instructions and provide an update on actions done within thirty days.
The move by TRAI is to curb the menacing calls as due to this, the number of scam cases is increasing, and now a new trend of scams started as recently, a Twitter user reported receiving an automated call from +91 96681 9555 with the message “This call is from Delhi Police.” It then asked her to stay in the queue since some of her documents needed to be picked up. Then he said he works as a sub-inspector at the Kirti Nagar police station in New Delhi. He then inquired whether she had recently misplaced her Aadhaar card, PAN card, or ATM card, to which she replied ‘no’. The scammer then poses as a cop and requests that she authenticate the last four digits of her card because they have found a card with her name on it. And a lot of other people tweeted about it.

Conclusion
TRAI directed the telcos to check the calls and messages from Unregistered numbers. This step of TRAI will curb the pesky calls and messages and catch the Frauds who are not registered with the regulation. Sometimes the unregistered sender sends fraudulent links, and through these fraudulent calls and messages, the sender tries to take the personal information of the customers, which results in financial losses.

Introduction
To combat the problem of annoying calls and SMS, telecom regulator TRAI has urged service providers to create a uniform digital platform in two months that will allow them to request, maintain, and withdraw customers’ approval for promotional calls and messages. In the initial stage, only subscribers will be able to initiate the process of registering their consent to receive promotional calls and SMS, and later, business entities will be able to contact customers to seek their consent to receive promotional messages, according to a statement issued by the Telecom Regulatory Authority of India (TRAI) on Saturday.
TRAI Directs Telecom Providers to Set Up Digital Platform
TRAI has now directed all access providers to develop and deploy the Digital Consent Acquisition (DCA) facility for creating a unified platform and process to digitally register customers’ consent across all service providers and principal entities. Consent is received and maintained under the current system by several key entities such as banks, other financial institutions, insurance firms, trading companies, business entities, real estate businesses, and so on.
The purpose, scope of consent, and the principal entity or brand name shall be clearly mentioned in the consent-seeking message sent over the short code,” according to the statement.
It stated that only approved online or app links, call-back numbers, and so on will be permitted to be used in consent-seeking communications.
TRAI issued guidelines to guarantee that all voice-based Telemarketers are brought under a single Distributed ledger technology (DLT) platform for more efficient monitoring of nuisance calls and unwanted communications. It also instructs operators to actively deploy AI/ML-based anti-phishing systems as well as to integrate tech solutions on the DLT platform to deal with malicious calls and texts.
TRAI has issued two separate Directions to Access Service Providers under TCCCPR-2018 (Telecom Commercial Communications Customer Preference Regulations) to ensure that all promotional messages are sent through Registered Telemarketers (RTMs) using approved Headers and Message Templates on Distributed Ledger Technologies (DLT) platform, and to stop misuse of Headers and Message Templates,” the regulator said in a statement.
Users can already block telemarketing calls and texts by texting 1909 from their registered mobile number. By dialing 1909, customers can opt out of getting advertising calls by activating the do not disturb (DND) feature.

Telecom providers operate DLT platforms, and businesses involved in sending bulk promotional or transactional SMS must register by providing their company information, including sender IDs and SMS templates.
According to the instructions, telecom companies will send consent-seeking messages using the common short code 127. The goal, extent of consent, and primary entity/brand name must be clearly stated in the consent-seeking message delivered via the shortcode.
TRAI stated that only whitelisted URLs/APKs (Android package kits file format)/OTT links/call back numbers, etc., shall be used in consent-seeking messages.
Telcos must “ensure that promotional messages are not transmitted by unregistered telemarketers or telemarketers using telephone numbers (10 digits numbers).” Telecom providers have been urged to act against all erring telemarketers in accordance with the applicable regulations and legal requirements.
Users can, however, refuse to receive any consent-seeking messages launched by any significant Telcos have been urged to create an SMS/IVR (interactive voice response)/online service for this purpose.
According to TRAI’s timeline, the consent-taking process by primary companies will begin on September 1.According to a nationwide survey conducted by a local circle, 66% of mobile users continue to receive three or more bothersome calls per day, the majority of which originate from personal cell numbers.
There are scams surfacing on the internet with new types of scams, like WhatsApp international call scams. The latest scam is targeting Delhi police, the scammers pretend to be police officials of Delhi and ask for the personal details of the users and the calling them from a 9-digit number.
A recent scam
A Twitter user reported receiving an automated call from +91 96681 9555, stating, “This call is from Delhi Police.” It went on to ask her to stay in the queue since some of her documents needed to be picked up. Then he said he is a sub-inspector at New Delhi’s Kirti Nagar police station. He then questioned if she had lately misplaced her Aadhaar card, PAN card, or ATM card, to which she replied ‘no’. The fraudster then claims to be a cop and asks her to validate the final four digits of her card because they have discovered a card with her name on it. And so many other people tweeted about this.
The scams are constantly increasing as earlier these scammers asked for account details and claimed to be Delhi police and used 9-digit numbers for scamming people.
TRAI’s new guidelines regarding the consent to receive any promotional calls and messages to telecommunication providers will be able to curb the scams.
The e- KYC is an essential requirement as e-KYC offers a more secure identity verification process in an increasingly digital age that uses biometric technologies to provide quick results.

Conclusion
The aim is to prevent unwanted calls and communications sent to customers via digital methods without their permission. Once this platform is implemented, an organization can only send promotional calls or messages with the customer’s explicit approval. Companies use a variety of methods to notify clients about their products, including phone calls, text messages, emails, and social media. Customers, however, are constantly assaulted with the same calls and messages as a result of this practice. With the constant increase in scams, the new guideline of TRAI will also curb the calling of Scams. digital KYC prevents SIM fraud and offers a more secure identity verification method.

Introduction
Online Gaming has gained popularity over the past few years, attracting young players worldwide and global concerns. In response to the growing fame of this industry, the Indian government has recently announced introducing a set of regulations to address various concerns and ensure a safer and more regulated online gaming environment. In this blog post, we will explore the critical aspects of these regulations and their impact on the gaming industry.
Why are Regulations needed?
Recently some games faced a ban in India – games that involve betting, games that can be harmful to the user, and games that involve a factor of addiction. Furthermore, with rising popularity, With the exponential rise of online gaming platforms in India, extensive laws to safeguard players and ensure fair gameplay needs to be implemented. Players’ protection is one of the critical factors addressing the issues which involve online addiction, underage involvement, fraud, and data privacy has become critical for the well-being of Indian gamers.
Regulatory Ambiguity: The previous legislative structure, such as the outmoded Public Gambling Act of 1867, required an update to fit the digital gambling age fully.
Outline of the New Regulations
Implementing new regulations for online gaming in India represents the government’s commitment to addressing different issues and ensuring a safer and more regulated gaming sector. Let’s have a look at these rules in detail:
National-Level Standards: The Indian government is currently working on creating national-level standards to standardise online gaming practices across all states. These rules attempt to create a uniform platform for both operators and participants. The government has also made an announcement to set SRO within 90 days to regulate online gaming.
Licencing and Compliance: To legally operate in the Indian market, online gaming firms must secure licences. The operator’s financial soundness, security measures, and adherence to responsible gaming practices will be scrutinised throughout the licencing process. Operators will need to comply with the regulations in order to maintain operations.
Measures to Promote Ethical Gaming: The new regulations emphasise player protection and ethical gaming practices. This includes steps like age verification to prevent underage involvement, self-exclusion choices for gamers who want to limit their gaming activities, and adopting tools like session limits and reality checks to promote responsible gaming.
Data Privacy: Recognising the importance of data privacy, the laws are intended to contain protections for protecting user data. To safeguard sensitive player information from unauthorised access or exploitation, online gambling operators must comply with data protection regulations and deploy strong security measures.
Restrictions on Advertising and Marketing: The legislation may limit the advertising and marketing of online gaming platforms. The emphasis will be on eliminating aggressive marketing tactics that target vulnerable people, such as kids. Stricter standards for ad content and placement may be implemented.
Anti-Fraud and Anti-Money Laundering Measures: To combat criminal activity within the gaming ecosystem, the new legislation will almost certainly force online gambling companies to employ anti-fraud and anti-money laundering measures. Operators may need to set up mechanisms to detect fraud, report suspicious activity, and work with law enforcement.
Consumer Grievance Redressal: The legislation may emphasise the construction of efficient channels for resolving consumer complaints. Players should be able to report difficulties, seek resolution, and offer feedback on their play experiences through channels. The objective is to create a transparent and accountable conflict resolution mechanism.

Impact on Online Gaming Ecosystem
Adopting new laws for online gambling in India will likely have several consequences for the gaming industry. Let us look at some of these consequences:
Increased Player Trust: Implementing restrictions will increase player confidence in online gaming platforms. Establishing clear rules and procedures and steps to safeguard participants’ interests will develop a sense of trust and transparency. This can lead to increased participation and engagement in the gaming community.
Industry Consolidation: Stricter restrictions may result in industry consolidation. Compliance with the new legislation would need resources and investments, which might favour more prominent and more established gambling firms. Smaller and more non-compliant operators may find it challenging to fulfil regulatory standards, resulting in a more consolidated gaming sector.
Technological Progress: The requirement to comply with rules could lead to technological advancements in the online gambling sector. Operators may invest in modern identity verification systems, fraud detection methods, and responsible gaming solutions to satisfy their regulatory requirements. This can result in technological breakthroughs that improve gamers’ overall gaming experience.
Foreign Investment and Collaboration: Clear laws might entice overseas investors to enter the Indian gaming business. The regulated environment may appeal to international gambling enterprises looking to enter or extend their presence in India. Collaborations between Indian and foreign gaming firms may also expand, resulting in the sharing of experience, resources, and the production of high-quality gaming products.
Legal Clarity: Implementing particular laws would give online gambling operators and users clearer legal standards. This transparency can eliminate ambiguity and possible legal issues, allowing stakeholders to navigate the gaming ecosystem with better confidence and knowledge.
Contribution to the Indian Economy: A well-regulated online gaming business has the potential to contribute to the Indian economy. It has the potential to create jobs, attract investment, and produce tax money for the government. The economic effect of the gaming ecosystem is expected to increase as it grows under the new restrictions.
Challenges and Future Approach
One of the toughest challenges will be the efficient implementation and enforcement of the new regulations. Consistency in applying the legislation across multiple jurisdictions and guaranteeing compliance by all operators would necessitate comprehensive monitoring and regulatory measures. Developing suitable enforcement organisations and transparent standards for reporting and dealing with noncompliance will be critical. Besides this, online gaming is open to more than area-specific and many gaming platforms and operates internationally. Ensuring cross-border operations is a big challenge in addressing jurisdictional challenges will be complex. Collaborative efforts between nations can regulate cross-border online gaming. There may be increased collaboration between Indian and foreign gaming firms, resulting in the exchange of information, skills, and resources. This partnership can help the Indian gaming sector flourish while attracting foreign players and investments.
Esports Development: Esports have grown in popularity worldwide, and India is no exception. The Indian esports business has the potential to thrive with proper regulation and support, drawing both players and viewers. Esports-specific factors like player contracts, tournament integrity, and licencing requirements may be addressed in the regulations.

Conclusion
Despite obstacles, India’s new online gambling legislation can potentially establish a safer and more regulated gaming sector. the future depends on successful implementation, adjusting to a shifting landscape, finding the correct balance between regulation and innovation, and promoting ethical gaming practices. The Indian online gaming business can develop sustainably with the appropriate strategy, benefiting gamers and the broader economy.

Introduction
Ministry of Electronics and Information Technology (MeitY) Announces to Centre Government to Plan to Certify Permissible Online Games.
In a recent update to the notification released by the Ministry of Electronics and Information Technology (MeitY) on April 6, MeitY has requested gaming entities to establish self-regulatory organisations (SROs) within a timeframe of 30 days or a maximum of 90 days from the date of the notification, which is April 6, 2023. The Ministry of Electronics and Information Technology (MeitY) has further announced that the central government will certify which online games are permissible until the SROs are officially established. The intention behind establishing SROs is to assist intermediaries, such as Apple or Google, in determining what constitutes a permitted online game, but the SRO will take 2-3 months to complete. In the meanwhile, the Central government will step in and determine what is a permissible online game.
Information Technology (Intermediary Guidelines and Digital Media Ethics Code) Rules, 2021 & Intermediary Guidelines and Digital Media Ethics Code Amendment Rules, 2023
By enacting these rules, the Indian government has taken decisive action to protect Indian gamers and their financial resources against scams and fraud. The rules also serve to promote responsible gaming while preventing young and vulnerable users from being exposed to indecent or abusive content.
Amendment Rules developed the concept of a “Permissible online real money game.” This designation is reserved for games that have passed a review process conducted by a self-regulatory body (SRB). Amendment rules indicate that Online Gaming Intermediaries must ensure that they do not permit any third party to host non-permissible online real money games on their platforms. This development is important because it empowers us to distinguish between legitimate and illicit real money games.
The Amendment Rules define an online gaming provider as an “intermediary” under the Information Technology Act of 2000, creating a separate classification called ‘Online Gaming Intermediary’.

Central government to certify what is an ‘Online Permissible Game’
The industry has been wondering what games come under wagering and will be banned. So, until the SROs are officially established, the government, in the interim, will certify what is a permissible game, what is wagering, and what is not wagering. Games that involve elements of wagering are going to be barred. The new regulations prohibit wagering on any outcome, whether in skill-based or chance-based games. Hence gaming applications involving wagering and betting apps will be barred.
Self-Regulatory Organizations (SROs)
According to the new regulations by the Ministry of Electronics and Information Technology (MeitY), online gaming intermediaries must establish a Self-Regulatory Body (SRO) to approve games offered to users over the Internet. The SRO must be registered with the Ministry and develop a framework to ensure compliance with the IT Rules 2021 objectives. An ‘online game’ can be registered by the SRO if it meets specific criteria, which include that the game is offered by an online gaming intermediary that is a member of the self-regulatory body, the game is not containing any content harmful to India’s interests, and complying with all relevant Indian regulations. If these requirements are met, the intermediary can display a visible registration mark indicating its registration with the self-regulatory authority.
Conclusion
MeitY found that with the rapid growth of the gaming industry, the real money gaming (RMG) sector had to be regulated properly. Rules framed must be properly implemented to stop gambling, betting, and wagering apps.
The IT Rules 2021, along with the Amendment Rules 2023, are created to take concrete action to curb the proliferation of gambling, betting, and wagering apps in India. These rules empower to issue of directives to ban specific apps that facilitate or promote such activities. The app ban directive allows the government to take decisive action by blocking access to these apps, making them unavailable for download or use within the country. This measure is aimed at curbing the negative impact of gambling, betting, and wagering on individuals and society, including issues related to addiction, financial loss, and illegal activities. Rules aim to actively combat the spread and influence of such apps and provide a safer online environment for gaming users.
The self-regulatory body in the context of online gaming will have the authority to grant membership to gaming intermediaries, register online games, develop a framework for regulation, interact with the Central Government, address user complaints, report instances of non-compliance, and take necessary actions to safeguard online gaming users.

Introduction
India has been a nation where technology penetration has been a little slower in the previous decades; however, that has changed now. Cyberspace has influenced and touched every country and has significantly diminished the gap between developing nations, developed nations, and underdeveloped nations. This has also been substantiated and strengthened during the Covid-19 pandemic as the world went into lockdown and the cyberspace was the only medium of communication and information. India witnessed a rise of 61% in terms of internet users, and a significant part of this number represented rural India.
New Standards
These standards have been released in threefold aspects covering – Digital Television Receivers, USB Type-C chargers, and Video Surveillance Systems, thus streamlining the use of gadgets and reduction of e-waste for the country.
1. Digital Television Receivers
The Indian standard IS 18112:2022 specification for digital television, and this standard would enable reception of free-to-air TV and radio channels just by connecting a dish antenna with LNB mounted on a suitable area with good signal reception. This will help in the transmission of knowledge about government initiatives and schemes, the educational content of Doordarshan, and the repository of Indian cultural programs. Doordarshan is in the process of phasing out analog transmission, and free-to-air channels will continue to be broadcast using digital satellite transmission. The keen aspects of educational and awareness programs run by the Govt and CSOs will impact more Indians than before as the Ministry of Information and Broadcast intends to increase their free channels of Doordarshan from 55 to 200 by the end of this year, which shows the importance of developments in the mass media industry.
2. USB Type C
Standard (IS/IEC 62680-1-3:2022) for USB Type-C receptacles, plugs, and cables adopting the existing global standard IEC 62680-1-3:2022. This standard provides for the requirements for USB type C ports and cables for use in various electronic devices like laptops, mobile phones, and other gadgets. This standard is similar to the new European standard, which is also aimed at the reduction of carbon emissions and e-waste; this move will result in ease for the industry and the end users. This will also contribute towards the strengthening of the cyber security aspects and prevent threats like ‘Juice Jacking’ to a massive extent.
3. Video Surveillance System
IS 16190, this standard provides a detailed outline of the aspects of a video surveillance system, such as requirements for its components like camera devices, interfaces, system requirements, and tests to ascertain the camera’s image quality on different devices. This series of standards would assist customers, installers, and users in establishing their requirements and determining the appropriate equipment required for their intended application and also provide means of evaluating the performance of the VSS objectively. This will also help in the improvement of surveillance by the individuals, and this will also help in the better investigation by Law enforcement agencies and faster apprehension of criminals, thus contributing to an overall safe society.

The Advantages
These standards are in power with the Internationally prevalent standards, thus taking the safety factors to the global aspect. This will also allow the Indian industry to create world-class products which can be shared all across the globe. This will open India to various opportunities and job avenues, thus opening the world to invest in India. The aspect of Atma Nirbhar Bharat and Digital India will be strengthened to a new level as the nation will be able to deliver products in power with quality in developed countries. The end Indian consumer will benefit the most from these upgraded standards in terms of Digital Televisions, Type ‘C’ USB chargers, and Video surveillance systems, as these impacts the consumers’ daily activities in terms of security and access to information.
- Reduction in Carbon Emission
- Production of World Class components and devices
- Boost to the economy and Atmanirbhar Bharat
- New avenues and opportunities for startups and MSMEs
- Better transmission of Knowledge
- Boosting FDI
- Improved quality of products for the end consumer
- New innovation hubs and exposure to global talents
This government move simply shows how India is working toward securing the Sustainable development Goals (SDG) by United Nations. This clearly shares the message to the world that India is ready for the future and will also be a helping hand to various developing and underdeveloped nations in the times to come.
Conclusion
These standards will significantly contribute towards the reduction of E-Waste and unnecessary accessories for daily use gadgets. This strengthens the reduction in carbon emissions and thus contributes towards the perseverance of the environment and working towards sustainable development goals. Such standards will lead the future towards securing the netizens and their new and evolving digital habits. In the current phase of cyberspace, the most essential aspect of establishing Critical Infrastructure as the same will act as a shield against the threats of cyberspace.


