Navigating the Path to CyberPeace: Insights and Strategies
Featured Blogs
.jpeg)
Introduction
Quantum mechanics is not a new field. It finds its roots in the works of physicists such as Niels Bohr in the 1920s, and has informed the development of technologies like nuclear power in the past. But with developments in science and engineering, we are at the cusp of harnessing quantum mechanics for a new wave of real-world uses in sensing and metrology, computing, networking, security, and more. While at different stages of development, quantum technologies have the potential to revolutionise global security, economic systems, and digital infrastructure. The science is dazzling, but it is equally urgent to start preparing for its broader impact on society, especially regarding privacy and digital security. This article explores quantum computing, its threat to information integrity, and global interdependencies as they exist today, and discusses policy areas that should be addressed.
What Is Quantum Computing?
Classical computers use binary bits (0 or 1) to represent and process information. This binary system forms the base of modern computing. But quantum computers use qubits (quantum bits) as a basic unit, which can exist in multiple states ( 0, 1, both, or with other qubits) simultaneously due to quantum principles like superposition and entanglement. This creates an infinite range of possibilities in information processing and allows quantum machines to perform complex computations at speeds impossible for traditional computers. While still in their early stages, large-scale quantum computers could eventually:
- Break modern encryption systems
- Model complex molecules for drug discovery
- Optimise global logistics and financial systems
- Accelerate AI and machine learning
While this could eventually present significant opportunities in fields such as health innovation, material sciences, climate modelling, and cybersecurity, challenges will continue to arise even before the technology is ready for commercial application. Policymakers must start anticipating their impact.
Threats
Policy solutions surrounding quantum technologies will depend on the pace of development of the elements of the quantum ecosystem. However, the most urgent concerns regarding quantum computing applications are the risk to encryption and the impact on market competition.
1. Cybersecurity Threat: Digital infrastructure today (e.g., cloud services, networks, servers, etc.) across sectors such as government, banking and finance, healthcare, energy, etc., depends on encryption for secure data handling and communications. Threat actors can utilise quantum computers to break this encryption. Widely used asymmetric encryption keys, such as RSA or ECC, are particularly susceptible to being broken. Threat actors could "harvest now, decrypt later”- steal encrypted data now and decrypt it later when quantum capabilities mature. Although AES-256, a symmetric encryption standard, is currently considered resistant to quantum decryption, it only protects data after a secure connection is established through a process that today relies on RSA or ECC. This is why governments and companies are racing to adopt Post- Quantum Cryptography (PQC) and quantum key distribution (QKD) to protect security and privacy in digital infrastructure.
2. Market Monopoly: Quantum computing demands significant investments in infrastructure, talent, and research, which only a handful of countries and companies currently possess. As a result, firms that develop early quantum advantage may gain unprecedented competitive leverage through offerings such as quantum-as-a-service, disrupting encryption-dependent industries, or accelerating innovation in pharmaceuticals, finance, and logistics. This could reinforce the existing power asymmetries in the global digital economy. Given these challenges, proactive and forward-looking policy frameworks are critical.
What Should Quantum Computing Policy Cover?
Commercial quantum computing will transform many industries. Policy will have to be flexible and be developed in iterations to account for fast-paced developments in the field. It will also require enduring international collaboration to effectively address a broad range of concerns, including ethics, security, privacy, competition, and workforce implications.
1. Cybersecurity and Encryption: Quantum policy should prioritise the development and standardisation of quantum-resistant encryption methods. This includes ongoing research into Post-Quantum Cryptography (PQC) algorithms and their integration into digital infrastructure. Global policy will need to align national efforts with international standards to create unified quantum-safe encryption protocols.
2. Market Competition and Access: Given the high barriers to entry, regulatory frameworks should promote fair competition, enabling smaller players like startups and developing economies to participate meaningfully in the quantum economy. Frameworks to ensure equitable access, interoperability, and fair competition will become imperative as the quantum ecosystem matures so that society can reap its benefits as a whole.
4. Ethical Considerations: Policymakers will have to consider the impact on privacy and security, and push for the responsible use of quantum capabilities. This includes ensuring that quantum advances do not contribute to cybercrime, disproportionate surveillance, or human rights violations.
5. International Standard-Setting: Setting benchmarks, shared terminologies, and measurement standards will ensure interoperability and security across diverse stakeholders and facilitate global collaboration in quantum research and infrastructure.
6. Military and Defence Implications: Militarisation of quantum technologies is a growing concern, and national security affairs related to quantum espionage are being urgently explored. Nations will have to develop regulations to protect sensitive data and intellectual property from quantum-enabled attacks.
7. Workforce Development and Education: Policies should encourage quantum computing education at various levels to ensure a steady pipeline of talent and foster cross-disciplinary programs that blend quantum computing with fields like machine learning, AI, and engineering.
8. Environmental and Societal Impact: Quantum computing hardware requires specialised conditions such as extreme cooling. Policy will have to address the environmental footprint of the infrastructure and energy consumption of large-scale quantum systems. Broader societal impacts of quantum computing, including potential job displacement, accessibility issues, and the equitable distribution of quantum computing benefits, will have to be explored.
Conclusion
Like nuclear power and AI, the new wave of quantum technologies is expected to be an exciting paradigm shift for society. While they can bring numerous benefits to commercial operations and address societal challenges, they also pose significant risks to global information security. Quantum policy will require regulatory, strategic, and ethical frameworks to govern the rise of these technologies, especially as they intersect with national security, global competition, and privacy. Policymakers must act in collaboration to mitigate unethical use of these technologies and the entrenchment of digital divides across countries. The OECD’s Anticipatory Governance of Emerging Technologies provides a framework of essential values like respect for human rights, privacy, and sustainable development, which can be used to set a baseline, so that quantum computing and related technologies benefit society as a whole.
References
- https://www.weforum.org/stories/2024/07/explainer-what-is-quantum-technology/
- https://www.paconsulting.com/insights/what-is-quantum-technology
- https://delinea.com/blog/quantum-safe-encryption#:~:text=This%20can%20result%20in%20AES,%2D128%20to%20AES%2D256.
- https://www.oecd.org/en/publications/a-quantum-technologies-policy-primer_fd1153c3-en.html

Introduction
As our experiments with Generative Artificial Intelligence (AI) continue, companies and individuals look for new ways to incorporate and capitalise on it. This also includes big tech companies betting on their potential through investments. This process also sheds light on how such innovations are being carried out, used, and affect other stakeholders. Google’s AI overview feature has raised concerns from various website publishers and regulators. Recently, Chegg, a US-based tech education company that provides online resources for high school and college students, has filed a lawsuit against Google alleging abuse of monopoly over the searching mechanism.
Legal Background
Google’s AI Overview/Search Generative Experience (SGE) is a feature that incorporates AI into its standard search tool and helps summarise search results. This is then presented at the top, over the other published websites, when one looks for the search result. Although the sources of the information present are linked, they are half-covered, and it is ambiguous to tell which claims made by the AI come from which link. This creates an additional step for the searcher as, to find out the latter, their user interface requires the searcher to click on a drop-down box. Individual publishers and companies like Chegg have argued that such summaries deter their potential traffic and lead to losses as they continue to bid higher for advertisement services that Google offers, only to have their target audience discouraged from visiting their websites. What is unique about the lawsuit that has been filed by Chegg, is that it is based on anti-trust law rather than copyright law, which it has dealt with previously. In August 2024, a US Federal Judge had ruled that Google had an illegal monopoly over internet search and search text advertising markets, and by November, the US Department of Justice (DOJ) filed its proposed remedy. Some of them were giving advertisers and publishers more control of their data flowing through Google’s products, opening Google’s search index to the rest of the market, and imposing public oversight over Google’s AI investments. Currently, the DOJ has emphasised its stand on dismantling the search monopoly through structural separations, i.e., divesting Google of Chrome. The company is slated to defend itself before the DC District Court Judge Amit Mehta starting April 20, 2025.
CyberPeace Insights
As per a report by Statista (Global market share of leading search engines 2015-2025), Google, as the market leader, held a search traffic share of around 89.62 per cent. It is also stated that its advertising services account for the majority of its revenue, which amounted to a total of 305.63 billion U.S. dollars in 2023. The inclusion of the AI feature is undoubtedly changing how we search for things online. Benefits for users include an immediate, convenient scan of general information pertaining to the looked-up subject, but it may also raise concerns on the part of the website publishers and their loss of ad revenue owing to fewer impressions/clicks. Even though links (sources) are mentioned, they are usually buried. Such a searching mechanism questions the incentive on both ends- the user to explore various viewpoints, as people are now satisfied with the first few results that pop up, and the incentive for a creator/publisher to create new content as well as generate an income out of it. There might be a shift to more passive consumption rather than an active one, where one looks up/or is genuinely searching for information.
Conclusion
AI might make life more convenient, but in this case, it might also take away from small businesses, their finances, and the results of their hard work. It is also necessary for regulators, publishers, and users to continue asking such critical questions to keep the accountability of big tech giants in check, whilst not compromising their creations and publications.
References
- https://www.washingtonpost.com/technology/2024/05/13/google-ai-search-io-sge/
- https://www.theverge.com/news/619051/chegg-google-ai-overviews-monopoly
- https://economictimes.indiatimes.com/tech/technology/google-leans-further-into-ai-generated-overviews-for-its-search-engine/articleshow/118742139.cms?from=mdr
- https://www.nytimes.com/2024/12/03/technology/google-search-antitrust-judge.html
- https://www.odinhalvorson.com/monopoly-and-misuse-googles-strategic-ai-narrative/
- https://cio.economictimes.indiatimes.com/news/artificial-intelligence/google-leans-further-into-ai-generated-overviews-for-its-search-engine/118748621
- https://www.techpolicy.press/the-elephant-in-the-room-in-the-google-search-case-generative-ai/
- https://www.karooya.com/blog/proposed-remedies-break-googles-monopoly-antitrust/
- https://getellipsis.com/blog/googles-monopoly-and-the-hidden-brake-on-ai-innovation/
- https://www.statista.com/statistics/266249/advertising-revenue-of-google/#:~:text=Google:%20annual%20advertising%20revenue%202001,local%20products%20are%20more%20preferred.
- https://www.statista.com/statistics/1381664/worldwide-all-devices-market-share-of-search-engines/
- https://www.techpolicy.press/doj-sets-record-straight-of-whats-needed-to-dismantle-googles-search-monopoly/

Introduction
The Kerala High Court banned the use of mobile phones during office hours on the 2nd of December 2024, and issued an Official Memorandum titled, ‘Indulgence In Online Gaming And Watching Social Media Content During Office Hours’. This memorandum, issued by the Registrar General, prohibits mobile phone usage for personal activities such as gaming and social media during working hours. This memorandum aims to curb the productivity woes and reinforce professional discipline and further ensure the smooth functioning of the office operations.
The memorandum reiterated its earlier notices from 2009 and 2013, where the High Court had emphasised that violations would be taken seriously. This reflects the High Court’s commitment to maintaining efficiency and professionalism in the workplace. According to the memorandum, controlling officers will monitor the staff for violations and strict actions will be taken if the rules are flouted.
Background
The circumstances that led to the Kerala HC’s decision are as follows: staff engaged in playing online games, browsing social media, watching videos or movies and even engaging in online shopping or trading during work hours, excluding the allocated lunch recess (as per the memorandum).
As mentioned earlier, this memorandum is not the first of its kind. There were similar directives that were issued in 2009 and 2013 to target the poor productivity standards, rooted in the staff members' behaviours. The present memorandum is unlike the previously mentioned ones as, it specifically addresses the rise in mobile-based distractions, like online gaming and trading. The present directive does not outline any exceptions to senior officials with designated responsibilities, and emphasises universal adherence for all levels of the workforce.
According to Cell Phones at Workplace Statistics, around 97% of workers use their smartphones during work hours, mixing personal and job-related activities. And more than 55% of managers say that cell phones are a major reason for lower productivity among employees.
Therefore, it can be safely concluded that even though smartphones have become indispensable tools for communication, their misuse has wider implications for overall organisational productivity.
CyberPeace Outlook
The Kerala High Court's decision to restrict personal mobile phone usage during work hours underscores the importance of fostering a disciplined and focused workplace environment. While smartphones are vital for communication, their misuse poses significant productivity challenges. Some proactive steps that employers can take are implementing clear policies, conducting regular training sessions and promoting a culture of accountability. Balancing digital freedom and professional responsibility is the key to ensuring that technological tools serve as enablers of efficiency rather than distractions in the workplace.
References
- https://www.thehindu.com/sci-tech/technology/kerala-high-court-issues-memo-banning-staff-from-gaming-and-social-media-during-work-hours/article68963949.ece
- https://timesofindia.indiatimes.com/technology/tech-news/kerala-high-court-bans-mobile-gaming-and-social-media-for-staff-during-work-hours/articleshow/116101149.cms
- https://images.assettype.com/barandbench/2024-12-05/1hiq8ffv/Kerala_High_Court_OM.pdf
- https://www.coolest-gadgets.com/cell-phones-at-workplace-statistics/

Introduction
So it's that time of year when you feel bright and excited to start the year with new resolutions; your goals could be anything from going to the gym to learning new skills and being productive this year, but with cybercrime on the rise, you must also be smart and take your New Year Cyber Resolutions seriously. Yes, you heard it right: it's a new year, a new you, but the same hackers with advanced dangers. It's time to make a cyber resolution this year to be secure, smart, and follow the best cyber safety tips for 2K25 and beyond.
Best Cyber Security Tips For You
So while taking your cyber resolutions this 2k25, remember that hackers have resolutions too; so you have to make yours better! CyberPeace has curated a list of great tips and cyber hygiene practices you must practice in 2025:
- Be Aware Of Your Digital Rights: Netizens should be aware of their rights in the digital space. It's important to know where to report issues, how to raise concerns with platforms, and what rights are available to you under applicable IT and Data Protection laws. And as we often say, sharing is caring, so make sure to discuss and share your knowledge of digital rights with your family, peers, and circle. Not only will this help raise awareness, but you’ll also learn from their experiences, collectively empowering yourselves. After all, a well-informed online community is a happy one.
- Awareness Is Your First Line Of Defence: Awareness serves as the first line of defence, especially in light of the lessons learned from 2024, where new forms of cybercrimes have emerged with serious consequences. Scams like digital arrests, romance frauds, lottery scams, and investment scams have become more prevalent. As we move into 2025, remember that sophisticated cyber scams require equally advanced strategies to stay protected. As cybercrimes evolve and become more complex, it's crucial to stay updated with specific strategies and hygiene tips to defend yourself. Build your first line of defence by being aware of these growing scams, and say goodbye to the manipulative tactics used by cyber crooks.
- Customise Social Media Media Profile And Privacy Settings: With the rising misuse of advanced technologies such as deepfake, it’s crucial to share access to your profile only with people you trust and know. Customize your social media profile settings based on your convenience, such as who can add you, who can see your uploaded pictures and stories, and who can comment on your posts. Tailor these settings to suit your needs and preferences, ensuring a safer digital environment for yourself.
- Be Cautious: Choose wisely, just because an online deal seems exciting doesn’t mean it’s legitimate. A single click could have devastating consequences. Not every link leads to a secure website; it could be a malware or phishing attempt. Be cautious and follow basic cyber hygiene tips, such as only visiting websites with a padlock symbol, a secure connection, and the 'HTTPS' status in the URL.
- Don’t Let Fake News Fake You Out: Online misinformation and disinformation have sparked serious concern due to their widespread proliferation. That’s why it’s crucial to 'Spot The Lies Before They Spot You.' Exercise due care and caution when consuming, sharing, or forwarding any online information. Always verify it from trusted sources, recognize the red flags of misleading claims, and contribute to creating a truthful online information landscape.
- Turn the Tables on Cybercriminals: It is crucial to know the proper reporting channels for cybercrimes, including specific reporting methods based on the type of issue. For example, ‘unsolicited commercial communications’ can be reported on the Chakshu portal by the government. Unauthorized electronic transactions can be reported to the RBI toll-free number at 14440, while women can report incidents to the National Commission for Women. If you encounter issues on a platform, you can reach out to the platform's grievance officer. All types of cybercrimes can be reported through the National Cyber Crime Reporting Portal (cybercrime.gov.in) and the helpline at 1930. It’s essential to be aware of the right authorities and reporting mechanisms, so if something goes wrong in your digital experience, you can take action, turn the tables on cybercrooks, and stay informed about official grievances and reporting channels.
- Log Out, Chill Out: The increased use of technology can have far-reaching consequences that are often overlooked, such as procrastination, stress, anxiety, and eye strain (also known as digital eye strain or computer vision syndrome). Sometimes, it’s essential to switch off the digital curtains. This is where a ‘Digital Detox’ comes in, offering a chance to recharge and reset. We’re all aware of how our devices and phones influence our daily lives, shaping our behaviours, decisions, and lifestyles from morning until night, even impacting our sleep. Taking time to unplug can provide a much-needed psychological and physical boost. Practicing a digital detox at regular suitable intervals, such as twice a month, can help restore balance, reduce stress, and improve overall well-being.
Final Words & the Idea of ‘Tech for Good’
Remember that we are in the technological era, and these technologies are created for our ease and convenience. There are certain challenges that bad actors pose, but to counter this, the change starts from you. Remember that technology, while having its risks, also brings tremendous benefits to society. We encourage you to take a step and encourage the responsible and ethical use of the technology. The vision for ‘Tech for Good’ will have to be expanded to a larger picture. Do not engage in a behaviour that you would not ordinarily do in an offline environment, the online environment is also the same and has far-reaching effects. Use technology for good, and follow and encourage ethical and responsible behaviour in online communities. The emphasis should be on using technology in a safer environment for everyone and combatting dishonest practices.
The effective strategies for preventing cybercrime and dishonest practices requires cooperation , efforts by citizens, government agencies, and technology businesses. We intend to employ technology's good aspects to build a digital environment that values security, honesty, and moral behaviour while promoting innovation and connectedness. In 2025, together we can make a cyber safe resilient society.

Disclaimer:
This report is based on extensive research conducted by CyberPeace Research using publicly available information, and advanced analytical techniques. The findings, interpretations, and conclusions presented are based on the data available at the time of study and aim to provide insights into global ransomware trends.
The statistics mentioned in this report are specific to the scope of this research and may vary based on the scope and resources of other third-party studies. Additionally, all data referenced is based on claims made by threat actors and does not imply confirmation of the breach by CyberPeace. CyberPeace includes this detail solely to provide factual transparency and does not condone any unlawful activities. This information is shared only for research purposes and to spread awareness. CyberPeace encourages individuals and organizations to adopt proactive cybersecurity measures to protect against potential threats.
CyberPeace Research does not claim to have identified or attributed specific cyber incidents to any individual, organization, or nation-state beyond the scope of publicly observable activities and available information. All analyses and references are intended for informational and awareness purposes only, without any intention to defame, accuse, or harm any entity.
While every effort has been made to ensure accuracy, CyberPeace Research is not liable for any errors, omissions, subsequent interpretations and any unlawful activities of the findings by third parties. The report is intended to inform and support cybersecurity efforts globally and should be used as a guide to foster proactive measures against cyber threats.
Executive Summary:
The 2024 ransomware landscape reveals alarming global trends, with 166 Threat Actor Groups leveraging 658 servers/underground resources and mirrors to execute 5,233 claims across 153 countries. Monthly fluctuations in activity indicate strategic, cyclical targeting, with peak periods aligned with vulnerabilities in specific sectors and regions. The United States was the most targeted nation, followed by Canada, the UK, Germany, and other developed countries, with the northwestern hemisphere experiencing the highest concentration of attacks. Business Services and Healthcare bore the brunt of these operations due to their high-value data, alongside targeted industries such as Pharmaceuticals, Mechanical, Metal, Electronics, and Government-related professional firms. Retail, Financial, Technology, and Energy sectors were also significantly impacted.
This research was conducted by CyberPeace Research using a systematic modus operandi, which included advanced OSINT (Open-Source Intelligence) techniques, continuous monitoring of Ransomware Group activities, and data collection from 658 servers and mirrors globally. The team utilized data scraping, pattern analysis, and incident mapping to track trends and identify hotspots of ransomware activity. By integrating real-time data and geographic claims, the research provided a comprehensive view of sectoral and regional impacts, forming the basis for actionable insights.
The findings emphasize the urgent need for proactive Cybersecurity strategies, robust defenses, and global collaboration to counteract the evolving and persistent threats posed by ransomware.
Overview:
This report provides insights into ransomware activities monitored throughout 2024. Data was collected by observing 166 Threat Actor Groups using ransomware technologies across 658 servers/underground resources and mirrors, resulting in 5,233 claims worldwide. The analysis offers a detailed examination of global trends, targeted sectors, and geographical impact.
Top 10 Threat Actor Groups:
The ransomware group ‘ransomhub’ has emerged as the leading threat actor, responsible for 527 incidents worldwide. Following closely are ‘lockbit3’ with 522 incidents and ‘play’ with 351. Other Groups are ‘akira’, ‘hunters’, ‘medusa’, ‘blackbasta’, ‘qilin’, ‘bianlian’, ‘incransom’. These groups usually employ advanced tactics to target critical sectors, highlighting the urgent need for robust cybersecurity measures to mitigate their impact and protect organizations from such threats.

Monthly Ransomware Incidents:
In January 2024, the value began at 284, marking the lowest point on the chart. The trend rose steadily in the subsequent months, reaching its first peak at 557 in May 2024. However, after this peak, the value dropped sharply to 339 in June. A gradual recovery follows, with the value increasing to 446 by August. September sees another decline to 389, but a sharp rise occurs afterward, culminating in the year’s highest point of 645 in November. The year concludes with a slight decline, ending at 498 in December 2024 (till 28th of December).

Top 10 Targeted Countries:
- The United States consistently topped the list as the primary target probably due to its advanced economic and technological infrastructure.
- Other heavily targeted nations include Canada, UK, Germany, Italy, France, Brazil, Spain, and India.
- A total of 153 countries reported ransomware attacks, reflecting the global scale of these cyber threats

Top Affected Sectors:
- Business Services and Healthcare faced the brunt of ransomware threat due to the sensitive nature of their operations.
- Specific industries under threats:
- Pharmaceutical, Mechanical, Metal, and Electronics industries.
- Professional firms within the Government sector.
- Other sectors:
- Retail, Financial, Technology, and Energy sectors were also significant targets.

Geographical Impact:
The continuous and precise OSINT(Open Source Intelligence) work on the platform, performed as a follow-up action to data scraping, allows a complete view of the geography of cyber attacks based on their claims. The northwestern region of the world appears to be the most severely affected by Threat Actor groups. The figure below clearly illustrates the effects of this geographic representation on the map.

Ransomware Threat Trends in India:
In 2024, the research identified 98 ransomware incidents impacting various sectors in India, marking a 55% increase compared to the 63 incidents reported in 2023. This surge highlights a concerning trend, as ransomware groups continue to target India's critical sectors due to its growing digital infrastructure and economic prominence.

Top Threat Actors Group Targeted India:
Among the following threat actors ‘killsec’ is the most frequent threat. ‘lockbit3’ follows as the second most prominent threat, with significant but lower activity than killsec. Other groups, such as ‘ransomhub’, ‘darkvault’, and ‘clop’, show moderate activity levels. Entities like ‘bianlian’, ‘apt73/bashe’, and ‘raworld’ have low frequencies, indicating limited activity. Groups such as ‘aps’ and ‘akira’ have the lowest representation, indicating minimal activity. The chart highlights a clear disparity in activity levels among these threats, emphasizing the need for targeted cybersecurity strategies.

Top Impacted Sectors in India:
The pie chart illustrates the distribution of incidents across various sectors, highlighting that the industrial sector is the most frequently targeted, accounting for 75% of the total incidents. This is followed by the healthcare sector, which represents 12% of the incidents, making it the second most affected. The finance sector accounts for 10% of the incidents, reflecting a moderate level of targeting. In contrast, the government sector experiences the least impact, with only 3% of the incidents, indicating minimal targeting compared to the other sectors. This distribution underscores the critical need for enhanced cybersecurity measures, particularly in the industrial sector, while also addressing vulnerabilities in healthcare, finance, and government domains.

Month Wise Incident Trends in India:
The chart indicates a fluctuating trend with notable peaks in May and October, suggesting potential periods of heightened activity or incidents during these months. The data starts at 5 in January and drops to its lowest point, 2, in February. It then gradually increases to 6 in March and April, followed by a sharp rise to 14 in May. After peaking in May, the metric significantly declines to 4 in June but starts to rise again, reaching 7 in July and 8 in August. September sees a slight dip to 5 before the metric spikes dramatically to its highest value, 24, in October. Following this peak, the count decreases to 10 in November and then drops further to 7 in December.

CyberPeace Advisory:
- Implement Data Backup and Recovery Plans: Backups are your safety net. Regularly saving copies of your important data ensures you can bounce back quickly if ransomware strikes. Make sure these backups are stored securely—either offline or in a trusted cloud service—to avoid losing valuable information or facing extended downtime.
- Enhance Employee Awareness and Training: People often unintentionally open the door to ransomware. By training your team to spot phishing emails, social engineering tricks, and other scams, you empower them to be your first line of defense against attacks.
- Adopt Multi-Factor Authentication (MFA): Think of MFA as locking your door and adding a deadbolt. Even if attackers get hold of your password, they’ll still need that second layer of verification to break in. It’s an easy and powerful way to block unauthorized access.
- Utilize Advanced Threat Detection Tools: Smart tools can make a world of difference. AI-powered systems and behavior-based monitoring can catch ransomware activity early, giving you a chance to stop it in its tracks before it causes real damage.
- Conduct Regular Vulnerability Assessments: You can’t fix what you don’t know is broken. Regularly checking for vulnerabilities in your systems helps you identify weak spots. By addressing these issues proactively, you can stay one step ahead of attackers.
Conclusion:
The 2024 ransomware landscape reveals the critical need for proactive cybersecurity strategies. High-value sectors and technologically advanced regions remain the primary targets, emphasizing the importance of robust defenses. As we move into 2025, it is crucial to anticipate the evolution of ransomware tactics and adopt forward-looking measures to address emerging threats.
Global collaboration, continuous innovation in cybersecurity technologies, and adaptive strategies will be imperative to counteract the persistent and evolving threats posed by ransomware activities. Organizations and governments must prioritize preparedness and resilience, ensuring that lessons learned in 2024 are applied to strengthen defenses and minimize vulnerabilities in the year ahead.

Introduction
In September 2024, the Australian government announced the Communications Legislation Amendment (Combatting Misinformation and Disinformation) Bill 2024 ( CLA Bill 2024 hereon), to provide new powers to the Australian Communications and Media Authority (ACMA), the statutory regulatory body for Australia's communications and media infrastructure, to combat online misinformation and disinformation. It proposed allowing the ACMA to hold digital platforms accountable for the “seriously harmful mis- and disinformation” being spread on their platforms and their response to it, while also balancing freedom of expression. However, the Bill was subsequently withdrawn, primarily over concerns regarding the possibility of censorship by the government. This development is reflective of the global contention on the balance between misinformation regulation and freedom of speech.
Background and Key Features of the Bill
According to the BBC’s Global Minds Survey of 2023, nearly 73% of Australians struggled to identify fake news and AI-generated misinformation. There has been a substantial rise in misinformation on platforms like Facebook, Twitter, and TikTok since the COVID-19 pandemic, especially during major events like the bushfires of 2020 and the 2022 federal elections. The government’s campaign against misinformation was launched against this background, with the launch of The Australian Code of Practice on Disinformation and Misinformation in 2021. The main provisions of the CLA Bill, 2024 were:
- Core Transparency Obligations of Digital Media Platforms: Publishing current media literacy plans, risk assessment reports, and policies or information on their approach to addressing mis- and disinformation. The ACMA would also be allowed to make additional rules regarding complaints and dispute-handling processes.
- Information Gathering and Record-Keeping Powers: The ACMA would form rules allowing it to gather consistent information across platforms and publish it. However, it would not have been empowered to gather and publish user information except in limited circumstances.
- Approving Codes and Making Standards: The ACMA would have powers to approve codes developed by the industry and make standards regarding reporting tools, links to authoritative information, support for fact-checking, and demonetisation of disinformation. This would make compliance mandatory for relevant sections of the industry.
- Parliamentary Oversight: The transparency obligations, codes approved and standards set by ACMA under the Bill would be subject to parliamentary scrutiny and disallowance. ACMA would be required to report to the Parliament annually.
- Freedom of Speech Protections: End-users would not be required to produce information for ACMA unless they are a person providing services to the platform, such as its employees or fact-checkers. Further, it would not be allowed to call for removing content from platforms unless it involved inauthentic behavior such as bots.
- Penalties for Non-Compliance: ACMA would be required to employ a “graduated, proportionate and risk-based approach” to non-compliance and enforcement in the form of formal warnings, remedial directions, injunctions, or significant civil penalties as decided by the courts, subject to review by the Administrative Review Tribunal (ART). No criminal penalties would be imposed.
Key Concerns
- Inadequacy of Freedom of Speech Protections: The biggest contention on this Bill has been regarding the issue of possible censorship, particularly of alternative opinions that are crucial to the health of a democratic system. To protect the freedom of speech, the Bill defined mis- and disinformation, what constitutes “serious harm” (election interference, harming public health, etc.), and what would be excluded from its scope. However, reservations among the Opposition persisted due to the lack of a clear mechanism to protect divergent opinions from the purview of this Bill.
- Efficacy of Regulatory Measures: Many argue that by allowing the digital platform industry to make its codes, this law lets it self-police. Big Tech companies have no incentive to curb misinformation effectively since their business models allow them to reap financial benefits from the rampant spread of misinformation. Unless there are financial non- or dis- incentives to curb misinformation, Big Tech is not likely to address the situation at war footing. Thus, this law would run the risk of being toothless. Secondly, the Bill did not require platforms to report on the “prevalence of” false content which, along with other metrics, is crucial for researchers and legislators to track the efficacy of the current misinformation-curbing practices employed by platforms.
- Threat of Government Overreach: The Bill sought to expand the ACMA’s compliance and enforcement powers concerning misinformation and disinformation on online communication platforms by giving it powers to form rules on information gathering, code registration, standard-making powers, and core transparency obligations. However, even though the ACMA as a regulatory authority is answerable to the Parliament, the Bill was unclear in defining limits to these powers. This raised concerns from civil society about potential government overreach in a domain filled with contextual ambiguities regarding information.
Conclusion
While the Communications Legislation Amendment (Combatting Misinformation and Disinformation) Bill sought to equip the ACMA with tools to hold digital platforms accountable and mitigate the harm caused by false information, its critique highlights the complexities of regulating such content without infringing on freedom of speech. Legislations and proposals regarding the matter all over the world are having to contend with this challenge. Globally, legislation and proposals addressing this issue face similar challenges, emphasizing the need for a continuous discourse at the intersection of platform accountability, regulatory restraint, and the protection of diverse viewpoints.
To regulate Big Tech effectively, governments can benefit from adopting a consultative, incremental, and cooperative approach, as exemplified by the European Union’s Digital Services Act 2023. Such a framework provides for a balanced response, fostering accountability while safeguarding democratic freedoms.
Resources
- https://www.infrastructure.gov.au/sites/default/files/documents/factsheet-misinformation-disinformation-bill.pdf
- https://www.infrastructure.gov.au/have-your-say/new-acma-powers-combat-misinformation-and-disinformation
- https://www.mi-3.com.au/07-02-2024/over-80-australians-feel-they-may-have-fallen-fake-news-says-bbc
- https://www.hrlc.org.au/news/misinformation-inquiry
- https://humanrights.gov.au/our-work/legal/submission/combatting-misinformation-and-disinformation-bill-2024
- https://www.sbs.com.au/news/article/what-is-the-misinformation-bill-and-why-has-it-triggered-worries-about-freedom-of-speech/4n3ijebde
- https://www.hrw.org/report/2023/06/14/no-internet-means-no-work-no-pay-no-food/internet-shutdowns-deny-access-basic#:~:text=The%20Telegraph%20Act%20allows%20authorities,preventing%20incitement%20to%20the%20commission
- https://www.hrlc.org.au/submissions/2024/11/8/submission-combatting-misinformation?utm_medium=email&utm_campaign=Media%20Release%20Senate%20Committee%20to%20hear%20evidence%20calling%20for%20Albanese%20Government%20to%20regulate%20and%20hold%20big%20tech%20accountable%20for%20misinformation&utm_content=Media%20Release%20Senate%20Committee%20to%20hear%20evidence%20calling%20for%20Albanese%20Government%20to%20regulate%20and%20hold%20big%20tech%20accountable%20for%20misinformation+Preview+CID_31c6d7200ed9bd2f7f6f596ba2a8b1fb&utm_source=Email%20campaign&utm_term=Read%20the%20Human%20Rights%20Law%20Centres%20submission%20to%20the%20inquiry
.webp)
Executive Summary
This report analyses a recently launched social engineering attack that took advantage of Microsoft Teams and AnyDesk to deliver DarkGate malware, a MaaS tool. This way, through Microsoft Teams and by tricking users into installing AnyDesk, attackers received unauthorized remote access to deploy DarkGate that offers such features as credential theft, keylogging, and fileless persistence. The attack was executed using obfuscated AutoIt scripts for the delivery of malware which shows how threat actors are changing their modus operandi. The case brings into focus the need to put into practice preventive security measures for instance endpoint protection, staff awareness, limited utilization of off-ice-connection tools, and compartmentalization to safely work with the new and increased risks that contemporary cyber threats present.
Introduction
Hackers find new technologies and application that are reputable for spreading campaigns. The latest use of Microsoft Teams and AnyDesk platforms for launching the DarkGate malware is a perfect example of how hackers continue to use social engineering and technical vulnerabilities to penetrate the defenses of organizations. This paper focuses on the details of the technical aspect of the attack, the consequences of the attack together with preventive measures to counter the threat.
Technical Findings
1. Attack Initiation: Exploiting Microsoft Teams
The attackers leveraged Microsoft Teams as a trusted communication platform to deceive victims, exploiting its legitimacy and widespread adoption. Key technical details include:
- Spoofed Caller Identity: The attackers used impersonation techniques to masquerade as representatives of trusted external suppliers.
- Session Hijacking Risks: Exploiting Microsoft Teams session vulnerabilities, attackers aimed to escalate their privileges and deploy malicious payloads.
- Bypassing Email Filters: The initial email bombardment was designed to overwhelm spam filters and ensure that malicious communication reached the victim’s inbox.
2. Remote Access Exploitation: AnyDesk
After convincing victims to install AnyDesk, the attackers exploited the software’s functionality to achieve unauthorized remote access. Technical observations include:
- Command and Control (C2) Integration: Once installed, AnyDesk was configured to establish persistent communication with the attacker’s C2 servers, enabling remote control.
- Privilege Escalation: Attackers exploited misconfigurations in AnyDesk to gain administrative privileges, allowing them to disable antivirus software and deploy payloads.
- Data Exfiltration Potential: With full remote access, attackers could silently exfiltrate data or install additional malware without detection.
3. Malware Deployment: DarkGate Delivery via AutoIt Script
The deployment of DarkGate malware utilized AutoIt scripting, a programming language commonly used for automating Windows-based tasks. Technical details include:
- Payload Obfuscation: The AutoIt script was heavily obfuscated to evade signature-based antivirus detection.
- Process Injection: The script employed process injection techniques to embed DarkGate into legitimate processes, such as explorer.exe or svchost.exe, to avoid detection.
- Dynamic Command Loading: The malware dynamically fetched additional commands from its C2 server, allowing real-time adaptation to the victim’s environment.
4. DarkGate Malware Capabilities
DarkGate, now available as a Malware-as-a-Service (MaaS) offering, provides attackers with advanced features. Technical insights include:
- Credential Dumping: DarkGate used the Mimikatz module to extract credentials from memory and secure storage locations.
- Keylogging Mechanism: Keystrokes were logged and transmitted in real-time to the attacker’s server, enabling credential theft and activity monitoring.
- Fileless Persistence: Utilizing Windows Management Instrumentation (WMI) and registry modifications, the malware ensured persistence without leaving traditional file traces.
- Network Surveillance: The malware monitored network activity to identify high-value targets for lateral movement within the compromised environment.
5. Attack Indicators
Trend Micro researchers identified several indicators of compromise (IoCs) associated with the DarkGate campaign:
- Suspicious Domains: example-remotesupport[.]com and similar domains used for C2 communication.
- Malicious File Hashes:some text
- AutoIt Script: 5a3f8d0bd6c91234a9cd8321a1b4892d
- DarkGate Payload: 6f72cde4b7f3e9c1ac81e56c3f9f1d7a
- Behavioral Anomalies:some text
- Unusual outbound traffic to non-standard ports.
- Unauthorized registry modifications under HKCU\Software\Microsoft\Windows\CurrentVersion\Run.
Broader Cyber Threat Landscape
In parallel with this campaign, other phishing and malware delivery tactics have been observed, including:
- Cloud Exploitation: Abuse of platforms like Cloudflare Pages to host phishing sites mimicking Microsoft 365 login pages.
- Quishing Campaigns: Phishing emails with QR codes that redirect users to fake login pages.
- File Attachment Exploits: Malicious HTML attachments embedding JavaScript to steal credentials.
- Mobile Malware: Distribution of malicious Android apps capable of financial data theft.
Implications of the DarkGate Campaign
This attack highlights the sophistication of threat actors in leveraging legitimate tools for malicious purposes. Key risks include:
- Advanced Threat Evasion: The use of obfuscation and process injection complicates detection by traditional antivirus solutions.
- Cross-Platform Risk: DarkGate’s modular design enables its functionality across diverse environments, posing risks to Windows, macOS, and Linux systems.
- Organizational Exposure: The compromise of a single endpoint can serve as a gateway for further network exploitation, endangering sensitive organizational data.
Recommendations for Mitigation
- Enable Advanced Threat Detection: Deploy endpoint detection and response (EDR) solutions to identify anomalous behavior like process injection and dynamic command loading.
- Restrict Remote Access Tools: Limit the use of tools like AnyDesk to approved use cases and enforce strict monitoring.
- Use Email Filtering and Monitoring: Implement AI-driven email filtering systems to detect and block email bombardment campaigns.
- Enhance Endpoint Security: Regularly update and patch operating systems and applications to mitigate vulnerabilities.
- Educate Employees: Conduct training sessions to help employees recognize and avoid phishing and social engineering tactics.
- Implement Network Segmentation: Limit the spread of malware within an organization by segmenting high-value assets.
Conclusion
Using Microsoft Teams and AnyDesk to spread DarkGate malware shows the continuous growth of the hackers’ level. The campaign highlights how organizations have to start implementing adequate levels of security preparedness to threats, including, Threat Identification, Training employees, and Rights to Access.
The DarkGate malware is a perfect example of how these attacks have developed into MaaS offerings, meaning that the barrier to launch highly complex attacks is only decreasing, which proves once again why a layered defense approach is crucial. Both awareness and flexibility are still the key issues in addressing the constantly evolving threat in cyberspace.
Reference:

2025 is knocking firmly at our door and we have promises to make and resolutions to keep. Time you make your list for the New Year and check it twice.
- Lifestyle targets 🡪 Check
- Family targets 🡪 Check
- Social targets 🡪 Check
Umm, so far so good, but what about your cybersecurity targets for the year? Hey, you look confused and concerned. Wait a minute, you do not have one, do you?
I get it. Though the digital world still puzzles, and sometimes outright scares us, we still are not in the ‘Take-Charge-Of-Your-Digital-Safety Mode. We prefer to depend on whatever software security we are using and keep our fingers crossed that the bad guys (read threat actors) do not find us.
Let me illustrate why cybersecurity should be one of your top priorities. You know that stress is a major threat to our continued good health, right? However, if your devices, social media accounts, office e-mail or network, or God forbid, bank accounts become compromised, would that not cause stress? Think about it and the probable repercussions and you will comprehend why I am harping on prioritising security.
Fret not. We will keep it brief as we well know you have 101 things to do in the next few days leading up to 01/01/2025. Just add cyber health to the list and put in motion the following:
- Install and activate comprehensive security software on ALL internet-enabled devices you have at home. Yes, including your smartphones.
- Set yourself a date to change and create separate unique passwords for all accounts. Or use the password manager that comes with all reputed security software to make life simpler.
- Keep home Wi-Fi turned off at night
- Do not set social media accounts to auto-download photos/documents
- Activate parental controls on all the devices used by your children to monitor and mentor them. But keep them apprised.
- Do not blindly trust anyone or anything online – this includes videos, speeches, emails, voice calls, and video calls. Be aware of fakes.
- Be aware of the latest threats and talk about unsafe cyber practices and behaviour often at home.
Short and sweet, as promised.
We will be back, with more tips, and answers to your queries. Drop us a line anytime, and we will be happy to resolve your doubts.
Ciao!
.webp)
Executive Summary:
A viral online video claims to show a Syrian prisoner experiencing sunlight for the first time in 13 years. However, the CyberPeace Research Team has confirmed that the video is a deep fake, created using AI technology to manipulate the prisoner’s facial expressions and surroundings. The original footage is unrelated to the claim that the prisoner has been held in solitary confinement for 13 years. The assertion that this video depicts a Syrian prisoner seeing sunlight for the first time is false and misleading.

Claim A viral video falsely claims that a Syrian prisoner is seeing sunlight for the first time in 13 years.


Factcheck:
Upon receiving the viral posts, we conducted a Google Lens search on keyframes from the video. The search led us to various legitimate sources featuring real reports about Syrian prisoners, but none of them included any mention of such an incident. The viral video exhibited several signs of digital manipulation, prompting further investigation.

We used AI detection tools, such as TrueMedia, to analyze the video. The analysis confirmed with 97.0% confidence that the video was a deepfake. The tools identified “substantial evidence of manipulation,” particularly in the prisoner’s facial movements and the lighting conditions, both of which appeared artificially generated.


Additionally, a thorough review of news sources and official reports related to Syrian prisoners revealed no evidence of a prisoner being released from solitary confinement after 13 years, or experiencing sunlight for the first time in such a manner. No credible reports supported the viral video’s claim, further confirming its inauthenticity.
Conclusion:
The viral video claiming that a Syrian prisoner is seeing sunlight for the first time in 13 years is a deep fake. Investigations using tools like Hive AI detection confirm that the video was digitally manipulated using AI technology. Furthermore, there is no supporting information in any reliable sources. The CyberPeace Research Team confirms that the video was fabricated, and the claim is false and misleading.
- Claim: Syrian prisoner sees sunlight for the first time in 13 years, viral on social media.
- Claimed on: Facebook and X(Formerly Twitter)
- Fact Check: False & Misleading

Executive Summary:
A post on X (formerly Twitter) featuring an image that has been widely shared with misleading captions, claiming to show men riding an elephant next to a tiger in Bihar, India. This post has sparked both fascination and skepticism on social media. However, our investigation has revealed that the image is misleading. It is not a recent photograph; rather, it is a photo of an incident from 2011. Always verify claims before sharing.

Claims:
An image purporting to depict men riding an elephant next to a tiger in Bihar has gone viral, implying that this astonishing event truly took place.

Fact Check:
After investigation of the viral image using Reverse Image Search shows that it comes from an older video. The footage shows a tiger that was shot after it became a man-eater by forest guard. The tiger killed six people and caused panic in local villages in the Ramnagar division of Uttarakhand in January, 2011.

Before sharing viral posts, take a brief moment to verify the facts. Misinformation spreads quickly and it’s far better to rely on trusted fact-checking sources.
Conclusion:
The claim that men rode an elephant alongside a tiger in Bihar is false. The photo presented as recent actually originates from the past and does not depict a current event. Social media users should exercise caution and verify sensational claims before sharing them.
- Claim: The video shows people casually interacting with a tiger in Bihar
- Claimed On:Instagram and X (Formerly Known As Twitter)
- Fact Check: False and Misleading

The United Nations in December 2019 passed a resolution that established an open-ended ad hoc committee. This committee was tasked to develop a ‘comprehensive international convention on countering the use of ICTs for criminal purposes’. The UN Convention on Cybercrime is an initiative of the UN member states to foster the principles of international cooperation and establish legal frameworks to provide mechanisms for combating cybercrime. The negotiations for the convention had started in early 2022. It became the first binding international criminal justice treaty to have been negotiated in over 20 years upon its adoption by the UN General Assembly.
This convention addresses the limitations of the Budapest Convention on Cybercrime by encircling a broader range of issues and perspectives from the member states. The UN Convention against Cybercrime will open for signature at a formal ceremony hosted in Hanoi, Viet Nam, in 2025. The convention will finally enter into force 90 days after being ratified by the 40th signatory.
Objectives and Features of the Convention
- The UN Convention against Cybercrime addresses various aspects of cybercrime. These include prevention, investigation, prosecution and international cooperation.
- The convention aims to establish common standards for criminalising cyber offences. These include offences like hacking, identity theft, online fraud, distribution of illegal content, etc. It outlines procedural and technical measures for law enforcement agencies for effective investigation and prosecution while ensuring due process and privacy protection.
- Emphasising the importance of cross-border collaboration among member states, the convention provides mechanisms for mutual legal assistance, extradition and sharing of information and expertise. The convention aims to enhance the capacity of developing countries to combat cybercrime through technical assistance, training, and resources.
- It seeks to balance security measures with the protection of fundamental rights. The convention highlights the importance of safeguarding human rights and privacy in cybercrime investigations and enforcement.
- The Convention emphasises the importance of prevention through awareness campaigns, education, and the promotion of a culture of cybersecurity. It encourages collaborations through public-private partnerships to enhance cybersecurity measures and raise awareness, such as protecting vulnerable groups like children, from cyber threats and exploitation.
Key Provisions of the UN Cybercrime Convention
Some key provisions of the Convention are as follows:
- The convention differentiates cyber-dependent crimes like hacking from cyber-enabled crimes like online fraud. It defines digital evidence and establishes standards for its collection, preservation, and admissibility in legal proceedings.
- It defines offences against confidentiality, integrity, and availability of computer data and includes unauthorised access, interference with data, and system sabotage. Further, content-related offences include provisions against distributing illegal content, such as CSAM and hate speech. It criminalises offences like identity theft, online fraud and intellectual property violations.
- LEAs are provided with tools for electronic surveillance, data interception, and access to stored data, subject to judicial oversight. It outlines the mechanisms for cross-border investigations, extradition, and mutual legal assistance.
- The establishment of a central body to coordinate international efforts, share intelligence, and provide technical assistance includes the involvement of experts from various fields to advise on emerging threats, legal developments, and best practices.
Comparisons with the Budapest Convention
The Budapest Convention was adopted by the Committee of Ministers of the Council of Europe at the 109th Session on 8 November 2001. This Convention was the first international treaty that addressed internet and computer crimes. A comparison between the two Conventions is as follows:
- The global participation in the UNCC is inclusive of all UN member states whereas the latter had primarily European with some non-European signatories.
- The scope of the UNCC is broader and covers a wide range of cyber threats and cybercrimes, whereas the Budapest convention is focused on specific offences like hacking and fraud.
- UNCC strongly focuses on privacy and human rights protections and the Budapest Convention had limited focus on human rights.
- UNCC has extensive provisions for assistance to developing countries and this is in contrast to the Budapest Convention which did not focus much on capacity building.
Future Outlook
The development of the UNCC was a complex process. The diverse views on key issues have been noted and balancing different legal systems, cultural perspectives and policy priorities has been a challenge. The rapid technology evolution that is taking place requires the Convention to be adaptable to effectively address emerging cyber threats. Striking a balance remains a critical concern. The Convention aims to provide a blended approach to tackling cybercrime by addressing the needs of countries, both developed and developing.
Conclusion
The resolution containing the UN Convention against Cybercrime is a step in global cooperation to combat cybercrime. It was adopted without a vote by the 193-member General Assembly and is expected to enter into force 90 days after ratification by the 40th signatory. The negotiations and consultations are finalised for the Convention and it is open for adoption and ratification by member states. It seeks to provide a comprehensive legal framework that addresses the challenges posed by cyber threats while respecting human rights and promoting international collaboration.
References
- https://consultation.dpmc.govt.nz/un-cybercrime-convention/principlesandobjectives/supporting_documents/Background.pdf
- https://news.un.org/en/story/2024/12/1158521
- https://www.interpol.int/en/News-and-Events/News/2024/INTERPOL-welcomes-adoption-of-UN-convention-against-cybercrime#:~:text=The%20UN%20convention%20establishes%20a,and%20grooming%3B%20and%20money%20laundering
- https://www.cnbctv18.com/technology/united-nations-adopts-landmark-global-treaty-to-combat-cybercrime-19529854.htm

Introduction
Google’s search engine is widely known for its ability to tailor its search results based on user activity, enhancing the relevance of search outcomes. Recently, Google introduced the ‘Try Without Personalisation’ feature. This feature allows users to view results independent of their prior activity. This change marks a significant shift in platform experiences, offering users more control over their search experience while addressing privacy concerns.
However, even in this non-personalised mode, certain contextual factors including location, language, and device type, continue to influence results. This essentially provides the search with a baseline level of relevance. This feature carries significant policy implications, particularly in the areas of privacy, consumer rights, and market competition.
Understanding the Feature
When users engage with this option of non-personalised search, it will no longer show them helpful individual results that are personalisation-dependent and will instead provide unbiased search results. Essentially,this feature provides users with neutral (non-personalised) search results by bypassing their data.
This feature allows the following changes:
- Disables the user’s ability to find past searches in Autofill/Autocomplete.
- Does not pause or delete stored activity within a user’s Google account. Users, because of this feature, will be able to pause or delete stored activity through data and privacy controls.
- The feature doesn't delete or disable app/website preferences like language or search settings are some of the unaffected preferences.
- It also does not disable or delete the material that users save.
- When a user is signed in, they can ‘turn off the personalisation’ by clicking on the search option at the end of the webpage. These changes, offered by the feature, in functionality, have significant implications for privacy, competition, and user trust.
Policy Implications: An Analysis
This feature aligns with global privacy frameworks such as the GDPR in the EU and the DPDP Act in India. By adhering to principles like data minimisation and user consent, it offers users control over their data and the choice to enable or disable personalisation, thereby enhancing user autonomy and trust.
However, there is a trade-off between user expectations for relevance and the impartiality of non-personalised results. Additionally, the introduction of such features may align with emerging regulations on data usage, transparency, and consent. Policymakers play a crucial role in encouraging innovations like these while ensuring they safeguard user rights and maintain a competitive market.
Conclusion and Future Outlook
Google's 'Try Without Personalisation' feature represents a pivotal moment for innovation by balancing user privacy with search functionality. By aligning with global privacy frameworks such as the GDPR and the DPDP Act, it empowers users to control their data while navigating the complex interplay between relevance and neutrality. However, its success hinges on overcoming technical hurdles, fostering user understanding, and addressing competitive and regulatory scrutiny. As digital platforms increasingly prioritise transparency, such features could redefine user expectations and regulatory standards in the evolving tech ecosystem.
References

Introduction
Netflix is no stranger to its subscribers being targeted by SMS and email-led phishing campaigns. But the most recent campaign has been deployed at a global scale, affecting paid users in as many as 23 countries according to cybersecurity firm Bitdefender. In this particular campaign, attackers are using the carrot-and-stick tactic of either creating a false sense of urgency or promising rewards to steal financial information and Netflix credentials. For example, users may be contacted via SMS and told that their account is being suspended due to payment failures. A fake website may be shared through a link, encouraging the individual to share sensitive information to restore their account. Once this information has been input, it is now accessible to the attackers. This can create significant stress and even financial loss for its users. Thus, they are encouraged to develop the necessary skills to recognize and respond to these threats effectively.
How The Netflix Scam Works
Users are typically contacted through SMS. Bitdefender reports that these messages may look something like this:
"NETFLIX: There was an issue processing your payment. To keep your services active, please sign in and confirm your details at: https://account-details[.]com"
On clicking the link, the victim is directed to a website designed to mimic an authentic user experience interface, containing Netflix’s logo, color scheme, and grammatically-correct text. The website uses this interface to encourage the victim to divulge sensitive personal information, such as account credentials and payment details. Since this is a phishing website, the user’s personal information becomes accessible to the attacker as soon as it is entered. This information is then sold individually or in bundles on the dark web.
Practical Steps to Stay Safe
- Know Netflix’s Customer Interface: According to Netflix, it will never ask users to share personal information including credit or debit card numbers, bank account details, and Netflix passwords. It will also never ask for payment through a third-party vendor or website.
- Verify Authenticity: Do not open links from unknown sources sent by email or sms. If unsure, access Netflix directly by typing the URL into the browser instead of clicking on links in emails or texts. If the link has been opened, do not enter any information.
- Use Netflix’s Official Support Channels: Confirm any suspicious communication through Netflix’s verified help page or app. Write to phishing@netflix.com with any complaints about such an issue.
- Contact Your Financial Institution: If you have entered your personal information into a phishing website, you should immediately reach out to your bank to block your card and change your Netflix password. Contact the authorities via www.cybercrime.gov.in or by calling the helpline at 1930 in case of loss of funds.
- Use Strong Passwords and Enable MFA/2FA: Users are advised to use a unique, strong password with multiple characters. Enable Multi-Factor Authentication or Two Factor Authentication to your accounts, if available, to add an extra level of security.
Conclusion
Phishing campaigns which are designed to gather customer data through fraudulent means often involve sending links to as many users as possible, with the aim of monetizing stolen information. Attackers exploit user trust in online platforms to steal sensitive personal information, making such campaigns more sophisticated as highlighted above. This underscores the need for users of online platforms to practice good cyber hygiene by verifying information, learning to detect suspicious information and ignoring it, and staying aware of the types of online fraud they may be exposed to.
Sources
- https://www.bitdefender.com/en-gb/blog/hotforsecurity/netflix-scam-stay-safe
- https://help.netflix.com/en/node/65674
- https://timesofindia.indiatimes.com/technology/tech-news/netflix-users-beware-this-netflix-subscription-scam-is-active-in-23-countries-how-to-spot-one-and-stay-safe/articleshow/115820070.cms

Executive Summary:
QakBot, a particular kind of banking trojan virus, is capable of stealing personal data, banking passwords, and session data from a user's computer. Since its first discovery in 2009, Qakbot has had substantial modifications.
C2 Server commands infected devices and receives stolen data, which is essentially the brain behind Qakbot's operations.Qakbot employs PEDLL (Communication Files), a malicious program, to interact with the server in order to accomplish its main goals. Sensitive data, including passwords or personal information, is taken from the victims and sent to the C2 server. Referrer files start the main line of communication between Qakbot and the C2 server, such as phishing papers or malware droppers. WHOIS data includes registration details for this server, which helps to identify its ownership or place of origin.
This report specifically focuses on the C2 server infrastructure located in India, shedding light on its architecture, communication patterns, and threat landscape.
Introduction:
QakBot is also known as Pinkslipbot, QuakBot, and QBot, capable of stealing personal data, banking passwords, and session data from a user's computer. Malware is bad since it spreads very quickly to other networks, affecting them like a worm.,It employs contemporary methods like web injection to eavesdrop on customer online banking interactions. Qakbot is a member of a kind of malware that has robust persistence techniques, which are said to be the most advanced in order to gain access to compromised computers for extended periods of time.
Technical Analysis:
The following IP addresses have been confirmed as active C2 servers supporting Qbot malware activity:

Sample IP's
- 123.201.40[.]112
- 117.198.151[.]182
- 103.250.38[.]115
- 49.33.237[.]65
- 202.134.178[.]157
- 124.123.42[.]115
- 115.96.64[.]9
- 123.201.44[.]86
- 117.202.161[.]73
- 136.232.254[.]46
These servers have been operational in the past 14 days (report created in the month of Nov) and are being leveraged to perpetuate malicious activities globally.
URL/IP: 123.201.40[.]112

- inetnum: 123.201.32[.]0 - 123.201.47[.]255
- netname: YOUTELE
- descr: YOU Telecom India Pvt Ltd
- country: IN
- admin-c: HA348-AP
- tech-c: NI23-AP
- status: ASSIGNED NON-PORTABLE
- mnt-by: MAINT-IN-YOU
- last-modified: 2022-08-16T06:43:19Z
- mnt-irt: IRT-IN-YOU
- source: APNIC
- irt: IRT-IN-YOU
- address: YOU Broadband India Limited
- address: 2nd Floor, Millennium Arcade
- address: Opp. Samarth Park, Adajan-Hazira Road
- address: Surat-395009,Gujarat
- address: India
- e-mail: abuse@youbroadband.co.in
- abuse-mailbox: abuse@youbroadband.co.in
- admin-c: HA348-AP
- tech-c: NI23-AP
- auth: # Filtered
- mnt-by: MAINT-IN-YOU
- last-modified: 2022-08-08T10:30:51Z
- source: APNIC
- person: Harindra Akbari
- nic-hdl: HA348-AP
- e-mail: harindra.akbari@youbroadband.co.in
- address: YOU Broadband India Limited
- address: 2nd Floor, Millennium Arcade
- address: Opp. Samarth Park, Adajan-Hazira Road
- address: Surat-395009,Gujarat
- address: India
- phone: +91-261-7113400
- fax-no: +91-261-2789501
- country: IN
- mnt-by: MAINT-IN-YOU
- last-modified: 2022-08-10T11:01:47Z
- source: APNIC
- person: NOC IQARA
- nic-hdl: NI23-AP
- e-mail: network@youbroadband.co.in
- address: YOU Broadband India Limited
- address: 2nd Floor, Millennium Arcade
- address: Opp. Samarth Park, Adajan-Hazira Road
- address: Surat-395009,Gujarat
- address: India
- phone: +91-261-7113400
- fax-no: +91-261-2789501
- country: IN
- mnt-by: MAINT-IN-YOU
- last-modified: 2022-08-08T10:18:09Z
- source: APNIC
- route: 123.201.40.0/24
- descr: YOU Broadband & Cable India Ltd.
- origin: AS18207
- mnt-lower: MAINT-IN-YOU
- mnt-routes: MAINT-IN-YOU
- mnt-by: MAINT-IN-YOU
- last-modified: 2012-01-25T11:25:55Z
- source: APNIC


IP 123.201.40[.]112 uses the requested URL-path to make a GET request on the IP-address at port 80. "NOT RESPONDED" is the response status code for the request "C:\PROGRAM FILES GOOGLE CHROME APPLICATION CHROME.EXE" that was started by the process.
Programs that retrieve their server data using a GET request are considered legitimate. The Google Chrome browser, a fully functional application widely used for web browsing, was used to make the actual request. It asks to get access to the server with IP 123.201.40[.]112 in order to collect its data and other resources.
Malware uses GET requests to retrieve more commands or to send data back to the command and control servers. In this instance, it may be an attack server making the request to a known IP address with a known port number. Since the server has not replied to the request, the response status "NOT RESPONDED" may indicate that the activity was carried out with malicious intent.
This graph illustrates how the Qakbot virus operates and interacts with its C2 server, located in India and with the IP address 123.201.40[.]112.

Impact
Qbot is a kind of malware that is typically distributed through hacked websites, malicious email attachments, and phishing operations. It targets private user information, including corporate logins or banking passwords. The deployment of ransomware: Payloads from organizations such as ProLock and Egregor ransomware are delivered by Qbot, a predecessor. Network Vulnerability: Within corporate networks, compromised systems will act as gateways for more lateral movement.
Proposed Recommendations for Mitigation
- Quick Action: To stop any incoming or outgoing traffic, the discovered IP addresses will be added to intrusion detection/prevention systems and firewalls.
- Network monitoring: Examining network log information for any attempts to get in touch with these IPs
- Email security: Give permission for anti-phishing programs.
- Endpoint Protection: To identify and stop Qbot infestations, update antivirus definitions.,Install tools for endpoint detection and response.
- Patch management: To reduce vulnerabilities that Qbot exploits, update all operating systems and software on a regular basis.
- Incident Response: Immediately isolate compromised computers.
- Awareness: Dissemination of this information to block the IP addresses of active C2 servers supporting Qbot malware activity has to be carried out.
Conclusion:
The discovery of these C2 servers reveals the growing danger scenario that Indian networks must contend with. To protect its infrastructure from future abuse, organizations are urged to act quickly and put the aforementioned precautions into place.
Reference:
- Threat Intelligence - ANY.RUN
- https://www.virustotal.com/gui
- https://www.virustotal.com/gui/ip-address/123.201.40.112/relations

"Cybercriminals are unleashing a surprisingly high volume of new threats in this short period of time to take advantage of inadvertent security gaps as organizations are in a rush to ensure business continuity.”
Cyber security firm Fortinet on Monday announced that over the past several weeks, it has been monitoring a significant spike in COVID-19 related threats.
An unprecedented number of unprotected users and devices are now online with one or two people in every home connecting remotely to work through the internet. Simultaneously there are children at home engaged in remote learning and the entire family is engaged in multi-player games, chatting with friends as well as streaming music and video. The cybersec firm’s FortiGuard Labs is observing this perfect storm of opportunity being exploited by cybercriminals as the Threat Report on the Pandemic highlights:
A surge in Phishing Attacks: The research shows an average of about 600 new phishing campaigns every day. The content is designed to either prey on the fears and concerns of individuals or pretend to provide essential information on the current pandemic. The phishing attacks range from scams related to helping individuals deposit their stimulus for Covid-19 tests, to providing access to Chloroquine and other medicines or medical device, to providing helpdesk support for new teleworkers.
Phishing Scams Are Just the Start: While the attacks start with a phishing attack, their end goal is to steal personal information or even target businesses through teleworkers. Majority of the phishing attacks contain malicious payloads – including ransomware, viruses, remote access trojans (RATs) designed to provide criminals with remote access to endpoint systems, and even RDP (remote desktop protocol) exploits.
A Sudden Spike in Viruses: The first quarter of 2020 has documented a 17% increase in viruses for January, a 52% increase for February and an alarming 131% increase for March compared to the same period in 2019. The significant rise in viruses is mainly attributed to malicious phishing attachments. Multiple sites that are illegally streaming movies that were still in theatres secretly infect malware to anyone who logs on. Free game, free movie, and the attacker is on your network.
Risks for IoT Devices magnify: As users are all connected to the home network, attackers have multiple avenues of attack that can be exploited targeting devices including computers, tablets, gaming and entertainment systems and even online IoT devices such as digital cameras, smart appliances – with the ultimate goal of finding a way back into a corporate network and its valuable digital resources.
Ransomware like attack to disrupt business: If the device of a remote worker can be compromised, it can become a conduit back into the organization’s core network, enabling the spread of malware to other remote workers. The resulting business disruption can be just as effective as ransomware targeting internal network systems for taking a business offline. Since helpdesks are now remote, devices infected with ransomware or a virus can incapacitate workers for days while devices are mailed in for reimaging.
“Though organizations have completed the initial phase of transitioning their entire workforce to remote telework and employees are becoming increasingly comfortable with their new reality, CISOs continue to face new challenges presented by maintaining a secure teleworker business model. From redefining their security baseline, or supporting technology enablement for remote workers, to developing detailed policies for employees to have access to data, organizations must be nimble and adapt quickly to overcome these new problems that are arising”, said Derek Manky, Chief, Security Insights & Global Threat Alliances at Fortinet – Office of CISO.

WhatsApp messages masquerading as an offer from Maruti Suzuki with links luring unsuspecting users with the promise of Maruti Suzuki 40th Anniversary Celebration presents, have been making the rounds on the app. If you receive such messages try to stay away from it, as it can be a scam.
The Research Wing of CyberPeace Foundation along with Autobot Infosec Private Limited have conducted a study based on a WhatsApp message that contained a link pretending to be a free gift offer from Maruti Suzuki which asks users to participate in a survey in order to get a chance to win a Maruti Baleno Sigma MT car.
Warning SignsThe campaign pretends to be an offer from Maruti Suzuki but is hosted on a third party domain instead of the official Maruti Suzuki website which makes it more suspicious.
The domain names associated with the campaign have been registered in very recent times.
Multiple redirections have been noticed between the links.
No reputed site would ask its users to share the campaign on WhatsApp.
The prize is kept really attractive to lure the laymen.
Grammatical mistakes have been noticed.
A congratulations message appears on the landing page with an attractive photo of Maruti Suzuki cars that asks users to participate in a quick survey in order to get a “Maruti Suzuki BALENO Sigma MT”. Also, the bottom of the page seems to appear like a comment section with public comments establishing the truthfulness of the offer.
The survey starts with some basic questions like Do you know Maruti Suzuki?, How old are you?, How do you think of Maruti Suzuki?, Are you male or female? Etc. Once the user answers the questions a “congratulatory message” is displayed.
On clicking the OK button users are given three attempts to win the prize. After completing all the attempts a message pops up that the user has won “Maruti Suzuki BALENO Sigma MT”. It then prompts the user to share the message on WhatsApp.
Strangely enough the user has to keep clicking the WhatsApp button until the progress bar completes. After clicking on the green ‘WhatsApp’ button multiple times it shows a section where an instruction has been given to complete registration in order to get the prize.
After clicking on the green ‘Complete registration’ button, it redirects the user to multiple advertisements web pages varying each time the user clicks on the button.
During the analysis the research team found a javascript code called hm.js was being executed in the background from the host hm[.]baidu[.]com which is a subdomain of Baidu and is used for Baidu Analytics, also known as Baidu Tongji. The important part is that Baidu is a Chinese multinational technology company specializing in Internet-related services, products and artificial intelligence, headquartered in Beijing’s Haidian district, China.To read the full report, please click (https://www.cyberpeace.org/CyberPeace/Repository/20210828Research-report-on-Maruti-Suzuki-40th-Anniversary-Celebration-free-gift-scam.pdf) here:
Conclusive Summary
1. The whole research activity was performed in a secured sandbox environment where the WhatsApp application was not installed. If any user opens the link from a device like smartphones where the WhatsApp application is installed, the sharing features on the site will open the Whatsapp application on the device to share the link.
2. The campaign collects browser and system information from the users.
3. Most of the domain names associated with the campaign have the registrant country as China.
4. Cybercriminals used Cloudflare technologies to mask the real IP addresses of the front-end domain names used in this Maruti Suzuki 40th Anniversary Celebration free gift campaign. But during the phases of investigation, the research team has identified a domain name that was requested in the background and has been traced as belonging to China.
CyberPeace Advisory
1. CyberPeace Foundation and Autobot Infosec recommend that people should avoid opening such messages sent via social platforms.
2. If at all, the user gets into this trap, it could lead to whole system compromise such as access to the microphone, Camera, Text Messages, Contacts, Pictures, Videos, Banking Applications, etc as well as financial losses.
3. Do not share confidential details like login credentials, banking information with such a type of scam.
4. Do not share or forward fake messages containing links without proper verification.
5. There is a need for International Cyber Cooperation between countries to bust the cybercriminal gangs running the fraud campaigns affecting individuals and organizations, to make Cyberspace resilient and peaceful.

Introduction
The two-day Apple’s Worldwide Developer Conference (WWDC) 2023, which was held on the 6th & 7th of June, has become an essential and highly anticipated part of our calendar as frequently as the trend. This year’s keynote announcements will include all of the usual enhancements for iOS, iPadOS, watchOS, macOS, and more. However, this year is also unique due to the unveiling of the Vision Pro headset, a brand-new Apple product.
In this blog, we will examine the exciting announcements made at Apple WWDC 2023, which was a ground-breaking event.
macOS Sonoma
macOS Sonoma, the new presentation of macOS disclosed at the WWDC full of exciting features. It comes with stunning video screensavers that show stunning scenes from all over the world. Gadgets can now be added genuinely to the work area and adjusted totally based on the client’s action. Also, it changes variety and blurring out of the spotlight while utilising applications. In addition, Death Stranding: Directors Cut for Mac announced that the Game Mode is added to make Macs more suitable for gaming. A presenter overlay enhances video presentations, and viewers can respond to them with interactive responses. Updated Safari is also included in the WebApp feature that turns frequently used websites into dedicated windows, a new Profile system for separating browsing history, and secure password sharing. Currently, the developer beta is available and the public beta will be available in July, and the final release is anticipated for the fall.
ios 16
Apple WWDC 2023 shows the following iOS, and iOS 16 replication, offering plenty of energising highlights for iPhone and iPad clients. Apple maintains its commitment to privacy with iOS 16, which introduces enhanced privacy settings that give users even more control over their data and online privacy. Users can also personalise their devices according to their preferences thanks to the new operating system’s refinement and customisable user interface.Improved multitasking capabilities like redesigned Files app and advanced note-taking features are just a few of the productivity enhancements included in the iOS 16. With iOS 16, Apple also improves its AR capabilities, allowing developers to develop even more immersive and interactive AR experiences.

WatchOS 9
Apple WWDC 2023 carried energising updates to the Apple Watch with the presentation of watchOS 9. The Apple Watch is an essential companion for sustaining a healthy lifestyle because the most recent version of the operating system includes cutting-edge health and fitness features. WatchOS 9 gives users unprecedented control over their health, offering personalised fitness recommendations and advanced sleep tracking.
Additionally, new watch faces were added, enhancing communication capabilities and improving app performance in watchOS 9, making the Apple Watch even easier to use daily.
ios 17
Rather than focusing on major features, Apple focused on quality-of-life enhancements when it announced iOS 17 at WWDC 2023. Live Voicemail with real-time transcripts of voicemails, personalised personal contact “posters,” and video voicemails for FaceTime are all part of the update. Search filters, a catch-up arrow, live location sharing, and a safety feature called Check-In are all available in Messages. AirDrop now supports NameDrop for transferring contact information; stickers have been expanded. The autocorrect and recording features on the keyboard have been improved for accuracy. Standby in the lock screen is an intelligent home display that shows the weather, upcoming appointments, and notifications. Siri works on Standby and adjusts itself for the night. The developer beta is currently available now, and a public beta will take place next month before the full release is in the fall.
Vision Pro VR Headset
Apple unveiled the Vision Pro AR headset, their first foray into virtual reality (VR), during the WWDC keynote. The Vision Pro is a virtual reality headset that competes with PlayStation VR2 and Meta Quest 3. This is in contrast to the long-awaited Apple smart glasses. Apple put a lot of effort into making a thin and light headset by using premium materials when needed. Voice, hand, and eye commands are all used to operate the Digital Crown-equipped device. The showcases offer extraordinary clarity, which is fueled by Apple’s M2 processor with a committed R1 chip. The Vision Pro combines virtual reality (VR) and augmented reality (AR), enabling users to interact with Apple apps and gain access to the company’s existing ecosystem. The expanded reality space created by the headset’s sensors and cameras allows users to place apps in real-world environments and adjust their level of concentration. Optic ID is a security and unlocking eye-tracking technology that is incorporated into the Vision Pro. It allows for a more immersive screen experience because it is compatible with Apple accessories like Magic Keyboard and Mac. At launch, the Vision Pro supports over a hundred Apple game galleries. Disney gave a hint that Apple and Disney might work together in the future by announcing support for the Vision Pro and making the Disney Plus app available immediately. The show highlighted the headset’s lightweight plan and recommended Apple clients wear it for extended periods. However, widespread adoption may be difficult due to the high price of $3,499 (₹289,093.01 approx). Apple is expected to release the Vision Pro for public use in 2024.

15-inch MacBook Air
At the WWDC event, Apple revealed a new MacBook Air with a larger 15-inch model instead of the standard 13-inch model. The 15-inch MacBook Air features a powerful Apple M2 processor, a thin, light, and long-lasting design, and a stunning 15.3-inch Retina display. It comes in four colours and has a headphone jack, two USB-C ports, and MagSafe charging. The display has six spatial speakers, a 1080p webcam, and 500 nits of brightness. Apple claims a battery life of up to 18 hours.
Conclusion
At Apple’s 2023 WWDC, the company demonstrated its commitment to developing technology that is user-friendly and accessible to all. Apple’s commitment to improving the user experience across all of its products is demonstrated in the updates to operating systems, improvements of Siri, breakthroughs in augmented reality, and enhancements to health and fitness.By making complex innovations more like-minded and easy to understand, Apple is enabling people to use the maximum capacity of their gadgets. Apple’s innovations at WWDC 2023 are expected to shape the future of technology, simplifying everyday tasks and revolutionising how we interact with the digital world.As we push ahead, it is exciting to guess what these advancements will proceed to develop and decidedly mean for our lives. The future holds even more incredible possibilities for all of us because of Apple’s focus on privacy, user-centric design, and pushing the boundaries of innovation. Thus, prepare to embrace a future where innovation flawlessly incorporates into our lives because of the endeavours displayed at Apple WWDC 2023.

Introduction
In recent years, India has witnessed a significant rise in the popularity and recognition of esports, which refers to online gaming. Esports has emerged as a mainstream phenomenon, influencing players and youngsters worldwide. In India, with the penetration of the internet at 52%, the youth has got its attracted to Esports. In this blog post, we will look at how the government is booting the players, establishing professional leagues, and supporting gaming companies and sponsors in the best possible manner. As the ecosystem continues to rise in prominence and establish itself as a mainstream sporting phenomenon in India.
Factors Shaping Esports in India: A few factors are shaping and growing the love for esports in India here. Let’s have a look.
Technological Advances: The availability and affordability of high-speed internet connections and smart gaming equipment have played an important part in making esports more accessible to a broader audience in India. With the development of smartphones and low-cost gaming PCs, many people may now easily participate in and watch esports tournaments.
Youth Demographic: India has a large population of young people who are enthusiastic gamers and tech-savvy. The youth demographic’s enthusiasm for gaming has spurred the expansion of esports in the country, as they actively participate in competitive gaming and watch major esports competitions.
Increase in the Gaming community: Gaming has been deeply established in Indian society, with many people using it for enjoyment and social contact. As the competitive component of gaming, esports has naturally gained popularity among gamers looking for a more competitive and immersive experience.
Esports Infrastructure and Events: The creation of specialised esports infrastructure, such as esports arenas, gaming cafés, and tournament venues, has considerably aided esports growth in India. Major national and international esports competitions and leagues have also been staged in India, offering exposure and possibilities for prospective esports players. Also supports various platforms such as YouTube, Twitch, and Facebook gaming, which has played a vital role in showcasing and popularising Esports in India.
Government support: Corporate and government sectors in India have recognised the potential of esports and are actively supporting its growth. Major corporate investments, sponsorships, and collaborations with esports organisations have supplied the financial backing and resources required for the country’s esports development. Government attempts to promote esports have also been initiated, such as forming esports governing organisations and including esports in official sporting events.
Growing Popularity and Recognition: Esports in India has witnessed a significant surge in viewership and fanbase, all thanks to online streaming platforms such as Twitch, YouTube which have provided a convenient way for fans to watch live esports events at home and at high-definition quality social media platforms let the fans to interact with their favourite players and stay updated on the latest esports news and events.

Esports Leagues in India
The organisation of esports tournaments and leagues in India has increased, with the IGL being one of the largest and most popular. The ESL India Premiership is a major esports event the Electronic Sports League organised in collaboration with NODWIN Gaming. Viacom18, a well-known Indian media business, established UCypher, an esports league. It focuses on a range of gaming games such as CS: GO, Dota 2, and Tekken in order to promote esports as a professional sport in India. All of these platforms provide professional players with a venue to compete and establish their profile in the esports industry.
India’s Performance in Esports to Date
Indian esports players have achieved remarkable global success, including outstanding results in prominent events and leagues. Individual Indian esports players’ success stories illustrate their talent, determination, and India’s ability to flourish in the esports sphere. These accomplishments contribute to the worldwide esports landscape’s awareness and growth of Indian esports. To add the name of the players and their success stories that have bought pride to India, they are Tirth Metha, Known as “Ritr”, a CS:GO player, Abhijeet “Ghatak”, Ankit “V3nom”, Saloni “Meow16K”.Apart from this Indian women’s team has also done exceptionally well in CS:GO and has made it to the finale.
Government and Corporate Sectors support: The Indian esports business has received backing from the government and corporate sectors, contributing to its growth and acceptance as a genuine sport.
Government Initiatives: The Indian government has expressed increased support for esports through different initiatives. This involves recognising esports as an official sport, establishing esports regulating organisations, and incorporating esports into national sports federations. The government has also announced steps to give financial assistance, subsidies, and infrastructure development for esports, therefore providing a favourable environment for the industry’s growth. Recently, Kalyan Chaubey, joint secretary and acting CEO of the IOA, personally gave the athletes cutting-edge training gear during this occasion, providing kits to the players. The kit includes the following:
Advanced gaming mouse.
Keyboard built for quick responses.
A smooth mousepad
A headphone for crystal-clear communication
An eSports bag to carry the equipment.
Corporate Sponsorship and Partnerships
Indian corporations have recognised esports’ promise and actively sponsored and collaborated with esports organisations, tournaments, and individual players. Companies from various industries, including technology, telecommunications, and entertainment, have invested in esports to capitalise on its success and connect with the esports community. These sponsorships and collaborations give financial support, resources, and visibility to esports in India. The leagues and championships provide opportunities for young players to showcase their talent.
Challenges and future
While esports provides great job opportunities, several obstacles must be overcome in order for the industry to expand and gain recognition:
Infrastructure & Training Facilities: Ensuring the availability of high-quality training facilities and infrastructure is critical for developing talent and allowing players to realise their maximum potential. Continued investment in esports venues, training facilities, and academies is critical for the industry’s long-term success.
Fostering a culture of skill development and giving outlets for formal education in esports would improve the professionalism and competitiveness of Indian esports players. Collaborations between educational institutions and esports organisations can result in the development of specialised programs in areas such as game analysis, team management, and sports psychology.
Establishing a thorough legal framework and governance structure for esports will help it gain legitimacy as a professional sport. Clear standards on player contracts, player rights, anti-doping procedures, and fair competition policies are all part of this.
Conclusion
Esports in India provide massive professional opportunities and growth possibilities for aspiring esports athletes. The sector’s prospects are based on overcoming infrastructure, perception, talent development, and regulatory barriers. Esports may establish itself as a viable and acceptable career alternative in India with continued support, investment, and stakeholder collaboration

BharOS’s successful testing grabbed massive online attention after Ashwini Vaishnaw, Minister of Communications and Electronics & IT, and Union Education Minister Dharmendra Pradhan unveiled the new mobile operating system. On Data Privacy Day, January 28, it’s appropriate to discuss the safety factors.
The OS is developed by JandKops, which has been incubated by IIT Madras Pravartak Technologies Foundation. It is claimed that BharOS will ensure the prevention of the “execution of any malware” and “execution of any malicious application”.
Even though it is called a Made in India OS, there are many people who disagree with this. It is because the OS is based on an AOSP (Android Open Source Project). It includes similar methodologies, functionalities, and basics used in Google Android.
Global safety factor
Security and data safety has been worldwide issue. A few years ago, Alphabet CEO Sundar Pichai also testified in front of US Congress while facing questions related to privacy, data collection, and location tracking.
While experts say that Android’s app ecosystem is a privacy and security disaster, a study that examined 82,501 apps pre-installed on 1,742 Android smartphones sold by 214 vendors concluded that users are woefully unaware of the significant security and privacy risks posed by pre-installed applications.
Even Apple, which takes cybersafety issues as a top priority, sometimes finds itself in a vulnerable situation. For example, last year Apple users were advised to update their devices to protect against a pair of security flaws that could allow attackers to take complete control.
It was said that one of the software flaws affected the kernel, the deepest layer of the OS shared by all Apple devices, while the other had an impact on WebKit, the technology that powers the Safari web browser.
Security researchers, including NordVPN, said that Apple’s closed development OS makes it more difficult for hackers to develop exploits, while Android raises the threat level since anyone can see its source code to develop exploits.
BharOS is not like iOS but it is kind of similar to Android and based on AOSP. So the question is, how safe would this OS be?
‘Security blanket’
Sandip Kumar Panda, Co-founder and CEO of InstaSafe, told News18: “BharOS acts as a security blanket for devices. The framework is designed in a manner that it prevents the execution of any malicious app and verifies each app on the devices before making it live on the BharOS platform.”
There are no apps without any vulnerabilities, he said. “As the app development progresses, vulnerabilities get introduced either in the form of insecure coding practices or third-party software vulnerabilities integrated with the platform. Since several Android vulnerabilities were discovered over the years, all those bugs would have been fixed now and updates would already have been for AOSP, which will be much more mature now,” he added.
Vineet Kumar, Founder and President of CyberPeace Foundation, believes that “the use of AOSP as the foundation for BharOS is a positive step” as it is a robust platform.
But according to him, it is important to note that no OS can be completely immune to all forms of cyber threats. “The key to staying safe online is to stay vigilant, use security software, keep your software updated, and be mindful of the apps you install and the websites you visit,” he said,
Furthermore, the expert stated that it is possible to make an OS more secure by implementing a variety of security features and technologies such as sandboxing, whitelisting, and application control, as well as rigorous testing and code review processes.
Kumar said: “It would be important for an independent, reputable security firm to evaluate BharOS and test its security features before it can be stated with certainty that it is more secure than other OSs.”
It is difficult to say whether the BharOS will be free of cybersecurity issues without more information about the specific features and security measures that have been implemented, he noted while adding that this OS has to go through a rigorous testing and certification process.
“It will be important to see how it measures up against established security standards and how well it can withstand real-world attacks,” the expert stated.
Reference Link : https://www.news18.com/amp/news/tech/data-privacy-day-how-safe-is-bharos-what-do-cybersecurity-experts-say-you-are-about-to-find-out-6932521.html

Introduction
The world has been surfing the wave of technological advancements and innovations for the past decade, and it all pins down to one device – our mobile phone. For all mobile users, the primary choices of operating systems are Android and iOS. Android is an OS created by google in 2008 and is supported by most brands like – One+, Mi, OPPO, VIVO, Motorola, and many more and is one of the most used operating systems. iOS is an OS that was developed by Apple and was introduced in their first phone – The iPhone, in 2007. Both OS came into existence when mobile phone penetration was slow globally, and so the scope of expansion and advancements was always in favor of such operating systems.
The Evolution
iOS
Ever since the advent of the iPhone, iOS has seen many changes since 2007. The current version of iOs is iOS 16. However, in the course of creating new iOS and updating the old ones, Apple has come out with various advancements like the App Store, Touch ID & Face ID, Apple Music, Podcasts, Augmented reality, Contact exposure, and many more, which have later become part of features of Android phone as well. Apple is one of the oldest tech and gadget developers in the world, most of the devices manufactured by Apple have received global recognition, and hence Apple enjoys providing services to a huge global user base.
Android
The OS has been famous for using the software version names on the food items like – Pie, Oreo, Nougat, KitKat, Eclairs, etc. From Android 10 onwards, the new versions were demoted by number. The most recent Android OS is Android 13; this OS is known for its practicality and flexibility. In 2012 Android became the most popular operating system for mobile devices, surpassing Apple’s iOS, and as of 2020, about 75 percent of mobile devices run Android.
Android vs. iOS
1. USER INTERFACE
One of the most noticeable differences between Android and iPhone is their user interface. Android devices have a more customizable interface, with options to change the home screen, app icons, and overall theme. The iPhone, on the other hand, has a more uniform interface with less room for customization. Android allows users to customize their home screen by adding widgets and changing the layout of their app icons. This can be useful for people who want quick access to certain functions or information on their home screen. IOS does not have this feature, but it does allow users to organize their app icons into folders for easier navigation.
2. APP SELECTION
Another factor to consider when choosing between Android and iOS is the app selection. Both platforms have a wide range of apps available, but there are some differences to consider. Android has a larger selection of apps overall, including a larger selection of free apps. However, some popular apps, such as certain music streaming apps and games, may be released first or only available on iPhone. iOS also has a more curated app store, meaning that all apps must go through a review process before being accepted for download. This can result in a higher quality of apps overall, but it can also mean that it takes longer for new apps to become available on the platform. iPhone devices tend to have less processing power and RAM. But they are generally more efficient in their use of resources. This can result in longer battery life, but it may also mean that iPhones are slower at handling multiple tasks or running resource-intensive apps.
3. PERFORMANCE
When it comes to performance, both Android and iPhone have their own strengths and weaknesses. Android devices tend to have more processing power and RAM. This can make them faster and more capable of handling multiple tasks simultaneously. However, this can also lead to Android devices having shorter battery life compared to iPhones.
4. SECURITY
Security is an important consideration for any smartphone user, and Android and iPhone have their own measures to protect user data. Android devices are generally seen as being less secure than iPhones due to their open nature. Android allows users to install apps from sources other than the Google Play Store, which can increase the risk of downloading malicious apps. However, Android has made improvements in recent years to address this issue. Including the introduction of Google Play Protect, which scans apps for malware before they are downloaded. On the other hand, iPhone devices have a more closed ecosystem, with all apps required to go through Apple‘s review process before being available for download. This helps reduce the risk of downloading malicious apps, but it can also limit the platform’s flexibility.
Conclusion
The debate about the better OS has been going on for some time now, and it looks like it will get more comprehensive in the times to come, as netizens go deeper into cyberspace, they will get more aware and critical of their uses and demands, which will allow them to opt for the best OS for their convenience. Although the Andriod OS, due to its integration, stands more vulnerable to security threats as compared to iOS, no software is secure in today’s time, what is secure is its use and application hence the netizen and the platforms need to increase their awareness and knowledge to safeguard themselves and the wholesome cyberspace.

Introduction
Established in the US, one of the world’s largest cab networks came into existence in 2010 and, since its inception, has expanded all over the globe with operations in 10,000 cities across 71 countries. It made a remarkable start in India in 2017 and, since then, has seen a rise in the customers and drivers for the company. India is among the largest markets for Uber, with 600,000 monthly drivers and 8.5 million monthly riders.
GeM
Government e-Marketplace (GeM) is a one-stop portal to facilitate online procurement of common-use Goods & Services required by various Government Departments / Organizations / PSUs. GeM aims to enhance transparency, efficiency and speed in public procurement. It provides the tools of e-bidding, reverses e-auction and demand aggregation to facilitate government users achieve the best value for their money. Government e-Marketplace owes its genesis to the recommendations of two Groups of Secretaries to the Prime Minister in January 2016. They recommended setting up a dedicated e-market for different goods & services procured or sold by Government/PSUs besides reforming DGS&D. Subsequently, the Finance Minister, in his Budget speech for FY 2016-17, announced setting up of a technology-driven platform to facilitate procurement of goods and services by various Ministries and agencies of the Government. The portal was launched on 9th August 2016 by the Commerce & Industry Minister.
Uber-GeM collaboration
The cab network giant has registered on the portal of the Government E-marketplace and has declared that it will offer its services to Government officials from Ministries and PSUs. The project is currently in its pilot phase and shall be executed systematically to cover all the ministries and PSUs in the nation. The officials can book cabs at a fixed price with no cancellation or surge fees on the rides. The authorised officials will be able to book a cab from the portal and select from the list of drivers available. It will be a cashless/cardless ride for the officials; additional vehicle categories for government riders have been added, namely, GeM Yatraa Hatch and GeM Yatraa Sedan, and there will be hourly rentals for multiple-stops, allowing the government officials to enjoy the flexible and easily accessible network of cabs in major cities.
Advantages
Such collaboration between Government institutions and corporates will go a long way to secure a stable equilibrium in the market. Uber, a US-based company, enjoys a vast user base in India and has created new job avenues. The advantages of the collaboration between GeM and Uber are as follows-
Easy accessibility
This will undoubtedly provide ease in accessibility in terms of being in a new place, and language barriers will no longer exist with such options for Government officials.
Increased jobs for drivers
With more cabs being engaged with ministries and PSUs, it is pertinent that the requirement for drivers will grow, thus increasing the employability rate in India and allowing the user to have an uninterrupted experience.
Ease of travel and commuting
This move will provide flexibility, thus leading to more ease in travel in cases of emergencies or places inaccessible by trains or other modes of transport.
Rise in travel and tourism
Coupled with the other factors, the opportunities for the users to visit different places will be an added advantage which will help boost the tourism industry, thus creating a balance in the market.
Sustainable Government corporate relationship

Such collaborations between the government and corporates will be substantial, signifying the ease of doing business in India. They will also act as a beacon of example for compliance with opportunities for the other companies and stakeholders.
Opportunities for collaboration with ingenious start-ups
With such major corporate joining hands with the government, the indigenous start-ups will have various opportunities to engage with companies and recreate similar businesses rooted in India, thus transforming the economy.
Conclusion
Transportation and communication play a vital role in our lives, thus, such collaboration will go a long way in creating a better and more uniform user experience in the country. This also goes a long way to showcase that the Governmental platforms also offer services of a global standard. Such portals exist in South Korea, Singapore, the US and Europe. The network of cabs can only be sustained using the locals as drivers, hence these collaborations are win-win for all as the market dynamics are improving, employability will increase, and improved user experience will be seen.

THREE CENTRES OF EXCELLENCE IN ARTIFICIAL INTELLIGENCE:
India’s Finance Minister, Mrs. Nirmala Sitharaman, with a vision of ‘Make AI for India’ and ‘Make AI work for India, ’ announced during the presentation of Union Budget 2023 that the Indian Government is planning to set up three ‘Centre of Excellence’ for Artificial Intelligence in top Educational Institutions to revolutionise fields such as health, agriculture, etc.
Under the ‘Amirt Kaal,’ i.e., the budget of 2023 is a stepping stone by the government to have a technology-driven knowledge-based economy and the seven priorities that have been set up by the government called ‘Saptarishi’ such as inclusive development, reaching the last mile, infrastructure investment, unleashing potential, green growth, youth power, and financial sector will guide the nation in this endeavor along with leading industry players that will partner in conducting interdisciplinary research, developing cutting edge applications and scalable problem solutions in such areas.
The government has already formed the roadmap for AI in the nation through MeitY, NASSCOM, and DRDO, indicating that the government has already started this AI revolution. For AI-related research and development, the Centre for Artificial Intelligence and Robotics (CAIR) has already been formed, and biometric identification, facial recognition, criminal investigation, crowd and traffic management, agriculture, healthcare, education, and other applications of AI are currently being used.
Even a task force on artificial intelligence (AI) was established on August 24, 2017. The government had promised to set up Centers of Excellence (CoEs) for research, education, and skill development in robotics, artificial intelligence (AI), digital manufacturing, big data analytics, quantum communication, and the Internet of Things (IoT) and by announcing the same in the current Union budget has planned to fulfill the same.
The government has also announced the development of 100 labs in engineering institutions for developing applications using 5G services that will collaborate with various authorities, regulators, banks, and other businesses.
Developing such labs aims to create new business models and employment opportunities. Among others, it will also create smart classrooms, precision farming, intelligent transport systems, and healthcare applications, as well as new pedagogy, curriculum, continual professional development dipstick survey, and ICT implementation will be introduced for training the teachers.
POSSIBLE ROLES OF AI:
The use of AI in top educational institutions will help students to learn at their own pace, using AI algorithms providing customised feedback and recommendations based on their performance, as it can also help students identify their strengths and weaknesses, allowing them to focus their study efforts more effectively and efficiently and will help train students in AI and make the country future-ready.
The main area of AI in healthcare, agriculture, and sustainable cities would be researching and developing practical AI applications in these sectors. In healthcare, AI can be effective by helping medical professionals diagnose diseases faster and more accurately by analysing medical images and patient data. It can also be used to identify the most effective treatments for specific patients based on their genetic and medical history.
Artificial Intelligence (AI) has the potential to revolutionise the agriculture industry by improving yields, reducing costs, and increasing efficiency. AI algorithms can collect and analyse data on soil moisture, crop health, and weather patterns to optimise crop management practices, improve yields and the health and well-being of livestock, predict potential health issues, and increase productivity. These algorithms can identify and target weeds and pests, reducing the need for harmful chemicals and increasing sustainability.
ROLE OF AI IN CYBERSPACE:
Artificial Intelligence (AI) plays a crucial role in cyberspace. AI technology can enhance security in cyberspace, prevent cyber-attacks, detect and respond to security threats, and improve overall cybersecurity. Some of the specific applications of AI in cyberspace include:
- Intrusion Detection: AI-powered systems can analyse large amounts of data and detect signs of potential cyber-attacks.
- Threat Analysis: AI algorithms can help identify patterns of behaviour that may indicate a potential threat and then take appropriate action.
- Fraud Detection: AI can identify and prevent fraudulent activities, such as identity theft and phishing, by analysing large amounts of data and detecting unusual behaviour patterns.
- Network Security: AI can monitor and secure networks against potential cyber-attacks by detecting and blocking malicious traffic.
- Data Security: AI can be used to protect sensitive data and ensure that it is only accessible to authorised personnel.
CONCLUSION:
Introducing AI in top educational institutions and partnering it with leading industries will prove to be a stepping stone to revolutionise the development of the country, as Artificial Intelligence (AI) has the potential to play a significant role in the development of a country by improving various sectors and addressing societal challenges. Overall, we hope to see an increase in efficiency and productivity across various industries, leading to increased economic growth and job creation, improved delivery of healthcare services by increasing access to care and, improving patient outcomes, making education more accessible and effective as AI has the potential to improve various sectors of a country and contribute to its overall development and progress. However, it’s important to ensure that AI is developed and used ethically, considering its potential consequences and impact on society.
References:

Introduction
It’s a proud moment for Indians that India will host the G- 20 administration, which will bring the world’s 20 largest profitable nations together on a single platform during the post-economic recovery and the Russia- Ukraine conflict, which has increased geopolitical pressures among nations over the last many times and made the G- 20 a precedence of nations. With this administration, India has to make cybersecurity precedence, as the security and integrity of the critical structure and digital platforms are top precedence in 2023. The necessity for a secure cyberspace is pivotal given the exponential increase in the volume and kind of cyber-attacks, particularly to crucial structures the most recent illustration is the ongoing interruption at New Delhi’s All India Institute of Medical lores caused by a ransomware assault. It has been observed that the mode of attacks are more sophisticated and targets communication structure, critical structure, transport systems, and especially the information technology sector and fiscal system.
The structure that enables the delivery of government services to be more effective. As a result,cyber-secured critical structures and digital public forums are necessary for public security, bettered governance, and, most importantly, maintaining people’s trust. The G20 can be enhanced and contribute towards securing digital public platforms and the integrity of the critical structure. This time, in 2023, digital security is the top precedence.
G20 cybersecurity enterprises and politic sweat
The emphasis on cybersecurity was maintained throughout the Italian and Indonesian regulations in 2021 and 2022, independently, by emphasizing the significance of cyberspace during Digital Economy Working Group addresses. Specifically, under the Indonesian Presidency, the prominent cybersecurity focus was clear in the recent Bali Leaders’ protestation, which noted, among other effects, the significance of fighting misinformation juggernauts and cyber attacks, as well as guaranteeing connectivity structure security. The cyber incident report by the Financial Stability Board on carrying further uniformity in cyber incident reporting In 2016, a G20 digital task force was created under the Chinese administration to understand digital technology issues. Under the Saudi administration, the cybersecurity gap at the G20 was bridged by addressing the issues of MSMs. India has also refocused on the significance of creating secure, secure, and stronger-friendly digital platforms.
G20- India’s digital invention alliance( G-20-DIA) a cyber-secure Bharat
- Under India’s administration, the G20’s Digital Economy Working Group is led by the Ministry of Electronics and Information Technology( MeitY, DEWG).
- The Ministry concentrated on three major areas during India’s G20 administration digital skill development, digital public structure, and cyber security.
- The EWG’s DIA and Stay Safe Online enterprise further the ideal of lesser digital metamorphosis by guaranteeing a safe and creative cyber terrain. They want to offer a smooth and secure delivery of public services.

The G20 Digital Innovation Alliance
(G20- DIA) strives to find, admit, and encourage the relinquishment of innovative and poignant digital technologies produced by invited G20 startups and-member governments.
- These technologies must meet humanity’s conditions in six crucial areas husbandry, health, education, finance, secure digital structure, and indirect frugality.
- The inventions created around these motifs will be supported by the Digital Public Goods structure, allowing them to be espoused encyclopedically, closing the digital gap and icing sustainable and indifferent growth.
- The G20 Digital Innovation Alliance( G20- DIA) conference will be held on the perimeters of the Digital Economy Working Group( DEWG) meeting in Bengaluru.
- Top-nominated entrepreneurs from each order will present their ideas to a worldwide community of investors, instructors, pots, and other stakeholders at this event.
India’s” Stay Safe Online crusade”
The” Stay Safe Online” crusade attempts to raise mindfulness about the significance of remaining safe in the online world amid our adding reliance on it. With the fast expansion of the technical terrain and the growing number of internet druggies in India, new difficulties are arising. The Stay Safe Online crusade aims to educate individuals about cyber pitfalls and how to avoid them. The time-long crusade will target children, women, scholars, and aged citizens, as well as individuals with disabilities, preceptors, and government officers in particular. It’ll be done in Hindi, English, and indigenous languages to reach a larger followership. It’ll distribute mindfulness information in infographics, short pictures, cartoon stories, and so on through extensively employed social media platforms and other channels. The primary stakeholders will be government agencies, civil societies, and NGOs.
Conclusion
To wind up, it can be said that cyber security has become the most essential part of transnational affairs. As India hosts the G20 administration in 2023, the docket relating to cybersecurity gains a global stage, where cyber-related issues are addressed and honored encyclopedically, and nations can combat these issues; also, India aims to raise cyber mindfulness among its citizens.

Introduction
The year, 2022 has been a year of transition and change for the gaming industry. This year esports and gaming including the industry’s greater increased acceptance by the sports authorities and higher prize pools for top players, has been more commercial than ever, according to research by the year 2025 the industry will witness growth by 5 million dollars and around 420 million active gamers from India. Since, India is on the way to become world’s largest gaming market, with revenue earned in 2021 increasing by up to 28%, or 1.2 billion dollars, and predicted to reach 2 billion dollars by 2024 as a result of the COVID-19 expanding internet access throughout the country.
After a lengthy debate, the government has finally decided to bring online gaming under the purview of the law. The President of India has changed the rules governing e-sports and requested that the Sports Ministry and the Ministry of Electronics and Information Technology (MeitY) include e-sports in multi-sport competitions. India’s gaming sector has reached new heights this year, with the country winning its first bronze medal in the first esports event organized by this year’s Commonwealth Games, and this is only the beginning.
Indian government takes on E-sports
The Indian government has given esports a huge boost. It has been introduced into the traditional sports disciplines of the nation. Droupadi Murmu, the President of India, changed the regulations governing eSports using the authority “conferred by clause (3) of Article 77 of the Constitution,” and requested that “e-Sports be included as part of multi-sports events” from the Ministries of Electronics and Information Technology and Sports. Some crucial points will clarify the government’s position on e-sports.
- E-sports were added as a demonstration sport to the 2018 Asian Games in Jakarta, which meant that medals earned in the sport were not counted in the official total of medals.
- There is a greater desire for Esports to be integrated with school curricula.
- E-Sports (Electronic Sports) have been acknowledged by the Indian government as a component of multi-sport tournaments.

Why is e-sports important?
The Indian Esports Industry has worked hard to distinguish Esports from the broader category of “Gaming.” Esports is a competitive sport in which esports athletes compete in specific video game genres in a virtual, electronic environment using their physical and mental prowess, according to the industry.
According to studies, as individuals have gotten more screen aware and online gaming has become a part of their life, internet gaming not only improves fine motor skills but also sharpens the mind. The industry has the most users and stakeholders, and it has become critical to governing it; consequently, legislation is required to regulate it.
The online regulation bill 2022
The Online Gaming (Regulations) Bill, 2022, was recently filed in the Lok Sabha to create an effective regulatory mechanism for the online gaming business to prevent fraud and misuse of things related to or incidental to it. There are 20 sections spread throughout three chapters. It intends to establish an Online Gaming Commission, the authority, mandate, and jurisdiction of which will be specified by the Bill. An online gaming server will be licensed, relinquished, revoked, or suspended by the Commission’s key highlights of the bill to make it more clear
- The Bill establishes a regulating agency, the Online Gaming Commission (“OGC”), comprised of five members chosen by the Central Government, each with at least one specialist in the fields of law, cyber technology, and law enforcement experience.
- The OGC will be able to oversee the functions of online gaming websites, issue periodic or special reports on Online Gaming issues, recommend appropriate measures to control and curb illegal Online Gaming, grant, suspend, and revoke licenses for online gaming websites, and set fees for license applications and renewals.
- Without a website and a non-transferable and non-assignable license, the Bill proposes to make online gambling illegal. Anyone operating an online gaming server or website without a license risks up to three years in prison and a fine. The permission will be good for a six-year term.
- The license intended to be given under the Bill may be terminated or canceled if the licensee violates any of the license’s requirements or any of Bill’s provisions. However, the Bill does not apply to anybody providing backend services in India, including hosting and maintenance for any international gaming website situated outside of India.
- The bill also mentions the Foreign Direct Investment and Technology Collaboration in Online Gaming

Few misses in the bill that can be addressed to make it stronger and a better version
- The law does not address Know Your Customer (KYC) requirements, customer complaint procedures, advertising and marketing restrictions, user data protection, responsible gaming guidelines, and other concerns.
- In the bill, there is no clear distinction between money involved in the game. This is a matter of concern and needs to be addressed so the money laundering aspect can be determined.
- The distinction between “games of chance” and “games of skill” is not addressed in the Bill. Furthermore, the Bill does not specify whether its prohibitions apply only to for-real-money games or to free games.
Conclusion
Despite the bill’s flaws, it has offered optimism to the burgeoning gaming sector, which desperately needs a robust regulatory and legal framework free of ambiguity, allowing players to play safely, and encouraging entrepreneurs to enter the field with safety and security. An improved regulatory framework will increase job prospects while also assisting the government. A transparent framework will also aid in the protection of the rights of actors and stakeholders.

Introduction
With the increasing reliance on digital technologies in the banking industry, cyber threats have become a significant concern. Cyberlaw plays a crucial role in safeguarding the banking sector from cybercrimes and ensuring the security and integrity of financial systems.
The banking industry has witnessed a rapid digital transformation, enabling convenient services and greater access to financial resources. However, this digitalisation also exposes the industry to cyber threats, necessitating the formulation and implementation of effective cyber law frameworks.
Recent Trends in the Banking Industry
Digital Transformation: The banking industry has embraced digital technologies, such as mobile banking, internet banking, and financial apps, to enhance customer experience and operational efficiency.
Open Banking: The concept of open banking has gained prominence, enabling data sharing between banks and third-party service providers, which introduces new cyber risks.

How Cyber Law Helps the Banking Sector
The banking sector and cyber crime share an unspoken synergy due to the mass digitisation of banking services. Thanks to QR codes, UPI and online banking payments, India is now home to 40% of global online banking transactions. Some critical aspects of the cyber law and banking sector are as follows:
Data Protection: Cyberlaw mandates banks to implement robust data protection measures, including encryption, access controls, and regular security audits, to safeguard customer data.
Incident Response and Reporting: Cyberlaw requires banks to establish incident response plans, promptly report cyber incidents to regulatory authorities, and cooperate in investigations.
Customer Protection: Cyberlaw enforces regulations related to online banking fraud, identity theft, and unauthorised transactions, ensuring that customers are protected from cybercrimes.
Legal Framework: Cyberlaw provides a legal foundation for digitalisation in the banking sector, assuring customers that regulations protect their digital transactions and data.
Cybersecurity Training and Awareness: Cyberlaw encourages banks to conduct regular training programs and create awareness among employees and customers about cyber threats, safe digital practices, and reporting procedures.

RBI Guidelines
The RBI, as India’s central banking institution, has issued comprehensive guidelines to enhance cyber resilience in the banking industry. These guidelines address various aspects, including:
Technology Risk Management
Cyber Security Framework
IT Governance
Cyber Crisis Management Plan
Incident Reporting and Response
Recent Trends in Banking Sector Frauds and the Role of Cyber Law
Phishing Attacks: Cyberlaw helps banks combat phishing attacks by imposing penalties on perpetrators and mandating preventive measures like two-factor authentication.
Insider Threats: Cyberlaw regulations emphasise the need for stringent access controls, employee background checks, and legal consequences for insiders involved in fraudulent activities.
Ransomware Attacks: Cyberlaw frameworks assist banks in dealing with ransomware attacks by enabling legal actions against hackers and promoting preventive measures, such as regular software updates and data backups.
Master Directions on Cyber Resilience and Digital Payment Security Controls for Payment System Operators (PSOs)
Draft of Master Directions on Cyber Resilience and Digital Payment Security Controls for Payment System Operators (PSOs) issued by the Reserve Bank of India (RBI). The directions provide guidelines and requirements for PSOs to improve the safety and security of their payment systems, with a focus on cyber resilience. These guidelines for PSOs include mobile payment service providers like Paytm or digital wallet payment platforms.
Here are the highlights-
The Directions aim to improve the safety and security of payment systems operated by PSOs by providing a framework for overall information security preparedness, with an emphasis on cyber resilience.
The Directions apply to all authorised non-bank PSOs.
PSOs must ensure adherence to these Directions by unregulated entities in their digital payments ecosystem, such as payment gateways, third-party service providers, vendors, and merchants.
The PSO’s Board of Directors is responsible for ensuring adequate oversight over information security risks, including cyber risk and cyber resilience. A sub-committee of the Board may be delegated with primary oversight responsibilities.
PSOs must formulate a Board-approved Information Security (IS) policy that covers roles and responsibilities, measures to identify and manage cyber security risks, training and awareness programs, and more.
PSOs should have a distinct Board-approved Cyber Crisis Management Plan (CCMP) to detect, contain, respond, and recover from cyber threats and attacks.
A senior-level executive, such as a Chief Information Security Officer (CISO), should be responsible for implementing the IS policy and the cyber resilience framework and assessing the overall information security posture of the PSO.
PSOs need to define Key Risk Indicators (KRIs) and Key Performance Indicators (KPIs) to identify potential risk events and assess the effectiveness of security controls. The sub-committee of the Board is responsible for monitoring these indicators.
PSOs should conduct a cyber risk assessment when launching new products, services, technologies, or significant changes to existing infrastructure or processes.
PSOs, including inventory management, identity and access management, network security, application security life cycle, security testing, vendor risk management, data security, patch and change management life cycle, incident response, business continuity planning, API security, employee awareness and training, and other security measures should implement various baseline information security measures and controls.
PSOs should ensure that payment transactions involving debit to accounts conducted electronically are permitted only through multi-factor authentication, except where explicitly permitted/relaxed.

Conclusion
The relationship between cyber law and the banking industry is crucial in ensuring a secure and trusted digital environment. Recent trends indicate that cyber threats are evolving and becoming more sophisticated. Compliance with cyber law provisions and adherence to guidelines such as those provided by the RBI is essential for banks to protect themselves and their customers from cybercrimes. By embracing robust cyber law frameworks, the banking industry can foster a resilient ecosystem that enables innovation while safeguarding the interests of all stakeholders or users.

Introduction
The insurance industry is a target for cybercriminals due to the sensitive nature of the information it holds. This makes it essential for insurance companies to have robust cybersecurity measures to protect their data and customers’ personal information.
Cyber fraud in India’s insurance industry is increasing. It is reported that the Indian insurance sector has witnessed a surge in cyber-attacks, with several instances of data breaches, identity thefts, and financial fraud being reported. These cybercrimes not only pose a significant threat to the financial stability of the insurance industry but also to the privacy and security of policyholders.
Cyber Frauds in the Insurance Industry
The insurance industry in India has been the target of increasing cyber fraud in recent years. With the growing digital transformation trend, insurance companies have become increasingly vulnerable to cyber-attacks. Cyber frauds in the insurance industry are initiated by hackers who use various techniques such as phishing, malware, ransomware, and social engineering to gain unauthorised access to policyholders’ personal data and sensitive information
Kinds of cyber frauds in the insurance industry
It is essential for insurers and policyholders alike to be aware of these kinds of cyber-attacks on insurance companies in today’s digital age. Staying educated about these threats can help prevent them from happening in the future.
Identity theft– One common type of cyber fraud that occurs in the insurance industry is identity theft. In this type of fraud, criminals steal personal information such as name, address, date of birth and social security numbers through phishing emails or fraudulent websites. They then use this information to open fraudulent policies or access existing ones.
Payment fraud- Another type of cyber fraud that is on the rise is payment fraud. In this type of fraud, hackers intercept electronic payments made by policyholders or agents using fake bank accounts or compromised payment gateways. The money is then siphoned into untraceable accounts, making it difficult for law enforcement agencies to identify and arrest the perpetrators.
Phishing attacks- Where the fraudsters posed as company officials and sent emails to policyholders requesting their account details. The unsuspecting customers fell for this scam and shared their sensitive information, which was then used to access their accounts and steal funds.
Hacking- Where hackers breach the company’s system to gain access to policyholder data. The hackers’ stoles personal records, including names, addresses, phone numbers, social security numbers, and financial information, which they later sell on the dark web.
Fake policies scam- Fraudsters create fake policies using stolen identities and collect premiums from innocent customers. The insurer then voided these policies due to fraudulent activity leaving those people without valid coverage when they needed it most. The victims suffer significant financial losses due to this scam.
Fake Insurance Websites- Discuss the creation of deceptive websites that imitate well-known insurance companies, where unsuspecting individuals provide their personal details, leading to identity theft or financial losses.

Prevention of Cyber Frauds in the Insurance Industry- Best practices to follow
Prevention is better than cure, which also holds true in the case of cyber fraud in the insurance industry. The industry must take proactive steps to prevent such frauds from occurring in the first place. One of the most effective ways to do so is by investing in cybersecurity measures that are specifically designed for the insurance sector.
Insurance companies must conduct regular employee training programs on cybersecurity best practices. This includes educating employees on how to identify and avoid phishing emails, create strong passwords, and recognise potential cyber threats. Companies should also establish a reporting mechanism for employees to report suspicious activity or incidents immediately.
Having proper access controls in place is also necessary. This means limiting access to sensitive data only to those employees who need it, implementing two-factor authentication, and regularly monitoring user activity logs. Regular audits can also provide an extra layer of protection against potential threats by identifying vulnerabilities that may have been overlooked during routine security checks.
Another essential step is encrypting all data transmitted between different systems and devices. Encryption scrambles data into unreadable codes that can only be deciphered using a decryption key, making it difficult for hackers to intercept or steal information in transit.
Legal Framework for Cyber Frauds in the Insurance Industry
The legal framework for cyber fraud in the insurance industry is critical to preventing such crimes. The Insurance Regulatory and Development Authority of India (IRDAI) has issued guidelines for insurers to establish a cybersecurity framework. The guidelines require insurers to conduct regular risk assessments, implement security measures, and ensure compliance with data privacy laws.
The Information Technology Act 2000, is another significant piece of legislation dealing with cyber fraud in India. The act defines offences such as unauthorised access to a computer system, hacking, and tampering with data. It also provides for stringent penalties and imprisonment for those found guilty of such offences.
The IRDAI’s guidelines provide insurers with a roadmap to establish robust cybersecurity measures to help prevent cyber fraud in the insurance industry. Stringent implementation of these guidelines will go a long way in safeguarding sensitive customer information from falling into the wrong hands.
Best Practices for Insurers and Policyholders
Insurers:
Implementing Strong Authentication: Encouraging the use of multi-factor authentication and secure login processes to safeguard customer accounts and prevent unauthorised access.
Regular Employee Training: Conduct cybersecurity awareness programs to educate employees about the latest threats and preventive measures.
Investing in Advanced Technologies: Utilizing robust cybersecurity tools and systems to promptly detect and mitigate potential cyber threats.
Policyholders:
Vigilance and Awareness: Policyholders must stay vigilant while sharing personal information online and verify the authenticity of insurance websites and communication channels.
Regular Updates and Patches: Advising individuals to keep their devices and software up to date to minimise vulnerabilities that cybercriminals can exploit.
Secure Online Practices: Encouraging the use of strong and unique passwords, avoiding sharing sensitive information on unsecured networks, and exercising caution when clicking on suspicious links or attachments.

Conclusion
As the Indian insurance industry embraces digitisation, the risk of cyber scams and data breaches becomes a significant concern. Insurers and policyholders must collaborate to ensure robust cybersecurity measures are in place to protect sensitive information and financial interests.
It is essential for insurance companies to invest in robust cybersecurity measures that can detect and prevent fraud attempts. Additionally, educating employees on the dangers of cyber fraud and implementing strict compliance measures can go a long way in mitigating risks. With these efforts, the insurance industry can continue to provide trustworthy and reliable services to its customers while protecting against cyber threats. As technology continues to evolve, it is imperative that the insurance industry adapts accordingly and remains vigilant against emerging threats.

Introduction
The European Union has fined the meta $ 1.3 billion for infringing the EU privacy laws by transferring the personal data of Facebook users to the United States. The EU fined Meta’s business in Ireland. As per the European Union, transferring Personal data to the US is a breach of the General data protection Regulation or European Union law on data protection and privacy.
GDPR Compliance
The terms of GDPR promise to gather users’ personal information legally and under strict conditions. And those who collect and manage personal data must protect users’ personal data from exploitation. The GDPR restricts an organisation’s capacity to transfer personal data outside the EU if the transfer is solely based on that body’s evaluation of the sufficiency of the personal data’s protection. Transfers should only be made where European authorities have determined that a third country, a territory within that third country, or an international organisation provides acceptable protection for data protection.
Violation by Meta
The punishment, announced by Ireland’s Data Protection Commission, might be one of the most significant in the five years since the European Union passed the landmark General Data Protection Regulation. According to regulators, Facebook failed to comply with a 2020 judgment by the European Union’s top court that Facebook data transferred over the Atlantic was not sufficiently safeguarded from American espionage agencies. However, whether Meta will ever need to encrypt Facebook users’ data in Europe is still being determined. Meta announced it would appeal the ruling, launching a potentially legal procedure.
Simultaneously, European Union and American officials are negotiating a new data-sharing pact that would provide legal protections for Meta and scores of other companies to continue moving information between the US and Europe. This pact could overturn much of the European Union’s Monday ruling.
Article 46(1) GDPR Has been violated by the meta, And as per the Irish privacy.
What is required by the GDPR before transferring personal information across national boundaries?

Personal data transfers to countries outside the European Economic Area are generally permitted if these nations are regarded to provide a sufficient degree of data protection. According to Article 45 of the GDPR, the European Commission evaluates the degree of personal data protection in third countries.
The European Union judgment demonstrates how government rules are upending the borderless way data has traditionally migrated. Companies are increasingly being pressed to store data within the country where it is acquired rather than allowing it to transfer freely to data centres around the world as a result of data-protection requirements, national security laws, and other regulations.
The US internet giant had previously warned that if forced to stop using SCCs (standard contractual clauses) without a proper alternative data transfer agreement in place, it would be compelled to shut down services such as Facebook and Instagram in Europe.
What will happen next for Facebook in Europe?
The ruling includes a six-month transition period before it must halt data flows, meaning the service will continue to operate in the meantime. (More specifically, Meta has been given a five-month transition period to freeze any future transfer of personal data to the United States and a six-month deadline to terminate the unlawful processing and/or storage of European user data it has previously transferred without a legitimate legal basis. Meta has also stated that it will appeal and appears to seek a stay of execution while it pursues its legal arguments in court.
Conclusion
The GDPR places restrictions on transferring personal data outside the European Union to third-party nations or international bodies to ensure that the GDPR’s level of protection for individuals is not jeopardised. But the meta violated the European Union’s privacy laws by the user’s personal information to the US. Under the compliance of GDPR, transferring and sending personal information to users intentionally is an offence. and presently, the personal data of Facebook users has been breached by the Meta, as they shared the information with the US.

Introduction
Recent advances in space exploration and technology have increased the need for space laws to control the actions of governments and corporate organisations. India has been attempting to create a robust legal framework to oversee its space activities because it is a prominent player in the international space business. In this article, we’ll examine India’s current space regulations and compare them to the situation elsewhere in the world.
Space Laws in India
India started space exploration with Aryabhtta, the first satellite, and Rakesh Sharma, the first Indian astronaut, and now has a prominent presence in space as many international satellites are now launched by India. NASA and ISRO work closely on various projects
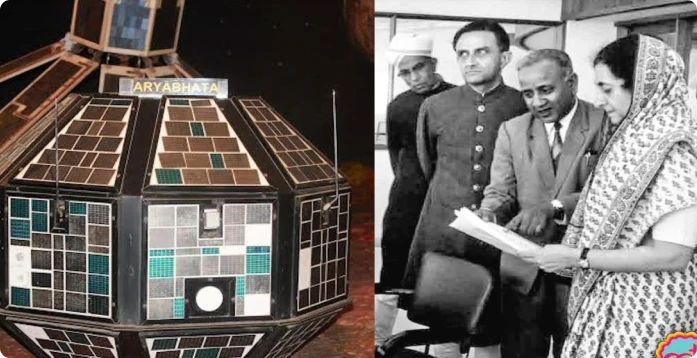
India currently lacks any space-related legislation. Only a few laws and regulations, such as the Indian Space Research Organisation (ISRO) Act of 1969 and the National Remote Sensing Centre (NRSC) Guidelines of 2011, regulate space-related operations. However, more than these rules and regulations are essential to control India’s expanding space sector. India is starting to gain traction as a prospective player in the global commercial space sector. Authorisation, contracts, dispute resolution, licencing, data processing and distribution related to earth observation services, certification of space technology, insurance, legal difficulties related to launch services, and stamp duty are just a few of the topics that need to be discussed. The necessary statute and laws need to be updated to incorporate space law-related matters into domestic laws.
India’s Space Presence
Space research activities were initiated in India during the early 1960s when satellite applications were in experimental stages, even in the United States. With the live transmission of the Tokyo Olympic Games across the Pacific by the American Satellite ‘Syncom-3’ demonstrating the power of communication satellites, Dr Vikram Sarabhai, the founding father of the Indian space programme, quickly recognised the benefits of space technologies for India.
As a first step, the Department of Atomic Energy formed the INCOSPAR (Indian National Committee for Space Research) under the leadership of Dr Sarabhai and Dr Ramanathan in 1962. The Indian Space Research Organisation (ISRO) was formed on August 15, 1969. The prime objective of ISRO is to develop space technology and its application to various national needs. It is one of the six largest space agencies in the world. The Department of Space (DOS) and the Space Commission were set up in 1972, and ISRO was brought under DOS on June 1, 1972.

Since its inception, the Indian space programme has been orchestrated well. It has three distinct elements: satellites for communication and remote sensing, the space transportation system and application programmes. Two major operational systems have been established – the Indian National Satellite (INSAT) for telecommunication, television broadcasting, and meteorological services and the Indian Remote Sensing Satellite (IRS) for monitoring and managing natural resources and Disaster Management Support.
Global Scenario
The global space race has been on and ever since the moon landing in 1969, and it has now transformed into the new cold war among developed and developing nations. The interests and assets of a nation in space need to be safeguarded by the help of effective and efficient policies and internationally ratified laws. All nations with a presence in space do not believe in good for all policy, thus, preventive measures need to be incorporated into the legal system. A thorough legal framework for space activities is being developed by the United Nations Office for Outer Space Affairs (UNOOSA). The “Outer Space Treaty,” a collection of five international agreements on space law, establishes the foundation of international space law. The agreements address topics such as the peaceful use of space, preventing space from becoming militarised, and who is responsible for damage caused by space objects. Well-established space laws govern both the United States and the United Kingdom. The National Aeronautics and Space Act, which was passed in the US in 1958 and established the National Aeronautics and Space Administration (NASA) to oversee national space programmes, is in place there. The Outer Space Act of 1986 governs how UK citizens and businesses can engage in space activity.

Conclusion
India must create a thorough legal system to govern its space endeavours. In the space sector, there needs to be a legal framework to avoid ambiguity and confusion, which may have detrimental effects. The Pacific use of space for the benefit of humanity should be covered by domestic space legislation in India. The overall scenario demonstrates the requirement for a clearly defined legal framework for the international acknowledgement of a nation’s space activities. India is fifth in the world for space technology, which is an impressive accomplishment, and a strong legal system will help India maintain its place in the space business.

Pretext
On 20th October 2022, the Competition Commission of India (CCI) imposed a penalty of Rs. 1,337.76 crores on Google for abusing its dominant position in multiple markets in the Android Mobile device ecosystem, apart from issuing cease and desist orders. The CCI also directed Google to modify its conduct within a defined timeline. Smart mobile devices need an operating system (OS) to run applications (apps) and programs. Android is one such mobile operating system that Google acquired in 2005. In the instant matter, the CCI examined various practices of Google w.r.t. licensing of this Android mobile operating system and various proprietary mobile applications of Google (e.g., Play Store, Google Search, Google Chrome, YouTube, etc.).
The Issue
Google was found to be misusing its dominant position in the tech market, and the same was the reason behind the penalty. Google argued about the competitive constraints being faced from Apple. In relation to understanding the extent of competition between Google’s Android ecosystem and Apple’s iOS ecosystem, the CCI noted the differences in the two business models, which affect the underlying incentives of business decisions. Apple’s business is primarily based on a vertically integrated smart device ecosystem that focuses on the sale of high-end smart devices with state-of-the-art software components. In contrast, Google’s business was found to be driven by the ultimate intent of increasing users on its platforms so that they interact with its revenue-earning service, i.e., online searches, which directly affects the sale of online advertising services by Google. It was seen that google had created a dominant position among the android phone manufacturers as they were made to have a set of google apps preinstalled in the device to increase the user’s dependency on google services. The CCI felt that Google had created a dominant position to which they replied that the same operations are done by Apple as well, to which the commission responded that apple is a phone and app manufacturer and they have Apple-owned apps in Apple devices only, but Google here in had made a pseudo mandate for android manufactures to have the google apps pre-installed which is, in turn, a possible way of disrupting the market equilibrium and violative of market practices. The CCI imposed a penalty of Rs. 1,337.76 for abusing its dominant position in multiple markets in India, CCI delineated the following five relevant markets in the present matter –

- The market for licensable OS for smart mobile devices in India
- The market for app store for Android smart mobile OS in India
- The market for general web search services in India
- The market for non-OS specific mobile web browsers in India
- The market for online video hosting platforms (OVHP) in India.
Supreme Courts Opinion
In October 2022, the Competition Commission of India (CCI) ruled that Google, owned by Alphabet Inc, exploited its dominant position in Android and told it to remove restrictions on device makers, including those related to the pre-installation of apps and ensuring exclusivity of its search. Google lost a challenge in the Supreme Court to block the directives, as the learned court refused to put a stay on the imposed penalty, further giving seven days to comply. The Supreme Court has said a lower tribunal—where Google first challenged the Android directives—can continue to hear the company’s appeal and must rule by March 31.
Counterpoint Research estimates that about 97% of 600 million smartphones in India run on Android. Apple has just a 3% share. Hoping to block the implementation of the CCI directives, Google challenged the CCI order in the Supreme Court by warning it could stall the growth of the Android ecosystem. It also said it would be forced to alter arrangements with more than 1,100 device manufacturers and thousands of app developers if the directives kick in. Google has been concerned about India’s decision as the steps are seen as more sweeping than those imposed in the European Commission’s 2018 ruling. There it was fined for putting in place what the Commission called unlawful restrictions on Android mobile device makers. Google is still challenging the record $4.3 billion fine in that case. In Europe, Google made changes later, including letting Android device users pick their default search engine, and said device makers would be able to license the Google mobile application suite separately from the Google Search App or the Chrome browser.
Conclusion
As the world goes deeper into cyberspace, the big tech companies have more control over the industry and the markets, but the same should not turn into anarchy in the global markets. The Tech giants need to be made aware that compliance is the utmost duty for all companies, and enforcement of the law of the land will be maintained no matter what. Earlier India lacked policies and legislation to govern cyberspace, but in the recent proactive stance by the govt, a lot of new bills have been tabled, one of them being the Intermediary Rules 2021, which has laid down the obligations nand duties of the companies by setting up an intermediary in the country. Such bills coupled with such crucial judgments on tech giants will act as a test and barrier for other tech companies who try to flaunt the rules and avoid compliance.

What are Wi-Fi attacks?
Wi-fi is an important area of cyber security and there is no need for physical cable for the network. Wi-Fi has access to a network signal radius everywhere. The devices and systems can have a network without physical access due to Wi-fi. But everything comes with cons and pros, and if we talk about cybersecurity, it has been established that Wi-fi networks are extremely vulnerable to security breaches and it is very easy to be hacked by hackers. Wi-Fi can be accessed by almost every device in the modern day: it can be smartphones, tablets, computers, and laptops. To know whether someone has been tampering with your personal Wi-Fi there are certain signs that can prove it. The first and most important sign is that your internet speed gets slower, as someone else is using your Wi-Fi surf.
Why would anyone hack someone’s Wi-Fi network?
Usually, hackers hack the network because they want access to the confidential data of someone and they can observe all the online activities and data that have been sent through a network. An unauthorize hacker will pretty much be able to see everything you do online. Wi-Fi allows hackers o view information on sites. Any financial information which is saved in the browser can be accessed by hackers and they can alter it and can alter the content you see online. And all the information saved in Wi-fi networks can be used by hackers for their own benefit, they can sell it, impersonate you, or even take money out of your bank through Wi-Fi.
Avoiding vulnerable Wi-Fi networks
The first and foremost rule of protection is that you should not use public networks if that network is easily open to you then that is also available to others and from others, and someone can who wishes to use your confidential and sensitive information, can access that. If you really need to access the public network in an urgent situation, then you must make sure to limit your activities while connected. And avoid accessing your online banking or pages that require login information. Also, a good measure to take as well is to always delete your cookies after using public WIFI.
How To Secure Your Home Wi-Fi Network
Your home’s wireless internet connection is your Wi-Fi network. Typically, a wireless router is used, which broadcasts a signal into the atmosphere. You can connect to the internet using that signal. However, if your network is not password-protected, any nearby device can grab the signal off the air and connect to your internet. The benefit of Wi-Fi? Wireless access to the internet is possible. The negative? Your internet activity, including your personal information, may be visible to neighboring users who connect to your unprotected network. Furthermore, if someone uses your network to conduct a crime or send out unauthorized spam, you might be held accountable.
Wi-Fi or Li-Fi? –
The common consensus is that Li-Fi technology is more secure than Wi-Fi. Li-Fi systems can be made more secure by integrating a variety of security features. Although these qualities might appear when Li-Fi is widely used in the near future, it is already thought to be safer because of a number of security features. Since the connection’s characteristics make it simpler to lock connections, limit access, and track users even in the absence of encryption and other security features, Li-Fi is seen as being safer. Li-Fi systems will be able to support new security protocols, which will not only enable high-speed networking but also open the door for innovative security techniques to strengthen connections.
Conclusion
A hacker can sniff the network packets without having to be in the same building where the network is located. As wireless networks communicate through radio waves, a hacker can easily sniff the network from a nearby location. Most attackers use network sniffing to find the SSID and hack a wireless network.
Any wireless network can theoretically be attacked in a number of different ways. Use of the default SSID or password, WPS pin authentication, insufficient access control, and leaving the access point available in open locations are all examples of potential vulnerabilities that could allow for the theft of sensitive data. Kismet’s architecture in WIDS mode may guard against DOS, MiTM, and MAC spoofing attacks. routine software updates on the other hand, the use of firewalls may help defend the network against outside intrusion. The act of finding infrastructure issues that could allow harmful code to be injected into a service, system, or organization is known as ethical hacking. They use this technique to prevent invasions by lawfully breaking into networks and looking for weak spots.

Introduction
Google Play has announced its new policy which will ensure trust and transparency on google play by providing a new framework for developer verification and app details. The new policy requires that new developer accounts on Google Play will have to provide a D-U-N-S number to verify the business. So when an organisation will create a new Play Console developer account the organisation will need to provide a D-U-N-S number. Which is a nine-digit unique identifier which will be used to verify their business. The new google play policy aims to enhance user trust. And the developer will provide detailed developer details on the app’s listing page. Users will get to know who is behind the app which they are installing.
Verifying Developer Identity with D-U-N-S Numbers
To boost security the google play new policy requires the developer account to provide the D-U-N-S number when creating a new Play Console developer account. The D-U-N-S number assigned by Dun & Bradstreet will be used to verify the business. Once the developer creates his new Play Console developer account by providing a D-U-N-S number, Google Play will verify the developer’s details, and he will be able to start publishing the apps. Through this step, Google Play aims to validate the business information in a more authentic way.
If your organisation does not have a D-U-N-S number, you may check on or request for it for free on this website (https://www.dnb.com/duns-number/lookup.html). The request process for D-U-N-S can take up to 30 days. Developers are also required to keep the information up to date.
Building User Trust with Enhanced App Details
In addition to verifying developer identities in a more efficient way, google play also requires that developer provides sufficient app details to the users. There will be an “App Support” section on the app’s store listing page, where the developer will display the app’s support email address and even can include their website and phone number for support.
The new section “About the developer” will also be introduced to provide users with verified identity information, including the developer’s name, address, and contact details. Which will make the users more informed about the valuable information of the app developers.
Key highlights of the Google Play Polic
- Google Play came up with the policy to keep the platform safe by verifying the developers’ identity and it will also help to reduce the spread of malware apps and help the users to make confident informed decisions about the apps they download. Google Play announced the policy by expanding its developer verification requirement to strengthen Google Play as a platform and build user trust. When you create a new Play Console Developer account and choose organisation as your account type you will now need to provide a D-U-N-S number.
- Users will get detailed information about the developers’ identities and contact information, building more transparency and encouraging responsible app development practices.
- This policy will enable the users to make informed choices about the apps they download.
- The new “App support” section will provide enhanced communication between users and developers by displaying support email addresses, website and support phone numbers, streamlining the support process and user satisfaction.
Timeline and Implementation
The new policy requirements for D-U-N-S numbers will start rolling out on 31 August 2023 for all new Play Console developer accounts. The “About the developer” section will be visible to users as soon as a new app is published. and In October 2023, existing developers will also be required to update and verify their existing accounts to comply with the new verification policy.
Conclusion
Google Play’s new policy will aim to enhance the more transparent app ecosystem. This new policy will provide the users with more information about the developers. Google Play aims to establish a platform where users can confidently discover and download apps. This new policy will enhance the user experience on google play in terms of a reliable and trustworthy platform.

Introduction
Recently, a Consultation Paper on Regulatory Mechanisms for Over-The-Top (OTT) Communication Services was published by the Telecom Regulatory Authority of India (TRAI). The paper explores several OTT regulation-related challenges and solicits input from stakeholders on a suggested regulatory framework. We’ll summarise the paper’s main conclusions in this blog.
Structure of the Paper
The Telecom Regulatory Authority of India’s Consultation Paper on Regulatory Mechanism for Over-The-Top (OTT) Communication Services and Selective Banning of OTT Services intends to solicit comments and recommendations from stakeholders about the regulation of OTT services in India. The paper is broken up into five chapters that cover the introduction and background, issues with regulatory mechanisms for OTT communication services, issues with the selective banning of OTT services, a summary of the issues for consultation, and an overview of international practices on the topic. Written comments from interested parties are requested and may be sent electronically to the Advisor (Networks, Spectrum and Licencing) at TRAI. These comments will also be posted on the TRAI website.
Overview of the Paper
- Chapter 1: Introduction and Background
- The first chapter of the essay introduces the subject of OTT communication services and argues why regulatory frameworks are necessary. The chapter also gives a general outline of the topics and the paper’s organisation that will be covered in the following chapters.
- Chapter 2: Examination of the Issues Related to Regulatory Mechanism for Over-The-Top Communication Services
- The second chapter of the essay looks at the problems with OTT communication service regulation. It talks about the many kinds of OTT services and how they affect the conventional telecom sector. The chapter also looks at the regulatory issues raised by OTT services and the various strategies used by various nations to address them.
- Chapter 3: Examination of the Issues Related to Selective Banning of OTT Services
- The final chapter of the essay looks at the problems of selectively outlawing OTT services. It analyses the justifications for government restrictions on OTT services as well as the possible effects of such restrictions on consumers and the telecom sector. The chapter also looks at the legal and regulatory structures that determine how OTT services are prohibited in various nations.
- Chapter 4: International Practices
- An overview of global OTT communication service best practices is given in the paper’s fourth chapter. It talks about the various regulatory strategies used by nations throughout the world and how they affect consumers and the telecom sector. The chapter also looks at the difficulties regulators encounter when trying to create efficient regulatory frameworks for OTT services.
- Chapter 5: Issues for Consultation
- This chapter is the spirit of the consultation paper as it covers the points and questions for consultation. This chapter has been classified into two sub-sections – Issues Related to Regulatory Mechanisms for OTT Communication Services and Issues Related to the Selective Banning of OTT Services. The inputs will be entirely focused on these sub headers, and the scope, extent, and ambit of the consultation paper rests on these questions and necessary inputs.
Conclusion
An important publication that aims to address the regulatory issues raised by OTT services is the Consultation Paper on Regulatory Mechanisms for Over-The-Top Communication Services. The paper offers a thorough analysis of the problems with OTT service regulation and requests input from stakeholders on the suggested regulatory structure. In order to make sure that the regulatory framework is efficient and advantageous for everyone, it is crucial for all stakeholders to offer their opinion on the document.

Introduction
Twitter Inc.’s appeal against barring orders for specific accounts issued by the Ministry of Electronics and Information Technology was denied by a single judge on the Karnataka High Court. Twitter Inc. was also given an Rs. 50 lakh fine by Justice Krishna Dixit, who claimed the social media corporation had approached the court defying government directives.
As a foreign corporation, Twitter’s locus standi had been called into doubt by the government, which said they were ineligible to apply Articles 19 and 21 to their situation. Additionally, the government claimed that because Twitter was only designed to serve as an intermediary, there was no “jural relationship” between Twitter and its users.
The Issue
In accordance with Section 69A of the Information Technology Act, the Ministry issued the directives. Nevertheless, Twitter had argued in its appeal that the orders “fall foul of Section 69A both substantially and procedurally.” Twitter argued that in accordance with 69A, account holders were to be notified before having their tweets and accounts deleted. However, the Ministry failed to provide these account holders with any notices.
On June 4, 2022, and again on June 6, 2022, the government sent letters to Twitter’s compliance officer requesting that they come before them and provide an explanation for why the Blocking Orders were not followed and why no action should be taken against them.
Twitter replied on June 9 that the content against which it had not followed the blocking orders does not seem to be a violation of Section 69A. On June 27, 2022, the Government issued another notice stating Twitter was violating its directions. On June 29, Twitter replied, asking the Government to reconsider the direction on the basis of the doctrine of proportionality. On June 30, 2022, the Government withdrew blocking orders on ten account-level URLs but gave an additional list of 27 URLs to be blocked. On July 10, more accounts were blocked. Compiling the orders “under protest,” Twitter approached the HC with the petition challenging the orders.
Legality
Additionally, the government claimed that because Twitter was only designed to serve as an intermediary, there was no “jural relationship” between Twitter and its users.
Government attorney Additional Solicitor General R Sankaranarayanan argued that tweets mentioning “Indian Occupied Kashmir” and the survival of LTTE commander Velupillai Prabhakaran were serious enough to undermine the integrity of the nation.
Twitter, on the other hand, claimed that its users have pushed for these rights. Additionally, Twitter maintained that under Article 14 of the Constitution, even as a foreign company, they were entitled to certain rights, such as the right to equality. They also argued that the reason for the account blocking in each case was not stated and that Section 69a’s provision for blocking a URL should only apply to the offending URL rather than the entire account because blocking the entire account would prevent the creation of information while blocking the offending tweet only applied to already-created information.
Conclusion
The evolution of cyberspace has been substantiated by big tech companies like Facebook, Google, Twitter, Amazon and many more. These companies have been instrumental in leading the spectrum of emerging technologies and creating a blanket of ease and accessibility for users. Compliance with laws and policies is of utmost priority for the government, and the new bills and policies are empowering the Indian cyberspace. Non Compliance will be taken very seriously, and the same is legalised under the Intermediary Guidelines 2021 and 2022 by Meity. Referring to Section 79 of the Information Technology Act, which pertains to an exemption from liability of intermediary in some instances, it was said, “Intermediary is bound to obey the orders which the designate authority/agency which the government fixes from time to time.”

Introduction
Cert-In (Indian Computer Emergency Response Team) has recently issued the “Guidelines on Information Security Practices” for Government Entities for Safe & Trusted Internet. The guideline has come at a critical time when the Draft Digital India Bill is about to be released, which is aimed at revamping the legal aspects of Indian cyberspace. These guidelines lay down the policy framework and the requirements for critical infrastructure for all government organisations and institutions to improve the overall cyber security of the nation.
What is Cert-In?
A Computer Emergency Response Team (CERT) is a group of information security experts responsible for the protection against, detection of and response to an organisation’s cybersecurity incidents. A CERT may focus on resolving data breaches and denial-of-service attacks and providing alerts and incident handling guidelines. CERTs also conduct ongoing public awareness campaigns and engage in research aimed at improving security systems. The Ministry of Electronics and Information Technology (MeitY) oversees CERT-In. It regularly releases alerts to help individuals and companies safeguard their data, information, and ICT (Information and Communications Technology) infrastructure.
Indian Computer Emergency Response Team (CERT-In) has been established and appointed as national agency in respect of cyber incidents and cyber security incidents in terms of the provisions of section 70B of Information Technology (IT) Act, 2000.
CERT-In requests information from service providers, intermediaries, data centres, and body corporates to coordinate reaction actions and emergency procedures regarding cyber security incidents. It is a focal point for incident reporting and offers round-the-clock security services. It manages cyber occurrences that are tracked and reported while continuously analysing cyber risks. It strengthens the security barriers for the Indian Internet domain.
Background
India is fast becoming one of the world’s largest connected nations – with over 80 Crore Indians (Digital Nagriks) presently connected and using the Internet and cyberspace – and with this number is expected to touch 120 Crores in the coming few years. The Digital Nagriks of the country are using the Internet for business, education, finance and various applications and services including Digital Government services. Internet provides growth and innovation and at the same time it has seen rise in cybercrimes, user harm and other challenges to online safety. The policies of the Government are aimed at ensuring an Open, Safe & Trusted and Accountable Internet for its users. Government is fully cognizant and aware of the growing cyber security threats and attacks.
It is the Government of India’s objective to ensure that Digital Nagriks experience a Safe & Trusted Internet. Along with ubiquitous applications of Information & Communication Technologies (ICT) in almost all facets of service delivery and operations, continuously evolving cyber threats have become a concern for the Government. Cyber-attacks can come in the form of malware, ransomware, phishing, data breach etc., that adversely affect an organisation’s information and systems. Cyber threats leading to cyber-attacks or incidents can compromise the confidentiality, integrity, and availability of an organisation’s information and systems and can have far reaching impact on essential services and national interests. To protect against cyber threats, it is important for government entities to implement strong cybersecurity measures and follow best practices. As ICT infrastructure of the Government entities is one of the preferred targets of the malicious actors, responsibility of implementing good cyber security practices for protecting computers, servers, applications, electronic systems, networks, and data from digital attacks, also remain with the ICT assets’ owner i.e. Government entity.
What are the new Guidelines about?
The Government of India (distribution of business) Rules, 1961’s First Schedule lists a number of Ministries, Departments, Secretariats, and Offices, along with their affiliated and subordinate offices, which are all subject to the rules. They also comprise all governmental organisations, businesses operating in the public sector, and other governmental entities under their administrative control.
“The government has launched a number of steps to guarantee an accessible, trustworthy, and accountable digital environment. With a focus on capabilities, systems, human resources, and awareness, we are extending and speeding our work in the area of cyber security, according to Rajeev Chandrasekhar, Minister of State for Electronics, Information Technology, Skill Development, and Entrepreneurship.
The Recommendations
- Various security domains are covered in the standards, including network security, identity and access management, application security, data security, third-party outsourcing, hardening procedures, security monitoring, incident management, and security audits.
- For instance, the rules advise using only a Standard User (non-administrator) account to use computers and laptops for regular work regarding desktop, laptop, and printer security in the workplace. Users may only be granted administrative access with the CISO’s consent.
- The usage of lengthy passwords containing at least eight characters that combine capital letters, tiny letters, numerals, and special characters; Never save any usernames or passwords in your web browser. Likewise, never save any payment-related data there.
- They include guidelines created by the National Informatics Centre for Chief Information Security Officers (CISOs) and staff members of Central government Ministries/Departments to improve cyber security and cyber hygiene in addition to adhering to industry best practises.
Conclusion
The government has been proactive in the contemporary times to eradicate the menace of cybercrimes and therreats from the Indian cyberspace and hence now we have seen a series of new bills and polices introduced by the Ministry of Electronics and Information Technology, and various other government organisations like Cert-In and TRAI. These policies have been aimed towards being relevant to time and current technologies. The threats from emerging technologies like web 3.0 cannot be ignored and hence with active netizen participation and synergy between government and corporates will lead to a better and improved cyber ecosystem in India.

Introduction
The Telecom Regulatory Authority of India (TRAI) issued a consultation paper titled “Encouraging Innovative Technologies, Services, Use Cases, and Business Models through Regulatory Sandbox in Digital Communication Sector. The paper presents a draft sandbox structure for live testing of new digital communication products or services in a regulated environment. TRAI seeks comments from stakeholders on several parts of the framework.
What is digital communication?
Digital communication is the use of internet tools such as email, social media messaging, and texting to communicate with other people or a specific audience. Even something as easy as viewing the content on this webpage qualifies as digital communication.
Aim of Paper
- Frameworks are intended to support regulators’ desire for innovation while also ensuring economic resilience and consumer protection. Considering this, the Department of Telecom (DoT) asked TRAI to offer recommendations on a regulatory sandbox framework. TRAI approaches the issue with the goal of encouraging creativity and hastening the adoption of cutting-edge digital communications technologies.
- Artificial intelligence, the Internet of Things, edge computing, and other emerging technologies are revolutionizing how we connect, communicate, and access information, driving the digital communication sector to rapidly expand. To keep up with this dynamic environment, an enabling environment for the development and deployment of novel technologies, services, use cases, and business models is required.
- The regulatory sandbox concept is becoming increasingly popular around the world as a means of encouraging innovation in a range of industries. A regulatory sandbox is a regulated environment in which businesses and innovators can test their concepts, commodities, and services while operating under changing restrictions.
- Regulatory Sandbox will benefit the telecom startup ecosystem by providing access to a real-time network environment and other data, allowing them to evaluate the reliability of new applications before releasing them to the market. Regulatory Sandbox also attempts to stimulate cross-sectoral collaboration for carrying out such testing by engaging the assistance of other ministries and departments in order to give the starting company with a single window for acquiring all clearances.
What is regulatory sandbox?
- A regulatory sandbox is a controlled regulatory environment in which new products or services are tested in real-time.
- It serves as a “safe space” for businesses because authorities may or may not allow certain relaxations for the sole purpose of testing.
- The sandbox enables the regulator, innovators, financial service providers, and clients to perform field testing in order to gather evidence on the benefits and hazards of new financial innovations, while closely monitoring and mitigating their risks.
What are the advantages of having a regulatory sandbox?
- Firstly, regulators obtain first-hand empirical evidence on the benefits and risks of emerging technologies and their implications, allowing them to form an informed opinion on the regulatory changes or new regulations that may be required to support useful innovation while mitigating the associated risks.
- Second, sandbox customers can evaluate the viability of a product without the need for a wider and more expensive roll-out. If the product appears to have a high chance of success, it may be authorized and delivered to a wider market more quickly.
Digital communication sector and Regulatory Sandbox
- Many countries’ regulatory organizations have built sandbox settings for telecom tech innovation.
- These frameworks are intended to encourage regulators’ desire for innovation while also promoting economic resilience and consumer protection.
- In this context, the Department of Telecom (DoT) had asked TRAI to give recommendations on a regulatory sandbox framework.
- Written comments on the drafting framework will be received until July 17, 2023, and counter-comments will be taken until August 1, 2023. The Authority’s goal in the digital communication industry is to foster creativity and expedite the use of emerging technologies such as artificial intelligence (AI), the Internet of Things (IoT), and edge computing. These technologies are changing the way individuals connect, engage, and access information, causing rapid changes in the industry.
Conclusion
According to TRAI, these technologies are changing how individuals connect, engage, and obtain information, resulting in significant changes in the sector.
The regulatory sandbox also wants to stimulate cross-sectoral collaboration for carrying out such testing by engaging the assistance of other ministries and departments in order to give the starting company with a single window for acquiring all clearances. The consultation paper covers some of the worldwide regulatory sandbox frameworks in use in the digital communication industry, as well as some of the frameworks in use inside the country in other sectors.

Introduction
The Telecom Regulatory Authority of India (TRAI) has directed all telcos to set up detection systems based on Artificial Intelligence and Machine Learning (AI/ML) technologies in order to identify and control spam calls and text messages from unregistered telemarketers (UTMs).
The TRAI Directed telcos
The telecom regulator, TRAI, has directed all Access Providers to detect Unsolicited commercial communication (UCC)by systems, which is based on Artificial Intelligence and Machine Learning to detect, identify, and act against senders of Commercial Communication who are not registered in accordance with the provisions of the Telecom Commercial Communication Customer Preference Regulations, 2018 (TCCCPR-2018). Unregistered Telemarketers (UTMs) are entities that do not register with Access Providers and use 10-digit mobile numbers to send commercial communications via SMS or calls.
TRAI steps to curb Unsolicited commercial communication
TRAI has taken several initiatives to reduce Unsolicited Commercial Communication (UCC), which is a major source of annoyance for the public. It has resulted in fewer complaints filed against Registered Telemarketers (RTMs). Despite the TSPs’ efforts, UCC from Unregistered Telemarketers (UTMs) continues. Sometimes, these UTMs use messages with bogus URLs and phone numbers to trick clients into revealing crucial information, leading to financial loss.
To detect, identify, and prosecute all Unregistered Telemarketers (UTMs), the TRAI has mandated that Access Service Providers implement the UCC.
Detect the System with the necessary functionalities within the TRAI’s Telecom Commercial Communication Customer Preference Regulations, 2018 framework.
Access service providers have implemented such detection systems based on their applicability and practicality. However, because UTMs are constantly creating new strategies for sending unwanted communications, the present UCC detection systems provided by Access Service providers cannot detect such UCC.
TRAI also Directs Telecom Providers to Set Up Digital Platform for Customer Consent to Curb Promotional Calls and Messages.
Unregistered Telemarketers (UTMs) sometimes use messages with fake URLs and phone numbers to trick customers into revealing essential information, resulting in financial loss.

TRAI has urged businesses like banks, insurance companies, financial institutions, and others to re-verify their SMS content templates with telcos within two weeks. It also directed telecom companies to stop misusing commercial messaging templates within the next 45 days.
The telecom regulator has also instructed operators to limit the number of variables in a content template to three. However, if any business intends to utilise more than three variables in a content template for communicating with their users, this should be permitted only after examining the example message, as well as adequate justifications and justification.
In order to ensure consistency in UCC Detect System implementations, TRAI has directed all Access Providers to deploy UCC and detect systems based on artificial intelligence and Machine Learning that are capable of constantly evolving to deal with new signatures, patterns, and techniques used by UTMs.
Access Providers have also been directed to use the DLT platform to share intelligence with others. Access Providers have also been asked to ensure that such UCC Detect System detects senders that send unsolicited commercial communications in bulk and do not comply with the requirements. All Access Providers are directed to follow the instructions and provide an update on actions done within thirty days.
The move by TRAI is to curb the menacing calls as due to this, the number of scam cases is increasing, and now a new trend of scams started as recently, a Twitter user reported receiving an automated call from +91 96681 9555 with the message “This call is from Delhi Police.” It then asked her to stay in the queue since some of her documents needed to be picked up. Then he said he works as a sub-inspector at the Kirti Nagar police station in New Delhi. He then inquired whether she had recently misplaced her Aadhaar card, PAN card, or ATM card, to which she replied ‘no’. The scammer then poses as a cop and requests that she authenticate the last four digits of her card because they have found a card with her name on it. And a lot of other people tweeted about it.

Conclusion
TRAI directed the telcos to check the calls and messages from Unregistered numbers. This step of TRAI will curb the pesky calls and messages and catch the Frauds who are not registered with the regulation. Sometimes the unregistered sender sends fraudulent links, and through these fraudulent calls and messages, the sender tries to take the personal information of the customers, which results in financial losses.

Introduction
To combat the problem of annoying calls and SMS, telecom regulator TRAI has urged service providers to create a uniform digital platform in two months that will allow them to request, maintain, and withdraw customers’ approval for promotional calls and messages. In the initial stage, only subscribers will be able to initiate the process of registering their consent to receive promotional calls and SMS, and later, business entities will be able to contact customers to seek their consent to receive promotional messages, according to a statement issued by the Telecom Regulatory Authority of India (TRAI) on Saturday.
TRAI Directs Telecom Providers to Set Up Digital Platform
TRAI has now directed all access providers to develop and deploy the Digital Consent Acquisition (DCA) facility for creating a unified platform and process to digitally register customers’ consent across all service providers and principal entities. Consent is received and maintained under the current system by several key entities such as banks, other financial institutions, insurance firms, trading companies, business entities, real estate businesses, and so on.
The purpose, scope of consent, and the principal entity or brand name shall be clearly mentioned in the consent-seeking message sent over the short code,” according to the statement.
It stated that only approved online or app links, call-back numbers, and so on will be permitted to be used in consent-seeking communications.
TRAI issued guidelines to guarantee that all voice-based Telemarketers are brought under a single Distributed ledger technology (DLT) platform for more efficient monitoring of nuisance calls and unwanted communications. It also instructs operators to actively deploy AI/ML-based anti-phishing systems as well as to integrate tech solutions on the DLT platform to deal with malicious calls and texts.
TRAI has issued two separate Directions to Access Service Providers under TCCCPR-2018 (Telecom Commercial Communications Customer Preference Regulations) to ensure that all promotional messages are sent through Registered Telemarketers (RTMs) using approved Headers and Message Templates on Distributed Ledger Technologies (DLT) platform, and to stop misuse of Headers and Message Templates,” the regulator said in a statement.
Users can already block telemarketing calls and texts by texting 1909 from their registered mobile number. By dialing 1909, customers can opt out of getting advertising calls by activating the do not disturb (DND) feature.

Telecom providers operate DLT platforms, and businesses involved in sending bulk promotional or transactional SMS must register by providing their company information, including sender IDs and SMS templates.
According to the instructions, telecom companies will send consent-seeking messages using the common short code 127. The goal, extent of consent, and primary entity/brand name must be clearly stated in the consent-seeking message delivered via the shortcode.
TRAI stated that only whitelisted URLs/APKs (Android package kits file format)/OTT links/call back numbers, etc., shall be used in consent-seeking messages.
Telcos must “ensure that promotional messages are not transmitted by unregistered telemarketers or telemarketers using telephone numbers (10 digits numbers).” Telecom providers have been urged to act against all erring telemarketers in accordance with the applicable regulations and legal requirements.
Users can, however, refuse to receive any consent-seeking messages launched by any significant Telcos have been urged to create an SMS/IVR (interactive voice response)/online service for this purpose.
According to TRAI’s timeline, the consent-taking process by primary companies will begin on September 1.According to a nationwide survey conducted by a local circle, 66% of mobile users continue to receive three or more bothersome calls per day, the majority of which originate from personal cell numbers.
There are scams surfacing on the internet with new types of scams, like WhatsApp international call scams. The latest scam is targeting Delhi police, the scammers pretend to be police officials of Delhi and ask for the personal details of the users and the calling them from a 9-digit number.
A recent scam
A Twitter user reported receiving an automated call from +91 96681 9555, stating, “This call is from Delhi Police.” It went on to ask her to stay in the queue since some of her documents needed to be picked up. Then he said he is a sub-inspector at New Delhi’s Kirti Nagar police station. He then questioned if she had lately misplaced her Aadhaar card, PAN card, or ATM card, to which she replied ‘no’. The fraudster then claims to be a cop and asks her to validate the final four digits of her card because they have discovered a card with her name on it. And so many other people tweeted about this.
The scams are constantly increasing as earlier these scammers asked for account details and claimed to be Delhi police and used 9-digit numbers for scamming people.
TRAI’s new guidelines regarding the consent to receive any promotional calls and messages to telecommunication providers will be able to curb the scams.
The e- KYC is an essential requirement as e-KYC offers a more secure identity verification process in an increasingly digital age that uses biometric technologies to provide quick results.

Conclusion
The aim is to prevent unwanted calls and communications sent to customers via digital methods without their permission. Once this platform is implemented, an organization can only send promotional calls or messages with the customer’s explicit approval. Companies use a variety of methods to notify clients about their products, including phone calls, text messages, emails, and social media. Customers, however, are constantly assaulted with the same calls and messages as a result of this practice. With the constant increase in scams, the new guideline of TRAI will also curb the calling of Scams. digital KYC prevents SIM fraud and offers a more secure identity verification method.

Introduction
Online Gaming has gained popularity over the past few years, attracting young players worldwide and global concerns. In response to the growing fame of this industry, the Indian government has recently announced introducing a set of regulations to address various concerns and ensure a safer and more regulated online gaming environment. In this blog post, we will explore the critical aspects of these regulations and their impact on the gaming industry.
Why are Regulations needed?
Recently some games faced a ban in India – games that involve betting, games that can be harmful to the user, and games that involve a factor of addiction. Furthermore, with rising popularity, With the exponential rise of online gaming platforms in India, extensive laws to safeguard players and ensure fair gameplay needs to be implemented. Players’ protection is one of the critical factors addressing the issues which involve online addiction, underage involvement, fraud, and data privacy has become critical for the well-being of Indian gamers.
Regulatory Ambiguity: The previous legislative structure, such as the outmoded Public Gambling Act of 1867, required an update to fit the digital gambling age fully.
Outline of the New Regulations
Implementing new regulations for online gaming in India represents the government’s commitment to addressing different issues and ensuring a safer and more regulated gaming sector. Let’s have a look at these rules in detail:
National-Level Standards: The Indian government is currently working on creating national-level standards to standardise online gaming practices across all states. These rules attempt to create a uniform platform for both operators and participants. The government has also made an announcement to set SRO within 90 days to regulate online gaming.
Licencing and Compliance: To legally operate in the Indian market, online gaming firms must secure licences. The operator’s financial soundness, security measures, and adherence to responsible gaming practices will be scrutinised throughout the licencing process. Operators will need to comply with the regulations in order to maintain operations.
Measures to Promote Ethical Gaming: The new regulations emphasise player protection and ethical gaming practices. This includes steps like age verification to prevent underage involvement, self-exclusion choices for gamers who want to limit their gaming activities, and adopting tools like session limits and reality checks to promote responsible gaming.
Data Privacy: Recognising the importance of data privacy, the laws are intended to contain protections for protecting user data. To safeguard sensitive player information from unauthorised access or exploitation, online gambling operators must comply with data protection regulations and deploy strong security measures.
Restrictions on Advertising and Marketing: The legislation may limit the advertising and marketing of online gaming platforms. The emphasis will be on eliminating aggressive marketing tactics that target vulnerable people, such as kids. Stricter standards for ad content and placement may be implemented.
Anti-Fraud and Anti-Money Laundering Measures: To combat criminal activity within the gaming ecosystem, the new legislation will almost certainly force online gambling companies to employ anti-fraud and anti-money laundering measures. Operators may need to set up mechanisms to detect fraud, report suspicious activity, and work with law enforcement.
Consumer Grievance Redressal: The legislation may emphasise the construction of efficient channels for resolving consumer complaints. Players should be able to report difficulties, seek resolution, and offer feedback on their play experiences through channels. The objective is to create a transparent and accountable conflict resolution mechanism.

Impact on Online Gaming Ecosystem
Adopting new laws for online gambling in India will likely have several consequences for the gaming industry. Let us look at some of these consequences:
Increased Player Trust: Implementing restrictions will increase player confidence in online gaming platforms. Establishing clear rules and procedures and steps to safeguard participants’ interests will develop a sense of trust and transparency. This can lead to increased participation and engagement in the gaming community.
Industry Consolidation: Stricter restrictions may result in industry consolidation. Compliance with the new legislation would need resources and investments, which might favour more prominent and more established gambling firms. Smaller and more non-compliant operators may find it challenging to fulfil regulatory standards, resulting in a more consolidated gaming sector.
Technological Progress: The requirement to comply with rules could lead to technological advancements in the online gambling sector. Operators may invest in modern identity verification systems, fraud detection methods, and responsible gaming solutions to satisfy their regulatory requirements. This can result in technological breakthroughs that improve gamers’ overall gaming experience.
Foreign Investment and Collaboration: Clear laws might entice overseas investors to enter the Indian gaming business. The regulated environment may appeal to international gambling enterprises looking to enter or extend their presence in India. Collaborations between Indian and foreign gaming firms may also expand, resulting in the sharing of experience, resources, and the production of high-quality gaming products.
Legal Clarity: Implementing particular laws would give online gambling operators and users clearer legal standards. This transparency can eliminate ambiguity and possible legal issues, allowing stakeholders to navigate the gaming ecosystem with better confidence and knowledge.
Contribution to the Indian Economy: A well-regulated online gaming business has the potential to contribute to the Indian economy. It has the potential to create jobs, attract investment, and produce tax money for the government. The economic effect of the gaming ecosystem is expected to increase as it grows under the new restrictions.
Challenges and Future Approach
One of the toughest challenges will be the efficient implementation and enforcement of the new regulations. Consistency in applying the legislation across multiple jurisdictions and guaranteeing compliance by all operators would necessitate comprehensive monitoring and regulatory measures. Developing suitable enforcement organisations and transparent standards for reporting and dealing with noncompliance will be critical. Besides this, online gaming is open to more than area-specific and many gaming platforms and operates internationally. Ensuring cross-border operations is a big challenge in addressing jurisdictional challenges will be complex. Collaborative efforts between nations can regulate cross-border online gaming. There may be increased collaboration between Indian and foreign gaming firms, resulting in the exchange of information, skills, and resources. This partnership can help the Indian gaming sector flourish while attracting foreign players and investments.
Esports Development: Esports have grown in popularity worldwide, and India is no exception. The Indian esports business has the potential to thrive with proper regulation and support, drawing both players and viewers. Esports-specific factors like player contracts, tournament integrity, and licencing requirements may be addressed in the regulations.

Conclusion
Despite obstacles, India’s new online gambling legislation can potentially establish a safer and more regulated gaming sector. the future depends on successful implementation, adjusting to a shifting landscape, finding the correct balance between regulation and innovation, and promoting ethical gaming practices. The Indian online gaming business can develop sustainably with the appropriate strategy, benefiting gamers and the broader economy.

Introduction
Ministry of Electronics and Information Technology (MeitY) Announces to Centre Government to Plan to Certify Permissible Online Games.
In a recent update to the notification released by the Ministry of Electronics and Information Technology (MeitY) on April 6, MeitY has requested gaming entities to establish self-regulatory organisations (SROs) within a timeframe of 30 days or a maximum of 90 days from the date of the notification, which is April 6, 2023. The Ministry of Electronics and Information Technology (MeitY) has further announced that the central government will certify which online games are permissible until the SROs are officially established. The intention behind establishing SROs is to assist intermediaries, such as Apple or Google, in determining what constitutes a permitted online game, but the SRO will take 2-3 months to complete. In the meanwhile, the Central government will step in and determine what is a permissible online game.
Information Technology (Intermediary Guidelines and Digital Media Ethics Code) Rules, 2021 & Intermediary Guidelines and Digital Media Ethics Code Amendment Rules, 2023
By enacting these rules, the Indian government has taken decisive action to protect Indian gamers and their financial resources against scams and fraud. The rules also serve to promote responsible gaming while preventing young and vulnerable users from being exposed to indecent or abusive content.
Amendment Rules developed the concept of a “Permissible online real money game.” This designation is reserved for games that have passed a review process conducted by a self-regulatory body (SRB). Amendment rules indicate that Online Gaming Intermediaries must ensure that they do not permit any third party to host non-permissible online real money games on their platforms. This development is important because it empowers us to distinguish between legitimate and illicit real money games.
The Amendment Rules define an online gaming provider as an “intermediary” under the Information Technology Act of 2000, creating a separate classification called ‘Online Gaming Intermediary’.

Central government to certify what is an ‘Online Permissible Game’
The industry has been wondering what games come under wagering and will be banned. So, until the SROs are officially established, the government, in the interim, will certify what is a permissible game, what is wagering, and what is not wagering. Games that involve elements of wagering are going to be barred. The new regulations prohibit wagering on any outcome, whether in skill-based or chance-based games. Hence gaming applications involving wagering and betting apps will be barred.
Self-Regulatory Organizations (SROs)
According to the new regulations by the Ministry of Electronics and Information Technology (MeitY), online gaming intermediaries must establish a Self-Regulatory Body (SRO) to approve games offered to users over the Internet. The SRO must be registered with the Ministry and develop a framework to ensure compliance with the IT Rules 2021 objectives. An ‘online game’ can be registered by the SRO if it meets specific criteria, which include that the game is offered by an online gaming intermediary that is a member of the self-regulatory body, the game is not containing any content harmful to India’s interests, and complying with all relevant Indian regulations. If these requirements are met, the intermediary can display a visible registration mark indicating its registration with the self-regulatory authority.
Conclusion
MeitY found that with the rapid growth of the gaming industry, the real money gaming (RMG) sector had to be regulated properly. Rules framed must be properly implemented to stop gambling, betting, and wagering apps.
The IT Rules 2021, along with the Amendment Rules 2023, are created to take concrete action to curb the proliferation of gambling, betting, and wagering apps in India. These rules empower to issue of directives to ban specific apps that facilitate or promote such activities. The app ban directive allows the government to take decisive action by blocking access to these apps, making them unavailable for download or use within the country. This measure is aimed at curbing the negative impact of gambling, betting, and wagering on individuals and society, including issues related to addiction, financial loss, and illegal activities. Rules aim to actively combat the spread and influence of such apps and provide a safer online environment for gaming users.
The self-regulatory body in the context of online gaming will have the authority to grant membership to gaming intermediaries, register online games, develop a framework for regulation, interact with the Central Government, address user complaints, report instances of non-compliance, and take necessary actions to safeguard online gaming users.

Introduction
India has been a nation where technology penetration has been a little slower in the previous decades; however, that has changed now. Cyberspace has influenced and touched every country and has significantly diminished the gap between developing nations, developed nations, and underdeveloped nations. This has also been substantiated and strengthened during the Covid-19 pandemic as the world went into lockdown and the cyberspace was the only medium of communication and information. India witnessed a rise of 61% in terms of internet users, and a significant part of this number represented rural India.
New Standards
These standards have been released in threefold aspects covering – Digital Television Receivers, USB Type-C chargers, and Video Surveillance Systems, thus streamlining the use of gadgets and reduction of e-waste for the country.
1. Digital Television Receivers
The Indian standard IS 18112:2022 specification for digital television, and this standard would enable reception of free-to-air TV and radio channels just by connecting a dish antenna with LNB mounted on a suitable area with good signal reception. This will help in the transmission of knowledge about government initiatives and schemes, the educational content of Doordarshan, and the repository of Indian cultural programs. Doordarshan is in the process of phasing out analog transmission, and free-to-air channels will continue to be broadcast using digital satellite transmission. The keen aspects of educational and awareness programs run by the Govt and CSOs will impact more Indians than before as the Ministry of Information and Broadcast intends to increase their free channels of Doordarshan from 55 to 200 by the end of this year, which shows the importance of developments in the mass media industry.
2. USB Type C
Standard (IS/IEC 62680-1-3:2022) for USB Type-C receptacles, plugs, and cables adopting the existing global standard IEC 62680-1-3:2022. This standard provides for the requirements for USB type C ports and cables for use in various electronic devices like laptops, mobile phones, and other gadgets. This standard is similar to the new European standard, which is also aimed at the reduction of carbon emissions and e-waste; this move will result in ease for the industry and the end users. This will also contribute towards the strengthening of the cyber security aspects and prevent threats like ‘Juice Jacking’ to a massive extent.
3. Video Surveillance System
IS 16190, this standard provides a detailed outline of the aspects of a video surveillance system, such as requirements for its components like camera devices, interfaces, system requirements, and tests to ascertain the camera’s image quality on different devices. This series of standards would assist customers, installers, and users in establishing their requirements and determining the appropriate equipment required for their intended application and also provide means of evaluating the performance of the VSS objectively. This will also help in the improvement of surveillance by the individuals, and this will also help in the better investigation by Law enforcement agencies and faster apprehension of criminals, thus contributing to an overall safe society.

The Advantages
These standards are in power with the Internationally prevalent standards, thus taking the safety factors to the global aspect. This will also allow the Indian industry to create world-class products which can be shared all across the globe. This will open India to various opportunities and job avenues, thus opening the world to invest in India. The aspect of Atma Nirbhar Bharat and Digital India will be strengthened to a new level as the nation will be able to deliver products in power with quality in developed countries. The end Indian consumer will benefit the most from these upgraded standards in terms of Digital Televisions, Type ‘C’ USB chargers, and Video surveillance systems, as these impacts the consumers’ daily activities in terms of security and access to information.
- Reduction in Carbon Emission
- Production of World Class components and devices
- Boost to the economy and Atmanirbhar Bharat
- New avenues and opportunities for startups and MSMEs
- Better transmission of Knowledge
- Boosting FDI
- Improved quality of products for the end consumer
- New innovation hubs and exposure to global talents
This government move simply shows how India is working toward securing the Sustainable development Goals (SDG) by United Nations. This clearly shares the message to the world that India is ready for the future and will also be a helping hand to various developing and underdeveloped nations in the times to come.
Conclusion
These standards will significantly contribute towards the reduction of E-Waste and unnecessary accessories for daily use gadgets. This strengthens the reduction in carbon emissions and thus contributes towards the perseverance of the environment and working towards sustainable development goals. Such standards will lead the future towards securing the netizens and their new and evolving digital habits. In the current phase of cyberspace, the most essential aspect of establishing Critical Infrastructure as the same will act as a shield against the threats of cyberspace.


