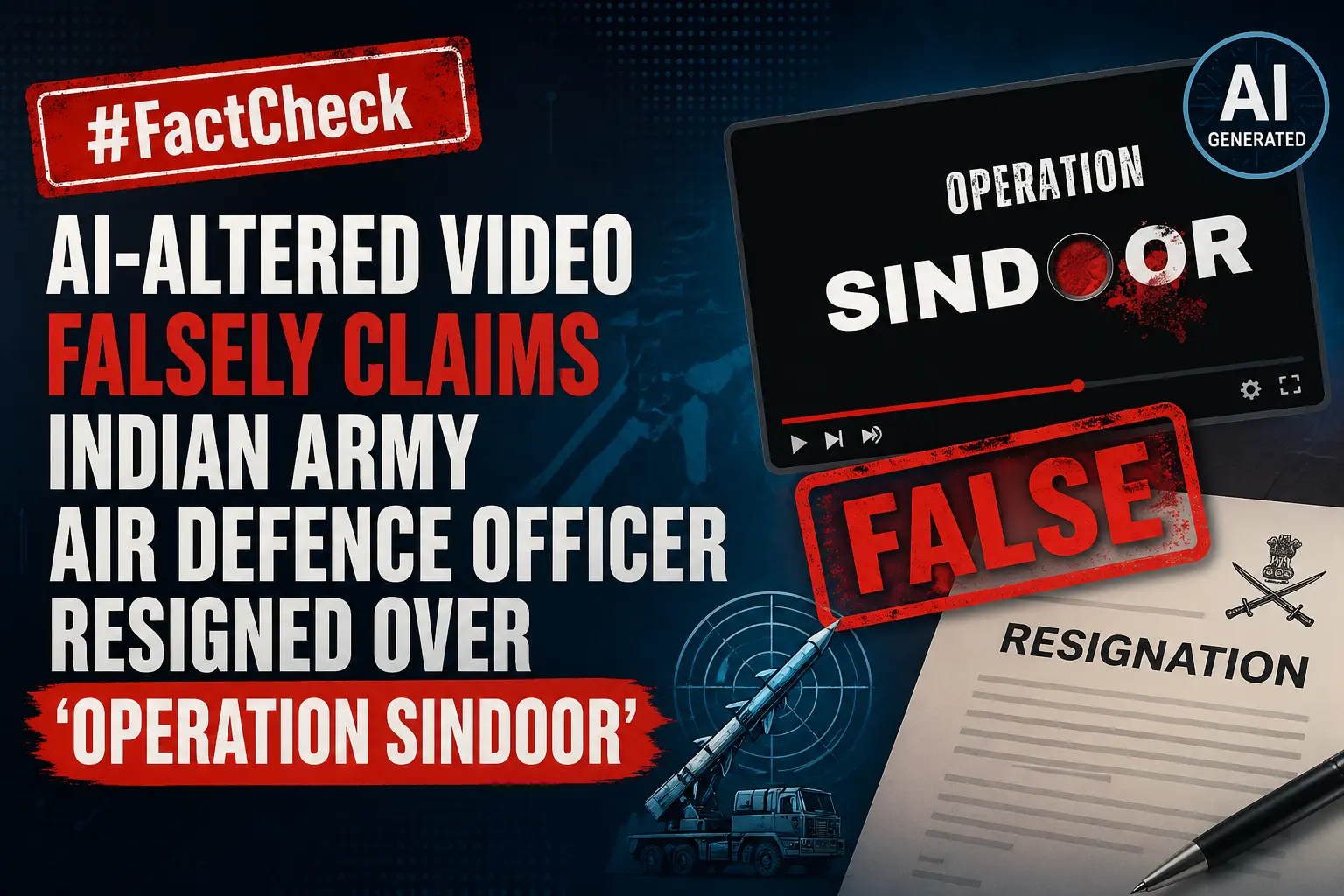
#FactCheck -AI-Generated Video Falsely Shared as IAF Pilot Complaining After Sukhoi-30 Crash
Executive Summary
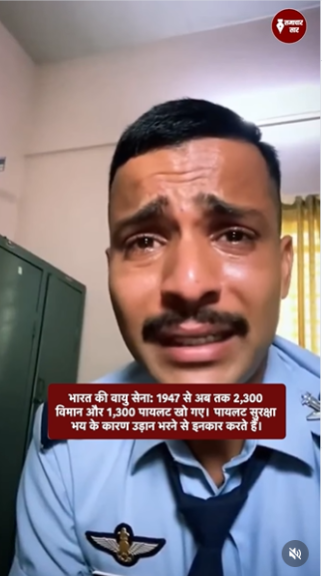
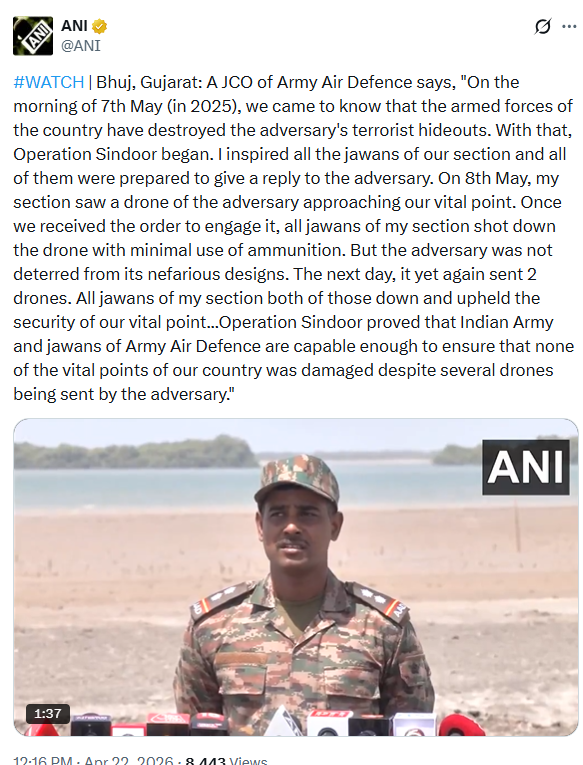
A video circulating widely on social media claims to show a pilot of the Indian Air Force (IAF) crying and expressing fear about flying fighter jets, allegedly citing poor maintenance and frequent crashes. The clip is being linked to the crash of an IAF Sukhoi-30 fighter jet in Assam on March 5, in which two pilots lost their lives. In the viral video, a man dressed like a pilot is seen speaking emotionally, saying that flying fighter jets has become frightening due to lack of maintenance and repeated accidents. Several users are sharing the clip claiming that the man in the video is an IAF pilot revealing the reality behind aircraft crashes. However, research by the CyberPeace found the claim to be false. The video does not depict a real pilot or an actual incident. Instead, it appears to be an AI-generated clip created and circulated with the intent to spread misinformation.
Claim:
An Instagram user, ‘samacharsaar0’, shared the viral video on March 10, 2026, with the English caption: “2300 aircraft crashes, 1300 pilots dead: A major challenge before the IAF.”
- Source: :https://www.instagram.com/reel/DVqa4lNiYJQ
- Archived link::https://perma.cc/EUZ8-DHE3
Fact Check:
The claim was also debunked by PIB Fact Check. While verifying the viral video, PIB clarified that the clip is artificially generated and not related to any real IAF personnel.
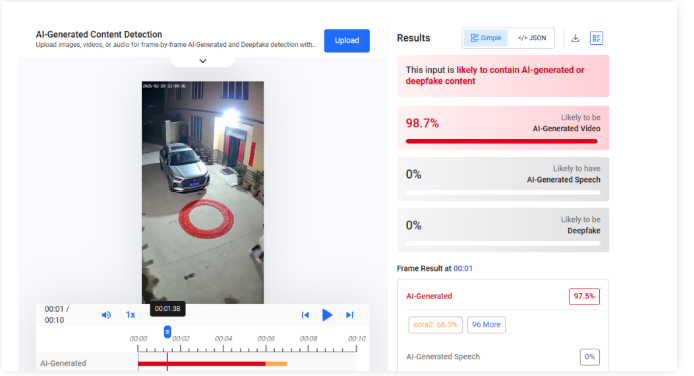
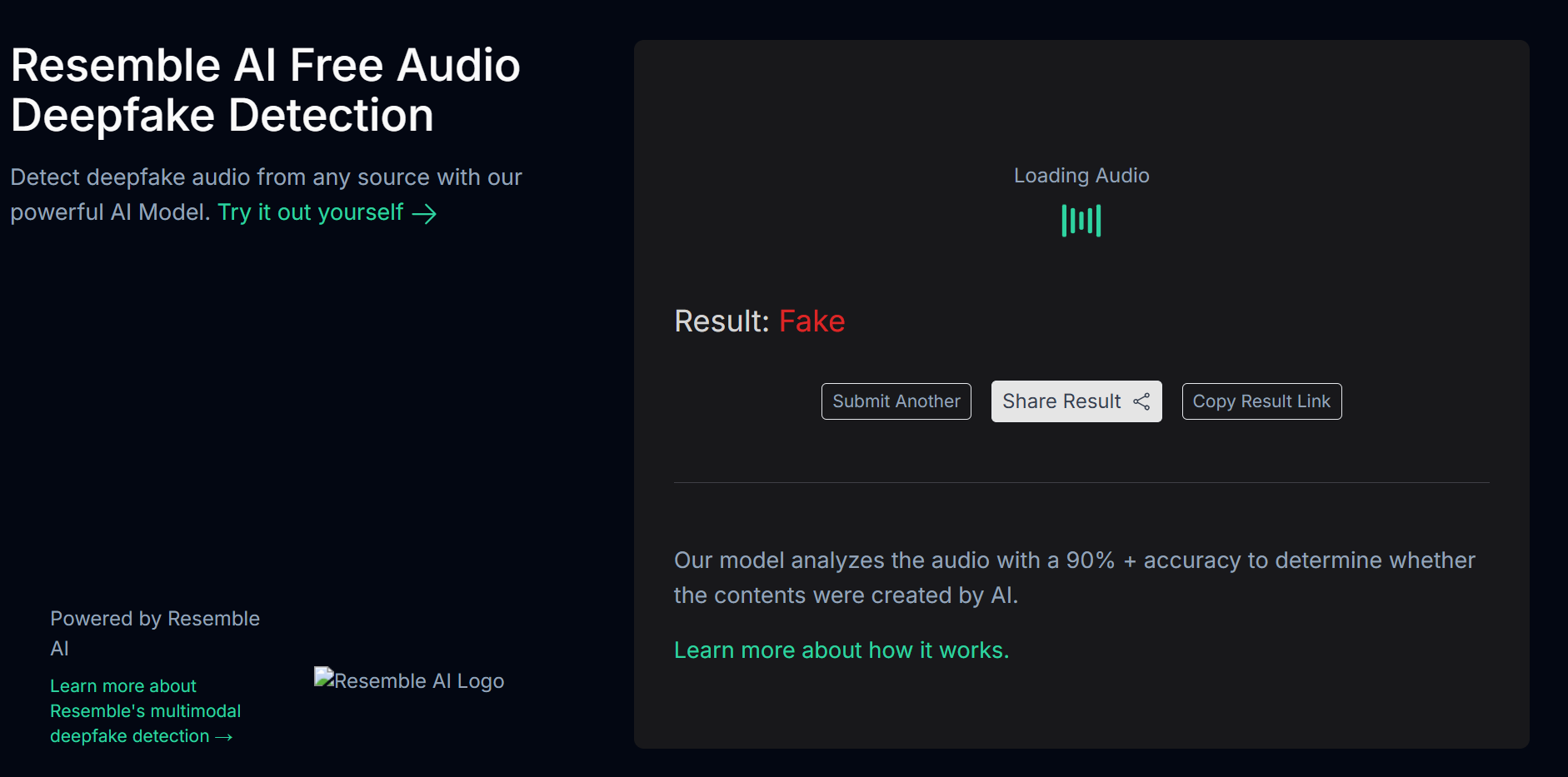
To further verify the authenticity of the video, we analyzed it using AI detection tools. The tool Hive Moderation indicated a 99.9% probability that the video was generated using artificial intelligence.
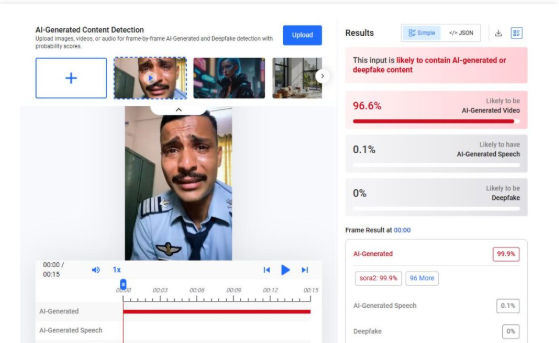
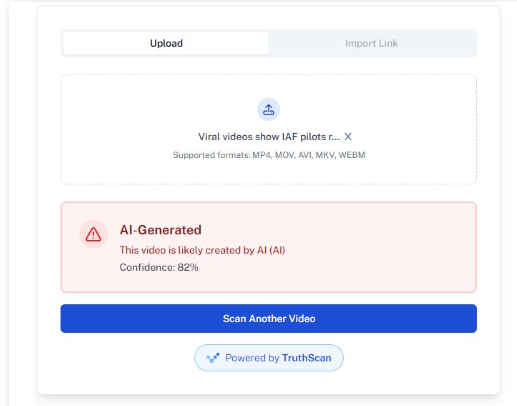
We also examined the clip using another AI detection platform, Undetectable. The analysis suggested an 82% likelihood that the video was created with AI tools. The tool also indicated the possibility that the footage may have been generated using the Sora AI video generation tool.
Conclusion
Our research concludes that the viral video of a crying “pilot” is not authentic. The clip has been created using artificial intelligence and is being misleadingly shared as a real Indian Air Force pilot speaking about aircraft crashes. The government has also denied the claim associated with the video.


.webp)

.webp)