#FactCheck- AI-Generated Deepfake Falsely Attributes Film Remark to Army Chief Upendra Dwivedi
Executive Summary
A video circulating on social media, shared by a Pakistani account, claims to show Indian Army Chief General Upendra Dwivedi making a controversial statement. In the clip, he is allegedly heard saying that he requested Prime Minister Narendra Modi to connect him with film director Ranjan Agnihotri so he could provide inputs and a script for a movie on “Operation Sindoor.”
However, research by CyberPeace has found that the viral video is an AI-generated deepfake. General Upendra Dwivedi has made no such statement.
Claim
A Pakistani user shared the viral video on X (formerly Twitter) on April 10, 2026, making the above claim.
Post links:
- https://x.com/DanishNawaz2773/status/2042312967811973225?s=20
- https://archive.ph/kAwoR

Fact Check
To verify the claim, we conducted keyword searches on Google but found no credible media reports supporting it. Further research led us to the original video posted on the X account of ANI. In this authentic clip, General Upendra Dwivedi is seen speaking at the ‘Ran Samwad’ seminar held in Bengaluru.
In the original video, he discusses the operational aspects of “Operation Sindoor,” including ground intelligence, cyber and electronic warfare inputs, Pakistan’s behaviour, and the challenges of a two-front scenario. There is no mention whatsoever of Pakistan mediation, Prime Minister Modi, Ranjan Agnihotri, any movie script, or a film based on Operation Sindoor.
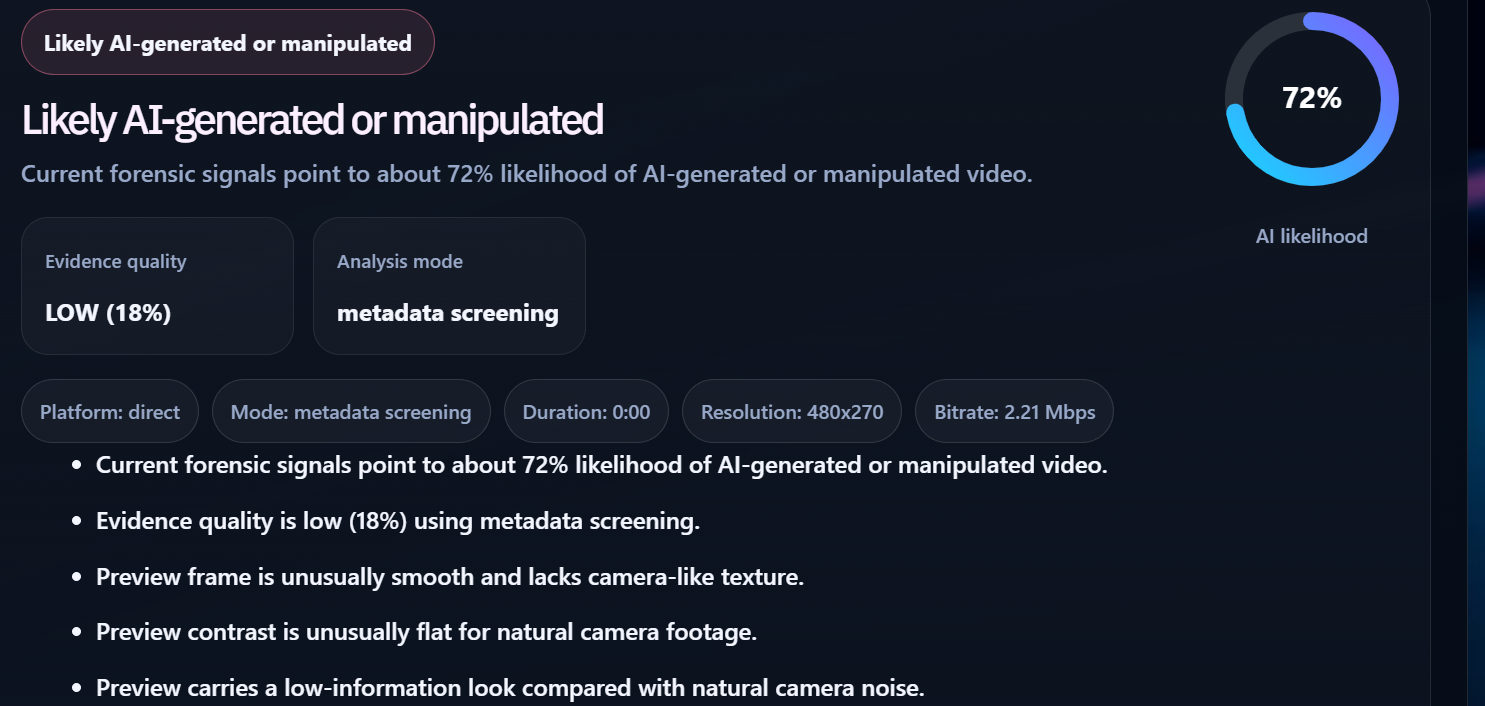
This clearly indicates that the viral clip has been manipulated and taken out of context. The video was further analyzed using the AI detection tool DetectVideo AI, which indicated a 72% probability that the content is AI-generated. This strongly supports the conclusion that the video is a deepfake.
Conclusion
The viral claim is false. The video featuring General Upendra Dwivedi has been digitally altered using AI techniques to insert fabricated statements. The original footage is from the ‘Ran Samwad’ seminar in Bengaluru, where he spoke about military strategy and multi-domain operations, not about any film or director. There is no evidence to suggest that he made any statement regarding contacting a filmmaker or contributing to a movie script. The inclusion of such references in the viral clip is entirely fabricated. This case highlights how AI-generated deepfakes are increasingly being used to spread misinformation, especially in sensitive contexts involving the military and international relations. Viewers are advised to rely on verified sources and exercise caution before sharing such content.
Related Blogs

Executive Summary
Muslims offering prayers inside a crowded train in Japan is being widely shared on social media, amid ongoing discussions around the country’s alleged rise in anti-immigration sentiment. The clip is being presented as a recent and real incident. However, an research reveals that the video is not authentic. Experts noted that the prayer postures shown in the clip do not align with standard Islamic practices, raising doubts about its credibility. Further analysis indicates that the video has been generated using artificial intelligence (AI).
Claim
A user shared the viral video on YouTube, showing a group of men—mostly dressed in long tunics and skullcaps—appearing to offer prayers inside a moving subway train. Passengers can be seen seated on both sides of the carriage. In the clip, two men are kneeling on the floor and bowing their heads onto a small mat placed in front of them, with their heads coming very close to the knees of seated passengers. Another man is seen bending forward at the waist while standing, and a fourth appears to be standing upright with his eyes closed.
- Link: https://www.youtube.com/shorts/cZHMCUgbDIA

,
Fact Check
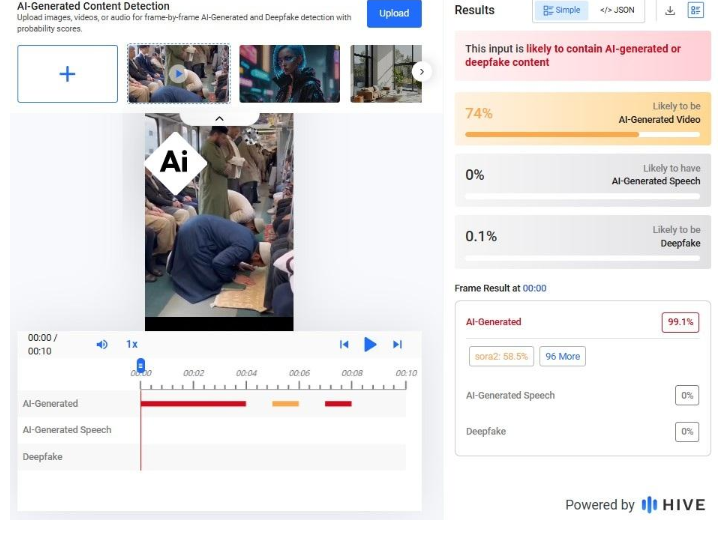
A closer examination of the video reveals several visual inconsistencies. One passenger appears to be fused with the seat rails, creating a distorted overlap. Others seem to be seated in areas where seats do not normally exist, such as directly in front of a door. Additionally, an advertisement visible in the background appears blurred and oddly shaped—another common indicator of AI-generated content. An analysis conducted using the Hive Moderation tool found that the video is “likely to contain AI-generated or deepfake content.”
Conclusion
The viral claim is misleading. The video does not depict a real incident in Japan. Instead, it is likely AI-generated content being circulated with a false narrative, misrepresenting both the context and religious practices shown in the clip.

In the vast, uncharted territories of the digital world, a sinister phenomenon is proliferating at an alarming rate. It's a world where artificial intelligence (AI) and human vulnerability intertwine in a disturbing combination, creating a shadowy realm of non-consensual pornography. This is the world of deepfake pornography, a burgeoning industry that is as lucrative as it is unsettling.
According to a recent assessment, at least 100,000 deepfake porn videos are readily available on the internet, with hundreds, if not thousands, being uploaded daily. This staggering statistic prompts a chilling question: what is driving the creation of such a vast number of fakes? Is it merely for amusement, or is there a more sinister motive at play?
Recent Trends and Developments
An investigation by India Today’s Open-Source Intelligence (OSINT) team reveals that deepfake pornography is rapidly morphing into a thriving business. AI enthusiasts, creators, and experts are extending their expertise, investors are injecting money, and even small financial companies to tech giants like Google, VISA, Mastercard, and PayPal are being misused in this dark trade. Synthetic porn has existed for years, but advances in AI and the increasing availability of technology have made it easier—and more profitable—to create and distribute non-consensual sexually explicit material. The 2023 State of Deepfake report by Home Security Heroes reveals a staggering 550% increase in the number of deepfakes compared to 2019.
What’s the Matter with Fakes?
But why should we be concerned about these fakes? The answer lies in the real-world harm they cause. India has already seen cases of extortion carried out by exploiting deepfake technology. An elderly man in UP’s Ghaziabad, for instance, was tricked into paying Rs 74,000 after receiving a deep fake video of a police officer. The situation could have been even more serious if the perpetrators had decided to create deepfake porn of the victim.
The danger is particularly severe for women. The 2023 State of Deepfake Report estimates that at least 98 percent of all deepfakes is porn and 99 percent of its victims are women. A study by Harvard University refrained from using the term “pornography” for creating, sharing, or threatening to create/share sexually explicit images and videos of a person without their consent. “It is abuse and should be understood as such,” it states.
Based on interviews of victims of deepfake porn last year, the study said 63 percent of participants talked about experiences of “sexual deepfake abuse” and reported that their sexual deepfakes had been monetised online. It also found “sexual deepfake abuse to be particularly harmful because of the fluidity and co-occurrence of online offline experiences of abuse, resulting in endless reverberations of abuse in which every aspect of the victim’s life is permanently disrupted”.
Creating deepfake porn is disturbingly easy. There are largely two types of deepfakes: one featuring faces of humans and another featuring computer-generated hyper-realistic faces of non-existing people. The first category is particularly concerning and is created by superimposing faces of real people on existing pornographic images and videos—a task made simple and easy by AI tools.
During the investigation, platforms hosting deepfake porn of stars like Jennifer Lawrence, Emma Stone, Jennifer Aniston, Aishwarya Rai, Rashmika Mandanna to TV actors and influencers like Aanchal Khurana, Ahsaas Channa, and Sonam Bajwa and Anveshi Jain were encountered. It takes a few minutes and as little as Rs 40 for a user to create a high-quality fake porn video of 15 seconds on platforms like FakeApp and FaceSwap.
The Modus Operandi
These platforms brazenly flaunt their business association and hide behind frivolous declarations such as: the content is “meant solely for entertainment” and “not intended to harm or humiliate anyone”. However, the irony of these disclaimers is not lost on anyone, especially when they host thousands of non-consensual deepfake pornography.
As fake porn content and its consumers surge, deepfake porn sites are rushing to forge collaborations with generative AI service providers and have integrated their interfaces for enhanced interoperability. The promise and potential of making quick bucks have given birth to step-by-step guides, video tutorials, and websites that offer tools and programs, recommendations, and ratings.
Nearly 90 per cent of all deepfake porn is hosted by dedicated platforms that charge for long-duration premium fake content and for creating porn—of whoever a user wants, and take requests for celebrities. To encourage them further, they enable creators to monetize their content.
One such website, Civitai, has a system in place that pays “rewards” to creators of AI models that generate “images of real people'', including ordinary people. It also enables users to post AI images, prompts, model data, and LoRA (low-rank adaptation of large language models) files used in generating the images. Model data designed for adult content is gaining great popularity on the platform, and they are not only targeting celebrities. Common people are equally susceptible.
Access to premium fake porn, like any other content, requires payment. But how can a gateway process payment for sexual content that lacks consent? It seems financial institutes and banks are not paying much attention to this legal question. During the investigation, many such websites accepting payments through services like VISA, Mastercard, and Stripe were found.
Those who have failed to register/partner with these fintech giants have found a way out. While some direct users to third-party sites, others use personal PayPal accounts to manually collect money in the personal accounts of their employees/stakeholders, which potentially violates the platform's terms of use that ban the sale of “sexually oriented digital goods or content delivered through a digital medium.”
Among others, the MakeNude.ai web app – which lets users “view any girl without clothing” in “just a single click” – has an interesting method of circumventing restrictions around the sale of non-consensual pornography. The platform has partnered with Ukraine-based Monobank and Dublin’s BetaTransfer Kassa which operates in “high-risk markets”.
BetaTransfer Kassa admits to serving “clients who have already contacted payment aggregators and received a refusal to accept payments, or aggregators stopped payments altogether after the resource was approved or completely freeze your funds”. To make payment processing easy, MakeNude.ai seems to be exploiting the donation ‘jar’ facility of Monobank, which is often used by people to donate money to Ukraine to support it in the war against Russia.
The Indian Scenario
India currently is on its way to design dedicated legislation to address issues arising out of deepfakes. Though existing general laws requiring such platforms to remove offensive content also apply to deepfake porn. However, persecution of the offender and their conviction is extremely difficult for law enforcement agencies as it is a boundaryless crime and sometimes involves several countries in the process.
A victim can register a police complaint under provisions of Section 66E and Section 66D of the IT Act, 2000. Recently enacted Digital Personal Data Protection Act, 2023 aims to protect the digital personal data of users. Recently Union Government issued an advisory to social media intermediaries to identify misinformation and deepfakes. Comprehensive law promised by Union IT minister Ashwini Vaishnav will be able to address these challenges.
Conclusion
In the end, the unsettling dance of AI and human vulnerability continues in the dark web of deepfake pornography. It's a dance that is as disturbing as it is fascinating, a dance that raises questions about the ethical use of technology, the protection of individual rights, and the responsibility of financial institutions. It's a dance that we must all be aware of, for it is a dance that affects us all.
References
- https://www.indiatoday.in/india/story/deepfake-porn-artificial-intelligence-women-fake-photos-2471855-2023-12-04
- https://www.hindustantimes.com/opinion/the-legal-net-to-trap-peddlers-of-deepfakes-101701520933515.html
- https://indianexpress.com/article/opinion/columns/with-deepfakes-getting-better-and-more-alarming-seeing-is-no-longer-believing/

Introduction
The recent advisory issued by CERT, issued on April 26th, 2026, titled “Defending Against Frontier AI-Driven Cyber Risks”, on AI-driven cyber threats does not merely add to the list of routine cybersecurity warnings. Instead, it marks a shift in how cyber risk itself is understood. The concern, here, is not just that attacks are increasing, but also that their nature is changing. Artificial intelligence is no longer assisting cyber operations- whether legitimate or malicious, in fragments; it is beginning to organise and execute them at scale.
What is emerging is a situation where capability is no longer tied to human skill alone. Systems can now identify vulnerabilities, generate exploits, and carry out coordinated attacks with limited intervention. This alters the baseline assumption of cybersecurity, that attacks require effort, time, and expertise.
The Essence: Automation and Capability
At the core of the advisory lies the recognition that AI has introduced speed and autonomy into cyber operations. Tasks such as analysing code, identifying vulnerabilities, or crafting phishing content are no longer sequential processes. They can happen almost simultaneously and at scale.
This is not simply a matter of efficiency. It changes the structure of the threat itself. When attacks can be automated, they become repeatable and less dependent on specialised actors. The advisory also points to the ability of AI systems to conduct multi-stage attacks, moving across networks and adapting strategies in real time.
In a way, the threat is no longer just external. It is embedded within the logics of the technology being used.
Significance: Lower Barriers, Wider Exposure
One of the more important aspects of the advisory is its emphasis on ‘accessibility’. AI lowers the barrier of complexity in the commission of cybercrimes. Activities that once required coordinated teams can now be performed by individuals with access to advanced tools.
This has two consequences. First, the number of potential attackers increases. Second, the scale at which attacks can be carried out expands significantly. Systems that were previously considered low risk may become viable targets simply because automated tools can scan, test, and exploit them rapidly.
There is also a broader anxiety reflected in what is being described as “Mythos concerns”, a shorthand for uncertainty around frontier AI systems and their unpredictable capabilities. This signals that the risk is not fully mapped yet and that regulatory responses are still catching up.
Element of Continuous Risk
The advisory outlines impacts such as unauthorised access, data breaches, identity theft, and financial fraud. These are familiar categories. What is less explicit, but more important, is the shift in how these harms occur.
When AI enables rapid and repeated exploitation, risk becomes continuous. Systems are not attacked once and then secured. They are exposed to ongoing attempts. This creates pressure not only on technical infrastructure but also on legal frameworks that are designed around discrete incidents.
For instance, obligations under the Information Technology Act, 2000 or even emerging data protection frameworks often assume identifiable breaches and reportable events. Continuous probing complicates that model!
Response Framework: From Compliance to Vigilance
CERT-In’s recommendations reflect this change in threat perception. There is a clear emphasis on vigilance rather than mere compliance. Organisations are advised to adopt zero-trust approaches, reduce exposure surfaces, and treat vulnerabilities as immediately exploitable.
The insistence on rapid patching within short timeframes is particularly telling. It acknowledges that the window between vulnerability disclosure and exploitation is shrinking.
There is also a noticeable expansion of responsibility. The advisory does not limit itself to large organisations. It extends guidance to the MSMEs and individuals, recognising that cyber risk is now distributed across the entire digital ecosystem.
A Subtle Legal Shift
Although the advisory itself is not binding in law, it operates within the framework of Section 70B of the Information Technology Act, 2000, which empowers CERT-In to issue directions on cybersecurity best practices and guidelines.
So, while the advisory does not create liability directly, it influences what may later be considered ‘reasonable security practice’. In that sense, it serves as soft law, gradually informing standards of due diligence.
At the same time, there remains a gap. The advisory focuses on defensive measures, but it does not fully address attribution and accountability in AI driven attacks. When actions are automated and anonymised, identifying responsibility and imposing liability becomes more complex.
Conclusion
The CERT In advisory is not just a warning about new threats. It is an acknowledgement of a transition. Cyber risk is moving from being occasional and targeted to being constant and scalable. AI is not simply adding to existing threats; it is restructuring and advancing them.
For cyber vigilance frameworks, this suggests a need to rethink priorities. Static compliance measures are no longer sufficient. It has become necessary to adopt continuous monitoring, adaptive responses, and a clearer understanding of how technology is reshaping risk.
While the advisory does not resolve these questions, it does bring them into focus. And that, in itself, is significant.
References
- CERT-In issues advisory against AI driven cyber attacks for MSMEs, organisations and individuals, Moneycontrol (Apr. 27, 2026), https://www.moneycontrol.com/technology/cert-in-issues-advisory-against-ai-driven-cyber-attacks-for-msmes-organisations-and-individuals-article-13899942.html.
- CERT-In warns of rising AI driven cyber threats amid Mythos concerns, Ommcom News (2026), https://ommcomnews.com/science-tech/cert-in-warns-of-rising-ai-driven-cyber-threats-amid-mythos-concerns/.
- Indian Computer Emergency Response Team (CERT-In), Defending Against Frontier AI Driven Cyber Risks, Advisory No. CIAD-2026-0020 (Apr. 26, 2026)
- Information Technology Act, 2000, § 70B (India).


