Introduction
Iran stands as a nation poised at the threshold of a transformative era. The Islamic Republic, a land of ancient civilisations now grappling with the exigencies of the 21st century, is now making strides in the emerging field of artificial intelligence (AI). This is not merely an adoption of new tools; it is a strategic embrace, a calculated leap into the digital unknown, where the potential for economic growth and security enhancement resonates with the promise of a redefined future.
Embarking on this technological odyssey, Iranian President Ebrahim Raisi, in a conclave with the nation’s virtual business activists, delineated the ‘big steps’ being undertaken in the realm of AI. The gathering, as reported by the pro-government Tasnim News, was not a simple exchange of polite remarks but a profound discourse that offered an incisive overview of the burgeoning digital economy and the strides Iran is making in the AI landscape. The conversation deeply revolved around the current ecosystem of technology and innovation within Iran, delving into the burgeoning startup culture and the commendable drive within its youth populace to propel the nation to the forefront of technology.
Iranian AI Integration
Military Implications
The discourse ranged from the current technological infrastructure to the broader implications for the security and defense of the region. The Iranian polity, with its rich history that seamlessly blends with aspirations for the future, is acutely aware that the implications of AI reach far beyond mere economic growth. They extend into the very fibres of military might and the structure of national security. The investment in cyber capabilities in Iran is well-documented, a display of shrewdness and pragmatism. And the integration of AI technologies is the next logical step in an ever-evolving defense architecture. Brigadier General Alireza Sabahifard, Commander of the Iranian Army Air Defense Force, has underscored the pivotal role of AI in modern warfare. He identifies the ongoing adoption of AI technologies as a strategic imperative, a top priority fundamentally designed to elevate the air defense capabilities in Iran to meet 21st-century threats.
Economic Implications
Yet, the Iranian pursuit of AI is not solely confined to bolstering military prowess. It is also pervasive in nurturing economic opportunity. President Raisi’s rhetoric touches upon economic rejuvenation, job creation, and the proliferation of financial and legal support mechanisms, all blurred into a cohesive vision that would foster a suitable environment for the private sector in the AI domain. The ambition is grand and strikingly clear — a nation committed to training several thousand individuals in the digital economy sector, signaling a deep-rooted commitment to cultivating a healthy environment for AI-driven innovation.
The Iranian leader’s vision extends beyond the simple creation of infrastructure. It extends to the fostering of a healthy, competitive, and peaceful social milieu where domestic and international markets are within easy reach, promoting the prosperity of the digital economy and its activists. Such a vision of technological symbiosis, in many Western democracies, would be labelled as audaciously progressive. In Iran, however, withdrawing a major chunk of economic investments from the country's security state adds layers of complexity and nuance to this transformative narrative.
Cultural Integration
Still, Iran’s ambitious AI journey unfolds with a recognition of its cultural underpinnings and societal structure. The Nexus between the private sector, with its cyber-technocratic visionaries, and the regime, with its omnipresent ties to the Islamic Revolutionary Guard Corps, is a tightrope that requires unparalleled poise and vigilance.
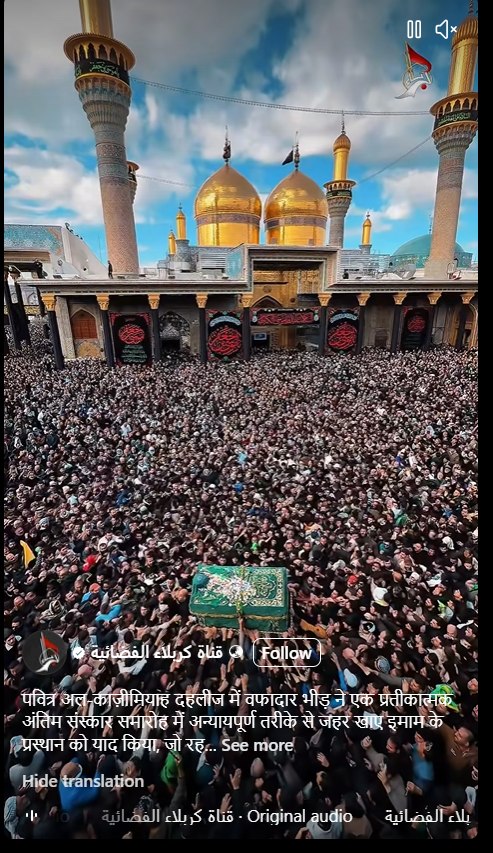
Moreover, in the holy city of Qom, a hub of intellectual fervour and the domicile of half of Iran's 200,000 Shia clerics, there burgeons a captivating interest in the possible synergies between AI and theological study. The clerical establishment, hidden within a stronghold of religious scholarship, perceives AI not as a problem but as a potential solution, a harbinger of progress that could ally with tradition. It sees in AI the potential of parsing Islamic texts with newfound precision, thereby allowing religious rulings, or fatwas, to resonate with the everchanging Iranian society. This integration of technology is a testament to the dynamic interplay between tradition and modernity.
Yet the integration of AI into the venerable traditions of societies such as Iran's is threaded with challenges. Herein lays the paradox, for as AI is poised to potentially bolster religious study, the threat of cultural dissolution remains present. AI, if not judiciously designed with local values and ethics in mind, could inadvertently propagate an ideology at odds with local customs, beliefs, and the cornerstone principles of a society.
Natural Resources
Similarly, Iran's strategic foray into AI extends into its sovereign dominion—the charge of its natural resources. As Mehr News Agency reports, the National Iranian Oil Company (NIOC) is on the cusp of pioneering a joint venture with international tech juggernauts, chiefly Chinese companies, to inject the lifeblood of AI into the heart of its oil and gas production processes. This grand undertaking is nothing short of a digital renaissance aimed at achieving 'great reforms’ and driving a drastic 20% improvement in efficiency. AI’s algorithmic potency, unleashed in the hydrocarbon fields, promises to streamline expenses, enhance efficacy, and maximise production outputs, thereby bolstering Iran's economic bulwark.
The AI way Forward
As we delve further into Iran's sophisticated AI strategy, we observe an approach that is both vibrant and multi-dimensional. From military development to religious tutelage, from the diligent charge of the environment to the pursuit of sustainable economic development, Iran's AI ventures are emblematic of the broader global discourse. They mark a vivid intersection of AI governance, security, and the future of technological enterprise, highlighting the evolution of technological adoption and its societal, ethical, and geopolitical repercussions.
Conclusion
The multifaceted nature of Iran's AI pursuits encapsulates a spectrum of strategic imperatives, bringing the spearheads of defense modernisation and religious academics with the imperatives of resource allocation. It reflects a nuanced approach to the adoption and integration of technology, adjudicating between the venerable pillars of traditional values and the inexorable forces of modernisation. As Iran continues to delineate and traverse its path through the burgeoning landscape of AI, attending global stakeholders, watch with renewed interest and measured apprehension. Mindful of the intricate geopolitical implications and the transformative potential inherent in Iran's burgeoning AI endeavours, the global community watches, waits, and wonders at what may emerge from this ancient civilisation’s bold, resolute strides into the future.
References
- https://www.fdd.org/analysis/op_eds/2024/03/17/irans-president-wants-new-focus-on-artificial-intelligence/
- https://www.jpost.com/middle-east/article-792391
- https://www.ft.com/content/9c1c3fd3-4aea-40ab-977b-24fe5527300c
- https://www.foxnews.com/world/iran-looks-ai-weather-western-sanctions-help-military-fight-cheap