#FactCheck: AI-Generated Footage Fuels False Claim of Strike on Al Udeid Air Base
Executive Summary
The ongoing conflict between the US-Israel and Iran has entered its third week. During this period, Iran reportedly targeted the US military base at Al Udeid in Qatar. Amid this, a video is going viral on social media showing people, vehicles, and chaos following an alleged attack. Some users are sharing it as footage of an Iranian missile strike on the Al Udeid Air Base. However, an research by the CyberPeacefound that the viral video is not real but AI-generated.
Claim:
An Instagram user “thenewscartel” shared the video on March 17, 2026, with the caption: “Al Udeid Air Base, Qatar (March 16, 2026): Iran launched ballistic missiles and drones at the US military’s largest Middle East base near Doha as retaliation for US-Israel strikes in Tehran. Qatar’s Defense Ministry confirmed multiple launches. Most were intercepted by Qatari air defense. One missile landed near the base or in an uninhabited area. No casualties or major damage reported. Explosions were heard in Doha, and smoke was seen in the sky.”

Fact Check:
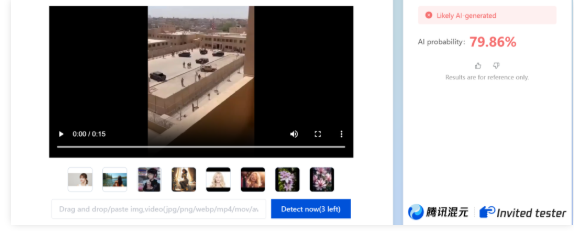
To verify the claim, we closely examined the viral video. We observed multiple visual inconsistencies—one person appears to be walking in reverse, another disappears and reappears, and the body shapes of people distort as they begin to run. These anomalies strongly indicate AI manipulation. We then analyzed the video using the AI detection tool Zhuque AI, which indicated an approximately 80 percent likelihood that the video is AI-generated.
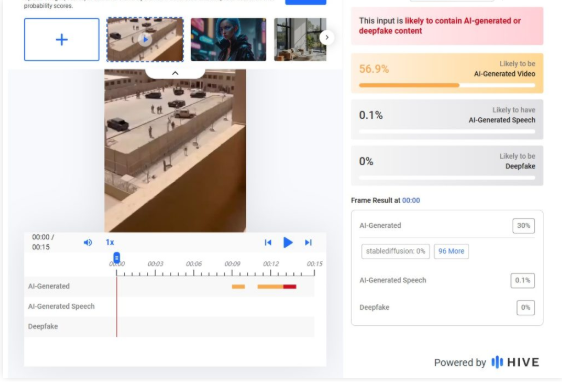
Further analysis using Hive Moderation showed around a 57 percent probability of the video being AI-generated.
Conclusion:
Our research found that the viral video being shared as footage of an Iranian attack on the US military base at Al Udeid in Qatar is AI-generated and not related to any real incident.
Related Blogs

Executive Summary
A graphic featuring Union Home Minister Amit Shah is being widely shared on social media, claiming that he has announced a complete ban on alcohol in West Bengal from September 30. The post further suggests that the state will move towards becoming a dry state. Notably, this claim surfaced soon after the BJP’s victory in the West Bengal Assembly elections. CyberPeace Research Wing research has found the viral claim to be false. Our research confirms that Home Minister Amit Shah has not made any such announcement.
Claim:
On Instagram, a user shared a viral graphic on May 8, 2026, alleging that Amit Shah announced a complete ban on alcohol in West Bengal starting September 30. The post link and archived version are provided below:
- https://www.instagram.com/reel/DYDy13zINV5/
- https://archive.ph/mYpZS

Fact Check
To verify the claim, we conducted a keyword-based search on Google. However, we did not find any credible media reports supporting the viral claim. Since the graphic carried the logo of India Today, we also checked the official website, YouTube channel, and social media handles of India Today. However, no matching report or graphic was found.
In the final step, we reviewed the official X account of the Ministry of Home Affairs. Even there, no statement or report confirming the viral claim was found. The relevant link is provided below:
- https://x.com/HMOIndia

Conclusion:
Our research confirms that Home Minister Amit Shah has made no such announcement regarding a complete alcohol ban in West Bengal.

Executive Summary:
A manipulated image showing someone making an offensive gesture towards Prime Minister Narendra Modi is circulating on social media. However, the original photo does not display any such behavior towards the Prime Minister. The CyberPeace Research Team conducted an analysis and found that the genuine image was published in a Hindustan Times article in May 2019, where no rude gesture was visible. A comparison of the viral and authentic images clearly shows the manipulation. Moreover, The Hitavada also published the same image in 2019. Further investigation revealed that ABPLive also had the image.

Claims:
A picture showing an individual making a derogatory gesture towards Prime Minister Narendra Modi is being widely shared across social media platforms.



Fact Check:
Upon receiving the news, we immediately ran a reverse search of the image and found an article by Hindustan Times, where a similar photo was posted but there was no sign of such obscene gestures shown towards PM Modi.

ABP Live and The Hitavada also have the same image published on their website in May 2019.


Comparing both the viral photo and the photo found on official news websites, we found that almost everything resembles each other except the derogatory sign claimed in the viral image.

With this, we have found that someone took the original image, published in May 2019, and edited it with a disrespectful hand gesture, and which has recently gone viral across social media and has no connection with reality.
Conclusion:
In conclusion, a manipulated picture circulating online showing someone making a rude gesture towards Prime Minister Narendra Modi has been debunked by the Cyberpeace Research team. The viral image is just an edited version of the original image published in 2019. This demonstrates the need for all social media users to check/ verify the information and facts before sharing, to prevent the spread of fake content. Hence the viral image is fake and Misleading.
- Claim: A picture shows someone making a rude gesture towards Prime Minister Narendra Modi
- Claimed on: X, Instagram
- Fact Check: Fake & Misleading

Introduction
Over the last few years, several public data breaches in Venezuela have revealed a lack of cohesion and progress in its data privacy system and left many people susceptible to fraud, identity theft and long-term harm via the internet. It is clear from these data breaches that when organizations fail to adequately protect their data, both through cybersecurity failures and weak legal protections, they can lead to problems throughout an entire system through which all individuals in the system could potentially suffer.
Among the more notable breaches are the Movistar Venezuela data breach from 2025 and the Cashea App data leak from earlier this year. Each of these examples demonstrates to some extent how the absence of an adequate privacy regulatory scheme can worsen the results of a data breach.
The Movistar Breach: A Regulatory Warning (2025)
Venezuelan digital rights group VE Sin Filtro published a report late in April 2025, which found a database revealed to have been opened onto the internet containing personal information belonging to over 3.2 million Movistar customers. The initial breach contained personal, and confidential, data of Venezuelan citizens such as national identification numbers, full names, city of residence, and phone numbers which could have been exploited to commit identity theft, SIM-swap fraud, and targeted scams.
One significant issue with this situation was that Movistar failed to disclose the breach publicly or contact impacted customers at the time of the disclosure. As a result, there appears to be a significant gap in Sanctions / Other Means of Enforcing Security Countermeasures Laws. Since there are numerous countries that enforce GDPR-style regulations and as such, this matter should lead to a complete investigation and possible fines against those responsible but in Venezuela there is still a lack of accountability.
Cashea App Leak: A 2026 Data Shock
A second alleged data breach came to light in February of 2026. It involved a Venezuelan buy-now-pay-later (BNPL) fintech called Cashea App, which is typically heavily utilized domestically. Reports have circulated that threat actors have been offering a database, believed to hold more than 79 million transaction records. This is more than double the size and sensitivity of the data involved in the Movistar Breach.
According to reports, the leaked data included:
- Bank account details and payment methods
- Merchant profiles and internal business identifiers
- Detailed transaction histories with names, national ID numbers, timestamps, and installment data
This level of exposure goes far beyond basic identifiers. Financial transaction histories combined with personal identifiers enable sophisticated fraud, targeted social engineering, and long-term misuse of financial identities. As with the Movistar breach, no official acknowledgment or notification was issued by Cashea at the time of reporting, again underscoring Venezuela’s weak enforcement environment.
Why These Breaches Matter: The Legal Dimension
The incidents show us that there is a bigger problem with the way Venezuela has set up its framework for protecting data. For instance, the Venezuelan Constitution recognises the principles of data protection and privacy; however, these rights only exist in a theoretical manner; they lack implementing legislation, procedural clarity, and institutional enforcement.
Constitutional Basis of Data Protection
The Supreme Tribunal of Justice (TSJ) stated the core principles for protecting data are found in the Venezuelan Constitution. After the TSJ issued its 2011 ruling, Article 28 of the Venezuelan Constitution gives individuals the right to know what data the state has about them, how the state uses that data, and to correct or delete any harmful data. Article 60 of the Venezuelan Constitution protects individuals' privacy and restricts excessive data collection by the state.
The Constitutional Chamber also put into place additional guiding principles for how to protect personal data, including:
- The data subject must give prior informed and revocable consent.
- The purpose for which the data is collected must be specified and only the minimum amount of information necessary can be collected.
- The data collected must be accurate and of good quality.
- There are confidentiality obligations for third parties regarding the use of the data.
- It is the government's responsibility to put into place procedures and mechanisms to monitor compliance with the data protection laws.
- There are civil, criminal and administrative liabilities for individuals and legal entities that violate the data protection laws.
But, in a civil law country, when courts make rulings, they usually are persuasive only as opposed to being legally binding, and even constitutional rulings cannot be implemented until enabling legislation is passed.
Absence of a Comprehensive Data Protection Law
In contrast to the European Union's GDPR (General Data Protection Regulation), the United States' sectoral approach, and emerging Latin American data protection systems such as the ones in Brazil, Chile and Colombia, Venezuela has no independent data protection law. This lack of law leads to numerous types of uncertainty in the realm of data protection laws:
- No defined data controller or processor obligations
- No standardized lawful bases for processing
- No clear breach notification timelines
- No independent data protection authority
- No procedural pathway for individuals to seek redress
As a result, data protection in Venezuela is not treated as an independent legal discipline but instead becomes derivative, arising incidentally within constitutional litigation or sector-specific disputes.
Regulatory Fragmentation and Institutional Weakness
Due to the TSJ decisions made in 2011, there has been a lack of regulatory action taken in a systematic fashion and instead most actions have been done on a case by case basis as valid incidents arise. The National Cybersecurity Council was established in 2024; however, its function is to support the establishment of cybersecurity infrastructure and has no defined powers regarding the enforcement of privacy.
This creates a fragmented institutional landscape where:
- Authorities lack clear jurisdiction over privacy violations
- Companies face minimal compliance guidance
- Individuals struggle to understand or enforce their rights
The Movistar and Cashea incidents highlight how this fragmentation translates into practical impunity following major data exposures.
What’s Next? A Legal Opportunity for Reform
The repercussions of insufficient safeguards for data protection extend past the damage incurred to a person's privacy:
- Loss of trust in both financial and digital services
- Heightened likelihood of financial fraud and crime
- Lack of willingness from foreign companies to conduct business with Venezuela’s platforms.
- Long-term negative impact on the reputation of domestic companies.
- Possible inability to access cross-border transfer of data due to other jurisdictions’ decisions to restrict transfers into jurisdictions without cutting-edge enforcement of protections for privacy.
In a digital economy that increasingly requires robust data protection to function successfully, a lack of action to create strong protections will cause a significant economic impact.
Conclusion
Major data breaches such as the ones at Movistar in 2025 and Cashea App in 2026 show that constitutional privacy rights alone are insufficient without enforceable legal framework. Privacy laws must move from being just a principle to being a law that has institutions, procedures, and accountability to make sure the privacy of the users is protected.
Now with the global digital economy being so interconnected, not having regulations creates openings for vulnerabilities for people. If Venezuela hopes to protect their citizens, create an innovation-friendly environment, and compete in the global market, they must implement comprehensive data privacy reforms as soon as possible.
REFERENCES
- https://iapp.org/news/a/venezuela-data-breach-highlights-scattered-privacy-regulation
- https://www.apolocybersecurity.com/en/blog-posts/ciberataque-a-movistar-que-ha-pasado-a-quien-afecta-y-como-proteger-tus-datos
- https://darknetsearch.com/knowledge/news/en/cashea-app-data-leak-79m-records-exposed-in-venezuela/
- https://www.binance.com/en-IN/square/post/294369884695410


