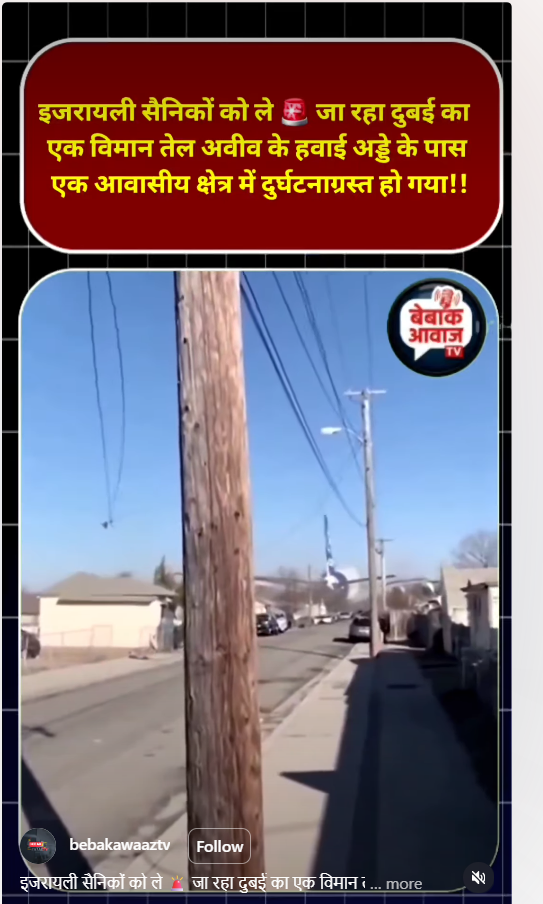
#FactCheck- AI Video Fuels False Claims of Israeli Soldiers’ Death in Plane Crash
Executive Summary
A video circulating on social media is being linked to the ongoing tensions in West Asia involving the United States, Israel, and Iran. The clip shows an aircraft crashing into a residential area, with users claiming that a Dubai-bound plane carrying Israeli soldiers crashed near Tel Aviv airport, killing everyone on board. However, an research by the CyberPeace has found the claim to be false. The viral video is AI-generated, and no such incident has taken place in Israel.
Claim
An Instagram user “bebakawaaztv” shared the video on April 7, 2026, claiming that a Dubai aircraft carrying Israeli soldiers crashed near Tel Aviv airport in a residential area, allegedly after being hit by debris from an Iranian hypersonic missile.
Fact Check
To verify the claim, we closely examined the viral video. Several visual inconsistencies indicated that it was not real. The aircraft appears to be flying unusually low over a residential area—something that is highly improbable under normal aviation conditions. Its landing gear seems to touch rooftops without causing any visible damage. Additionally, the wings of the aircraft pass through structures like poles without any collision impact, which is physically impossible. These anomalies strongly suggested that the video was artificially created.
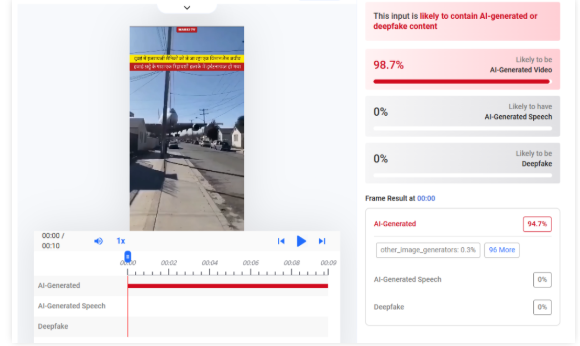
We further analyzed the video using the AI detection tool HIVE Moderation, which indicated a 99% probability that the content is AI-generated.
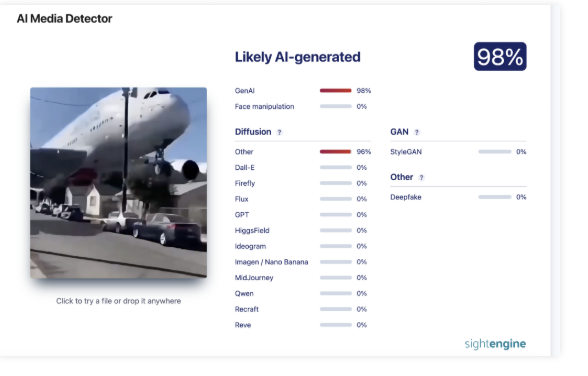
Another analysis using Sightengine also flagged the video as likely AI-generated.
Conclusion
The viral claim is false and misleading. There is no credible evidence or verified report confirming that any Dubai aircraft carrying Israeli soldiers crashed near Tel Aviv airport. No such incident has been reported by any reliable international or local media outlets. The video in question is digitally fabricated using AI technology, and the visual inconsistencies within the clip clearly indicate manipulation. Such content is often designed to exploit ongoing geopolitical tensions and spread misinformation at scale
Related Blogs

Executive Summary:
In the age of virtuality, misinformation and misleading techniques shape the macula of the internet, and these threaten human safety and well-being. Recently, an alarming fake information has surfaced, intended to provide a fake Government subsidy scheme with the name of Indian Post. This serves criminals, who attack people's weaknesses, laying them off with proposals of receiving help in exchange for info. In this informative blog, we take a deep dive into one of the common schemes of fraud during this time. We will go through the stages involved which illustrates how one is deceived and offer practical tips to avoid the fall.
Introduction:
Digital communication reaches individuals faster, and as a result, misinformation and mails have accelerated their spread globally. People, therefore, are susceptible to online scams as they add credibility to phenomena. In India, the recently increased fake news draws its target with the deceptive claims of being a subsidy from the Government mainly through the Indian post. These fraudulent schemes frequently are spread via social networks and messaging platforms, influence trust of the individual’s in respectable establishments to establish fraud and collect private data.
Understanding the Claim:
There is a claim circulating on the behalf of the Government at the national level of a great subsidy of $1066 for deserving residents. The individual will be benefited with the subsidy when they complete the questionnaire they have received through social media. The questionnaire may have been designed to steal the individual’s confidential information by way of taking advantage of naivety and carelessness.
The Deceptive Journey Unveiled:
Bogus Offer Presentation: The scheme often appeals to people, by providing a misleading message or a commercial purposely targeted at convincing them to act immediately by instilling the sense of an urgent need. Such messages usually combine the mood of persuasion and highly evaluative material to create an illusion of being authentic.
Questionnaire Requirement: After the visitors land on attractive content material they are directed to fill in the questionnaire which is supposedly required for processing the economic assistance. This questionnaire requests for non private information in their nature.
False Sense of Urgency: Simultaneously, in addition to the stress-causing factor of it being a fake news, even the false deadline may be brought out to push in the technique of compliance. This data collection is intended to put people under pressure and influence them to make the information transfer that immediate without thorough examination.
Data Harvesting Tactics: Despite the financial help actually serving, you might be unaware but lies beneath it is a vile motive, data harvesting. The collection of facts through questionnaires may become something priceless for scammers that they can use for a good while to profit from identity theft, financial crimes and other malicious means.
Analysis Highlights:
- It is important to note that at this particular point, there has not been any official declaration or a proper confirmation of an offer made by the India Post or from the Government. So, people must be very careful when encountering such messages because they are often employed as lures in phishing attacks or misinformation campaigns. Before engaging or transmitting such claims, it is always advisable to authenticate the information from trustworthy sources in order to protect oneself online and prevent the spread of wrongful information
- The campaign is hosted on a third party domain instead of any official Government Website, this raised suspicion. Also the domain has been registered in very recent times.

- Domain Name: ccn-web[.]buzz
- Registry Domain ID: D6073D14AF8D9418BBB6ADE18009D6866-GDREG
- Registrar WHOIS Server: whois[.]namesilo[.]com
- Registrar URL: www[.]namesilo[.]com
- Updated Date: 2024-02-27T06:17:21Z
- Creation Date: 2024-02-11T03:23:08Z
- Registry Expiry Date: 2025-02-11T03:23:08Z
- Registrar: NameSilo, LLC
- Name Server: tegan[.]ns[.]cloudflare[.]com
- Name Server: nikon[.]ns[.]cloudflare[.]com
Note: Cybercriminal used Cloudflare technology to mask the actual IP address of the fraudulent website.
CyberPeace Advisory:
Verification and Vigilance: It makes complete sense in this case that you should be cautious and skeptical. Do not fall prey to this criminal act. Examine the arguments made and the facts provided by either party and consult credible sources before disclosures are made.
Official Channels: Governments usually invoke the use of reliable channels which can as well be by disseminating subsidies and assistance programs through official websites and the legal channels. Take caution for schemes that are not following the protocols previously established.
Educational Awareness: Providing awareness through education and consciousness about on-line scams and the approaches which are fraudulent has to be considered a primary requirement. Through empowering individuals with capabilities and targets we, as a collective, can be armed with information that will prevent erroneous scheme spreading.
Reporting and Action: In a case of mission suspicious and fraudulent images, let them understand immediately by making the authorities and necessary organizations alert. Your swift actions do not only protect yourself but also help others avoid the costs of related security compromises.
Conclusion:
The rise of the ‘Indian Post Countrywide - government subsidy fake news’ poses a stern warning of the present time that the dangers within the virtual ecosystem are. The art of being wise and sharp in terms of scams always reminds us to show a quick reaction to the hacks and try to do the things that we should identify as per the CyberPeace advisories; thereby, we will contribute to a safer Cyberspace for everyone. Likewise, the ability to critically judge, and remain alert, is important to help defeat the variety of tricks offenders use to mislead you online.

Executive Summary:
A photoshopped image circulating online suggests Prime Minister Narendra Modi met with militant leader Hafiz Saeed. The actual photograph features PM Modi greeting former Pakistani Prime Minister Nawaz Sharif during a surprise diplomatic stopover in Lahore on December 25, 2015.
The Claim:
A widely shared image on social media purportedly shows PM Modi meeting Hafiz Saeed, a declared terrorist. The claim implies Modi is hostile towards India or aligned with terrorists.

Fact Check:
On our research and reverse image search we found that the Press Information Bureau (PIB) had tweeted about the visit on 25 December 2015, noting that PM Narendra Modi was warmly welcomed by then-Pakistani PM Nawaz Sharif in Lahore. The tweet included several images from various angles of the original meeting between Modi and Sharif. On the same day, PM Modi also posted a tweet stating he had spoken with Nawaz Sharif and extended birthday wishes. Additionally, no credible reports of any meeting between Modi and Hafiz Saeed, further validating that the viral image is digitally altered.


In our further research we found an identical photo, with former Pakistan Prime Minister Nawaz Sharif in place of Hafiz Saeed. This post was shared by Hindustan Times on X on 26 December 2015, pointing to the possibility that the viral image has been manipulated.
Conclusion:
The viral image claiming to show PM Modi with Hafiz Saeed is digitally manipulated. A reverse image search and official posts from the PIB and PM Modi confirm the original photo was taken during Modi’s visit to Lahore in December 2015, where he met Nawaz Sharif. No credible source supports any meeting between Modi and Hafiz Saeed, clearly proving the image is fake.
- Claim: Debunking the Edited Image Claim of PM Modi with Hafiz Saeed
- Claimed On: Social Media
- Fact Check: False and Misleading
Introduction
Cyberwarfare has evolved into one of the most decisive instruments of statecraft and conflict. The increasing digitisation of critical infrastructure like power grids, water systems, transportation systems, healthcare networks, and energy sources has made these systems new targets in the war of algorithms. Military logic is evolving to paralyse the nation’s critical infrastructure to keep its resources engaged in repairing them and thereby break the nation’s ability to deter and counter attacks, all without firing a single bullet.
From Ransomware to an Invisible Sabotage: The changing nature of warfare
The operational technology (OT) landscape has become the epicentre of cyber operations, all around the world. Once, which was insulated, related to industrial systems that controlled turbines, pipelines, or dams, they now stand connected to the Internet through supervisory control and data acquisition (SCADA) and the Internet of Things. These connections have also become gateways for attackers, besides enhancing the efficiency of the infrastructural lifelines of the nation.
Groups like Volt Typhoon, Sandworm, Laurionite, and Cyberavengers have transformed the art of digital infiltration into a strategic shift. Volt Typhoon, which is linked to China, has used “living-off-the-land” techniques to exploit the legitimate administrative tools to remain invisible while scanning the critical infrastructures in the US. Sandworm, which is aligned with Russia’s GRU (Glavnoye Razvedyvatelnoye Upravlenie) or Main Intelligence Directorate (in English), has demonstrated the power of cyber sabotage in real time, as its attacks on Ukraine’s power grids in 2015 and 2021 had left millions in darkness, coinciding with kinetic missile strikes. Meanwhile, the Iranian-affiliated Cyberavengers group, which has weaponised the AI-assisted malware, such as IOCONTROL, that are capable of hijacking water and energy control systems. Each of these systems used in these operations reflects a shift from direct espionage activities to a state of strategic paralysis.
In comparison to the traditional cybercrime activities that are aimed at stealing data and extortion of money, these campaigns repeatedly target the physical systems, which consist of the machinery that sustains civilian life and military preparedness.
The Military Logic behind Cyber Targeting: A Web of Vulnerabilities
A critical infrastructure is a complex ecosystem that covers power generation, transportation, communication, and manufacturing are all interconnected, which means a single compromised node can cascade into a national paralysis. For instance, a breach in the systems of the dam can flood an entire city, a grid shutdown can halt water supply to hospitals, and even affect air traffic. The 2015 Black Energy Malware attack in Ukraine has proved this possibility when three utilities were hacked, plunging thousands of homes into darkness. The Iranian hackers once again gained access to the Bowman Avenue Dam of New York and controlled its floodgates, which gave a chilling demonstration of the destructive reality of digital manipulation.
The systems remain vulnerable mainly for 3 reasons such as-
- Legacy Architectures: Many of these industrial systems were designed decades ago with no built-in cybersecurity mechanisms.
- Slow Patching and Segmentation Gaps: All updates and segmentation between IT and TO networks often lag, providing open entry points for attackers.
- Converging with IoT: The integration of smart sensors and cloud-based management tools has expanded the attack surface exponentially.
This interconnected fragility has turned our critical infrastructures into both a weapon and a target or a tool for coercion in modern hybrid warfare. Between 2023 and 2024, over 420 cyberattacks were witnessed in several critical global infrastructures, which averaged to 13 attacks per second, according to a news report. These were not just random acts of digital vandalism; they were deliberate and coordinated operational attempts by state-led actors from China, Russia, and Iran.
Developing a new Resilience as the new tool of Deterrence
Cyber deterrence no longer rests on the fear of retaliation, it relies on the need for resilience. Nations that can absorb attacks, maintain continuity, and recover rapidly would be the true superpowers of this digital age. Segmentation, real-time threat detection, and AI-assisted recovery models are vital pillars of this model of resilience. The logic of modern cyberwarfare is clear, which means that the more a nation digitizes, the more it will need to defend itself.
However, as the line between war and peace blurs, safeguarding critical infrastructure is no longer just an IT priority; rather, it is a national security doctrine. In this silent theatre of cyberwarfare, survival will depend not only on firepower, but on firewalls.
References
- https://rmcglobal.com/critical-infrastructure-under-siege-the-top-ot-threats-of-2025/
- https://ccdcoe.org/uploads/2018/10/Geers2009_The-Cyber-Threat-to-National-Critical-Infrastructures.pdf
- https://www.researchgate.net/publication/335752979_Cybersecurity_of_Critical_Infrastructure
- https://arxiv.org/html/2510.04118v1
- https://www.anapaya.net/blog/top-5-critical-infrastructure-cyberattacks


