#FactCheck- AI-Generated Video Falsely Linked to Iranian Attack on Amazon Data Center in Bahrain
Executive Summary
A video showing a damaged building allegedly belonging to Amazon is going viral on social media. The clip is being shared with the claim that it depicts the aftermath of an Iranian missile strike on an Amazon data center in Bahrain on April 1, 2026. However, research by CyberPeace has found the claim to be misleading. While reports confirm that Iran targeted a U.S.-linked cloud infrastructure in Bahrain, the viral video itself is not real footage and has been created using artificial intelligence.
Claim
A Facebook user, “Tripti Speaks,” shared the viral video on April 2, 2026, with the caption:“Iranian attack on Amazon’s cloud computing data center in Bahrain. IRGC fired missiles at Batelco in Bahrain where AWS infrastructure is located, damaging servers and disrupting services.”
- Archived link::https://perma.cc/XH7S-QTX6

Fact Check
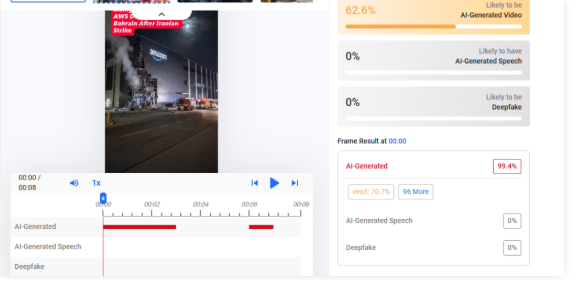
To verify the claim, we extracted multiple keyframes from the viral video and conducted a reverse image search using Google. However, we did not find any credible sources or reports featuring this specific footage. This raised suspicion about the authenticity of the video. We then analyzed it using the AI detection tool Hive Moderation, which indicated a 63% probability that the video is AI-generated.
According to a report published by Reuters on April 1, 2026, Iran launched a missile attack targeting Amazon’s cloud computing operations in Bahrain. The Islamic Revolutionary Guard Corps (IRGC) had earlier warned that U.S.-linked companies in the Middle East—including Microsoft, Google, and Apple—could be targeted.

Conclusion
Our research found that while there are credible reports confirming an Iranian attack on cloud infrastructure linked to Amazon in Bahrain, the viral video circulating on social media does not depict the real incident. The footage shows no presence in verified news coverage and has been flagged by AI detection tools as likely artificial. Therefore, the video is AI-generated and misleadingly linked to the incident.
Related Blogs

Cyber attacks in India besides becoming common are also getting deadlier. Each strike has taken proportions to drive home the fact that no one is safe.
Hacker ‘John Wick’, hasn’t spared India’s PM or Paytm. Cyber intelligence firm Cyble which dredges the Dark Web has red-flagged hacking episodes at Truecaller, Dunzo, Unacademy, Naukri.com, Bharat Earth Movers Limited (BEML), LimeRoad and IndiaBulls.Picture this, Mumbai-based cybersecurity firm Sequretek, says in Covid-hit 2020, India has seen a 4000% spike in phishing emails and a 400% uptake in the number of policy violations that have grown over 400% as per the latest statistics.Besides the threat to crucial data, the cost suffered by companies is phenomenal. According to a report by IBM’s ‘Cost of a Data Breach Report 2020’ report, Indian companies witnessed an average $2 Mn total cost of data breach in 2020, this is an increase of 9.4% from 2019.
Another survey by Barracuda Networks revealed that 66% of Indian organisations have had at least one data breach or cybersecurity incident since shifting to a remote working model during the pandemic.
Indian Startups At Mercy Of Cyber Attacks
More recently personal data of 2.8 Lakh WhiteHat Jr students and teachers were exposed, where crucial details of minors have been made available on the dark web. Another major breach that took place this week and exclusively reported by Inc42 was when data of 1.4 Mn job seekers was leaked when jobs portal IIMjobs was hacked.
Vineet Kumar, the founder of Cyber Peace Foundation (CPF), a think tank of cybersecurity and policy experts, said that with the increased digitisation of companies and their processes, data has become the new oil.
“You get good money when you sell users data on the dark web. Hackers discovering vulnerabilities and using SQL injections to pull entire databases remains a common practice for hacking,” Kumar told Inc42.
The CyberPeace Foundation says from mid-April to the end of June it noticed 8,98,7841 attacks, July and August saw 64,52,898 attacks. Whereas September and October saw 1,37,37,516 attacks and 18,149,233 attacks respectively.
Speaking to Inc42, Pankit Desai, cofounder and CEO, Sequretek says, “Originally only a limited set of systems were being exposed, now with WFH all systems have to be exposed to the internet as all your processes are enabled remotely. WFH also creates an additional challenge where ‘personal assets are being used for professional purposes’ and ‘professional assets are being used for personal purposes.”
Malwares like SpyMax, Blackwater are being used as a combination of phishing mails and poorly secured home computers to harvest credentials. These credentials are then used for carrying out attacks. The number of attacks with harvested credentials is already up 30%, the company revealed.
Government data shows that in 2019 alone, India witnessed 3.94 lakh instances of cybersecurity breaches. In terms of hacking of state and central government websites, Indian Computer Emergency Response Team (CERT-In) data shows that a total of 336 websites belonging to central ministries, departments, and state governments were hacked between 2017 and 2019.
According to Nasscom’s Data Security Council of India (DSCI) report 2019, India witnessed the second-highest number of cyber attacks in the world between 2016 and 2018. This comes at a time when digitisation of the Indian economy is predicted to result in a $435 Bn opportunity by 2025.On September 22, the Ministry of Electronics and Information Technology (MeITY) told the Parliament that Indian citizens, commercial and legal entities faced almost 7 lakh cyberattacks till August this year.
The Indian Computer Emergency Response Team (CERT-In) has “reported 49,455, 50,362, 53,117, 208,456, 394,499 and 696,938 cybersecurity incidents during the year 2015, 2016, 2017, 2018, 2019 and 2020 (till August) respectively,” the MeITY said while responding to an unstarred question in the Lok Sabha regarding cyberattacks on Indian citizens and India-based commercial and legal entities.“
India also lacks a cohesive nation-wide cyber-strategy, policies, and procedures. Regulations around data privacy, protection, and penalty should be enacted and enforced as these measures will help businesses evaluate their cybersecurity posture and seek ways to improve. Currently, incident reporting is not mandatory. By making it compulsory, there will be a body of research data that can provide insights on threats to India and inform the government on strategies it can undertake to strengthen the nation’s cyber posture,” said Kumar Ritesh, founder and CEO, Cyfirma.The Internet Crime Report for 2019, released by the USA’s Internet Crime Complaint Centre of the Federal Bureau of Investigation (FBI), has revealed that India stands third in the world among top 20 countries that are victims of internet crimes.
Kumar attributes these numbers to Indian’s lack of basic cyber awareness. However, a poignant point is also the lack of a robust cybersecurity policy in India. Though the issue was touched upon by Prime Minister Narendra Modi during his Independence Day speech on Aug 15, 2020, not much movement has happened on that front.
“Cybersecurity is a very important aspect, which cannot be ignored. The government is alert on this and is working on a new, robust policy,” Modi said.The PM’s announcement was made in the backdrop of the government’s initiative to connect 1.5 lakh gram panchayats through an optical fiber network, thereby increasing the country’s internet connectivity.
With India pipped to take on the world with its IT prowess and increased digital integration the need for a robust policy is now more than ever.
Source: https://inc42.com/buzz/3-94-lakhs-and-counting-how-cyberattacks-are-a-worry-for-digital-india/

A video circulating widely on social media claims that Indian cricketer Virat Kohli made a sarcastic remark about fast bowler Prasidh Krishna ahead of the New Zealand series. In the clip, Kohli is allegedly heard saying that he expected to be the top scorer of the series, but lost all hope after seeing Prasidh Krishna’s name in the squad.
Users sharing the video claim that Kohli publicly commented on Prasidh Krishna in this manner.
Research by the CyberPeace Foundation has found the viral claim to be false. Our probe revealed that the viral clip has been digitally manipulated. The video is originally from a 2024 advertisement featuring Virat Kohli, in which his voice has been altered using deepfake (AI-generated) technology and falsely presented with a misleading narrative.
Claim
The video was shared on Instagram on January 6, 2025, with users claiming that Kohli made the remark after the New Zealand squad was announced. The post included the altered audio suggesting Kohli’s disappointment over Prasidh Krishna’s selection. Link, archive link

Fact Check:
To verify the claim, we extracted key frames from the viral video and conducted a Google Reverse Image Search. This led us to the original video posted by Virat Kohli himself on X (formerly Twitter) on April 15, 2024. The original clip was part of a brand advertisement, and no such statement about the New Zealand series or Prasidh Krishna was made in it. Link and Screenshot

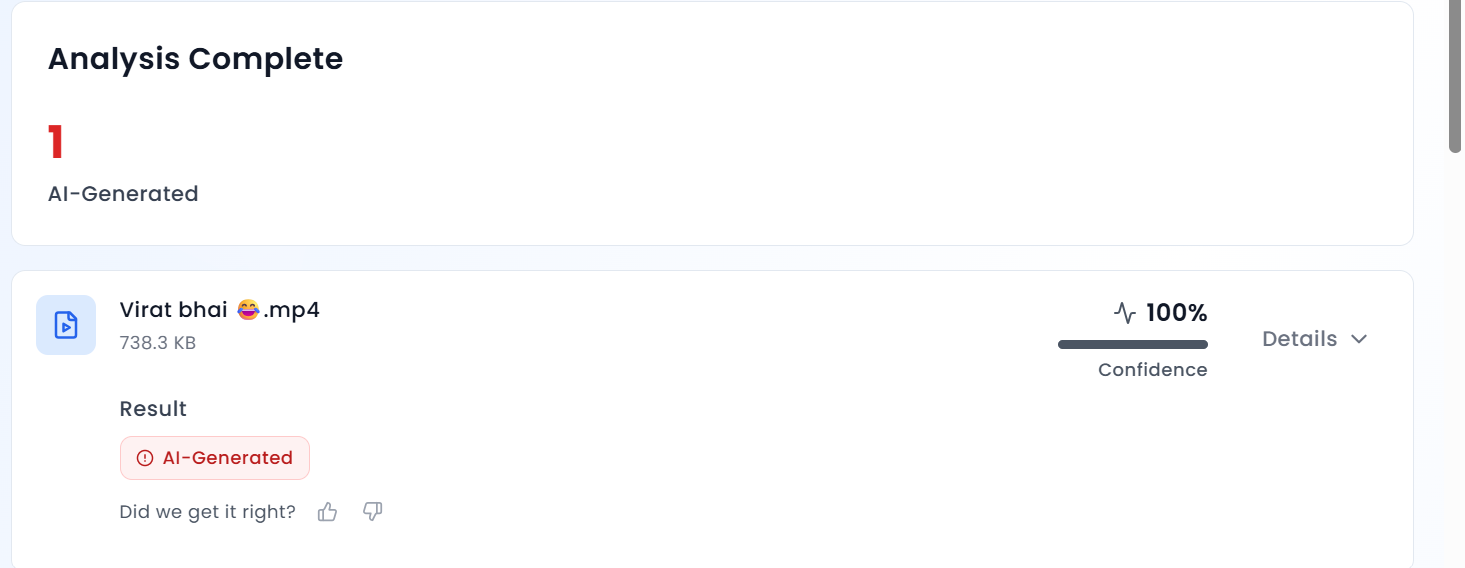
A close review of the viral clip raised suspicions due to the unnatural tone and inconsistencies in Kohli’s voice. To confirm this, we analysed the video using the AI detection tool Aurigin AI. The tool’s results showed that the audio in the viral clip is 100 percent AI-generated, confirming that Kohli’s voice was artificially manipulated.
Conclusion
The CyberPeace Foundation’s research confirms that the viral video claiming Virat Kohli mocked Prasidh Krishna is fake and misleading. The clip is taken from an old advertisement and has been doctored using deepfake technology to alter Kohli’s voice. The video is being circulated on social media with a false claim, and Virat Kohli has made no such statement regarding the New Zealand series or Prasidh Krishna.

Executive Summary:
One of the most complex threats that have appeared in the space of network security is focused on the packet rate attacks that tend to challenge traditional approaches to DDoS threats’ involvement. In this year, the British based biggest Internet cloud provider of Europe, OVHcloud was attacked by a record and unprecedented DDoS attack reaching the rate of 840 million packets per second. Targets over 1 Tbps have been observed more regularly starting from 2023, and becoming nearly a daily occurrence in 2024. The maximum attack on May 25, 2024, got to 2.5 Tbps, this points to a direction to even larger and more complex attacks of up to 5 Tbps. Many of these attacks target critical equipment such as Mikrotik models within the core network environment; detection and subsequent containment of these threats prove a test for cloud security measures.
Modus Operandi of a Packet Rate Attack:
A type of cyberattack where an attacker sends with a large volume of packets in a short period of time aimed at a network device is known as packet rate attack, or packet flood attack or network flood attack under volumetric DDoS attack. As opposed to the deliberately narrow bandwidth attacks, these raids target the computation time linked with package processing.
Key technical characteristics include:
- Packet Size: Usually compact, and in many cases is less than 100 bytes
- Protocol: Named UDP, although it can also involve TCP SYN or other protocol flood attacks
- Rate: Exceeding 100 million packets per second (Mpps), with recent attacks exceeding 840 Mpps
- Source IP Diversity: Usually originating from a small number of sources and with a large number of requests per IP, which testifies about the usage of amplification principles
- Attack on the Network Stack : To understand the impact, let's examine how these attacks affect different layers of the network stack:
1. Layer 3 (Network Layer):
- Each packet requires routing table lookups and hence routers and L3 switches have the problem of high CPU usage.
- These mechanisms can often be saturated so that network communication will be negatively impacted by the attacker.
2. Layer 4 (Transport Layer):
- Other stateful devices (e.g. firewalls, load balancers) have problems with tables of connections
- TCP SYN floods can also utilize all connection slots so that no incoming genuine connection can be made.
3. Layer 7 (Application Layer):
- Web servers and application firewalls may be triggered to deliver a better response in a large number of requests
- Session management systems can become saturated, and hence, the performance of future iterations will be a little lower than expected in terms of their perceived quality by the end-user.
Technical Analysis of Attack Vectors
Recent studies have identified several key vectors exploited in high-volume packet rate attacks:
1.MikroTik RouterOS Exploitation:
- Vulnerability: CVE-2023-4967
- Impact: Allows remote attackers to generate massive packet floods
- Technical detail: Exploits a flaw in the FastTrack implementation
2.DNS Amplification:
- Amplification factor: Up to 54x
- Technique: Exploits open DNS resolvers to generate large responses to small queries
- Challenge: Difficult to distinguish from legitimate DNS traffic
3.NTP Reflection:
- Command: monlist
- Amplification factor: Up to 556.9x
- Mitigation: Requires NTP server updates and network-level filtering
Mitigation Strategies: A Technical Perspective
1. Combating packet rate attacks requires a multi-layered approach:
- Hardware-based Mitigation:
- Implementation: FPGA-based packet processing
- Advantage: Can handle millions of packets per second with minimal latency
- Challenge: High cost and specialized programming requirements
2.Anycast Network Distribution:
- Technique: Distributing traffic across multiple global nodes
- Benefit: Dilutes attack traffic, preventing single-point failures
- Consideration: Requires careful BGP routing configuration
3.Stateless Packet Filtering:
- Method: Applying filtering rules without maintaining connection state
- Advantage: Lower computational overhead compared to stateful inspection
- Trade-off: Less granular control over traffic
4.Machine Learning-based Detection:
- Approach: Using ML models to identify attack patterns in real-time
- Key metrics: Packet size distribution, inter-arrival times, protocol anomalies
- Challenge: Requires continuous model training to adapt to new attack patterns
Performance Metrics and Benchmarking
When evaluating DDoS mitigation solutions for packet rate attacks, consider these key performance indicators:
- Flows per second (fps) or packet per second (pps) capability
- Dispersion and the latency that comes with it is inherent to mitigation systems.
- The false positive rate in the case of the attack detection
- Exposure time before beginning of mitigation from the moment of attack
Way Forward
The packet rate attacks are constantly evolving where the credible defenses have not stayed the same. The next step entails extension to edge computing and 5G networks for distributing mitigation closer to the attack origins. Further, AI-based proactive tools of analysis for prediction of such threats will help to strengthen the protection of critical infrastructure against them in advance.
In order to stay one step ahead in this, it is necessary to constantly conduct research, advance new technologies, and work together with other cybersecurity professionals. There is always a need to develop secure defenses that safeguard these networks.
Reference:
https://blog.ovhcloud.com/the-rise-of-packet-rate-attacks-when-core-routers-turn-evil/
https://cybersecuritynews.com/record-breaking-ddos-attack-840-mpps/
https://www.cloudflare.com/learning/ddos/famous-ddos-attacks/


