#FactCheck - Viral Video of Man ‘Running on Water’ Found to Be AI-Generated
Executive Summary:
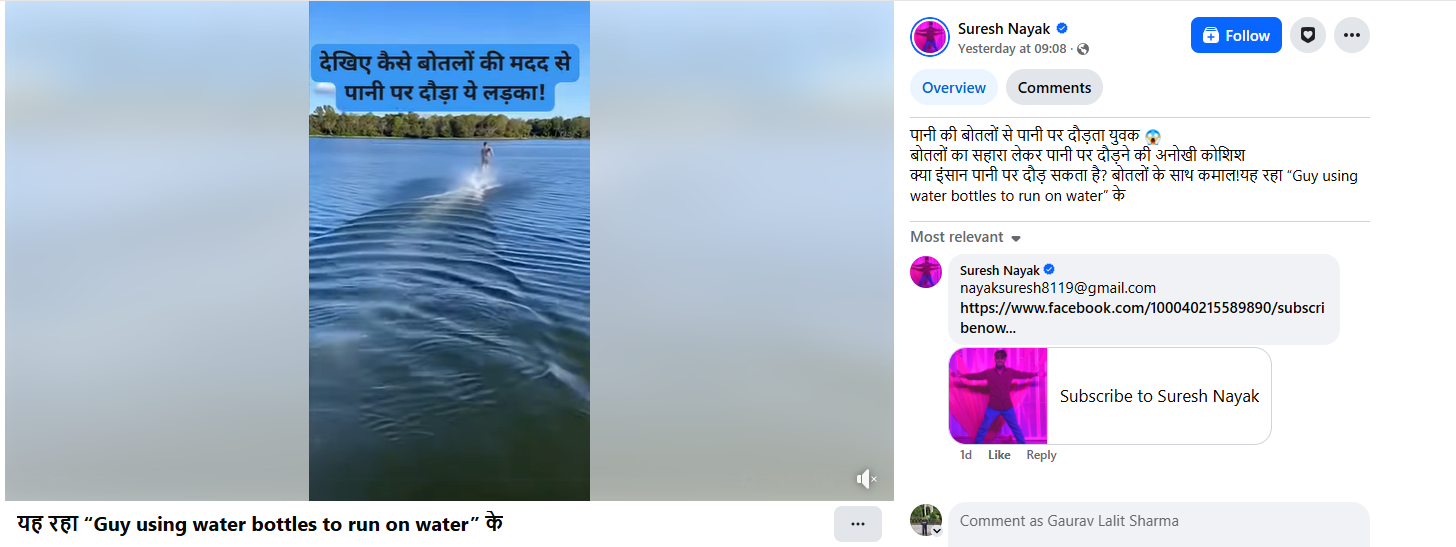
A video is being shared on social media showing a man running rapidly in a river with water bottles tied to both his feet. Users are circulating the video claiming that the man is attempting to run on water using the support of the bottles. CyberPeace’s research found the viral claim to be false. Our research revealed that the video being shared on social media is not real but has been generated using artificial intelligence (AI).
Claim :
The claim was shared by a Facebook user on February 5, 2026, who wrote that a man was running on water using water bottles tied to his feet, calling it a unique attempt and questioning whether humans can run on water. Links to the post, its archived version, and screenshots are provided below.
Fact Check:
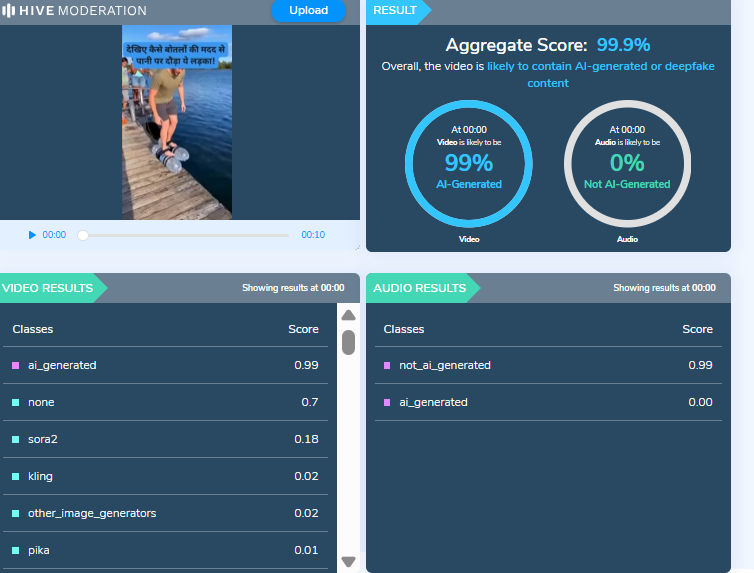
To verify the claim, we searched relevant keywords on Google but did not find any credible media reports supporting the incident. A closer examination of the viral video revealed several visual irregularities, raising suspicion that it may have been AI-generated. The video was then scanned using the AI detection tool Hive Moderation. According to the tool’s results, the video is 99 percent likely to be AI-generated.
Conclusion:
Our research confirms that the viral video does not depict a real incident and has been falsely shared as a genuine attempt to run on water.
Related Blogs

Introduction
Given the era of digital trust and technological innovation, the age of artificial intelligence has provided a new dimension to how people communicate and how they create and consume content. However, like all borrowed powers, the misuse of AI can lead to terrible consequences. One recent dark example was a cybercrime in Brazil: a sophisticated online scam using deepfake technology to impersonate celebrities of global stature, including supermodel Gisele Bündchen, in misleading Instagram ads. Luring in millions of reais in revenue, this crime clearly brings forth the concern of AI-generative content having rightfully set on the side of criminals.
Scam in Motion
Lately, the federal police of Brazil have stated that this scheme has been in circulation since 2024, when the ads were already being touted as apparently very genuine, using AI-generated video and images. The ads showed Gisele Bündchen and other celebrities endorsing skincare products, promotional giveaways, or time-limited discounts. The victims were tricked into making petty payments, mostly under 100 reais (about $19) for these fake products or were lured into paying "shipping costs" for prizes that never actually arrived.
The criminals leveraged their approach by scaling it up and focusing on minor losses accumulated from every victim, thus christening it "statistical immunity" by investigators. Victims being pocketed only a couple of dollars made most of them stay on their heels in terms of filing a complaint, thereby allowing these crooks extra limbs to shove on. Over time, authorities estimated that the group had gathered over 20 million reais ($3.9 million) in this elaborate con.
The scam was detected when a victim came forth with the information that an Instagram advertisement portraying a deepfake video of Gisele Bündchen was indeed false. With Anna looking to be Gisele and on the recommendation of a skincare company, the deepfake video was the most well-produced fake video. On going further into the matter, it became apparent that the investigations uncovered a whole network of deceptive social media pages, payment gateways, and laundering channels spread over five states in Brazil.
The Role of AI and Deepfakes in Modern Fraud
It is one of the first few large-scale cases in Brazil where AI-generated deepfakes have been used to perpetrate financial fraud. Deepfake technology, aided by machine learning algorithms, can realistically mimic human appearance and speech and has become increasingly accessible and sophisticated. Whereas before a level of expertise and computer resources were needed, one now only requires an online tool or app.
With criminals gaining a psychological advantage through deepfakes, the audiences would be more willing to accept the ad as being genuine as they saw a familiar and trusted face, a celebrity known for integrity and success. The human brain is wired to trust certain visual cues, making deepfakes an exploitation of this cognitive bias. Unlike phishing emails brimming with spelling and grammatical errors, deepfake videos are immersive, emotional, and visually convincing.
This is the growing terrain: AI-enabled misinformation. From financial scams to political propaganda, manipulated media is killing trust in the digital ecosystem.
Legalities and Platform Accountability
The Brazilian government had taken a proactive stance on the issue. In June 2025, the country's Supreme Court held that social media platforms could be held liable for failure to expeditiously remove criminal content, even in the absence of a formal order from a court. The icing on the cake is that that judgment would go a long way in architecting platform accountability in Brazil and potentially worldwide as jurisdictions adopt processes to deal with AI-generated fraud.
Meta, the parent company of Instagram, had said its policies forbid "ads that deceptively use public figures to scam people." Meta claims to use advanced detection mechanisms, trained review teams, and user tools to report violations. The persistence of such scams shows that the enforcement mechanisms still lag the pace and scale of AI-based deception.
Why These Scams Succeed
There are many reasons for the success of these AI-powered scams.
- Trust Due to Familiarity: Human beings tend to believe anything put forth by a known individual.
- Micro-Fraud: Keeping the money laundered from victims small prevents any increase in the number of complaints about these crimes.
- Speed To Create Content: New ads are being generated by criminals faster than ads can be checked for and removed by platforms via AI tools.
- Cross-Platform Propagation: A deepfake ad is then reshared onto various other social networking platforms once it starts gaining some traction, thereby worsening the problem.
- Absence of Public Awareness: Most users still cannot discern manipulated media, especially when high-quality deepfakes come into play.
Wider Implications on Cybersecurity and Society
The Brazilian case is but a microcosm of a much bigger problem. With deepfake technology evolving, AI-generated deception threatens not only individuals but also institutions, markets, and democratic systems. From investment scams and fake charters to synthetic IDs for corporate fraud, the possibilities for abuse are endless.
Moreover, with generative AIs being adopted by cybercriminals, law enforcement faces obstructions to properly attributing, validating evidence, and conducting digital forensics. Determining what is actual and what is manipulated has now given rise to the need for a forensic AI model that has triggered the deployment of the opposite on the other side, the attacker, thus initiating a rising tech arms race between the two parties.
Protecting Citizens from AI-Powered Scams
Public awareness has remained the best defence for people in such scams. Gisele Bündchen's squad encouraged members of the public to verify any advertisement through official brand or celebrity channels before engaging with said advertisements. Consumers need to be wary of offers that appear "too good to be true" and double-check the URL for authenticity before sharing any kind of personal information
Individually though, just a few acts go so far in lessening some of the risk factors:
- Verify an advertisement's origin before clicking or sharing it
- Never share any monetary or sensitive personal information through an unverifiable link
- Enable two-factor authentication on all your social accounts
- Periodically check transaction history for any unusual activity
- Report any deepfake or fraudulent advertisement immediately to the platform or cybercrime authorities
Collaboration will be the way ahead for governments and technology companies. Investing in AI-based detection systems, cooperating on international law enforcement, and building capacity for digital literacy programs will enable us to stem this rising tide of synthetic media scams.
Conclusion
The deepfake case in Brazil with Gisele Bündchen acts as a clarion for citizens and legislators alike. This shows the evolution of cybercrime that profited off the very AI technologies that were once hailed for innovation and creativity. In this new digital frontier that society is now embracing, authenticity stands closer to manipulation, disappearing faster with each dawn.
While keeping public safety will certainly still require great cybersecurity measures in this new environment, it will demand equal contributions on vigilance, awareness, and ethical responsibility. Deepfakes are not only a technology problem but a societal one-crossing into global cooperation, media literacy, and accountability at every level throughout the entire digital ecosystem.

Overview:
It is worth stating that millions of Windows users around the world are facing the Blue Screen of Death (BSOD) problem that makes systems shutdown or restart. This has been attributed to a CrowdStrike update that was released recently and has impacted many organizations, financial institutions, and government agencies across the globe. Indian airlines have also reported disruptions on X (formerly Twitter), informing passengers about the issue.
Understanding Blue Screen of Death:
Blue Screen errors, also known as black screen errors or STOP code errors, can occur due to critical issues forcing Windows to shut down or restart. You may encounter messages like "Windows has been shut down to prevent damage to your computer." These errors can be caused by hardware or software problems.
Impact on Industries
Some of the large U. S. airlines such as American Airlines, Delta Airlines, and United Airlines had to issue ground stops because of communication problems. Also, several airports on Friday suffered a massive technical issue in check-in kiosks for IndiGo, Akasa Air, SpiceJet, and Air India Express.
The Widespread Issue
The issue seems widespread and is causing disruption across the board as Windows PCs are deployed at workplaces and other public entities like airlines, banks, and even media companies. It has been pointed out that Windows PCs use a special cybersecurity solution from a company called CrowdStrike that seems to be the culprit for this outage, affecting most Windows PC users out there.
Microsoft's Response
The issue was acknowledged by Microsoft and the mitigations are underway. The company in its verified X handle Microsoft 365 status has shared a series information on the latest outage and they are looking into the matter. The issue is under investigation.
In one of the posts from Microsoft Azure, it is mentioned that they have become aware of an issue affecting Virtual Machines (VMs) running Windows Client and Windows Server with the CrowdStrike Falcon agent installed. These VMs may encounter a bug check (BSOD) and become stuck in a restarting state. Their analysis indicates that this issue started approximately at 19:00 UTC on July 18th. They have provided recommendations as follows:
Restore from Backup: In case customers have available backups prior to 19:00 UTC on July 18th, they should recover VM data from the backups. If the customer is using Azure Backup, they can get exact steps on how to restore VM data in the Azure portal. here.
Offline OS Disk Repair: Alternatively, customers can attempt offline repair of the OS disk by attaching an unmanaged disk to the affected VM. Encrypted disks may require additional steps to unlock before repair. Once attached, delete the following file:
Windows/System/System32/Drivers/CrowdStrike/C00000291*.sys
After deletion, reattach the disk to the original VM.
Microsoft Azure is actively investigating additional mitigation options for affected customers. We will provide updates as we gather more information.
Resolving Blue Screen Errors in Windows
Windows 11 & Windows 10:
Blue Screen errors can stem from both hardware and software issues. If new hardware was added before the error, try removing it and restarting your PC. If restarting is difficult, start your PC in Safe Mode.
To Start in Safe Mode:
From Settings:
Open Settings > Update & Security > Recovery.
Under "Advanced startup," select Restart now.
After your PC restarts to the Choose an option screen, select Troubleshoot > Advanced options > Startup Settings > Restart.
After your PC restarts, you'll see a list of options. Select 4 or press F4 to start in Safe Mode. If you need to use the internet, select 5 or press F5 for Safe Mode with Networking.
From the Sign-in Screen:
Restart your PC. When you get to the sign-in screen, hold the Shift key down while you select Power > Restart.
After your PC restarts, follow the steps above.
From a Black or Blank Screen:
Press the power button to turn off your device, then turn it back on. Repeat this two more times.
After the third time, your device will start in the Windows Recovery Environment (WinRE).
From the Choose an option screen, follow the steps to enter Safe Mode.
Additional Help:
Windows Update: Ensure your system has the latest patches.
Blue Screen Troubleshooter: In Windows, open Get Help, type Troubleshoot BSOD error, and follow the guided walkthrough.
Online Troubleshooting: Visit Microsoft's support page and follow the recommendations under "Recommended Help."
If none of those steps help to resolve your Blue Screen error, please try the Blue Screen Troubleshooter in the Get Help app:
- In Windows, open Get Help.
- In the Get Help app, type Troubleshoot BSOD error.
- Follow the guided walkthrough in the Get Help app.
[Note: If you're not on a Windows device, you can run the Blue Screen Troubleshooter on your browser by going to Contact Microsoft Support and typing Troubleshoot BSOD error. Then follow the guided walkthrough under "Recommended Help."]
For detailed steps and further assistance, please refer to the Microsoft support portal or contact their support team.
CrowdStrike’s Response:
In the statement given by CrowdStrike, they have clearly mentioned it is not any cyberattack and their resources are working to fix the issue on Windows. Further, they have identified the deployment issue and fixed the same. Crowdstrike mentions about their problematic versions as follows:
- “Channel file "C-00000291*.sys" with timestamp of 0527 UTC or later is the reverted (good) version.
- Channel file "C-00000291*.sys" with timestamp of 0409 UTC is the problematic version.
Note: It is normal for multiple "C-00000291*.sys files to be present in the CrowdStrike directory - as long as one of the files in the folder has a timestamp of 0527 UTC or later, that will be the active content.”
The CrowdStrike will be providing latest updates on the same and advises their customers and organizations to contact their officials officially to get latest updates and accurate information. It is encouraged to refer to customer’s support portal for further help.
Stay safe and ensure regular backups to mitigate the impact of such issues.
References:
https://status.cloud.microsoft/
https://www.crowdstrike.com/blog/statement-on-falcon-content-update-for-windows-hosts/

Introduction
The development of high-speed broadband internet in the 90s triggered a growth in online gaming, particularly in East Asian countries like South Korea and China. This culminated in the proliferation of competitive video game genres, which had otherwise existed mostly in the form of high-score and face-to-face competitions at arcades. The online competitive gaming market has only become bigger over the years, with a separate domain for professional competition, called esports. This industry is projected to reach US$4.3 billion by 2029, driven by advancements in gaming technology, increased viewership, multi-million dollar tournaments, professional leagues, sponsorships, and advertising revenues. However, the industry is still in its infancy and struggles with fairness and integrity issues. It can draw lessons in regulation from the traditional sports market to address these challenges for uniform global growth.
The Growth of Esports
The appeal of online gaming lies in its design innovations, social connectivity, and accessibility. Its rising popularity has culminated in online gaming competitions becoming an industry, formally organised into leagues and tournaments with reward prizes reaching up to millions of dollars. Professional teams now have coaches, analysts and psychologists supporting their players. For scale, the 2024 ESports World Cup (EWS) held in Saudi Arabia had the largest combined prize pool of over US$60 million. Such tournaments can be viewed in arenas and streamed online, and by 2025, around 322.7 million people are forecast to be occasional viewers of esports events.
According to Statista, esports revenue is expected to demonstrate an annual growth rate (CAGR 2024-2029) of 6.59%, resulting in a projected market volume of US$5.9 billion by 2029. Esports has even been recognised in traditional sporting events, debuting as a medal sport in the Asian Games 2022. In 2024, the International Olympic Committee (IOC) announced the Olympic Esports Games, with the inaugural event set to take place in 2025 in Saudi Arabia. Hosting esports events such as the EWS is expected to boost tourism and the host country’s local economy.
The Challenges of Esports Regulation
While the esports ecosystem provides numerous opportunities for growth and partnerships, its under-regulation presents challenges. Due to the lack of a single governing body like the IOC for the Olympics or FIFA for football to lay down centralised rules, the industry faces certain challenges, such as :
- Integrity issues: Esports are not immune to cheating attempts. Match-fixing, using advanced software hacks, doping (e.g., Adderall use), and the use of other illegal aids are common. DOTA, Counter-Strike, and Overwatch tournaments are particularly susceptible to cheating scandals.
- Players’ Rights: The teams that contractually own professional players provide remuneration and exercise significant control over athletes, who face issues like overwork, a short-lived career, stress, the absence of collective bargaining forums, instability, etc.
- Fragmented National Regulations: While multiple countries have recognised esports as a sport, policies on esports governance and allied regulation vary within and across borders. For example, age restrictions and laws on gambling, taxation, labour, and advertising differ by country. This can create confusion, risks and extra costs, impacting the growth of the ecosystem.
- Cybersecurity Concerns: The esports industry carries substantial prize pools and has growing viewer engagement, which makes it increasingly vulnerable to Distributed Denial of Service (DDoS) attacks, malware, ransomware, data breaches, phishing, and account hijacking. Tournament organisers must prioritise investments in secure network infrastructure, perform regular security audits, encrypt sensitive data, implement network monitoring, utilise API penetration testing tools, deploy intrusion detection systems, and establish comprehensive incident response and mitigation plans.
Proposals for Esports Regulation: Lessons from Traditional Sports
To address the most urgent challenges to the esports industry as outlined above, the following interventions, drawing on the governance and regulatory frameworks of traditional sports, can be made:
- Need for a Centralised Esports Governing Body: Unlike traditional sports, the esports landscape lacks a Global Sports Organisation (GSO) to oversee its governance. Instead, it is handled de facto by game publishers with industry interests different from those of traditional GSOs. Publishers’ primary source of revenue is not esports, which means they can adopt policies unsuitable for its growth but good for their core business. Appointing a centralised governing body with the power to balance the interests of multiple stakeholders and manage issues like unregulated gambling, athlete health, and integrity challenges is a logical next step for this industry.
- Gambling/Betting Regulations: While national laws on gambling/betting vary, GSOs establish uniform codes of conduct that bind participants contractually, ensuring consistent ethical standards across jurisdictions. Similar rules in esports are managed by individual publishers/ tournament organisers, leading to inconsistencies and legal grey areas. The esports ecosystem needs standardised regulation to preserve fair play codes and competitive integrity.
- Anti-Doping Policies: There is increasing adderall abuse among young players to enhance performance with the rising monetary stakes in esports. The industry must establish a global framework similar to the World Anti-Doping Code, which, in conjunction with eight international standards, harmonises anti-doping policies across all traditional sports and countries in the world. The esports industry should either adopt this or develop its own policy to curb stimulant abuse.
- Norms for Participant Health: Professional players start around age 16 or 17 and tend to retire around 24. They may be subjected to rigorous practice hours and stringent contracts by the teams that own them. There is a need for international norm-setting by a federation overseeing the protection of underage players. Enforcement of these norms can be one of the responsibilities of a decentralised system comprising country and state-level bodies. This also ensures fair play governance.
- Respect and Diversity: While esports is technologically accessible, it still has room for better representation of diverse gender identities, age groups, abilities, races, ethnicities, religions, and sexual orientations. Embracing greater diversity and inclusivity would benefit the industry's growth and enhance its potential to foster social connectivity through healthy competition.
Conclusion
The development of the world’s first esports island in Abu Dhabi gives impetus to the rapidly growing esports industry with millions of fans across the globe. To sustain this momentum, stakeholders must collaborate to build a strong governance framework that protects players, supports fans, and strengthens the ecosystem. By learning from traditional sports, esports can establish centralised governance, enforce standardised anti-doping measures, safeguard athlete rights, and promote inclusivity, especially for young and diverse communities. Embracing regulation and inclusivity will not only enhance esports' credibility but also position it as a powerful platform for unity, creativity, and social connection in the digital age.
Resources
- https://www.statista.com/outlook/amo/esports/worldwide
- https://www.statista.com/statistics/490480/global-esports-audience-size-viewer-type/
- https://asoworld.com/blog/global-esports-market-report-2024/#:~:text=A%20key%20driver%20of%20this%20growth%20is%20the%20Sponsorship%20%26%20Advertising,US%24288.9%20million%20in%202024.
- https://lawschoolpolicyreview.com/2023/12/28/a-case-for-recognising-professional-esports-players-as-employees-of-their-game-publisher/
- https://levelblue.com/blogs/security-essentials/the-hidden-risks-of-esports-cybersecurity-on-the-virtual-battlefield
- https://medium.com/@heyimJoost/esports-governance-and-its-failures-9ac7b3ec37ea
- https://www.google.com/search?q=adderall+abuse+in+esports&oq=adderall+abuse+in+esports&gs_lcrp=EgZjaHJvbWUyBggAEEUYOTIHCAEQIRiPAjIHCAIQIRiPAtIBCDU2MDdqMGo5qAIAsAIB&sourceid=chrome&ie=UTF-8
- https://americanaddictioncenters.org/blog/esports-adderall-abuse#:~:text=A%202020%20piece%20by%20the,it%20because%20everyone%20was%20using


