#FactCheck - Video Showing Sadhus in Ice Is Artificially Generated
Executive Summary
A video showing a group of Hindu ascetics (sadhus) allegedly performing intense penance while their bodies appear to be covered in ice is being widely shared on social media. Users are circulating the video as real and claiming that it represents an ancient tradition of Sanatan Dharma. CyberPeace research found the viral claim to be false.The research revealed that the video circulating on social media is not real but has been generated using artificial intelligence (AI).
Claim
On social media platform Facebook, a user shared the viral video on January 16, 2026. The video shows several ascetics engaged in penance, with their bodies seemingly covered in ice. Users shared the video while claiming that it depicts an authentic spiritual practice rooted in Sanatan Dharma.
Links to the post, archive link, and screenshots can be seen below.

Fact Check:
To verify the authenticity of the viral claim, CyberPeace searched relevant keywords on Google. However, no credible or reliable media reports supporting the claim were found. A close examination of the viral video raised suspicion that it may have been AI-generated. To verify this, the video was analysed using the AI detection tool Hive Moderation. According to the results, the video was found to be 99 percent AI-generated.
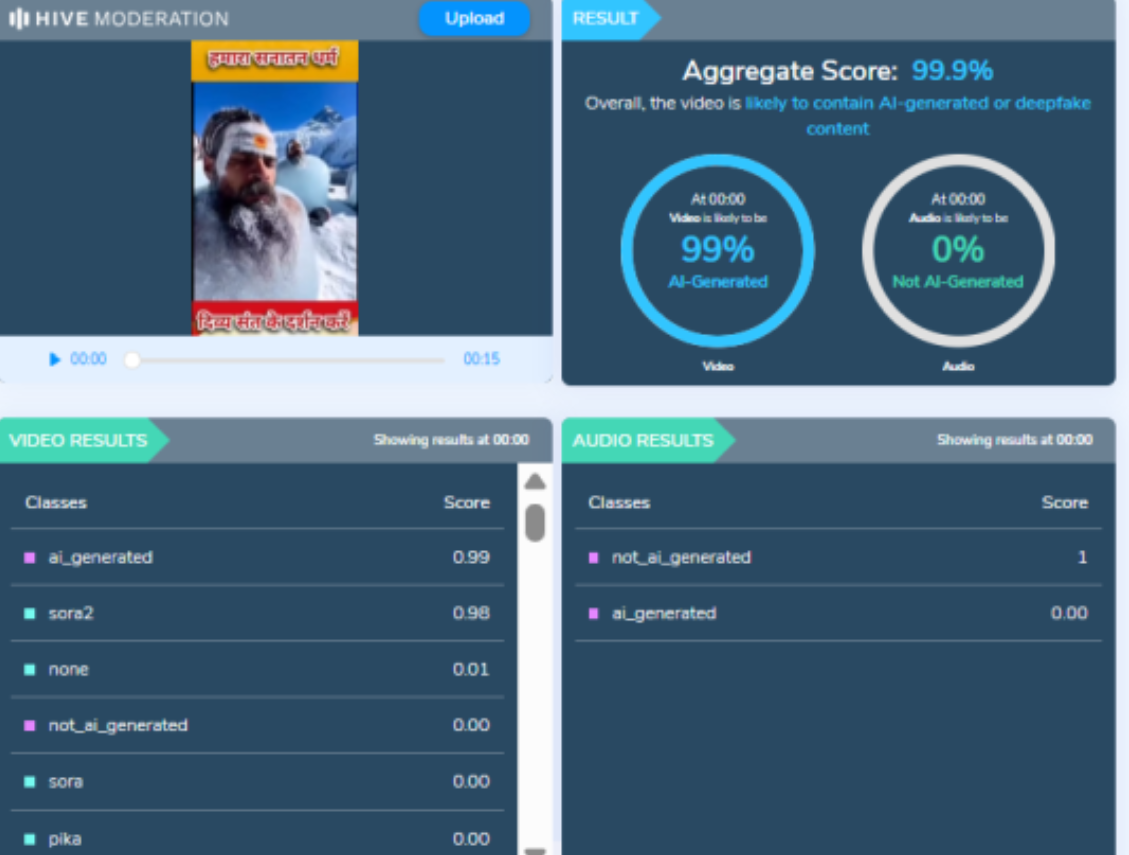
In the next step of the research, the same video was analysed using another AI detection tool, Sightengine. The results again indicated that the video was 99 percent AI-generated.
Conclusion
CyberPeace concludes that the video circulating on social media is not real. The viral video showing ascetics covered in ice was generated using artificial intelligence and does not depict an actual religious or spiritual practice.
Related Blogs

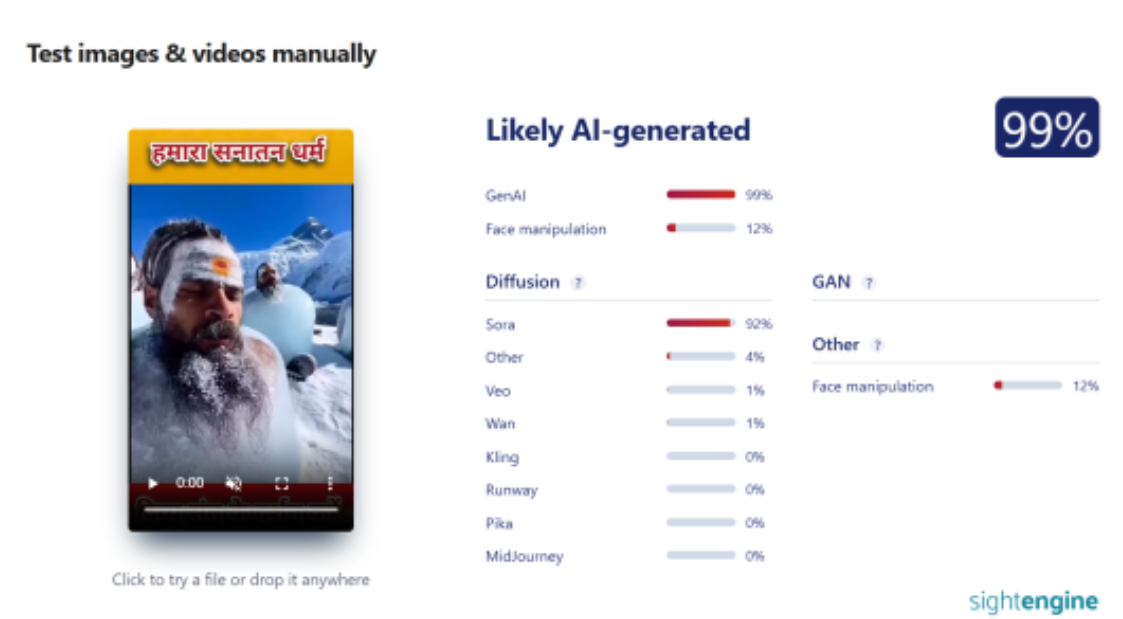
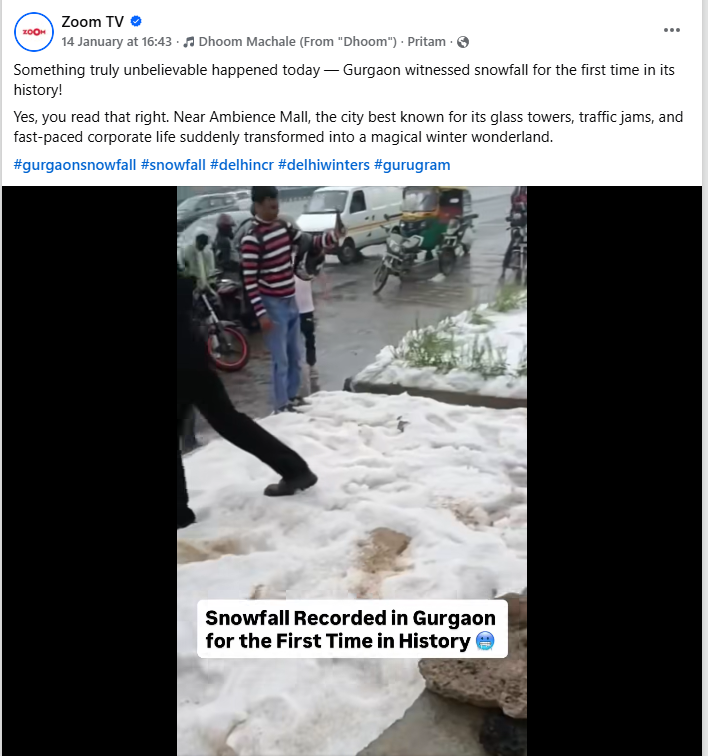
A video circulating widely on social media claims to show snowfall near Ambience Mall in Gurugram, Haryana. The clip is being shared alongside assertions that Gurugram witnessed snowfall for the first time in its history amid a severe cold wave in January 2026. However, an research by Cyber Peace Foundation has found the claim to be misleading. Our verification reveals that the viral video is not recent and has been available online since March 2023.
The Claim
On 14 January 2026, a Facebook user shared the video with the caption,“Something truly unbelievable happened today — Gurgaon witnessed snowfall for the first time in its history!”Through this post, the user implied that the visuals showed snowfall near Ambience Mall during the ongoing cold wave.link and screeshot
- https://www.instagram.com/reel/DTfS9X9DyBo/?utm_source=ig_embed&ig_rid=239ddaf7-ec53-4b1d-8f3b-a5e39540b3ee
- https://archive.ph/JVjHf
Fact Check:
To verify the claim, we conducted a detailed search using relevant keywords but found no credible media reports or official statements to support it. Although Gurugram’s temperature dropped to 0.6 degrees Celsius amid an IMD-issued cold wave warning, there is no evidence to suggest that the city experienced snowfall or hail. As of January 16, 2026, weather records and official sources confirm that no such weather event occurred in Gurugram.
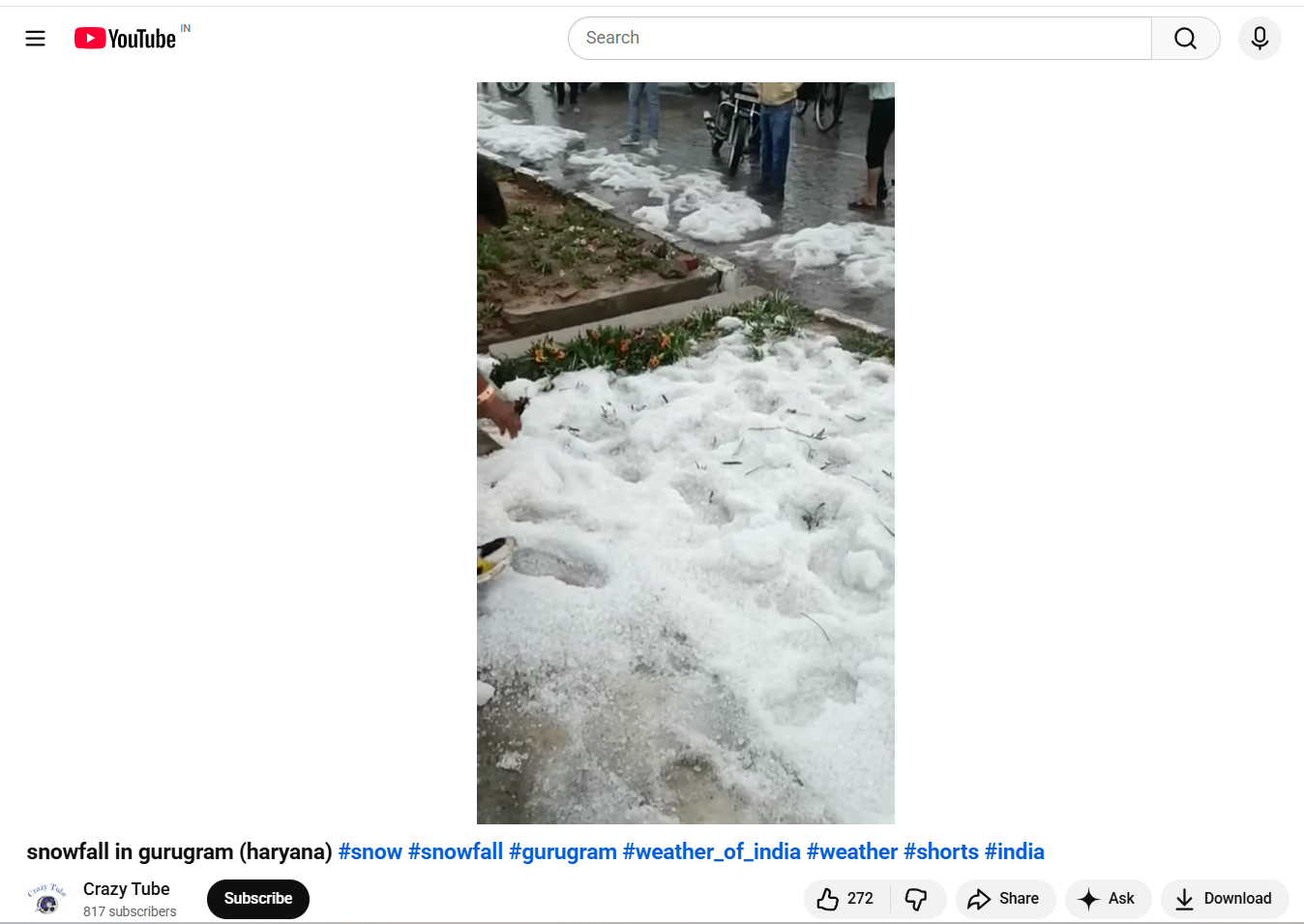
A reverse image search of keyframes extracted from the viral clip traced the same footage to a video uploaded on the YouTube channel Crazy Tube on March 21, 2023. This establishes that the video has been in circulation for nearly three years. In the original upload, the person filming clearly mentions that the visuals were recorded near a toll plaza, further indicating that the clip is unrelated to the recent weather conditions in Gurugram. Link and Screen Shot
We also came across an X (formerly Twitter) post from March 19, 2023, which featured images similar to those seen in the viral video. The post described the visuals as being from a hailstorm in Gurugram, indicating that the content predates the current weather conditions and is unrelated to the recent cold wave.

Conclusion:
The video is old and predates January 2026, and has been on the internet at least since March 2023. While Gurugram recorded a low of 0.6 degrees Celsius amid an IMD cold wave warning, the city did not experience snowfall or hail as of 16 January 2026. News reports from March 2023 confirm heavy rain and hail in Delhi and adjoining areas, including parts of Gurugram, but there is no evidence of snowfall in January 2026. Hence, the claim made in the post is MISLEADING.

Introduction
The United Nations (UN) has unveiled a set of principles, known as the 'Global Principles for Information Integrity', to combat the spread of online misinformation, disinformation, and hate speech. These guidelines aim to address the widespread harm caused by false information on digital platforms. The UN's Global Principles are based on five core principles: social trust and resilience, independent, free, and pluralistic media, healthy incentives, transparency and research, and public empowerment. The UN chief emphasized that the threats to information integrity are not new but are now spreading at unprecedented speeds due to digital platforms and artificial intelligence technologies.
These principles aim to enhance global cooperation in order to create a safer online environment. It was further highlighted that the spread of misinformation, disinformation, hate speech, and other risks in the information environment poses threats to democracy, human rights, climate action, and public health. This impact is intensified by the emergence of rapidly advancing Artificial Intelligence Technology (AI tech) that poses a growing threat to vulnerable groups in information environments.
The Highlights of Key Principles
- Societal Trust and Resilience: Trust in information sources and the ability and resilience to handle disruptions are critical for maintaining information integrity. Both are at risk from state and non-state actors exploiting the information ecosystem.
- Healthy Incentives: Current business models reliant on targeted advertising threaten information integrity. The complex, opaque nature of digital advertising benefits large tech companies and it requires reforms to ensure transparency and accountability.
- Public Empowerment: People require the capability to manage their online interactions, the availability of varied and trustworthy information, and the capacity to make informed decisions. Media and digital literacy are crucial, particularly for marginalized populations.
- Independent, Free, and Pluralistic Media: A free press supports democracy by fostering informed discourse, holding power accountable, and safeguarding human rights. Journalists must operate safely and freely, with access to diverse news sources.
- Transparency and research: Technology companies must be transparent about how information is propagated and how personal data is used. Research and privacy-preserving data access should be encouraged to address information integrity gaps while protecting those investigating and reporting on these issues.
Stakeholders Called for Action
Stakeholders, including technology companies, AI actors, advertisers, media, researchers, civil society organizations, state and political actors, and the UN, have been called to take action under the UN Global Principles for Information Integrity. These principles should be used to build and participate in broad cross-sector coalitions that bring together diverse expertise from civil society, academia, media, government, and the international private sector, focussing on capacity-building and meaningful youth engagement through dedicated advisory groups. Additionally, collaboration is required to develop multi-stakeholder action plans at regional, national, and local levels, engaging communities in grassroots initiatives and ensuring that youth are fully and meaningfully involved in the process.
Implementation and Monitoring
To effectively implement the UN Global Principles at large requires developing a multi-stakeholder action plan at various levels such as at the regional, national, and local levels. These plans should be informed and created by advice and counsel from an extensive range of communities including any of the grassroots initiatives having a deep understanding of regional challenges and their specific needs. Monitoring and evaluation are also regarded as essential components of the implementation process. Regular assessments of the progress, combined with the flexibility to adapt strategies as needed, will help ensure that the principles are effectively translated into practice.
Challenges and Considerations
Implementing these Global Principles of the UN will have certain challenges. The complexities that the digital landscape faces with the rapid pace of technological revamp, and alterations in the diversity of cultural and political contexts all present significant hurdles. Furthermore, the efforts to combat misinformation must be balanced with protecting fundamental rights, including the right to freedom of expression and privacy. Addressing these challenges to counter informational integrity will require continuous and ongoing collaboration with constant dialogue among stakeholders towards a commitment to innovation and continuous learning. It is also important to recognise and address the power imbalance within the information ecosystem, ensuring that all voices are heard and that any person, specifically, the marginalised communities is not cast aside.
Conclusion
The UN Global Principles for Online Misinformation and Information Integrity provide a comprehensive framework for addressing the critical challenges that are present while facing information integrity today. Advocating and promoting societal trust, healthy incentives, public empowerment, independent media, and transparency, these principles offer a passage towards a more resilient and trustworthy digital environment. The future success of these principles depends upon the collaborative efforts of all stakeholders, working together to safeguard the integrity of information for everyone.
References
- https://www.business-standard.com/world-news/un-unveils-global-principles-to-combat-online-misinformation-hate-speech-124062500317_1.html
- https://www.un.org/sustainabledevelopment/blog/2024/06/global-principles-information-integrity-launch/
- https://www.un.org/sites/un2.un.org/files/un-global-principles-for-information-integrity-en.pdf
- https://www.un.org/en/content/common-agenda-report/assets/pdf/Common_Agenda_Report_English.pdf
.webp)
Introduction
On September 27, 2024, the Indian government took a significant step toward enhancing national security by amending business allocation rules through an extraordinary gazette notification. This amendment, which assigns specific roles to different Union Ministries and Departments regarding telecom network security, cybersecurity, and cybercrime, aims to clarify and streamline efforts in these critical areas. With India's evolving cybersecurity landscape, the need for a structured regulatory framework is pressing, as threats grow in complexity. Recent developments, such as the July 2024 global cyber outage and increasing cyber crimes like SMS scams, highlight the urgency of such reforms. Under Article 77 clause (3), the President amended the Government of India (Allocation of Business) Rules, 1961, to designate clearer responsibilities, reinforcing India's readiness to tackle emerging digital threats.
Key Highlights of the Gazette Notification
- Telecom Networks Security: A new entry ‘1A’ matters relating to the security of telecom networks" has been added under the Department of Telecommunications, highlighting an increased focus on securing the nation's telecom infrastructure.
- Cyber Security Responsibilities: Cyber security responsibilities have been added as a new entry under the Ministry of Electronics and Information Technology (MeitY), "5B. This assigns responsibility to MeitY for cybersecurity issues, concerning the Information Technology Act of 2000, giving the ministry the mandate to support other ministries or departments regarding cybersecurity matters.
- Oversight for Cyber Crime: Under the Ministry of Home Affairs, Department of Internal Security, a new entry "36A Matters relating to Cyber Crime" is introduced. This emphasises that the MHA will handle cybercrime issues, highlighting the government's attention toward enhancing internal security against cyber threats.
- Cyber Security Strategic Coordination: Any matter related to the "overall coordination and strategic direction for Cyber Security," has been given to the National Security Council Secretariat (NSCS). This consolidates the role of the NSCS in guiding cybersecurity strategies at the national level.
Impact on Policy and Governance
The amendments introduced through the notification are poised to significantly enhance the Indian government's cybersecurity framework by clarifying the roles of various ministries. The clear separation of responsibilities, telecom network security to the Department of Telecommunications, cybercrime to the Ministry of Home Affairs, and overall cyber strategy to the National Security Council Secretariat could seen as better coordination between ministries. This clarity is expected to reduce bureaucratic delays, allowing for quicker response times in addressing cyber threats, cybercrimes, and telecom vulnerabilities. Such efficient handling is crucial, especially in the evolving landscape of digital threats. These changes have been largely welcomed as it recognises the potential for improved regulatory oversight and faster policy implementation and a step forward in bolstering India’s cyber resilience.
Conclusion
The Government of India (Allocation of Business) Rules, 1961 amendments mark a critical step in strengthening India's cybersecurity framework. By setting out specific responsibilities for telecom network security, cybercrime, and overall cybersecurity strategy among key ministries, the government seeks to improve coordination and reduce bureaucratic delays. This policy shift is poised to enhance India’s digital resilience, providing a foundation for rapid responses to emerging cyber threats. However, success hinges on effective implementation, resource allocation, and collaboration across ministries. Addressing concerns like potential jurisdictional overlap and ensuring the inclusion of bodies like NCIIPC will be pivotal to ensuring comprehensive cyber protection. The complexity of cyber crimes and threats is evolving every day and the government's ability and preparedness to handle them with regulatory insight is a high priority.
References
- https://egazette.gov.in/(S(4r5oclueuwrjypfvr5b4vtzg))/ViewPDF.aspx
- https://www.ptinews.com/story/national/govt-specifies-roles-on-matters-related-to-security-of-telecom-network-cyber-security-and-cyber-crime/1856627
- https://www.thehindubusinessline.com/economy/centre-to-further-streamline-mechanism-to-deal-with-cyber-security-cyber-crime/article68694330.ece
- https://telecom.economictimes.indiatimes.com/news/policy/govt-specifies-roles-on-matters-related-to-security-of-telecom-network-cyber-security-and-cyber-crime/113754501


