#FactCheck - AI-Generated Video Falsely Shows US Soldiers Surrendering to Iranian Forces
Executive Summary:
Amid the ongoing conflict between the United States, Israel, and Iran, a video circulating widely on social media claims to show American soldiers kneeling and surrendering to Iranian forces. In the clip, several soldiers appear to be sitting on their knees in front of armed personnel, creating the impression that they have been captured on the battlefield.
The video is being shared with the claim that the Iranian military has taken US soldiers prisoner during the war.
However, an research by the CyberPeace found that the claim is false. The viral clip is not authentic and has been generated using artificial intelligence. There is no credible evidence to support the claim that American soldiers have been captured by Iranian forces.
Claim
A Facebook user named “News Tick” shared the video on March 12, 2026, claiming that Iran had released footage of captured US soldiers. In the clip, the soldiers can be seen kneeling while armed personnel stand around them, giving the scene a highly dramatic appearance.

Fact Check
To verify the claim, we first searched the internet using relevant keywords. We found no credible reports from reputable news organizations confirming that US soldiers had been captured by Iran during the conflict. A closer examination of the video revealed several visual inconsistencies. The weapons carried by the soldiers appear unclear and oddly shaped. Additionally, the background looks unusually blurred and overly dramatic. The lighting and textures in the footage also appear artificial—common indicators of AI-generated visuals.
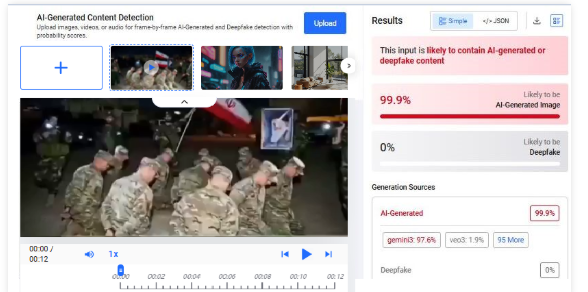
To confirm this suspicion, we analyzed the clip using multiple AI detection tools. The tool Hive Moderation indicated a 99% probability that the video was created using artificial intelligence.
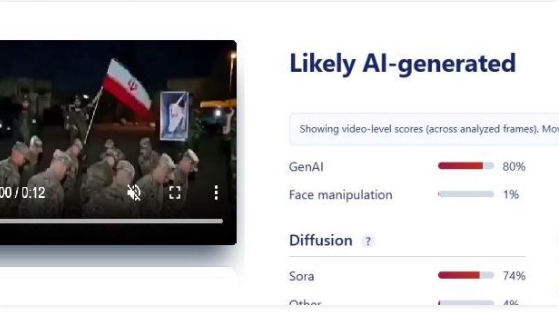
Further analysis using Sightengine also suggested that the video was likely AI-generated, estimating an 80% probability of AI creation.
Conclusion
Our research shows that the viral video claiming to depict American soldiers surrendering and being captured by Iranian forces is fake. The footage has been generated using AI and does not represent a real incident.
Related Blogs

Overview:
The National Payments Corporation of India (NPCI) officially revealed on the 31st of July 2024 that its client C-Edge Technologies had been subject to a ransomware attack. These circumstances have caused C-Edge to be separated from retail payment systems to eliminate more threats to the national payment systems. More than 200 cooperative and regional rural banks have been affected leading to disruptions in normal services including ATM withdrawals and UPI transactions.
About C-Edge Technologies:
C-Edge Technologies was founded in the year 2010 especially to meet the specific requirements of the Indian banking and other allied sectors accentuating more on the cooperative and the regional rural banks. The company offers a range of services such as Core Banking Solutions by functioning as the center of a bank where customers’ records are managed and accounting of transactions takes place, Payment Solutions through the implementation of payment gateways and mobile banking facilities, cybersecurity through threat detection and incident response to protect banking organizations, data analytics and AI through the analytics of big banking data to reduce risks and detect frauds.
Details of Ransomware attack:
Reports say, this ransomware attack has been attributed by the RansomEXX group which primarily targeted Brontoo Technology Solutions, a key collaborator with C-Edge, through a misconfigured Jenkins server, which allowed unauthorized access to the systems.
The RansomExx group also known as Defray777 or Ransom X utilized a sophisticated variant known as RansomEXX v2.0 to execute the attack. This group often targets large organizations and demands substantial ransoms. RansomEXX uses various malware tools such as IcedID, Vatet Loader, and PyXie RAT. It typically infiltrates systems through phishing emails, exploiting vulnerabilities in applications and services, including Remote Desktop Protocol (RDP). The ransomware encrypts files using the Advanced Encryption Standard (AES), with the encryption key further secured using RSA encryption. This dual-layer encryption complicates recovery efforts for victims. RansomEXX operates on a ransomware-as-a-service model, allowing affiliates to conduct attacks using its infrastructure. Earlier in 2021, it attacked StarHub and Gigabyte’s servers for ransome.
Impact due to the attack:
The immediate consequences of the ransomware attack include:
- Service Disruption: This has negative implications to consumers especially the citizens who use the banks to do their day to day banking activities such as withdrawals and online transactions. Among the complaints some of them relate to cases where the sender’s account has been debited without the corresponding credit to the receiver account.
- Isolation Measures: Likely, NPCI is already following the right measures as it had disconnected C-Edge from its networks to contain the proliferation of the ransomware. This decision was made as a precautionary measure so that all functional aspects in a larger financial system are safeguarded.
Operations resumed:
The National Payments Corporation of India (NPCI) said it has restored connectivity with C-Edge Technologies Ltd after the latter’s network connection was severed by NPCI over security concerns that were evaluated by an external forensic auditing firm. The audit affirmed that all affected systems were contained in order to avoid the occurrence of ransomware attack contagion. All the affected systems were localized in C-Edge’s data center and no repercussion was evidenced regarding the infrastructure of the cooperative banks or the regional rural banks that are involved in the business. Both NPCI and C-Edge Technologies have resumed normalcy so that the banking and financial services being offered by these banks remain safe and secure.
Major Implications for Banking Sector:
The attack on C-Edge Technologies raises several critical concerns for the Indian banking sector:
- Cybersecurity Vulnerabilities: It also shows the weak linkages which are present within the technology system that help smaller sized banks. Nevertheless, the service has been offered by C-Edge regarding their cybersecurity solution, this attack evidence that the securities required should improve in all types of banks and banking applications.
- Financial Inclusion Risks: Co operative and regional rural banks also have its importance in the financial inclusion especially in rural and semi urban areas. Gradually, interruptions to their services pose a risk to signal diminished improvement in financial literacy for the excluded groups contrary to the common year advancement.
- Regulatory Scrutiny: After this event, agencies such as the Reserve Bank of India (RBI) may enhance the examination of the banking sector’s cybersecurity mechanisms. Some of the directives may even require institutions to adhere to higher compliance measures regarding the defense against cyber threats.
Way Forward: Mitigation
- Strengthening Cybersecurity: It is important to enhance the cyber security to eliminate this kind of attacks in the future. This may include using better threat detection systems, penetration testing to find the vulnerabilities, system hardening, and network monitoring from time to time.
- Transition to Cloud-Based Solutions: The application of adaptations in cloud solutions can contribute to the enhancement in operative efficiency as well as optimization in the utilization of resources. The security features of cloud should be implemented for safety and protection against cyber threats for SMEs in the banking sector.
- Leveraging AI and Data Analytics: Development of the AI-based solutions for fraud and risk control means that bank organizations get the chance to address threats and to regain clients’ trust.
Conclusion:
This ransomware attack in C-Edge Technologies in the banking sector provides a warning for all the infrastructures. Initial cleanup methodologies and quarantining are effective. The continuous monitoring of cyber security features in the infrastructure and awareness between employees helps to avoid these kinds of attacks. Building up cyber security areas will also effectively safeguard the institution against other cyber risks in the future and fortify the confidence and reliability of the financial system, especially the regional rural banks.
Reference:
- https://www.businesstoday.in/technology/news/story/c-edge-technologies-a-deep-dive-into-the-indian-fintech-powerhouse-hit-by-major-cyberattack-439657-2024-08-01
- https://www.thehindu.com/sci-tech/technology/customers-at-several-small-sized-banks-affected-as-tech-provider-c-edge-suffers-ransomware-attack/article68470198.ece
- https://www.cnbctv18.com/technology/ransomware-attack-disrupts-over-200-co-operative-banks-regional-rural-banks-19452521.htm
- https://timesofindia.indiatimes.com/city/ahmedabad/ransomware-breach-at-c-edge-impacts-transactions-for-cooperative-banks/articleshow/112180914.cms
- https://www.emsisoft.com/en/blog/41027/ransomware-profile-ransomexx/
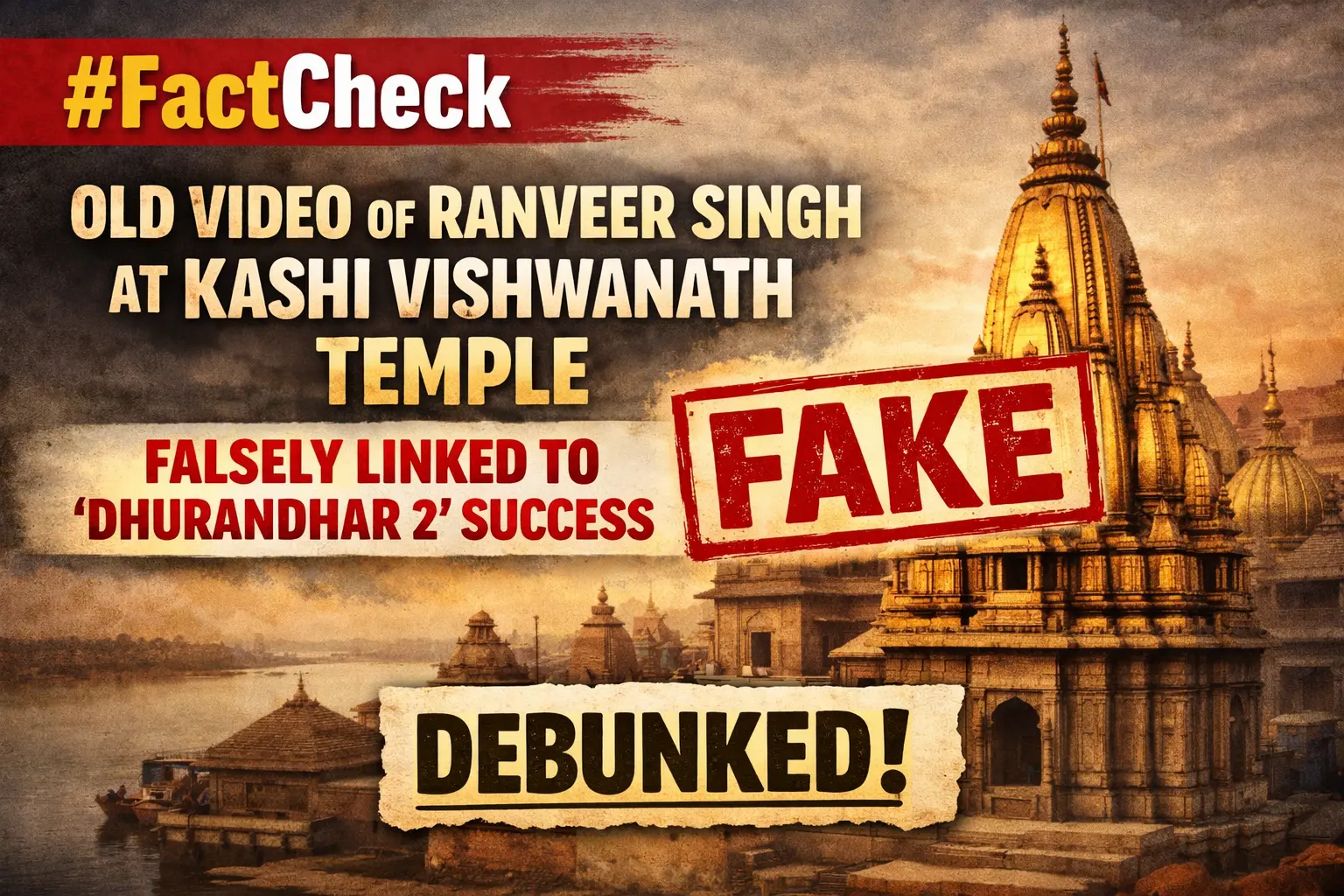
Executive Summary
Following the reported box office success of ‘Dhurandhar 2: The Revenge’, released on March 19, 2026, a video of Ranveer Singh visiting a temple is being widely shared on social media. Users claim that the actor visited the Kashi Vishwanath Temple to offer prayers after the film’s success. Research by CyberPeace found that the viral claim is misleading. The video of Ranveer Singh visiting the Kashi Vishwanath Temple is not recent. It dates back to 2024, when he visited the temple with Kriti Sanon, and is unrelated to the release or success of ‘Dhurandhar 2: The Revenge’.
Claim
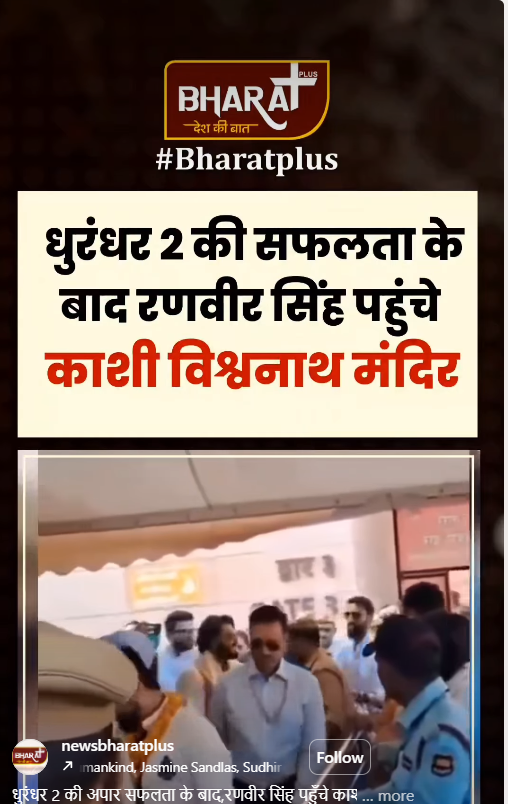
An Instagram user “newsbharatplus” shared the video on March 26, 2026, with a caption stating that after the massive success of Dhurandhar 2, Ranveer Singh visited the temple and performed rituals.
Fact Check
To verify the claim, we extracted keyframes from the viral video and conducted a reverse image search. This led us to a report published by Dainik Jagran on April 14, 2024. According to the report, Ranveer Singh had visited the Kashi Vishwanath Temple along with Kriti Sanon and noted fashion designer Manish Malhotra. During the visit, the trio was seen offering prayers, wearing traditional attire, and applying sandalwood tilak.
https://www.jagran.com/entertainment/bollywood-ranveer-singh-and-kriti-sanon-visits-kashi-vishwanath-temple-with-manish-malhotra-see-photos-here-23696781.html

We also found a video report on the official YouTube channel of Times Now Navbharat, uploaded on April 15, 2024, showing Ranveer Singh and Kriti Sanon at the temple. The report also featured visuals from a fashion event held in Varanasi.
- https://www.youtube.com/watch?v=OMuW_SVbfb4

Conclusion
The viral claim is misleading. The video of Ranveer Singh visiting the Kashi Vishwanath Temple is not recent. It dates back to 2024, when he visited the temple with Kriti Sanon, and is unrelated to the release or success of ‘Dhurandhar 2: The Revenge’.

Introduction
Twitter is a popular social media plate form with millions of users all around the world. Twitter’s blue tick system, which verifies the identity of high-profile accounts, has been under intense scrutiny in recent years. The platform must face backlash from its users and brands who have accused it of basis, inaccuracy, and inconsistency in its verification process. This blog post will explore the questions raised on the verification process and its impact on users and big brands.
What is Twitter’s blue trick System?
The blue tick system was introduced in 2009 to help users identify the authenticity of well-known public figures, Politicians, celebrities, sportspeople, and big brands. The Twitter blue Tick system verifies the identity of high-profile accounts to display a blue badge next to your username.
According to a survey, roughly there are 294,000 verified Twitter Accounts which means they have a blue tick badge with them and have also paid the subscription for the service, which is nearly $7.99 monthly, so think about those subscribers who have paid the amount and have also lost their blue badge won’t they feel cheated?
The Controversy
Despite its initial aim, the blue tick system has received much criticism from consumers and brands. Twitter’s irregular and non-transparent verification procedure has sparked accusations of prejudice and inaccuracy. Many Twitter users have complained that the network’s verification process is random and favours account with huge followings or celebrity status. In contrast, others have criticised the platform for certifying accounts that promote harmful or controversial content.
Furthermore, the verification mechanism has generated user confusion, as many need to understand the significance of the blue tick badge. Some users have concluded that the blue tick symbol represents a Twitter endorsement or that the account is trustworthy. This confusion has resulted in users following and engaging with verified accounts that promote misleading or inaccurate data, undermining the platform’s credibility.
How did the Blue Tick Row start in India?
On 21 May 2021, when the government asked Twitter to remove the blue badge from several profiles of high-profile Indian politicians, including the Indian National Congress Party Vice-President Mr Rahul Ghandhi.
The blue badge gives the users an authenticated identity. Many celebrities, including Amitabh Bachchan, popularly known as Big B, Vir Das, Prakash Raj, Virat Kohli, and Rohit Sharma, have lost their blue tick despite being verified handles.
What is the Twitter policy on blue tick?
To Twitter’s policy, blue verification badges may be removed from accounts if the account holder violates the company’s verification policy or terms of service. In such circumstances, Twitter typically notifies the account holder of the removal of the verification badge and the reason for the removal. In the instance of the “Twitter blue badge row” in India, however, it appears that Twitter did not notify the impacted politicians or their representatives before revoking their verification badges. Twitter’s lack of communication has exacerbated the controversy around the episode, with some critics accusing the company of acting arbitrarily and not following due process.
Is there a solution?
The “Twitter blue badge row” has no simple answer since it involves a complex convergence of concerns about free expression, social media policies, and government laws. However, here are some alternatives:
- Establish clear guidelines: Twitter should develop and constantly implement clear guidelines and policies for the verification process. All users, including politicians and government officials, would benefit from greater transparency and clarity.
- Increase transparency: Twitter’s decision-making process for deleting or restoring verification badges should be more open. This could include providing explicit reasons for badge removal, notifying impacted users promptly, and offering an appeals mechanism for those who believe their credentials were removed unfairly.
- Engage in constructive dialogue: Twitter should engage in constructive dialogue with government authorities and other stakeholders to address concerns about the platform’s content moderation procedures. This could contribute to a more collaborative approach to managing online content, leading to more effective and accepted policies.
- Follow local rules and regulations: Twitter should collaborate with the Indian government to ensure it conforms to local laws and regulations while maintaining freedom of expression. This could involve adopting more precise standards for handling requests for material removal or other actions from governments and other organisations.
Conclusion
To sum up, the “Twitter blue tick row” in India has highlighted the complex challenges that Social media faces daily in handling the conflicting interests of free expression, government rules, and their own content moderation procedures. While Twitter’s decision to withdraw the blue verification badges of several prominent Indian politicians garnered anger from the government and some public members, it also raised questions about the transparency and uniformity of Twitter’s verification procedure. In order to deal with this issue, Twitter must establish clear verification procedures and norms, promote transparency in its decision-making process, participate in constructive communication with stakeholders, and adhere to local laws and regulations. Furthermore, the Indian government should collaborate with social media platforms to create more effective and acceptable laws that balance the necessity for free expression and the protection of citizens’ rights. The “Twitter blue tick row” is just one example of the complex challenges that social media platforms face in managing online content, and it emphasises the need for greater collaboration among platforms, governments, and civil society organisations to develop effective solutions that protect both free expression and citizens’ rights.


