#Fact Check: AI Video Falsely Shows Afghanistan Downing Pakistani Fighter Jet
Executive Summary:
Amid escalating tensions between Afghanistan and Pakistan, a video is being widely shared on social media claiming that Afghanistan has shot down a Pakistani fighter jet. The posts further allege that the incident marks the formal beginning of a war between the two countries. However, research conducted by the CyberPeace found the viral claim to be false and the research revealed that the circulating video is not authentic but AI-generated.
Claim
On February 24, 2026, a user on X (formerly Twitter) shared the viral video with the caption: “Afghanistan has shot down a Pakistani fighter jet! Afghanistan announces that war with Pakistan has begun.”
- Original post link: https://x.com/JyotiDevSpeaks/status/2026348257186545914
- Archived link: https://ghostarchive.org/archive/7l00Y

Fact Check:
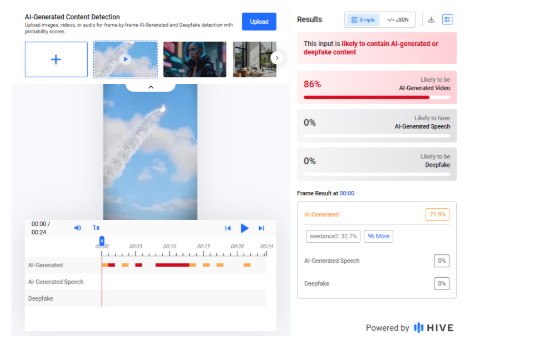
A careful review of the viral video revealed unusual visual patterns and artificial-looking effects, raising suspicions that it may have been created using artificial intelligence.We analyzed the video using the AI detection tool Hive Moderation, which indicated an 86 percent probability that the video was AI-generated.
To further verify the findings, we scanned the footage using another AI detection platform, Sightengine. The results showed a 99 percent likelihood that the video was AI-generated.

To understand the broader context of the ongoing tensions, we conducted a keyword search and found a report published on February 22, 2026, by BBC Hindi. According to the report, Pakistan claimed it had targeted “seven terrorist hideouts and camps” along the Pakistan–Afghanistan border based on intelligence inputs. Meanwhile, a spokesperson for the Taliban government in Afghanistan stated that Pakistani airstrikes in Nangarhar and Paktika provinces resulted in the deaths of dozens of people, including women and children.
- https://www.bbc.com/hindi/articles/clyz8141397o
Conclusion
Our research confirms that the viral video claiming Afghanistan shot down a Pakistani fighter jet and formally declared war on Pakistan is fake. The footage is AI-generated and is being circulated with a false and misleading narrative.
Related Blogs

Introduction
Election misinformation poses a major threat to democratic processes all over the world. The rampant spread of misleading information intentionally (disinformation) and unintentionally (misinformation) during the election cycle can not only create grounds for voter confusion with ramifications on election results but also incite harassment, bullying, and even physical violence. The attack on the United States Capitol Building in Washington D.C., in 2021, is a classic example of this phenomenon, where the spread of dis/misinformation snowballed into riots.
Election Dis/Misinformation
Election dis/misinformation is false or misleading information that affects/influences public understanding of voting, candidates, and election integrity. The internet, particularly social media, is the foremost source of false information during elections. It hosts fabricated news articles, posts or messages containing incorrectly-captioned pictures and videos, fabricated websites, synthetic media and memes, and distorted truths or lies. In a recent example during the 2024 US elections, fake videos using the Federal Bureau of Investigation’s (FBI) insignia alleging voter fraud in collusion with a political party and claiming the threat of terrorist attacks were circulated. According to polling data collected by Brookings, false claims influenced how voters saw candidates and shaped opinions on major issues like the economy, immigration, and crime. It also impacted how they viewed the news media’s coverage of the candidates’ campaign. The shaping of public perceptions can thus, directly influence election outcomes. It can increase polarisation, affect the quality of democratic discourse, and cause disenfranchisement. From a broader perspective, pervasive and persistent misinformation during the electoral process also has the potential to erode public trust in democratic government institutions and destabilise social order in the long run.
Challenges In Combating Dis/Misinformation
- Platform Limitations: Current content moderation practices by social media companies struggle to identify and flag misinformation effectively. To address this, further adjustments are needed, including platform design improvements, algorithm changes, enhanced content moderation, and stronger regulations.
- Speed and Spread: Due to increasingly powerful algorithms, the speed and scale at which misinformation can spread is unprecedented. In contrast, content moderation and fact-checking are reactive and are more time-consuming. Further, incendiary material, which is often the subject of fake news, tends to command higher emotional engagement and thus, spreads faster (virality).
- Geopolitical influences: Foreign actors seeking to benefit from the erosion of public trust in the USA present a challenge to the country's governance, administration and security machinery. In 2018, the federal jury indicted 11 Russian military officials for alleged computer hacking to gain access to files during the 2016 elections. Similarly, Russian involvement in the 2024 federal elections has been alleged by high-ranking officials such as White House national security spokesman John Kirby, and Attorney General Merrick Garland.
- Lack of Targeted Plan to Combat Election Dis/Misinformation: In the USA, dis/misinformation is indirectly addressed through laws on commercial advertising, fraud, defamation, etc. At the state level, some laws such as Bills AB 730, AB 2655, AB 2839, and AB 2355 in California target election dis/misinformation. The federal and state governments criminalize false claims about election procedures, but the Constitution mandates “breathing space” for protection from false statements within election speech. This makes it difficult for the government to regulate election-related falsities.
CyberPeace Recommendations
- Strengthening Election Cybersecurity Infrastructure: To build public trust in the electoral process and its institutions, security measures such as updated data protection protocols, publicized audits of election results, encryption of voter data, etc. can be taken. In 2022, the federal legislative body of the USA passed the Electoral Count Reform and Presidential Transition Improvement Act (ECRA), pushing reforms allowing only a state’s governor or designated executive official to submit official election results, preventing state legislatures from altering elector appointment rules after Election Day and making it more difficult for federal legislators to overturn election results. More investments can be made in training, scenario planning, and fact-checking for more robust mitigation of election-related malpractices online.
- Regulating Transparency on Social Media Platforms: Measures such as transparent labeling of election-related content and clear disclosure of political advertising to increase accountability can make it easier for voters to identify potential misinformation. This type of transparency is a necessary first step in the regulation of content on social media and is useful in providing disclosures, public reporting, and access to data for researchers. Regulatory support is also required in cases where popular platforms actively promote election misinformation.
- Increasing focus on ‘Prebunking’ and Debunking Information: Rather than addressing misinformation after it spreads, ‘prebunking’ should serve as the primary defence to strengthen public resilience ahead of time. On the other hand, misinformation needs to be debunked repeatedly through trusted channels. Psychological inoculation techniques against dis/misinformation can be scaled to reach millions on social media through short videos or messages.
- Focused Interventions On Contentious Themes By Social Media Platforms: As platforms prioritize user growth, the burden of verifying the accuracy of posts largely rests with users. To shoulder the responsibility of tackling false information, social media platforms can outline critical themes with large-scale impact such as anti-vax content, and either censor, ban, or tweak the recommendations algorithm to reduce exposure and weaken online echo chambers.
- Addressing Dis/Information through a Socio-Psychological Lens: Dis/misinformation and its impact on domains like health, education, economy, politics, etc. need to be understood through a psychological and sociological lens, apart from the technological one. A holistic understanding of the propagation of false information should inform digital literacy training in schools and public awareness campaigns to empower citizens to evaluate online information critically.
Conclusion
According to the World Economic Forum’s Global Risks Report 2024, the link between misleading or false information and societal unrest will be a focal point during elections in several major economies over the next two years. Democracies must employ a mixed approach of immediate tactical solutions, such as large-scale fact-checking and content labelling, and long-term evidence-backed countermeasures, such as digital literacy, to curb the spread and impact of dis/misinformation.
Sources
- https://www.cbsnews.com/news/2024-election-misinformation-fbi-fake-videos/
- https://www.brookings.edu/articles/how-disinformation-defined-the-2024-election-narrative/
- https://www.fbi.gov/wanted/cyber/russian-interference-in-2016-u-s-elections
- https://indianexpress.com/article/world/misinformation-spreads-fear-distrust-ahead-us-election-9652111/
- https://academic.oup.com/ajcl/article/70/Supplement_1/i278/6597032#377629256
- https://www.brennancenter.org/our-work/policy-solutions/how-states-can-prevent-election-subversion-2024-and-beyond
- https://www.bbc.com/news/articles/cx2dpj485nno
- https://msutoday.msu.edu/news/2022/how-misinformation-and-disinformation-influence-elections
- https://misinforeview.hks.harvard.edu/article/a-survey-of-expert-views-on-misinformation-definitions-determinants-solutions-and-future-of-the-field/
- https://reutersinstitute.politics.ox.ac.uk/sites/default/files/2023-06/Digital_News_Report_2023.pdf
- https://www.weforum.org/stories/2024/03/disinformation-trust-ecosystem-experts-curb-it/
- https://www.apa.org/topics/journalism-facts/misinformation-recommendations
- https://mythvsreality.eci.gov.in/
- https://www.brookings.edu/articles/transparency-is-essential-for-effective-social-media-regulation/
- https://www.brookings.edu/articles/how-should-social-media-platforms-combat-misinformation-and-hate-speech/

Executive Summary
A claim circulating on social media alleges that India refused to unload crude oil from two Iranian tankers following a call between US President Donald Trump and Prime Minister Narendra Modi, after the US announced fresh restrictions on Iranian oil exports. However, research by the CyberPeace Research Wing found the claim to be misleading. The probe revealed that two supertankers carrying Iranian crude are currently anchored off India’s western and eastern coasts. No credible evidence or reports suggest that India refused to unload the cargo or sent the vessels back.
Claim
A user on X claimed that India returned 2 million barrels of Iranian crude oil after a phone call from Donald Trump. According to the post, India had already paid for the oil and the tanker was en route, but following the call with Narendra Modi, authorities refused to unload the shipment and sent the tanker back to Iran.
Fact Check
No credible national or international media reports were found to support the claim that India refused to accept Iranian oil or returned the tankers. Given the global scrutiny on oil shipments amid tensions in West Asia, any such development would have drawn widespread coverage. According to Reuters, two large crude carriers loaded with Iranian oil reached Indian ports on April 13. The Iran-flagged Felicity arrived near Sikka port in Gujarat, while the Curacao-flagged Jaya reached Paradip port in Odisha. The report noted that this marked the first purchase of Iranian oil by Indian refiners since 2019.
Further, The Times of India reported that Felicity, owned by the National Iranian Tanker Company, anchored off Sikka on April 12 carrying around 2 million barrels of crude loaded from Kharg Island in mid-March. The second tanker, Jaya, also anchored near Paradip around the same time, having departed with a similar volume of crude in late February. While the buyers of these cargoes have not been officially disclosed, Paradip port is primarily used by Indian Oil Corporation, while Sikka port is used by Reliance Industries and Bharat Petroleum Corporation.
Conclusion
The viral claim is false and misleading. Available evidence shows that the Iranian oil tankers are stationed near Indian ports, and there is no confirmation that India refused to unload the cargo or sent the vessels back.

Executive Summary
Recent claims circulating on social media allege that an Indian Air Force MiG-29 fighter jet was shot down by Pakistani forces during "Operation Sindoor." These reports suggest the incident involved a jet crash attributed to hostile action. However, these assertions have been officially refuted. No credible evidence supports the existence of such an operation or the downing of an Indian aircraft as described. The Indian Air Force has not confirmed any such event, and the claim appears to be misinformation.

Claim
A social media rumor has been circulating, suggesting that an Indian Air Force MiG-29 fighter jet was shot down by Pakistani Air forces during "Operation Sindoor." The claim is accompanied by images purported to show the wreckage of the aircraft.

Fact Check
The social media posts have falsely claimed that a Pakistani Air Force shot down an Indian Air Force MiG-29 during "Operation Sindoor." This claim has been confirmed to be untrue. The image being circulated is not related to any recent IAF operations and has been previously used in unrelated contexts. The content being shared is misleading and does not reflect any verified incident involving the Indian Air Force.

After conducting research by extracting key frames from the video and performing reverse image searches, we successfully traced the original post, which was first published in 2024, and can be seen in a news article from The Hindu and Times of India.
A MiG-29 fighter jet of the Indian Air Force (IAF), engaged in a routine training mission, crashed near Barmer, Rajasthan, on Monday evening (September 2, 2024). Fortunately, the pilot safely ejected and escaped unscathed, hence the claim is false and an act to spread misinformation.

Conclusion
The claims regarding the downing of an Indian Air Force MiG-29 during "Operation Sindoor" are unfounded and lack any credible verification. The image being circulated is outdated and unrelated to current IAF operations. There has been no official confirmation of such an incident, and the narrative appears to be misleading. Peoples are advised to rely on verified sources for accurate information regarding defence matters.
- Claim: Pakistan Shot down an Indian Fighter Jet, MIG-29
- Claimed On: Social Media
- Fact Check: False and Misleading


