#FactCheck- AI-Generated Image of PM Modi Misleadingly Shared as Assam Campaign Shoot Setup
Executive Summary
An image of Prime Minister Narendra Modi is being widely circulated on social media. The picture is being shared with the claim that during an election campaign in Assam, a full-fledged shooting set was arranged in a tea garden where Modi interacted with women workers, complete with cameras, microphones, lights, and a director-led production team. However, research by the CyberPeace has found the claim to be false. Our research reveals that the viral image is AI-generated and is being shared with a misleading narrative.
Claim
An Instagram user shared the viral image with the caption suggesting that such a large-scale “shoot” setup had been arranged and questioned the cost involved.
Post link:

Fact Check
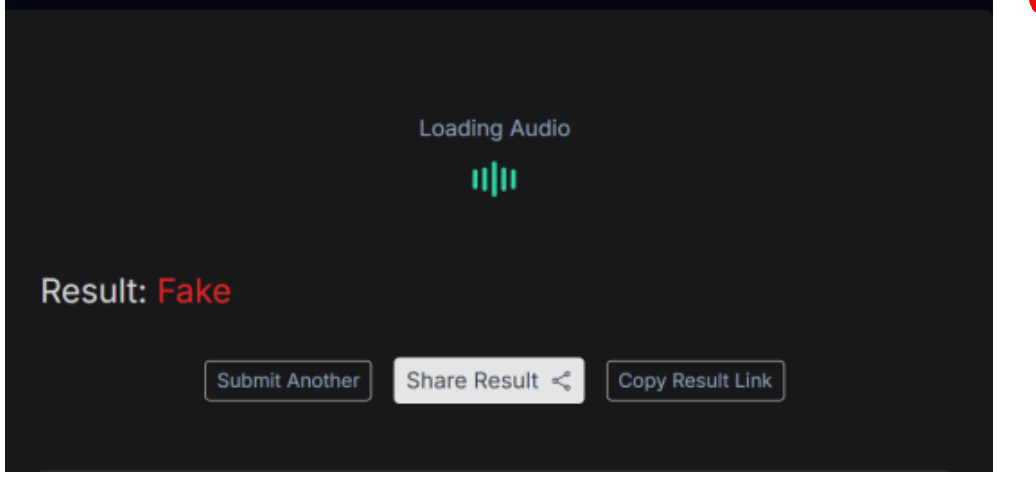
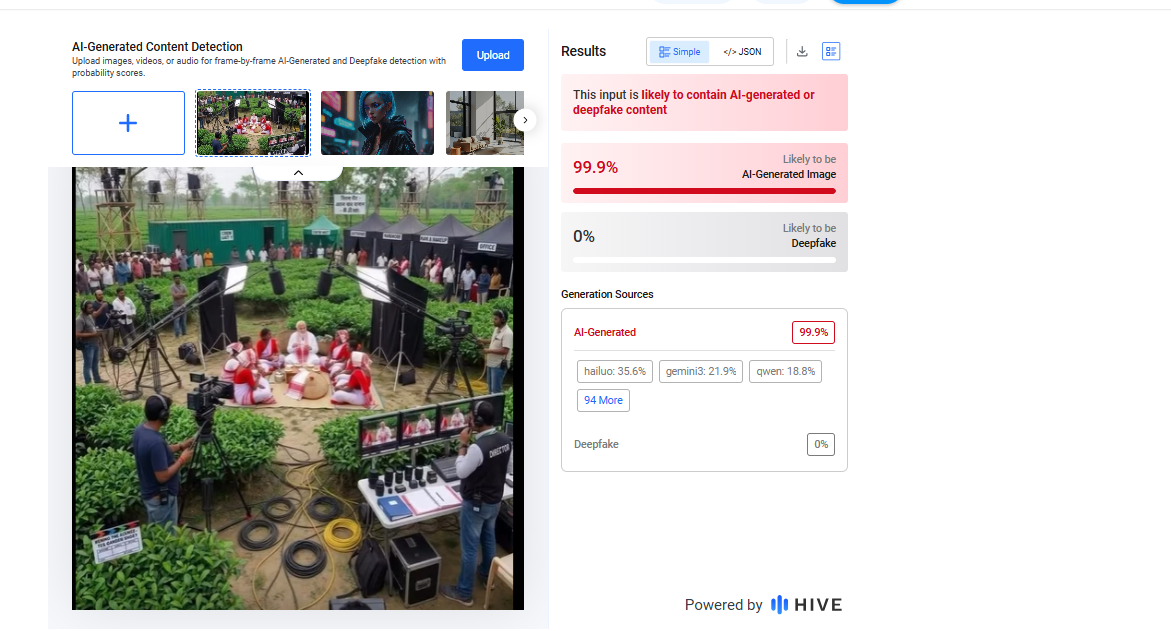
To verify the claim, we conducted a keyword-based search on Google. However, we did not find any credible media reports supporting the claim that such a shooting setup was arranged during Prime Minister Modi’s visit to Assam. Upon closely examining the viral image, we noticed several visual inconsistencies that raised suspicion about it being artificially generated. To confirm this, we analyzed the image using the AI detection tool Hive Moderation, which indicated that the image is approximately 99% AI-generated.
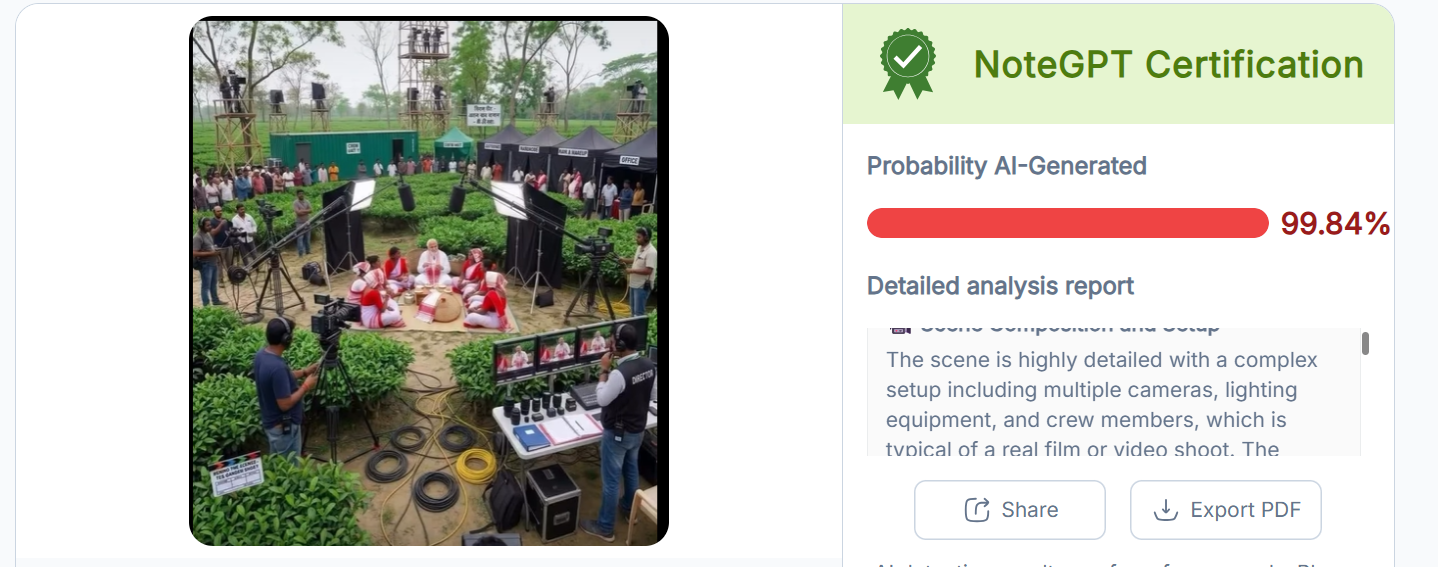
To further validate the findings, we also tested the image using another AI detection tool, NoteGPT, which similarly classified the image as 99% AI-generated.
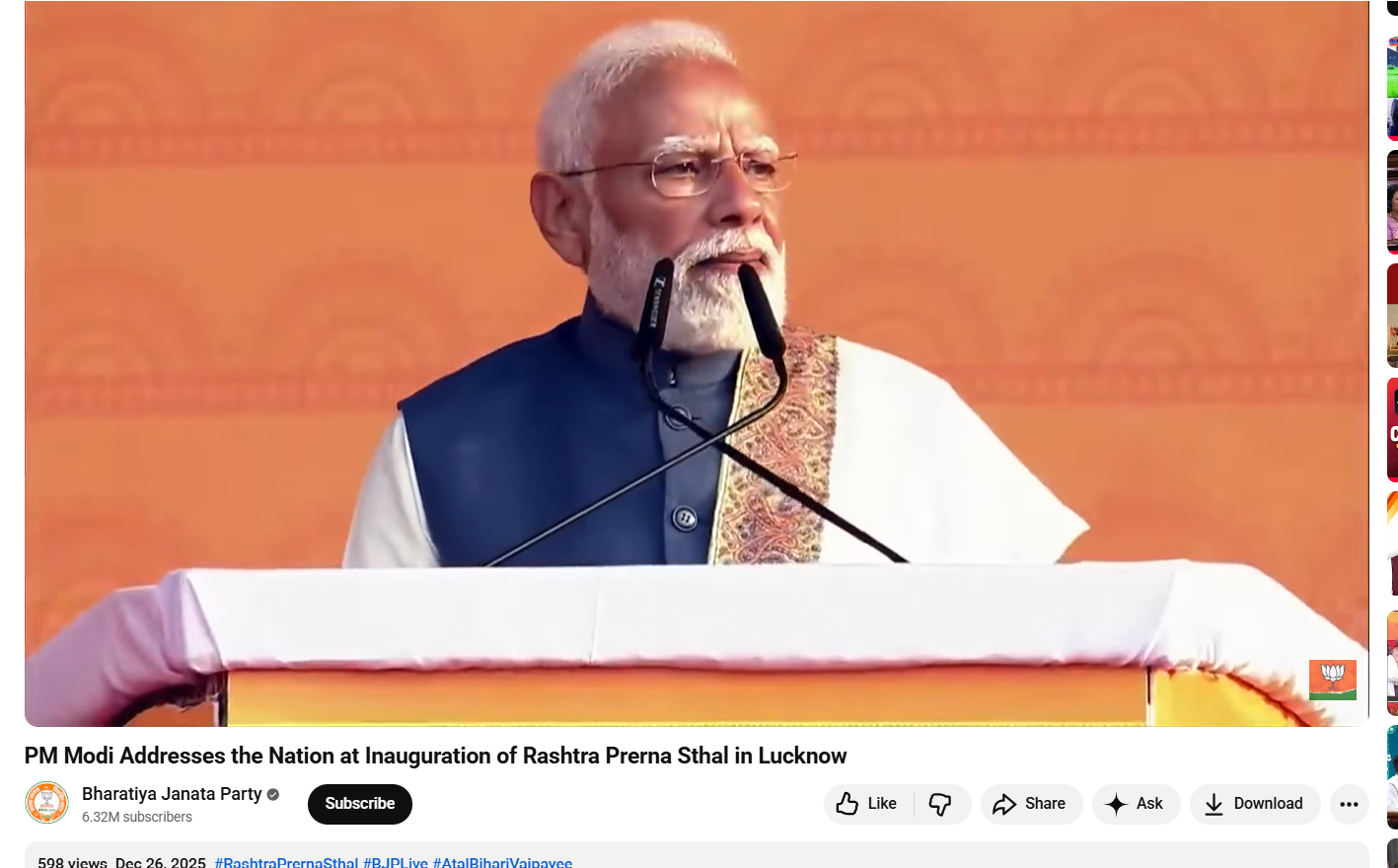
For context, ahead of the 2026 Assam Assembly elections, Prime Minister Narendra Modi has been on a campaign visit to the state. According to a report by DD News, he visited a tea garden in Dibrugarh, where he interacted with women workers and even plucked tea leaves himself.

Conclusion
Our research clearly establishes that the viral image of Prime Minister Narendra Modi is not authentic and has been digitally created using AI tools. There is no evidence to support the claim that a staged shooting setup involving cameras, lights, and a production crew was arranged during his visit. The image is being circulated with a misleading narrative to create a false impression. This case highlights how AI-generated visuals can be used to distort real events and spread misinformation.