#FactCheck- AI-Generated Image of Narendra Modi Goes Viral Ahead of Kerala Elections
Executive Summary
As Kerala gears up for its upcoming Assembly elections, political activity has intensified across the state. Amid this charged atmosphere, a purported image of Narendra Modi has gone viral on social media. The image shows the Prime Minister holding coconuts, with several photographers around him. It is being claimed that the photo was taken during his recent visit for the 2026 Kerala Assembly election campaign.
However, an research by the CyberPeace has debunked the claim, confirming that the image is fake and generated using artificial intelligence.
Claim
A Facebook user named “Javed Ahmad” shared the viral image on April 6, 2026, with a sarcastic caption suggesting that the Prime Minister was posing for reels during his Kerala visit.
- https://www.facebook.com/Ahmadspeaks4u/posts/pfbid0aRnhwXBjnfSXF9S48vaH1gTQrGQmxnRmhpJCRxMWazqLJhYs6zxM9rot51qtBgRLl
- https://perma.cc/N3AM-Q2YC

Fact Check
To verify the claim, we conducted keyword searches on Google but found no credible news reports supporting it. A reverse image search also did not yield any reliable sources. Additionally, a thorough review of the Prime Minister’s official social media accounts showed no trace of such an image or event. Given these inconsistencies, suspicion arose about the image’s authenticity.
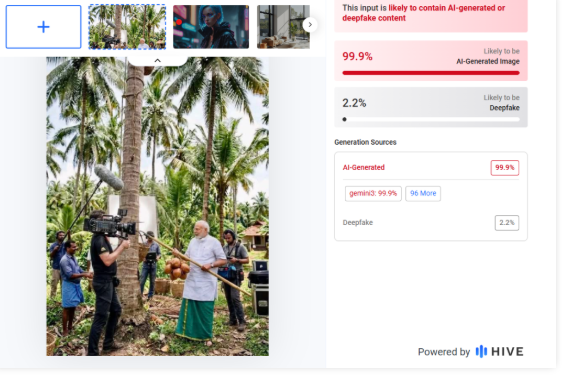
The viral image was then analyzed using AI detection tools. Results from HIVE Moderation indicated a 99% probability that the image is AI-generated.
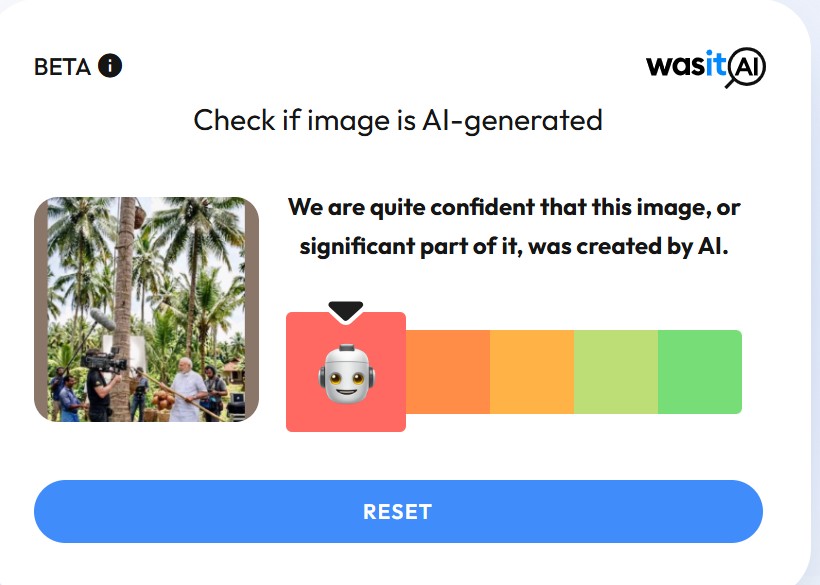
Another tool, Wasit AI, also confirmed that the image is artificially created.
Conclusion
The claim is false. The viral image of Prime Minister Narendra Modi is not real and has been generated using AI tools, likely similar to Google AI.
Related Blogs

In a recent ruling, a U.S. federal judge sided with Meta in a copyright lawsuit brought by a group of prominent authors who alleged that their works were illegally used to train Meta’s LLaMA language model. While this seems like a significant legal victory for the tech giant, it may not be so. Rather, this is a good case study for creators in the USA to refine their legal strategies and for policymakers worldwide to act quickly to shape the rules of engagement between AI and intellectual property.
The Case: Meta vs. Authors
In Kadrey v. Meta, the plaintiffs alleged that Meta trained its LLaMA models on pirated copies of their books, violating copyright law. However, U.S. District Judge Vince Chhabria ruled that the authors failed to prove two critical things: that their copyrighted works had been used in a way that harmed their market and that such use was not “transformative.” In fact, the judge ruled that converting text into numerical representations to train an AI was sufficiently transformative under the U.S. fair use doctrine. He also noted that the authors’ failure to demonstrate economic harm undermined their claims. Importantly, he clarified that this ruling does not mean that all AI training data usage is lawful, only that the plaintiffs didn’t make a strong enough case.
Meta even admitted that some data was sourced from pirate sites like LibGen, but the Judge still found that fair use could apply because the usage was transformative and non-exploitative.
A Tenuous Win
Chhabria’s decision emphasised that this is not a blanket endorsement of using copyrighted content in AI training. The judgment leaned heavily on the procedural weakness of the case and not necessarily on the inherent legality of Meta’s practices.
Policy experts are warning that U.S. courts are currently interpreting AI training as fair use in narrow cases, but the rulings may not set the strongest judicial precedent. The application of law could change with clearer evidence of commercial harm or a more direct use of content.
Moreover, the ruling does not address whether authors or publishers should have the right to opt out of AI model training, a concern that is gaining momentum globally.
Implications for India
The case highlights a glaring gap in India’s copyright regime: it is outdated. Since most AI companies are located in the U.S., courts have had the opportunity to examine copyright in the context of AI-generated content. India has yet to start. Recently, news agency ANI filed a case alleging copyright infringement against OpenAI for training on its copyrighted material. However, the case is only at an interim stage. The final outcome of the case will have a significant impact on the legality of these language models being able to use copyrighted material for training.
Considering that India aims to develop “state-of-the-art foundational AI models trained on Indian datasets” under the IndiaAI Mission, the lack of clear legal guidance on what constitutes fair dealing when using copyrighted material for AI training is a significant gap.
Thus, key points of consideration for policymakers include:
- Need for Fair Dealing Clarity: India’s fair-dealing provisions under the Copyright Act, 1957, are narrower than U.S. fair use. The doctrine may have to be reviewed to strike a balance between this law and the requirement of diverse datasets to develop foundational models rooted in Indian contexts. A parallel concern regarding data privacy also arises.
- Push for Opt-Out or Licensing Mechanisms: India should consider whether to introduce a framework that requires companies to license training data or provide an opt-out system for creators, especially given the volume of Indian content being scraped by global AI systems.
- Digital Public Infrastructure for AI: India’s policymakers could take this opportunity to invest in public datasets, especially in regional languages, that are both high quality and legally safe for AI training.
- Protecting Local Creators: India needs to ensure that its authors, filmmakers, educators and journalists are protected from having their work repurposed without compensation, since power asymmetries between Big Tech and local creators can lead to exploitation of the latter.
Conclusion
The ruling in Meta’s favour is just one win for the developer. The real questions about consent, compensation and creative control remain unanswered. Meanwhile, the lesson for India is urgent: it needs AI policies that balance innovation with creator rights and provide legal certainty and ethical safeguards as it accelerates its AI ecosystem. Further, as global tech firms race ahead, India must not remain a passive data source; it must set the terms of its digital future. This will help the country move a step closer to achieving its goal of building sovereign AI capacity and becoming a hub for digital innovation.
References
- https://www.theguardian.com/technology/2025/jun/26/meta-wins-ai-copyright-lawsuit-as-us-judge-rules-against-authors
- https://www.wired.com/story/meta-scores-victory-ai-copyright-case/
- https://www.cnbc.com/2025/06/25/meta-llama-ai-copyright-ruling.html
- https://www.mondaq.com/india/copyright/1348352/what-is-fair-use-of-copyright-doctrine
- https://www.pib.gov.in/PressReleasePage.aspx?PRID=2113095#:~:text=One%20of%20the%20key%20pillars,models%20trained%20on%20Indian%20datasets.
- https://www.ndtvprofit.com/law-and-policy/ani-vs-openai-delhi-high-court-seeks-responses-on-copyright-infringement-charges-against-chatgpt

Introduction
Apple launched Passkeys with iOS 16 as a more authentic and secure mechanism. It is safer than passwords, and it is more efficient in comparison to passwords. Apple users using iOS 16 passkeys features should enable two-factor authentication. The passkeys are an unchallenging mechanism than the passwords for the passkeys. The user just has to open the apps and websites, and then the biometric sensor automatically recognises the face and fingerprints. There can be a PIN and pattern used to log instead of passwords. The passkeys add an extra coating of protection to the user’s systems against cyber threats like phishing attacks by SMS and one-time password-based. In a report 9 to 5mac, there is confirmation that 95% of users are using passkeys. Also, with the passkeys, users’ experience will be better, and it is a more security-proof mechanism. The passwords were weak, reused credentials and credentials leaked, and the chances of phishing attacks were real.
What are passkeys?
Passkey is a digital key linked to users’ accounts and websites or applications. Passkeys allow the user to log into any application and website without entering passwords, usernames, or other details. The aim of this new feature is to replace the old long pattern of entering passwords for going through any websites and applications.
The passkeys are developed by Microsoft, Apple, and Google together, and it is also called FIDO Authentication (Fast identity online). It eliminates the need to remember passwords and the need for typing. So, the passkeys work as they replace the password with a unique digital key, which is tied to the account then, the key is stored in the device itself, and it is end-to-end encrypted. The passkeys will always be on the sites on which users specifically created them. the passkeys use the technology of cryptography for more security purposes. And the passkeys guarantee against the phish.
And since the passkeys follow FIDO standards so, this also can be used for third-party nonapple devices as the third-party device generate a QR code that enables the iOS user to scan that to log in. It will recognise the face of the person for authentication and then asks for permission on another device to deny or allow.
How are passkeys more secure than passwords?
The passkeys follow the public key cryptographic protocols that support the security keys, and they work against phishing and other cyber threats. It is more secure than SMS and apps based on one-time passwords. And another type of multi-factor authentication.
Why are passwords insecure?
The users create passwords easily, and it is wondering if they are secure. The very important passwords are short and easy to crack as they generally relate to the user’s personal information or popular words. One password is reused by the user to the different accounts, and then, in this case, hacking one account gives access to all accounts to the hackers. The problem is that passwords have inherent flaws, like they could be easily stolen.
Are passkeys about to become obligatory?
Many websites restrict the type of passwords, as some websites ask for mixtures of numbers and symbols, and many websites ask for two-factor authentication. There is no surety about the obligation of passkeys widespread as it is still a new concept and it will take time, so it is going to be optional for a while.
- There was a case of a Heartland payment system data breach, and Heartland was handling over 100 million monthly credit card transactions for 175,000 retailers at the time of the incident. Visa and MasterCard detected the hack in January 2009 when they notified Heartland of suspicious transactions. And this happened due to a password breach. The corporation paid an estimated $145 million in settlement for illegal payments. Today, data-driven breaches affect millions of people’s personal information.
- GoDaddy reported a security attack in November that affected the accounts of over a million of its WordPress customers. The attacker acquired unauthorised access to GoDaddy’s Managed WordPress hosting environment by hacking into the provisioning system in the company’s legacy Managed WordPress code.
Conclusion
The use of strong and unique passwords is an essential requirement to safeguard information and data from cyberattacks, but still, passwords have its own disadvantages. And by the replacement of passwords, a passkey, a digital key that ensures proper safety and there is security against cyberattacks and cybercrimes through passkey. There are cases above-mentioned that happened due to the password’s weaker security. And in this technology world, there is a need for something for protection and prevention from cybercrimes, and the world dumps passwords and adopts passkeys.
References
- https://www.cnet.com/tech/mobile/switch-to-passkeys-more-secure-than-passwords-on-ios-16-iphone-14/
- https://economictimes.indiatimes.com/magazines/panache/google-is-ending-passwords-rolls-out-passkeys-for-easy-log-in-how-to-set-it/articleshow/99988444.cms?from=mdr
- https://security.googleblog.com/2023/05/making-authentication-faster-than-ever.html#:~:text=Because%20they%20are%20based%20on,%2Dfactor%20authentication%20(MFA).
.webp)
Introduction
Cyber slavery has emerged as a serious menace. Offenders target innocent individuals, luring them with false promises of employment, only to capture them and subject them to horrific torture and forced labour. According to reports, hundreds of Indians have been imprisoned in 'Cyber Slavery' in certain Southeast Asian countries. Indians who have travelled to South Asian nations such as Cambodia in the hopes of finding work and establishing themselves have fallen victim to the illusion of internet slavery. According to reports, 30,000 Indians who travelled to this region on tourist visas between 2022 and 2024 did not return. India Today’s coverage demonstrated how survivors of cyber slavery who have somehow escaped and returned to India have talked about the terrifying experiences they had while being coerced into engaging in cyber slavery.
Tricked by a Job Offer, Trapped in Cyber Slavery
India Today aired testimonials of cyber slavery victims who described how they were trapped. One individual shared that he had applied for a well-paying job as an electrician in Cambodia through an agent in Delhi. However, upon arriving in Cambodia, he was offered a job with a Chinese company where he was forced to participate in cyber scam operations and online fraudulent activities.
He revealed that a personal system and mobile phone were provided, and they were compelled to cheat Indian individuals using these devices and commit cyber fraud. They were forced to work 12-hour shifts. After working there for several months, he repeatedly requested his agent to help him escape. In response, the Chinese group violently loaded him into a truck, assaulted him, and left him for dead on the side of the road. Despite this, he managed to survive. He contacted locals and eventually got in touch with his brother in India, and somehow, he managed to return home.
This case highlights how cyber-criminal groups deceive innocent individuals with the false promise of employment and then coerce them into committing cyber fraud against their own country. According to the Ministry of Home Affairs' Indian Cyber Crime Coordination Center (I4C), there has been a significant rise in cybercrimes targeting Indians, with approximately 45% of these cases originating from Southeast Asia.
CyberPeace Recommendations
Cyber slavery has developed as a serious problem, beginning with digital deception and progressing to physical torture and violent actions to commit fraudulent online acts. It is a serious issue that also violates human rights. The government has already taken note of the situation, and the Indian Cyber Crime Coordination Centre (I4C) is taking proactive steps to address it. It is important for netizens to exercise due care and caution, as awareness is the first line of defence. By remaining vigilant, they can oppose and detect the digital deceit of phony job opportunities in foreign nations and the manipulative techniques of scammers. Netizens can protect themselves from significant threats that could harm their lives by staying watchful and double-checking information from reliable sources.
References
- CyberPeace Highlights Cyber Slavery: A Serious Concern https://www.cyberpeace.org/resources/blogs/cyber-slavery-a-serious-concern
- https://www.indiatoday.in/india/story/india-today-operation-cyber-slaves-stories-of-golden-triangle-network-of-fake-job-offers-2642498-2024-11-29
- https://www.indiatoday.in/india/video/cyber-slavery-survivors-narrate-harrowing-accounts-of-torture-2642540-2024-11-29?utm_source=washare


