Cyber Threats
Executive Summary:
New Linux malware has been discovered by a cybersecurity firm Volexity, and this new strain of malware is being referred to as DISGOMOJI. A Pakistan-based threat actor alias ‘UTA0137’ has been identified as having espionage aims, with its primary focus on Indian government entities. Like other common forms of backdoors and botnets involved in different types of cyberattacks, DISGOMOJI, the malware allows the use of commands to capture screenshots, search for files to steal, spread additional payloads, and transfer files. DISGOMOJI uses Discord (messaging service) for Command & Control (C2) and uses emojis for C2 communication. This malware targets Linux operating systems.
The DISCOMOJI Malware:
- The DISGOMOJI malware opens a specific channel in a Discord server and every new channel corresponds to a new victim. This means that the attacker can communicate with the victim one at a time.
- This particular malware connects with the attacker-controlled Discord server using Emoji, a form of relay protocol. The attacker provides unique emojis as instructions, and the malware uses emojis as a feedback to the subsequent command status.
- For instance, the ‘camera with flash’ emoji is used to screenshots the device of the victim or to steal, the ‘fox’ emoji cracks all Firefox profiles, and the ‘skull’ emoji kills the malware process.
- This C2 communication is done using emojis to ensure messaging between infected contacts, and it is almost impossible for Discord to shut down the malware as it can always change the account details of Discord it is using once the maliciou server is blocked.
- The malware also has capabilities aside from the emoji-based C2 such as network probing, tunneling, and data theft that are needed to help the UTA0137 threat actor in achieving its espionage goals.
Specific emojis used for different commands by UTA0137:
- Camera with Flash (📸): Captures a picture of the target device’s screen as per the victim’s directions.
- Backhand Index Pointing Down (👇): Extracts files from the targeted device and sends them to the command channel in the form of attachments.
- Backhand Index Pointing Right (👉): This process involves sending a file found on the victim’s device to another web-hosted file storage service known as Oshi or oshi[. ]at.
- Backhand Index Pointing Left (👈): Sends a file from the victim’s device to transfer[. ]sh, which is an online service for sharing files on the Internet.
- Fire (🔥): Finds and transmits all files with certain extensions that exist on the victim’s device, such as *. txt, *. doc, *. xls, *. pdf, *. ppt, *. rtf, *. log, *. cfg, *. dat, *. db, *. mdb, *. odb, *. sql, *. json, *. xml, *. php, *. asp, *. pl, *. sh, *. py, *. ino, *. cpp, *. java,
- Fox (🦊): This works by compressing all Firefox related profiles in the affected device.
- Skull (💀): Kills the malware process in windows using ‘os. Exit()’
- Man Running (🏃♂️): Execute a command on a victim’s device. This command receives an argument, which is the command to execute.
- Index Pointing up (👆) : Upload a file to the victim's device. The file to upload is attached along with this emoji
Analysis:
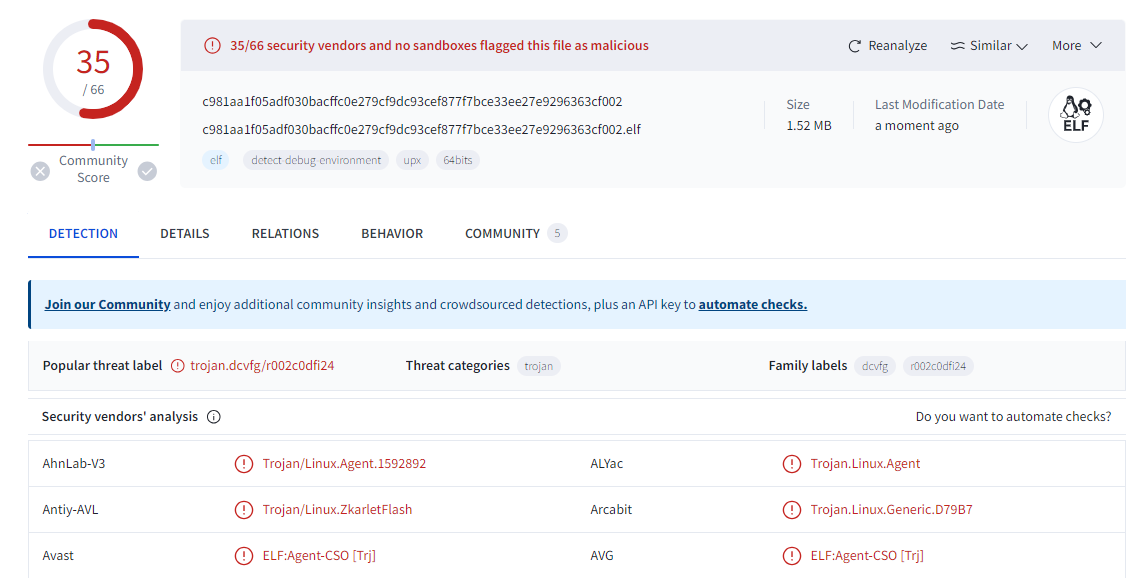
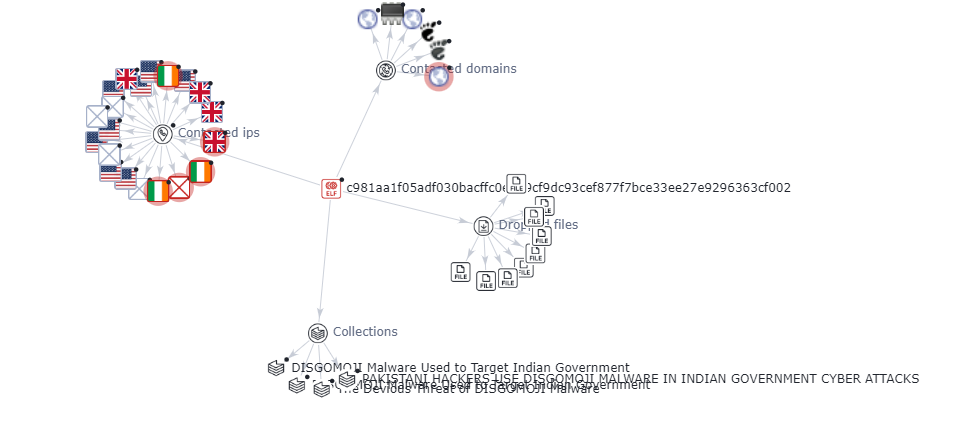
The analysis was carried out for one of the indicator of compromised SHA-256 hash file- C981aa1f05adf030bacffc0e279cf9dc93cef877f7bce33ee27e9296363cf002.
It is found that most of the vendors have marked the file as trojan in virustotal and the graph explains the malicious nature of the contacted domains and IPs.
Discord & C2 Communication for UTA0137:
- Stealthiness: Discord is a well-known messaging platform used for different purposes, which means that sending any messages or files on the server should not attract suspicion. Such stealthiness makes it possible for UTA0137 to remain dormant for greater periods before launching an attack.
- Customization: UTA0137 connected to Discord is able to create specific channels for distinct victims on the server. Such a framework allows the attackers to communicate with each of the victims individually to make a process more accurate and efficient.
- Emoji-based protocol: For C2 communication, emojis really complicates the attempt that Discord might make to interfere with the operations of the malware. In case the malicious server gets banned, malware could easily be recovered, especially by using the Discord credentials from the C2 server.
- Persistence: The malware, as stated above, has the ability to perpetually exist to hack the system and withstand rebooting of systems so that the virus can continue to operate without being detected by the owner of the hacked system.
- Advanced capabilities: Other features of DISGOMOJI are the Network Map using Nmap scanner, network tunneling through Chisel and Ligolo and Data Exfiltration by File Sharing services. These capabilities thus help in aiding the espionage goals of UTA0137.
- Social engineering: The virus and the trojan can show the pop-up windows and prompt messages, for example the fake update for firefox and similar applications, where the user can be tricked into inputting the password.
- Dynamic credential fetching: The malware does not write the hardcoded values of the credentials in order to connect it to the discord server. This also inconveniences analysts as they are unable to easily locate the position of the C2 server.
- Bogus informational and error messages: They never show any real information or errors because they do not want one to decipher the malicious behavior easily.
Recommendations to mitigate the risk of UTA0137:
- Regularly Update Software and Firmware: It is essential to regularly update all the application software and firmware of different devices, particularly, routers, to prevent hackers from exploiting the discovered and disclosed flaws. This includes fixing bugs such as CVE-2024-3080 and CVE-2024-3912 on ASUS routers, which basically entails solving a set of problems.
- Implement Multi-Factor Authentication: There are statistics that show how often user accounts are attacked, it is important to incorporate multi-factor authentication to further secure the accounts.
- Deploy Advanced Malware Protection: Provide robust guard that will help the user recognize and prevent the execution of the DISGOMOJI malware and similar threats.
- Enhance Network Segmentation: Utilize stringent network isolation mechanisms that seek to compartmentalize the key systems and data from the rest of the network in order to minimize the attack exposure.
- Monitor Network Activity: Scanning Network hour to hour for identifying and handling the security breach and the tools such as Nmap, Chisel, Ligolo etc can be used.
- Utilize Threat Intelligence: To leverage advanced threats intelligence which will help you acquire knowledge on previous threats and vulnerabilities and take informed actions.
- Secure Communication Channels: Mitigate the problem of the leakage of developers’ credentials and ways of engaging with the discord through loss of contact to prevent abusing attacks or gaining control over Discord as an attack vector.
- Enforce Access Control: Regularly review and update the user authentication processes by adopting stricter access control measures that will allow only the right personnel to access the right systems and information.
- Conduct Regular Security Audits: It is important to engage in security audits periodically in an effort to check some of the weaknesses present within the network or systems.
- Implement Incident Response Plan: Conduct a risk assessment, based on that design and establish an efficient incident response kit that helps in the early identification, isolation, and management of security breaches.
- Educate Users: Educate users on cybersecurity hygiene, opportunities to strengthen affinity with the University, and conduct retraining on threats like phishing and social engineering.
Conclusion:
The new threat actor named UTA0137 from Pakistan who was utilizing DISGOMOJI malware to attack Indian government institutions using embedded emojis with a command line through the Discord app was discovered by Volexity. It has the capability to exfiltrate and aims to steal the data of government entities. The UTA0137 was continuously improved over time to permanently communicate with victims. It underlines the necessity of having strong protection from viruses and hacker attacks, using secure passwords and unique codes every time, updating the software more often and having high-level anti-malware tools. Organizations can minimize advanced threats, the likes of DISGOMOJI and protect sensitive data by improving network segmentation, continuous monitoring of activities, and users’ awareness.
References:
https://otx.alienvault.com/pulse/66712446e23b1d14e4f293eb
https://thehackernews.com/2024/06/pakistani-hackers-use-disgomoji-malware.html?m=1
https://cybernews.com/news/hackers-using-emojis-to-command-malware/
https://www.volexity.com/blog/2024/06/13/disgomoji-malware-used-to-target-indian-government/

Introduction
The ‘Barbie’ fever is going high in India, and it’s hype to launch online scams in India. The cybercriminals attacking the ‘Barbie’ fans in India, as the popular malware and antivirus protection MacAfee has recently reported that India is in the top 3rd number among countries facing major malware attacks. After the release of ‘barbie’ in theatres, the Scams started spreading across India through the free download of the ‘Barbie’ movie from the link and other viruses. The scammers trick the victims by selling free ‘Barbie’ tickets and, after the movie’s hit, search for the free download links on websites which leads to the Scams.
What is the ‘Barbie’ malware?
After the release of the ‘Barbie’ movie, trying to keep up with the trend, Barbie fans started to search the links for free movie downloads from anonymous sources. And after downloading the movie, there was malware in the downloaded zip files. The online scam includes not genuine dubbed downloads of the movie that install malware, barbie-related viruses, and fake videos that point to free tickets, and also clicking on unverified links for the movie access resulted in Scam. It is important not to get stuck in these trends just because to keep up with them, as it could land you in trouble.
Case: As per the report of McAfee, several cases of malware trick victims into downloading the ‘ Barbie’ movie in different languages. By clicking the link, it prompts the user to download a Zip file, which is packed with malware
Countries-wise malware distribution
Cyber Scams witnessed a significant surge in just a few weeks, with hundreds of incidents of new malware cases. And The USA is on the top No. Among all the countries, In the USA there was 37 % of ‘Barbie’ malware attacks held per the, while Australia, the UK, and India suffered 6 % of malware attacks. And other countries like Japan, Ireland, and France faced 3% of Malware attacks.
What are the precautions?
Cyber scams are evolving everywhere, users must remain vigilant and take necessary precautions to protect their personal information. The user shall avoid clicking on suspicious links, also those which are related to unauthorised movie downloads or fake ticket offers. The people shall use legitimate and official platforms to access movie-related content. Keeping anti-malware and antivirus will add an extra layer of protection.
Here are some following precautions against Malware:
- Use security software.
- Use strong passwords and authentication.
- Enforce safe browsing and email.
- Data backup.
- Implement Anti-lateral Movement.
Conclusion
Cyberspace is evolving, and with that, Scams are also evolving. With the new trend of ‘Barbie’ Scams going on the rise everywhere, India is on top 3rd No. In India, McAfee reported several malicious attacks that attempted to trick the victims into downloading the free version of ‘Barbie’ movie in dubbed languages. This resulted in a Scam. People usually try to keep up with trends that land them in trouble. The users shall beware of these kinds of cyber-attacks. These scams result in huge losses. Technology should be used with proper precautions as per the incidents happening around.

Introduction
A famous quote, “Half knowledge is always dangerous”, but “Too much knowledge of anything can lead to destruction”. Recently very infamous spyware and malware named WyrmSpy and Dragon Egg were invented by a Chinese group of hackers APT41. The APT41 is a state-endorsed Clandstein active group based in the People’s Republic of China that has been active since 2012. In contrast to numerous countries-government supported, APT has a footprint record jeopardising both government organisations for clandestine activities as well as different private organisations or enterprises for their financial gain. APT41 group aims at Android devices through spyware wyrmspy and dragon egg, which masquerades as a legitimate application. According to the U.S. jury legal accusation from 2019 to 2020, the group was entangled in threatening over more than 100 public and private individuals and organisations in the United States and around the world.Moreover, a detailed analysis report was shared by the Lookout Threat Researchers, that has been actively monitoring and tracking both spyware and malware.
Briefing about how spyware attacks on Android devices take place
To begin with, this malware imitates a real source Android application to show some sort of notification. Once it is successfully installed on the user’s machine, proclaims multiple device’s permission to enable data filtration.
Wyrmspy complies with log files, photos, device locations, SMS(read and write), and audio recordings. It has also authenticated that there are no detection malware activities found on google play even after running multiple security levels. These malicious things are made with the intent to obtain rooting access privileges to the device and monitor activities to the specified commands received from the C2 servers.
Similarly, Dragon Egg can collect data files, contacts, locations, and audio recordings, and it also accesses camera photos once it successfully trade-off the device. Dragon egg receives a payload that is also known as “smallmload.jar”, which is either from APK(Android Packet Kit).
WyrmSpy initially masquerades as a default operation system application, and Dragon Egg simulates a third-party keyboard/ messaging application.
Overview of APT41 Chinese group background
APT41 is a Chinese-based stealth activity-carrying group that is said to be active since mid-2006. Rumours about APT41 that it was also a part of the 2nd Bureau of the People’s Liberation Army (PLA) General Staff Department’s (GSD) 3rd Department. Owning to that fact, 2006 has seen 140+ organisations’ security getting compromised, ranging from 20 strategically crucial companies.APT is also recognised for rationally plundering hundreds of terabytes of data from at least 141 organisations between 2006 and 2013. It typically begins with spear-phishing emails to the targeted victims. These sent emails contain official templates along with language pretending to be from a legitimate real source, carrying a malicious attachment. As the victim opens the attached file, the backdoor bestows the control of the targeted machine to the APT groups machine. Once there is an unauthorised gain of access, the attacker visits and revisits the victim’s machine. The group remains dormant for lengthy durations, more likely for months or even for years.
Advisory points need to adhere to while using Android devices
- The security patch update is necessary at least once a week
- Clearing up unwanted junk files.
- Cache files of every frequently used application need to clear out.
- Install only required applications from
Google play store. - Download only necessary APK files only it comes from trusted resources.
- Before giving device permission, it is advisable to run your files or URLs on VirusTotal.com this website will give a good closure to the malicious intent.
- Install good antivirus software.
- Individuals need to check the source of the email before opening an attachment to it.
- Never collect or add any randomly found device to your system
- Moreover, the user needs to keep track of their device activity. Rather than using devices just for entertainment purposes, it is more important to look for data protection on that device.
Conclusion
Network Crack Program Hacker Group (NCPH), which grew as an APT41 group with malicious intent, earlier performed the role of grey hat hacker, this group somehow grew up greedy to enhance more money laundering by hacking networks, devices, etc. As this group conducts a supply chain of attacks to gain unauthorised access to the network throughout the world, targeting hundreds of companies, including an extensive selection of industries such as social media, telecommunications, government, defence, education, and manufacturing. Last but not least, many more fraud-making groups with malicious intent will be forming and implementing in the future. It is on individuals and organisations to secure themselves but practise basic security levels to safeguard themselves against such threats and attacks.

Pretext
The Army Welfare Education Society has informed the Parents and students that a Scam is targeting the Army schools Students. The Scamster approaches the students by faking the voice of a female and a male. The scamster asks for the personal information and photos of the students by telling them they are taking details for the event, which is being organised by the Army welfare education society for the celebration of independence day. The Army welfare education society intimated that Parents to beware of these calls from scammers.
The students of Army Schools of Jammu & Kashmir, Noida, are getting calls from the scamster. The students were asked to share sensitive information. Students across the country are getting calls and WhatsApp messages from two numbers, which end with 1715 and 2167. The Scamster are posing to be teachers and asking for the students’ names on the pretext of adding them to the WhatsApp Groups. The scamster then sends forms links to the WhatsApp groups and asking students to fill out the form to seek more sensitive information.
Do’s
- Do Make sure to verify the caller.
- Do block the caller while finding it suspicious.
- Do be careful while sharing personal Information.
- Do inform the School Authorities while receiving these types of calls and messages posing to be teachers.
- Do Check the legitimacy of any agency and organisation while telling the details
- Do Record Calls asking for personal information.
- Do inform parents about scam calling.
- Do cross-check the caller and ask for crucial information.
- Do make others aware of the scam.
Don’ts
- Don’t answer anonymous calls or unknown calls from anyone.
- Don’t share personal information with anyone.
- Don’t Share OTP with anyone.
- Don’t open suspicious links.
- Don’t fill any forms, asking for personal information
- Don’t confirm your identity until you know the caller.
- Don’t Reply to messages asking for financial information.
- Don’t go to a fake website by following a prompt call.
- Don’t share bank Details and passwords.
- Don’t Make payment over a prompt fake call.

Introduction
Discussions took place focused on cybersecurity measures, specifically addressing cybercrime in the context of emerging technologies such as Non-Fungible Tokens (NFTs), Artificial Intelligence (AI), and the Metaverse. Session 5 of the conference focused on the interconnectedness between the darknet and cryptocurrency and the challenges it poses for law enforcement agencies and regulators. They discussed that Understanding AI is necessary for enterprises. AI models have difficulties, but we are looking forward to trustworthy AIs. and AI technology must be transparent.
Darknet and Cryptocurrency
The darknet refers to the hidden part of the internet where illicit activities have proliferated in recent years. It was initially developed to provide anonymity, privacy, and protection to specific individuals such as journalists, activists, and whistleblowers. However, it has now become a playground for criminal activities. Cryptocurrency, particularly Bitcoin, has been widely adopted on the darknet due to its anonymous nature, enabling anti-money laundering and unlawful transactions.
Three major points emerge from this relationship: the integrated nature of the darknet and cryptocurrency, the need for regulations to prevent darknet-based crimes, and the importance of striking a balance between privacy and security.
Key Challenges:
- Integrated Relations: The darknet and cryptocurrency have evolved independently, with different motives and purposes. It is crucial to understand the integrated relationship between them and how criminals exploit this connection.
- Regulatory Frameworks: There is a need for effective regulations to prevent crimes facilitated through the darknet and cryptocurrency while striking a balance between privacy and security.
- Privacy and Security: Privacy is a fundamental right, and any measures taken to enhance security should not infringe upon individual privacy. A multistakeholder approach involving tech companies and regulators is necessary to find this delicate balance.
Challenges Associated with Cryptocurrency Use:
The use of cryptocurrency on the darknet poses several challenges. The risks associated with darknet-based cryptocurrency crimes are a significant concern. Additionally, regulatory challenges arise due to the decentralised and borderless nature of cryptocurrencies. Mitigating these challenges requires innovative approaches utilising emerging technologies.
Preventing Misuse of Technologies:
The discussion emphasised that we can step ahead of the people who wish to use these beautiful technologies meant and developed for a different purpose, to prevent from using them for crime.
Monitoring the Darknet:
The darknet, as explained, is an elusive part of the internet that necessitates the use of a special browser for access. Initially designed for secure communication by the US government, its purpose has drastically changed over time. The darknet’s evolution has given rise to significant challenges for law enforcement agencies striving to monitor its activities.
Around 95% of the activities carried out on the dark net are associated with criminal acts. Estimates suggest that over 50% of the global cybercrime revenue originates from the dark net. This implies that approximately half of all cybercrimes are facilitated through the darknet.
The exploitation of the darknet has raised concerns regarding the need for effective regulation. Monitoring the darknet is crucial for law enforcement, national agencies, and cybersecurity companies. The challenges associated with the darknet’s exploitation and the criminal activities facilitated by cryptocurrency emphasise the pressing need for regulations to ensure a secure digital landscape.
Use of Cryptocurrency on the Darknet
Cryptocurrency plays a central role in the activities taking place on the darknet. The discussion highlighted its involvement in various illicit practices, including ransomware attacks, terrorist financing, extortion, theft, and the operation of darknet marketplaces. These applications leverage cryptocurrency’s anonymous features to enable illegal transactions and maintain anonymity.
AI's Role in De-Anonymizing the Darknet and Monitoring Challenges:
- 1.AI’s Potential in De-Anonymizing the Darknet
During the discussion, it was highlighted how AI could be utilised to help in de-anonymizing the darknet. AI’s pattern recognition capabilities can aid in identifying and analysing patterns of behaviour within the darknet, enabling law enforcement agencies and cybersecurity experts to gain insights into its operations. However, there are limitations to what AI can accomplish in this context. AI cannot break encryption or directly associate patterns with specific users, but it can assist in identifying illegal marketplaces and facilitating their takedown. The dynamic nature of the darknet, with new marketplaces quickly emerging, adds further complexity to monitoring efforts.
- 2.Challenges in Darknet Monitoring
Monitoring the darknet poses various challenges due to its vast amount of data, anonymous and encrypted nature, dynamically evolving landscape, and the need for specialised access. These challenges make it difficult for law enforcement agencies and cybersecurity professionals to effectively track and prevent illicit activities.
- 3.Possible Ways Forward
To address the challenges, several potential avenues were discussed. Ethical considerations, striking a balance between privacy and security, must be taken into account. Cross-border collaboration, involving the development of relevant laws and policies, can enhance efforts to combat darknet-related crimes. Additionally, education and awareness initiatives, driven by collaboration among law enforcement, government entities, and academia, can play a crucial role in combating darknet activities.
The panel also addressed the questions from the audience
- How law enforcement agencies and regulators can use AI to detect and prevent crimes on the darknet and cryptocurrency? The panel answered that- Law enforcement officers should also be AI and technology ready, and that kind of upskilling program should be there in place.
- How should lawyers and the judiciary understand the problem and regulate it? The panel answered that AI should only be applied by looking at the outcomes. And Law has to be clear as to what is acceptable and what is not.
- Aligning AI with human intention? Whether it’s possible? Whether can we create an ethical AI instead of talking about using AI ethically? The panel answered that we have to understand how to behave ethically. AI can beat any human. We have to learn AI. Step one is to focus on our ethical behaviour. And step two is bringing the ethical aspect to the software and technologies. Aligning AI with human intention and creating ethical AI is a challenge. The focus should be on ethical behaviour both in humans and in the development of AI technologies.
Conclusion
The G20 Conference on Crime and Security shed light on the intertwined relationship between the darknet and cryptocurrency and the challenges it presents to cybersecurity. The discussions emphasised the need for effective regulations, privacy-security balance, AI integration, and cross-border collaboration to tackle the rising cybercrime activities associated with the darknet and cryptocurrency. Addressing these challenges will require the combined efforts of governments, law enforcement agencies, technology companies, and individuals committed to building a safer digital landscape.

Introduction
According to a shocking report, there are multiple scam loan apps on the App Store in India that charge excessive interest rates and force users to pay by blackmailing and harassing them. Apple has prohibited and removed these apps from the App Store, but they may still be installed on your iPhone and running. You must delete any of these apps if you have downloaded them. Learn the names of these apps and how they operated the fraud.
Why Apple banned these apps?
- Apple has taken action to remove certain apps from the Indian App Store. These apps were engaging in unethical behaviour, such as impersonating financial institutions, demanding high fees, and threatening borrowers. Here are the titles of these apps, as well as what Apple has said about their suspension.
- Following user concerns, Apple removed six loan apps from the Indian App Store. Loan apps include White Kash, Pocket Kash, Golden Kash, Ok Rupee, and others.
- According to multiple user reviews, certain apps seek unjustified access to users’ contact lists and media. These apps also charge exorbitant fees that are not necessitated. Furthermore, companies have been found to engage in unethical tactics such as charging high-interest rates and “processing fees” equal to half the loan amount.
- Some lending app users have reported being harassed and threatened for failing to return their loans on time. In some circumstances, the apps threatened the user’s contacts if payment was not completed by the deadline. According to one user, the app company threatened to produce and send false photographs of her to her contacts.
- These loan apps were removed from the App Store, according to Apple, because they broke the norms and standards of the Apple Developer Program License Agreement. These apps were discovered to be falsely claiming financial institution connections.
Issue of Fake loan apps on the App Store
- The App Store and our App Review Guidelines are designed to ensure we provide our users with the safest experience possible,” Apple explained. “We do not tolerate fraudulent activity on the App Store and have strict rules against apps and developers who attempt to game the system.
- In 2022, Apple blocked nearly $2 billion in fraudulent App Store sales. Furthermore, it rejected nearly 1.7 million software submissions that did not match Apple’s quality and safety criteria and cancelled 428,000 developer accounts due to suspected fraudulent activities.
- The scammers also used heinous tactics to force the loanees to pay. According to reports, the scammers behind the apps gained access to the user’s contact list as well as their images. They would morph the images and then scare the individual by sharing their fake nude photos with their whole contact list.
Dangerous financial fraud apps have surfaced on the App Store
- TechCrunch acquired a user review from one of these apps. “I borrowed an amount in a helpless situation, and a day before the repayment due date, I got some messages with my picture and my contacts in my phone saying that repay your loan or they will inform our contacts that you are not paying the loan,” it said.
- Sandhya Ramesh, a journalist from The Print, recently tweeted a screenshot of a direct message she got. A victim’s friend told a similar story in the message.
- TechCrunch contacted Apple, who confirmed that the apps had been removed from the App Store for breaking the Apple Developer Program License Agreement and guidelines.
Conclusion
Recently, some users have claimed that some quick-loan applications, such as White Kash, Pocket Kash, and Golden Kash, have appeared on the Top Finance applications chart in recent days. These apps necessitate unauthorised and intrusive access to users’ contact lists and media. According to hundreds of user evaluations, these apps charged exorbitantly high and useless fees. They used unscrupulous techniques such as demanding “processing fees” equal to half the loan amount and charging high-interest rates. Users were also harassed and threatened with restitution. If payments were not made by the due date, the lending applications threatened to notify users’ contacts. According to one user, the app provider even threatened to generate phoney nude images of her and send them to her contacts.

Introduction
In a distressing incident that highlights the growing threat of cyber fraud, a software engineer in Bangalore fell victim to fraudsters who posed as police officials. These miscreants, operating under the guise of a fake courier service and law enforcement, employed a sophisticated scam to dupe unsuspecting individuals out of their hard-earned money. Unfortunately, this is not an isolated incident, as several cases of similar fraud have been reported recently in Bangalore and other cities. It is crucial for everyone to be aware of these scams and adopt preventive measures to protect themselves.
Bangalore Techie Falls Victim to ₹33 Lakh
The software engineer received a call from someone claiming to be from FedEx courier service, informing him that a parcel sent in his name to Taiwan had been seized by the Mumbai police for containing illegal items. The call was then transferred to an impersonator posing as a Mumbai Deputy Commissioner of Police (DCP), who alleged that a money laundering case had been registered against him. The fraudsters then coerced him into joining a Skype call for verification purposes, during which they obtained his personal details, including bank account information.
Under the guise of verifying his credentials, the fraudsters manipulated him into transferring a significant amount of money to various accounts. They assured him that the funds would be returned after the completion of the procedure. However, once the money was transferred, the fraudsters disappeared, leaving the victim devastated and financially drained.
Best Practices to Stay Safe
- Be vigilant and skeptical: Maintain a healthy level of skepticism when receiving unsolicited calls or messages, especially if they involve sensitive information or financial matters. Be cautious of callers pressuring you to disclose personal details or engage in immediate financial transactions.
- Verify the caller’s authenticity: If someone claims to represent a legitimate organisation or law enforcement agency, independently verify their credentials. Look up the official contact details of the organization or agency and reach out to them directly to confirm the authenticity of the communication.
- Never share sensitive information: Avoid sharing personal information, such as bank account details, passwords, or Aadhaar numbers, over the phone or through unfamiliar online platforms. Legitimate organizations will not ask for such information without proper authentication protocols.
- Use secure communication channels: When communicating sensitive information, prefer secure platforms or official channels that provide end-to-end encryption. Avoid switching to alternative platforms or applications suggested by unknown callers, as fraudsters can exploit these.
- Educate yourself and others: Stay informed about the latest cyber fraud techniques and scams prevalent in your region. Share this knowledge with family, friends, and colleagues to create awareness and prevent them from falling victim to similar schemes.
- Implement robust security measures: Keep your devices and software updated with the latest security patches. Utilize robust anti-virus software, firewalls, and spam filters to safeguard against malicious activities. Regularly review your financial statements and account activity to detect any unauthorized transactions promptly.
Conclusion:
The incident involving the Bangalore techie and other victims of cyber fraud highlights the importance of remaining vigilant and adopting preventive measures to safeguard oneself from such scams. It is disheartening to see individuals falling prey to impersonators who exploit their trust and manipulate them into sharing sensitive information. By staying informed, exercising caution, and following best practices, we can collectively minimize the risk and protect ourselves from these fraudulent activities. Remember, the best defense against cyber fraud is a well-informed and alert individual.

Introduction
Deepfakes are artificial intelligence (AI) technology that employs deep learning to generate realistic-looking but phoney films or images. Algorithms use large volumes of data to analyse and discover patterns in order to provide compelling and realistic results. Deepfakes use this technology to modify movies or photos to make them appear as if they involve events or persons that never happened or existed.The procedure begins with gathering large volumes of visual and auditory data about the target individual, which is usually obtained from publicly accessible sources such as social media or public appearances. This data is then utilised for training a deep-learning model to resemble the target of deep fakes.
Recent Cases of Deepfakes-
In an unusual turn of events, a man from northern China became the victim of a sophisticated deep fake technology. This incident has heightened concerns about using artificial intelligence (AI) tools to aid financial crimes, putting authorities and the general public on high alert.
During a video conversation, a scammer successfully impersonated the victim’s close friend using AI-powered face-swapping technology. The scammer duped the unwary victim into transferring 4.3 million yuan (nearly Rs 5 crore). The fraud occurred in Baotou, China.
AI ‘deep fakes’ of innocent images fuel spike in sextortion scams
Artificial intelligence-generated “deepfakes” are fuelling sextortion frauds like a dry brush in a raging wildfire. According to the FBI, the number of nationally reported sextortion instances came to 322% between February 2022 and February 2023, with a notable spike since April due to AI-doctored photographs. And as per the FBI, innocent photographs or videos posted on social media or sent in communications can be distorted into sexually explicit, AI-generated visuals that are “true-to-life” and practically hard to distinguish. According to the FBI, predators often located in other countries use doctored AI photographs against juveniles to compel money from them or their families or to obtain actual sexually graphic images.
Deepfake Applications
- Lensa AI.
- Deepfakes Web.
- Reface.
- MyHeritage.
- DeepFaceLab.
- Deep Art.
- Face Swap Live.
- FaceApp.
Deepfake examples
There are numerous high-profile Deepfake examples available. Deepfake films include one released by actor Jordan Peele, who used actual footage of Barack Obama and his own imitation of Obama to convey a warning about Deepfake videos.
A video shows Facebook CEO Mark Zuckerberg discussing how Facebook ‘controls the future’ with stolen user data, most notably on Instagram. The original video is from a speech he delivered on Russian election meddling; only 21 seconds of that address were used to create the new version. However, the vocal impersonation fell short of Jordan Peele’s Obama and revealed the truth.
The dark side of AI-Generated Misinformation
- Misinformation generated by AI-generated the truth, making it difficult to distinguish fact from fiction.
- People can unmask AI content by looking for discrepancies and lacking the human touch.
- AI content detection technologies can detect and neutralise disinformation, preventing it from spreading.
Safeguards against Deepfakes-
Technology is not the only way to guard against Deepfake videos. Good fundamental security methods are incredibly effective for combating Deepfake.For example, incorporating automatic checks into any mechanism for disbursing payments might have prevented numerous Deepfake and related frauds. You might also:
- Regular backups safeguard your data from ransomware and allow you to restore damaged data.
- Using different, strong passwords for different accounts ensures that just because one network or service has been compromised, it does not imply that others have been compromised as well. You do not want someone to be able to access your other accounts if they get into your Facebook account.
- To secure your home network, laptop, and smartphone against cyber dangers, use a good security package such as Kaspersky Total Security. This bundle includes anti-virus software, a VPN to prevent compromised Wi-Fi connections, and webcam security.
What is the future of Deepfake –
Deepfake is constantly growing. Deepfake films were easy to spot two years ago because of the clumsy movement and the fact that the simulated figure never looked to blink. However, the most recent generation of bogus videos has evolved and adapted.
There are currently approximately 15,000 Deepfake videos available online. Some are just for fun, while others attempt to sway your opinion. But now that it only takes a day or two to make a new Deepfake, that number could rise rapidly.
Conclusion-
The distinction between authentic and fake content will undoubtedly become more challenging to identify as technology advances. As a result, experts feel it should not be up to individuals to discover deep fakes in the wild. “The responsibility should be on the developers, toolmakers, and tech companies to create invisible watermarks and signal what the source of that image is,” they stated. Several startups are also working on approaches for detecting deep fakes.

Introduction
In recent years, the city of Hyderabad/Cyberabad has emerged as a technology hub, a place with the strong presence of multi corporations, Startups, and research institutions, Hyderabad has become a hub of innovations and technological advancement. However, this growing land of cyber opportunities has also become a hub for cybercriminals as well. In this blog post, we shall explore the reasons why professionals are being targeted and the effects of cyber fraud on techies. Through this investigation, we hope to raise awareness about the seriousness of the problem as well as give vital insights and techniques for Cyberabad’s computer workers to defend themselves against cyber theft. We can work together to make Cyberabad’s technology ecosystem safer and more secure.
Defining Cyber Fraud
In today’s age, where everything has an interconnected digital world, cyber fraud cases are increasing daily. Cyber fraud encompasses a wide range of threats and techniques employed by bad actors, such as Phishing, Ransomware, identity theft, online scams, data breaches, and fake websites designed for users. The sophistication of cyber fraud techniques is constantly evolving, making it challenging for individuals and organisations to stay ahead. Cybercriminals use software vulnerabilities, social engineering tactics, and flaws in cybersecurity defences to carry out their harmful operations. Individuals and organisations must grasp these dangers and tactics to protect themselves against cyber fraud.
Impact of Cyber Frauds
The consequences of Falling victim to cyber fraud can be devastating, both personally and professionally. The emotional and financial toll on individuals may be a challenge. Identity theft may lead to damaged credit scores, fraudulent transactions, and years of recovery work to rehabilitate one’s image. Financial fraud can result in depleted bank accounts, unauthorised charges, and substantial monetary losses. Furthermore, being tricked and violated in the digital environment can generate anxiety, tension, and a lack of confidence.
The impact of cyber fraud goes beyond immediate financial losses and can have long-term consequences for individuals’ and organisations’ entire well-being and stability. As the threat environment evolves, it is critical for people and organisations to recognise the gravity of these repercussions and take proactive actions to protect themselves against cyber theft.

Why are Cyberabad Tech Professionals Targeted?
Tech professionals in Cyberabad are particularly vulnerable to cyber due to various factors. Firstly, their expertise and knowledge in technology make them attractive targets for cybercrooks. These professionals possess valuable coding, Software, and administration skills, making them attractive to cybercriminals.
Secondly, the nature of work often involves enormous use of technology, including regular internet contacts, email exchanges, and access to private information. This expanded digital presence exposes them to possible cyber dangers and makes them more vulnerable to fraudsters’ social engineering efforts. Furthermore, the fast-moving nature of the tech industry, with many deadlines and work pressure to deliver, can create a distraction. This can let them click on some malicious links or share sensitive information unknowingly all these factors let the cyber criminals exploit vulnerabilities.
Unveiling the Statistics
According to various reports, 80% of cyber fraud victims in Hyderabad are techies; the rest are the public targeted by cyber crooks. This surprising number emphasises the critical need to address the vulnerabilities and threats this specific segment within the IT community faces.
Going further into the data, we can acquire insights into the many forms of cyber fraud targeting tech workers, the strategies used by cybercriminals, and the impact these occurrences have on individuals and organisations. Examining precise features and patterns within data might give important information for developing successful preventative and protection methods.
Factors Contributing
Several reasons contribute to the elevated risk of cyber fraud among ICT professionals in Cyberabad. Understanding these aspects helps explain why this group is specifically targeted and may be more vulnerable to such assaults.
Technical Expertise: Tech workers frequently have specialised technical knowledge, but this knowledge may only sometimes extend to cybersecurity. Their primary concentration is writing software, designing systems, or implementing technologies, which may result in missing possible vulnerabilities or a lack of overall cybersecurity understanding.
Confidence in Technology: IT workers have a higher level of confidence in technology because of their knowledge and dependence on technology. This trust can sometimes make individuals more vulnerable to sophisticated frauds or social engineering approaches that prey on their faith in the services they utilise.
Time Constraints and Pressure: Tech workers frequently operate under tight deadlines and tremendous pressure to reach project milestones. This may result in hurried decision-making or disregarding possible warning signals of cyber fraud, rendering them more exposed to assaults that prey on time-sensitive circumstances.
Cybercriminals know that technology workers have valuable knowledge, trade secrets, and intellectual property that may be economically profitable. As a result, they are attractive targets for attacks aiming at stealing sensitive data or gaining unauthorised access to critical systems.
The best practices that cyber techies can apply to safeguard their personal and professional data by following these simple tips:
Strong Passwords: create a strong password, using passwords for all your online accounts and changing them regularly. Remember to use unique combinations!
MFA (Multi-Factor Authentication): Enable MFA wherever possible. This provides an extra degree of protection by requiring a second form of verification, such as a code texted to your mobile device and your password.
Use Secured WiFi: Use secure and encrypted Wi-Fi networks, especially while viewing sensitive information. Avoid connecting to public or unprotected networks, as they can be readily exploited. Recognising Red Flags and Staying Ahead
Social Engineering: Be sceptical of unwanted solicitations or offers, both online and offline. Cybercriminals may try to persuade or fool you using social engineering tactics. Before revealing any personal or private information, think critically and confirm the veracity of the request.
Secure Web Browsing: Only browse trustworthy websites with valid SSL certificates (look for “https://” in the URL). Avoid clicking on strange links or downloading files from unknown sources since they may contain malware or ransomware.
Report Suspicious actions: If you encounter any suspicious or fraudulent actions, report them to the relevant authorities, such as the Cyber Crime Police or your organisation’s IT department. Reporting events can assist in avoiding additional harm and aid in identifying and apprehending hackers.
Stay Current on Security Practises: Stay up to speed on the newest cybersecurity risks and best practices. Follow credible sources, participate in cybersecurity forums or seminars, and remain current on new threats and preventative measures.

Conclusion
The rise in cybercrimes and fraud cases among tech experts in Cyberabad is a disturbing trend that requires prompt intervention. We can establish a safer tech cluster that lives on creativity, trust, and resilience by adopting proactive actions, raising awareness, and encouraging cooperation. Let us work together to prevent cybercrime and ensure the future of Cyberabad’s IT ecosystem.
Introduction
The information of hundreds of thousands of Indians who received the COVID vaccine was Leaked in a significant data breach and posted on a Telegram channel. Numerous reports claim that sensitive information, including a person’s phone number, gender, ID card details, and date of birth, leaked over Telegram. It could be obtained by typing a person’s name into a Telegram bot.
What really happened?
The records pertaining to the mobile number registered in the CoWin portal are accessible on the Malayalam news website channel. It is also feasible to determine which vaccination was given and where it was given.
According to The Report, the list of individuals whose data was exposed includes BJP Tamil Nadu president K Annamalai, Congress MP Karti Chidambaram, and former BJP union minister for health Harsh Vardhan. Telangana’s minister of information and communication technology, Kalvakuntla Taraka Rama Rao, is also on the list.
MEITY stated in response to the data leak, “It is old data, we are still confirming it. We have requested a report on the matter.
After the media Report, the bot was disabled, but experts said the incident raised severe issues because the information might be used for identity theft, phishing emails, con games, and extortion calls. The Indian Computer Emergency Response Team (CERT-In), the government’s nodal body, has opened an investigation into the situation
The central government declared the data breach reports regarding the repository of beneficiaries against Covid to be “mischievous in nature” on Monday and claimed the ‘bot’ that purportedly accessed the confidential data was not directly accessing the CoWIN database.
According to the first complaint by CERT-In, the government’s cybersecurity division, the government claimed the bot might be displaying information from “previously stolen data.” Reports.
The health ministry refuted the claim, asserting that no bots could access the information without first verifying with a one-time password.
“It is made clear that all of these rumours are false and malicious. The health ministry’s CoWIN interface is entirely secure and has sufficient data privacy protections. The security of the data on the CoWIN portal is being ensured in every way possible, according to a statement from the health ministry.
Meity said the CoWin program or database was not directly compromised, and the shared information appeared to be taken from a previous intrusion. But the hack again highlights the growing danger of cyber assaults, particularly on official websites.

Recent cases of data leak
Dominos India 2021– Dominos India, a division of Jubilant FoodWorks, faced a cyberattack on May 22, 2021, which led to the disclosure of information from 180 million orders. The breach exposed order information, email addresses, phone numbers, and credit card information. Although Jubilant FoodWorks acknowledged a security breach, it refuted any illegal access to financial data.
Air India – A cyberattack that affected Air India in May 2021 exposed the personal information of about 4.5 million customers globally. Personal information recorded between August 26, 2011, and February 3, 2021, including names, dates of birth, contact information, passport information, ticket details, frequent flyer information from Star Alliance and Air India, and credit card information, were exposed in the breach.
Bigbasket – BigBasket, an online supermarket, had a data breach in November 2020, compromising the personal information of approximately 20 million consumers. Email IDs, password hashes, PINs, phone numbers, addresses, dates of birth, localities, and IP addresses were among the information released from an insecure database containing over 15 GB of customer data. BigBasket admitted to the incident and reported it to the Bengaluru Cyber Crime Department.
Unacademy – Unacademy, an online learning platform, experienced a data breach in May 2020, compromising the email addresses of approximately 11 million subscribers. While no sensitive information, such as financial data or passwords, was compromised, user data, including IDs, passwords, date joined, last login date, email IDs, names, and user credentials, was. The breach was detected when user accounts were uncovered for sale on the dark web.
2022 Card Data- Cybersecurity researchers from AI-driven Singapore-based CloudSEK found a threat actor offering a database of 1.2 million cards for free on a Dark Web forum for crimes on October 12, 2022. This came after a second problem involving 7.9 million cardholder records that were reported on the BidenCash website. This comprised information pertaining to State Bank of India (SBI) clients. And other well-known companies were among those targeted in high-profile data breach cases that have surfaced in recent years.

Conclusion
Data breach cases are increasing daily, and attackers are mainly attacking the healthcare sectors and health details as they can easily find personal details. This recent CoWIN case has compromised thousands of people’s data. The All-India Institute of Medical Sciences’ systems were compromised by hackers a few months ago. Over 95% of adults have had their vaccinations, according to the most recent data, even if the precise number of persons impacted by the CoWin privacy breach could not be determined.

Introduction
The advent of AI-driven deepfake technology has facilitated the creation of explicit counterfeit videos for sextortion purposes. There has been an alarming increase in the use of Artificial Intelligence to create fake explicit images or videos for sextortion.
What is AI Sextortion and Deepfake Technology
AI sextortion refers to the use of artificial intelligence (AI) technology, particularly deepfake algorithms, to create counterfeit explicit videos or images for the purpose of harassing, extorting, or blackmailing individuals. Deepfake technology utilises AI algorithms to manipulate or replace faces and bodies in videos, making them appear realistic and often indistinguishable from genuine footage. This enables malicious actors to create explicit content that falsely portrays individuals engaging in sexual activities, even if they never participated in such actions.
Background on the Alarming Increase in AI Sextortion Cases
Recently there has been a significant increase in AI sextortion cases. Advancements in AI and deepfake technology have made it easier for perpetrators to create highly convincing fake explicit videos or images. The algorithms behind these technologies have become more sophisticated, allowing for more seamless and realistic manipulations. And the accessibility of AI tools and resources has increased, with open-source software and cloud-based services readily available to anyone. This accessibility has lowered the barrier to entry, enabling individuals with malicious intent to exploit these technologies for sextortion purposes.

The proliferation of sharing content on social media
The proliferation of social media platforms and the widespread sharing of personal content online have provided perpetrators with a vast pool of potential victims’ images and videos. By utilising these readily available resources, perpetrators can create deepfake explicit content that closely resembles the victims, increasing the likelihood of success in their extortion schemes.
Furthermore, the anonymity and wide reach of the internet and social media platforms allow perpetrators to distribute manipulated content quickly and easily. They can target individuals specifically or upload the content to public forums and pornographic websites, amplifying the impact and humiliation experienced by victims.
What are law agencies doing?
The alarming increase in AI sextortion cases has prompted concern among law enforcement agencies, advocacy groups, and technology companies. This is high time to make strong Efforts to raise awareness about the risks of AI sextortion, develop detection and prevention tools, and strengthen legal frameworks to address these emerging threats to individuals’ privacy, safety, and well-being.
There is a need for Technological Solutions, which develops and deploys advanced AI-based detection tools to identify and flag AI-generated deepfake content on platforms and services. And collaboration with technology companies to integrate such solutions.
Collaboration with Social Media Platforms is also needed. Social media platforms and technology companies can reframe and enforce community guidelines and policies against disseminating AI-generated explicit content. And can ensure foster cooperation in developing robust content moderation systems and reporting mechanisms.
There is a need to strengthen the legal frameworks to address AI sextortion, including laws that specifically criminalise the creation, distribution, and possession of AI-generated explicit content. Ensure adequate penalties for offenders and provisions for cross-border cooperation.
Proactive measures to combat AI-driven sextortion
Prevention and Awareness: Proactive measures raise awareness about AI sextortion, helping individuals recognise risks and take precautions.
Early Detection and Reporting: Proactive measures employ advanced detection tools to identify AI-generated deepfake content early, enabling prompt intervention and support for victims.
Legal Frameworks and Regulations: Proactive measures strengthen legal frameworks to criminalise AI sextortion, facilitate cross-border cooperation, and impose offender penalties.
Technological Solutions: Proactive measures focus on developing tools and algorithms to detect and remove AI-generated explicit content, making it harder for perpetrators to carry out their schemes.
International Cooperation: Proactive measures foster collaboration among law enforcement agencies, governments, and technology companies to combat AI sextortion globally.
Support for Victims: Proactive measures provide comprehensive support services, including counselling and legal assistance, to help victims recover from emotional and psychological trauma.
Implementing these proactive measures will help create a safer digital environment for all.
Misuse of Technology
Misusing technology, particularly AI-driven deepfake technology, in the context of sextortion raises serious concerns.
Exploitation of Personal Data: Perpetrators exploit personal data and images available online, such as social media posts or captured video chats, to create AI- manipulation violates privacy rights and exploits the vulnerability of individuals who trust that their personal information will be used responsibly.
Facilitation of Extortion: AI sextortion often involves perpetrators demanding monetary payments, sexually themed images or videos, or other favours under the threat of releasing manipulated content to the public or to the victims’ friends and family. The realistic nature of deepfake technology increases the effectiveness of these extortion attempts, placing victims under significant emotional and financial pressure.
Amplification of Harm: Perpetrators use deepfake technology to create explicit videos or images that appear realistic, thereby increasing the potential for humiliation, harassment, and psychological trauma suffered by victims. The wide distribution of such content on social media platforms and pornographic websites can perpetuate victimisation and cause lasting damage to their reputation and well-being.
Targeting teenagers– Targeting teenagers and extortion demands in AI sextortion cases is a particularly alarming aspect of this issue. Teenagers are particularly vulnerable to AI sextortion due to their increased use of social media platforms for sharing personal information and images. Perpetrators exploit to manipulate and coerce them.
Erosion of Trust: Misusing AI-driven deepfake technology erodes trust in digital media and online interactions. As deepfake content becomes more convincing, it becomes increasingly challenging to distinguish between real and manipulated videos or images.
Proliferation of Pornographic Content: The misuse of AI technology in sextortion contributes to the proliferation of non-consensual pornography (also known as “revenge porn”) and the availability of explicit content featuring unsuspecting individuals. This perpetuates a culture of objectification, exploitation, and non-consensual sharing of intimate material.
Conclusion
Addressing the concern of AI sextortion requires a multi-faceted approach, including technological advancements in detection and prevention, legal frameworks to hold offenders accountable, awareness about the risks, and collaboration between technology companies, law enforcement agencies, and advocacy groups to combat this emerging threat and protect the well-being of individuals online.

Introduction
In an alarming event, one of India’s premier healthcare institutes, AIIMS Delhi, has fallen victim to a malicious cyberattack for the second time in the year. The Incident serves as a clear-cut reminder of the escalating threat landscape faced by the healthcare organisation in this digital age. In the attack, which unfolded with grave implications, the attackers not only explored the vulnerabilities present in the healthcare sector, but this also raised the concern about the security of patient data and the uninterrupted delivery of critical healthcare services. In this blog post, we will explore the incident, what happened, and what safety measures can be taken.
Backdrop
The cyber-security systems deployed in AIIMS, New Delhi, recently detected a malware attack. The nature and scope of the attack were both sophisticated and targeted. This second hack acts as a wake-up call for healthcare organisations nationwide. As the healthcare business increasingly depends on digital technology to improve patient care and operational efficiency, cybersecurity must be prioritised to protect sensitive data. To minimise cyber-attack dangers, healthcare organisations must invest in robust defences such as multi-factor authentication, network security, frequent system upgrades, and employee training.
The attempt was successfully prevented, and the deployed cyber-security systems neutralised the threat. The e-Hospital services remain to be fully secure and are functioning normally.
Impact on AIIMS
Healthcare services have been under hackers’ radar worldwide, and the healthcare sector has been impacted badly. The attack on AIIMS Delhi’s effects has been both immediate and far-reaching. The organisation, which is recognised for delivering excellent healthcare services and performing breakthrough medical research, faced significant interruptions in its everyday operations. Patient care and treatment processes were considerably impeded, resulting in delays, cancellations, and the inability to access essential medical documents. The stolen data raises serious concerns about patient privacy and confidentiality, raising doubts about the institution’s capacity to protect sensitive information. Furthermore, the financial ramifications of the assault, such as the cost of recovery, deploying more robust cybersecurity measures, and potential legal penalties and forensic analyses, contribute to the scale of the effect. The event has also generated public concerns about the institution’s ability to preserve personal information, undermining confidence and degrading AIIMS Delhi’s image.
Impact on Patients: The attacks not only impact the institutes but also have serious implications for the patients and here are some key highlights:
Healthcare Service Disruption: The hack has affected the seamless delivery of healthcare services at AIIMS Delhi. Appointments, surgeries, and other medical treatments may be delayed, cancelled, or rescheduled. This disturbance can result in longer wait times, longer treatment periods, and potential problems from delayed or interrupted therapy.

Patient Privacy and Confidentiality are jeopardised because of the breach of sensitive patient data. Medical data, test findings, and treatment plans may have been compromised. This breach may diminish patient faith in the institution’s capacity to safeguard their personal information, discouraging them from seeking care or submitting sensitive information in the future.
As a result of the cyberattack, patients may endure mental anguish and worry. Fear of possible exploitation of personal health information, confusion about the scope of the breach, and concerns about the security of their healthcare data can all have a negative impact on their mental health. This stress might aggravate pre-existing medical issues and impede total recovery.
Trust at stake: A data breach may harm patients’ faith and confidence in AIIMS Delhi and the healthcare system. Patients rely on healthcare facilities to keep their information secure and confidential while providing safe, high-quality care. A hack can doubt the institution’s ability to safeguard patient data, affecting patients’ overall faith in the organisation and potentially leading to patients seeking care elsewhere.
Cybersecurity Measures
To avoid future hacks and protect patient data, AIIMS Delhi must prioritize enhancing its cybersecurity procedures. The institution can strengthen its resistance to changing threats by establishing strong security practices. The following steps can be considered.
Using Multi-factor Authentication: By forcing users to submit several forms of identity to access systems and data, multi-factor authentication offers an extra layer of protection. AIIMS Delhi may considerably lower the danger of unauthorised access by applying this precaution, even in the case of leaked passwords or credentials. Biometrics and one-time passwords, for example, should be integrated into the institution’s authentication systems.
Improving Network Security and Firewalls: AIIMS Delhi should improve network security by implementing strong firewalls, intrusion detection and prevention systems, and network segmentation. These techniques serve to construct barriers between internal systems and external threats, reducing attackers’ lateral movement within the network. Regular network traffic monitoring and analysis can assist in recognising and mitigating any security breaches.
Risk Assessment: Regular penetration testing and vulnerability assessments are required to uncover possible flaws and vulnerabilities in AIIMS Delhi’s systems and infrastructure. Security professionals can detect vulnerabilities and offer remedial solutions by carrying out controlled simulated assaults. This proactive strategy assists in identifying and addressing any security flaws before attackers exploit them.
Educating and training Healthcare Professionals: Education and training have a crucial role in enhancing cybersecurity practices in healthcare facilities. Healthcare workers, including physicians, nurses, administrators, and support staff, must be well-informed about the importance of cybersecurity and trained in risk-mitigation best practices. This will empower healthcare professionals to actively contribute to protecting the patient’s data and maintaining the trust and confidence of patients.
Learnings from Incidents
AIIMS Delhi should embrace cyber-attacks as learning opportunities to strengthen its security posture. Following each event, a detailed post-incident study should be performed to identify areas for improvement, update security policies and procedures, and improve employee training programs. This iterative strategy contributes to the institution’s overall resilience and preparation for future cyber-attacks. AIIMS Delhi can effectively respond to cyber incidents, minimise the impact on operations, and protect patient data by establishing an effective incident response and recovery plan, implementing data backup and recovery mechanisms, conducting forensic analysis, and promoting open communication. Proactive measures, constant review, and regular revisions to incident response plans are critical for staying ahead of developing cyber threats and ensuring the institution’s resilience in the face of potential future assaults.

Conclusion
To summarise, developing robust healthcare systems in the digital era is a key challenge that healthcare organisations must prioritise. Healthcare organisations can secure patient data, assure the continuation of key services, and maintain patients’ trust and confidence by adopting comprehensive cybersecurity measures, building incident response plans, training healthcare personnel, and cultivating a security culture. Adopting a proactive and holistic strategy for cybersecurity is critical to developing a healthcare system capable of withstanding and successfully responding to digital-age problems.


