#FactCheck: Old clip of Greenland tsunami depicts as tsunami in Japan
Executive Summary:
A viral video depicting a powerful tsunami wave destroying coastal infrastructure is being falsely associated with the recent tsunami warning in Japan following an earthquake in Russia. Fact-checking through reverse image search reveals that the footage is from a 2017 tsunami in Greenland, triggered by a massive landslide in the Karrat Fjord.

Claim:
A viral video circulating on social media shows a massive tsunami wave crashing into the coastline, destroying boats and surrounding infrastructure. The footage is being falsely linked to the recent tsunami warning issued in Japan following an earthquake in Russia. However, initial verification suggests that the video is unrelated to the current event and may be from a previous incident.

Fact Check:
The video, which shows water forcefully inundating a coastal area, is neither recent nor related to the current tsunami event in Japan. A reverse image search conducted using keyframes extracted from the viral footage confirms that it is being misrepresented. The video actually originates from a tsunami that struck Greenland in 2017. The original footage is available on YouTube and has no connection to the recent earthquake-induced tsunami warning in Japan
The American Geophysical Union (AGU) confirmed in a blog post on June 19, 2017, that the deadly Greenland tsunami on June 17, 2017, was caused by a massive landslide. Millions of cubic meters of rock were dumped into the Karrat Fjord by the landslide, creating a wave that was more than 90 meters high and destroying the village of Nuugaatsiaq. A similar news article from The Guardian can be found.

Conclusion:
Videos purporting to depict the effects of a recent tsunami in Japan are deceptive and repurposed from unrelated incidents. Users of social media are urged to confirm the legitimacy of such content before sharing it, particularly during natural disasters when false information can exacerbate public anxiety and confusion.
- Claim: Recent natural disasters in Russia are being censored
- Claimed On: Social Media
- Fact Check: False and Misleading
Related Blogs

Introduction
On April 30, 2025, the Supreme Court of India delivered a landmark judgment that cast a sharp light on one of the most overlooked yet pressing issues in modern governance—digital inequity. In a country that has a staggering 900 million Internet users, the ruling highlights a disheartening reality, a paradox that brings the “digital divide” to centre stage. While India may be the world’s second-largest online market, a significant segment of its population remains digitally disenfranchised. The judgment, delivered in response to two interconnected petitions, underscored that access to the internet is no longer a luxury but a lifeline integral to exercising fundamental rights. The court pointed out in clear terms that the government must build a digital ecosystem that is inclusive and accessible to all and attributed the right to digital access as an intrinsic part of the right to life and liberty under Article 21 as enshrined under the Indian Constitution.
Understanding the Context: What Prompted the Petitions?
The judgment springs out of two writ petitions, which sought instructions or guidelines for people with blindness or limited vision and acid attack survivors, respectively, to conduct digital Know Your Customer (KYC)/e-KYC/video KYC mandated by RBI’s KYC Master Directions, 2016, which were reserved for judgment on January 28. The court delivered the judgment on April 30, 2025, emphasising the fact that true inclusion in this digital era is confounded in an inclusive digital infrastructure, and it must provide reasonable accommodation to those who face impediments due to any disability or disfigurement.
In consonance with its view, it laid down various guidelines that ensure that all persons with disabilities or acid attack survivors are treated even when digital processes are involved in accordance with the provisions of the Right of Persons with Disabilities Act, 2016 (hereinafter referred to as “RPwD Act”)
Another major observation made by the Honourable SC judges is that the mode of facilitation of government services is through digital platforms, i.e., e-governance, and access to all these welfare schemes is the right of every citizen, irrespective of the fact that they suffer from any disability. The failure of the provisioning of e-governance of these facilities to these individuals is a gross failure of the objectives of these schemes.
Key Observations and Directives
The court directed the government to release fresh guidelines that establish alternative methods to conduct digital KYC/e-KYC for all persons who suffer any impairment, low vision, or disfigurement with greater sensitivity, particularly for acid-attack survivors. The court made its intention very clear that the right to digital access is intrinsic to the right to life and liberty. All the tasks that are included within the ambit of digital KYC, such as pen-on-paper signatures, screen signatures, and the brief window for OTP entry, create an inaccessible and exclusionary framework, violating not just the dignity but the legal rights granted protection under the RPwD Act, 2016. The ruling directs a fundamental reimagining of digital governance through the lens of inclusion, equality, and dignity.
Conclusion
The court is not mincing its words when it declares digital accessibility as a constitutional imperative; it has made it clear that bridging the digital divide is no longer optional but a legal duty. The decision marks the new beginning and a propeller of digital transformation, and a delightful amalgamation of digital access and the rights of people. The effect of this judgment will not be restricted to one class of people. Still, it will cater to all those individuals who face these obstacles on a daily basis due to the exclusionary nature of digital platforms.
References

The rapid innovation of technology and its resultant proliferation in India has integrated businesses that market technology-based products with commerce. Consumer habits have now shifted from traditional to technology-based products, with many consumers opting for smart devices, online transactions and online services. This migration has increased potential data breaches, product defects, misleading advertisements and unfair trade practices.
The need to regulate technology-based commercial industry is seen in the backdrop of various threats that technologies pose, particularly to data. Most devices track consumer behaviour without the authorisation of the consumer. Additionally, products are often defunct or complex to use and the configuration process may prove to be lengthy with a vague warranty.
It is noted that consumers also face difficulties in the technology service sector, even while attempting to purchase a product. These include vendor lock-ins (whereby a consumer finds it difficult to migrate from one vendor to another), dark patterns (deceptive strategies and design practices that mislead users and violate consumer rights), ethical concerns etc.
Against this backdrop, consumer laws are now playing catch up to adequately cater to new consumer rights that come with technology. Consumer laws now have to evolve to become complimentary with other laws and legislation that govern and safeguard individual rights. This includes emphasising compliance with data privacy regulations, creating rules for ancillary activities such as advertising standards and setting guidelines for both product and product seller/manufacturer.
The Legal Framework in India
Currently, Consumer Laws in India while not tech-targeted, are somewhat adequate; The Consumer Protection Act 2019 (“Act”) protects the rights of consumers in India. It places liability on manufacturers, sellers and service providers for any harm caused to a consumer by faulty/defective products. As a result, manufacturers and sellers of ‘Internet & technology-based products’ are brought under the ambit of this Act. The Consumer Protection Act 2019 may also be viewed in light of the Digital Personal Data Protection Act 2023, which mandates the security of the digital personal data of an individual. Envisioned provisions such as those pertaining to mandatory consent, purpose limitation, data minimization, mandatory security measures by organisations, data localisation, accountability and compliance by the DPDP Act can be applied to information generated by and for consumers.
Multiple regulatory authorities and departments have also tasked themselves to issue guidelines that imbibe the principle of caveat venditor. To this effect, the Networks & Technologies (NT) wing of the Department of Telecommunications (DoT) on 2 March 2023, issued the Advisory Guidelines to M2M/IoT stakeholders for securing consumer IoT (“Guidelines”) aiming for M2M/IoT (i.e. Machine to Machine/Internet of things) compliance with the safety and security standards and guidelines in order to protect the users and the networks that connect these devices. The comprehensive Guidelines suggest the removal of universal default passwords and usernames such as “admin” that come preprogrammed with new devices and mandate the password reset process to be done after user authentication. Web services associated with the product are required to use Multi-Factor Authentication and duty is cast on them to not expose any unnecessary user information prior to authentication. Further, M2M/IoT stakeholders are required to provide a public point of contact for reporting vulnerability and security issues. Such stakeholders must also ensure that the software components are updateable in a secure and timely manner. An end-of-life policy is to be published for end-point devices which states the assured duration for which a device will receive software updates.
The involvement of regulatory authorities depends on the nature of technology products; a single product or technical consumer threat may see multiple guidelines. The Advertising Standards Council of India (ASCI) notes that cryptocurrency and related products were considered as the most violative category to commit fraud. In an attempt to protect consumer safety, it introduced guidelines to regulate advertising and promotion of virtual digital assets (VDA) exchange and trading platforms and associated services as a necessary interim measure in February 2022. It mandates that all VDA ads must carry the stipulated disclaimer “Crypto products and NFTs are unregulated and can be highly risky. There may be no regulatory recourse for any loss from such transactions.” must be made in a prominent and unmissable manner.
Further, authorities such as Securities and Exchange Board of India (SEBI) and the Reserve Bank of India (RBI) also issue cautionary notes to consumers and investors against crypto trading and ancillary activities. Even bodies like Bureau of Indian Standards (BIS) act as a complimenting authority, since product quality, including electronic products, is emphasised by mandating compliance to prescribed standards.
It is worth noting that ASCI has proactively responded to new-age technology-induced threats to consumers by attempting to tackle “dark patterns” through its existing Code on Misleading Ads (“Code”), since it is applicable across media to include online advertising on websites and social media handles. It was noted by ASCI that 29% of advertisements were disguised ads by influencers, which is a form of dark pattern. Although the existing Code addressed some issues, a need was felt to encompass other dark patterns.
Perhaps in response, the Central Consumer Protection Authority in November 2023 released guidelines addressing “dark patterns” under the Consumer Protection Act 2019 (“Guidelines”). The Guidelines define dark patterns as deceptive strategies and design practices that mislead users and violate consumer rights. These may include creating false urgency, scarcity or popularity of a product, basket sneaking (whereby additional services are added automatically on purchase of a product or service), confirm shaming (it refers to statements such as “I will stay unsecured” when opting out of travel insurance on booking of transportation tickets), etc. The Guidelines also cater to several data privacy considerations; for example, they stipulate a bar on encouraging consumers from divulging more personal information while making purchases due to difficult language and complex settings of their privacy policies, thereby ensuring compliance of technology product sellers and e-commerce platforms/vendors with data privacy laws in India. It is to be noted that the Guidelines are applicable on all platforms that systematically offer goods and services in India, advertisers and sellers.
Conclusion
Consumer laws for technology-based products in India play a pivotal role in safeguarding the rights and interests of individuals in an era marked by rapid technological advancements. These legislative frameworks, spanning facets such as data protection, electronic transactions, and product liability, assume a pivotal role in establishing a regulatory equilibrium that addresses the nuanced challenges of the digital age. The dynamic evolution of the digital landscape necessitates an adaptive legal infrastructure that ensures ongoing consumer safeguarding amidst technological innovations. As the digital landscape evolves, it is imperative for regulatory frameworks to adapt, ensuring that consumers are protected from potential risks associated with emerging technologies. Striking a balance between innovation and consumer safety requires ongoing collaboration between policymakers, businesses, and consumers. By staying attuned to the evolving needs of the digital age, Indian consumer laws can provide a robust foundation for security and equitable relationships between consumers and technology-based products.
References:
- https://dot.gov.in/circulars/advisory-guidelines-m2miot-stakeholders-securing-consumer-iot
- https://www.mondaq.com/india/advertising-marketing--branding/1169236/asci-releases-guidelines-to-govern-ads-for-cryptocurrency
- https://www.ascionline.in/the-asci-code/#:~:text=Chapter%20I%20(4)%20of%20the,nor%20deceived%20by%20means%20of
- https://www.ascionline.in/wp-content/uploads/2022/11/dark-patterns.pdf
Executive Summary:
Amid escalating tensions between Afghanistan and Pakistan, a video is being widely shared on social media claiming that Afghanistan has shot down a Pakistani fighter jet. The posts further allege that the incident marks the formal beginning of a war between the two countries. However, research conducted by the CyberPeace found the viral claim to be false and the research revealed that the circulating video is not authentic but AI-generated.
Claim
On February 24, 2026, a user on X (formerly Twitter) shared the viral video with the caption: “Afghanistan has shot down a Pakistani fighter jet! Afghanistan announces that war with Pakistan has begun.”
- Original post link: https://x.com/JyotiDevSpeaks/status/2026348257186545914
- Archived link: https://ghostarchive.org/archive/7l00Y

Fact Check:
A careful review of the viral video revealed unusual visual patterns and artificial-looking effects, raising suspicions that it may have been created using artificial intelligence.We analyzed the video using the AI detection tool Hive Moderation, which indicated an 86 percent probability that the video was AI-generated.
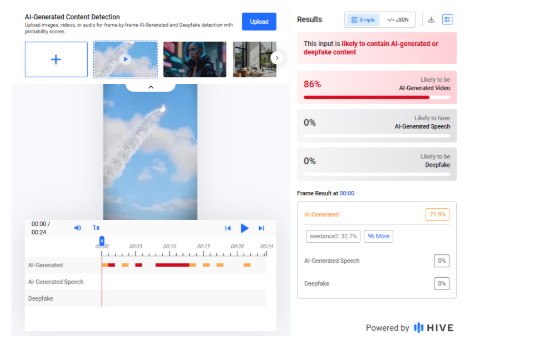
To further verify the findings, we scanned the footage using another AI detection platform, Sightengine. The results showed a 99 percent likelihood that the video was AI-generated.

To understand the broader context of the ongoing tensions, we conducted a keyword search and found a report published on February 22, 2026, by BBC Hindi. According to the report, Pakistan claimed it had targeted “seven terrorist hideouts and camps” along the Pakistan–Afghanistan border based on intelligence inputs. Meanwhile, a spokesperson for the Taliban government in Afghanistan stated that Pakistani airstrikes in Nangarhar and Paktika provinces resulted in the deaths of dozens of people, including women and children.
- https://www.bbc.com/hindi/articles/clyz8141397o
Conclusion
Our research confirms that the viral video claiming Afghanistan shot down a Pakistani fighter jet and formally declared war on Pakistan is fake. The footage is AI-generated and is being circulated with a false and misleading narrative.


