#FactCheck-Old 2020 Lockdown Video of PM Modi Resurfaces as Recent
Executive Summary
A video is being shared on social media in which Prime Minister Narendra Modi can be heard saying that “a complete lockdown will be imposed from midnight to save the country.” Research by the CyberPeace found the viral claim to be misleading. Our probe revealed that the video is from March 2020, when PM Modi had announced a nationwide lockdown to curb the spread of COVID-19.
Claim:
An Instagram user shared the viral video on March 25, 2026. The link and archive link of the post are given below.

Fact Check:
To verify the claim, we conducted a keyword search on Google. However, we did not find any credible media reports confirming that such a lockdown announcement had been made recently. We then extracted keyframes from the viral video and performed a reverse image search using Google Lens. During this process, we found the same video on a YouTube channel, where it had been uploaded on March 24, 2020.
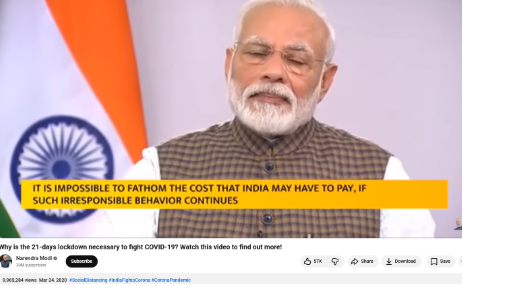
The viral portion of the clip appears around the 40-second mark in the original video.
Conclusion:
Our research found that the viral video is not recent. It dates back to March 24, 2020, when PM Modi announced a nationwide lockdown during the COVID-19 pandemic. The clip is being shared with a misleading claim.
Related Blogs

AI-generated content has been taking up space in the ever-changing dynamics of today's tech landscape. Generative AI has emerged as a powerful tool that has enabled the creation of hyper-realistic audio, video, and images. While advantageous, this ability has some downsides, too, particularly in content authenticity and manipulation.
The impact of this content is varied in the areas of ethical, psychological and social harms seen in the past couple of years. A major concern is the creation of non-consensual explicit content, including nudes. This content includes content where an individual’s face gets superimposed onto explicit images or videos without their consent. This is not just a violation of privacy for individuals, and can have humongous consequences for their professional and personal lives. This blog examines the existing laws and whether they are equipped to deal with the challenges that this content poses.
Understanding the Deepfake Technology
Deepfake technology is a media file (image, video, or speech) that typically represents a human subject that is altered deceptively using deep neural networks (DNNs). It is used to alter a person’s identity, and it usually takes the form of a “face swap” where the identity of a source subject is transferred onto a destination subject. The destination’s facial expressions and head movements remain the same, but the appearance in the video is that of the source. In the case of videos, the identities can be substituted by way of replacement or reenactment.
This superimposed content creates realistic content, such as fake nudes. Presently, creating a deepfake is not a costly endeavour. It requires a Graphics Processing Unit (GPU), software that is free, open-source, and easy to download, and graphics editing and audio-dubbing skills. Some of the common apps to create deepfakes are DeepFaceLab and FaceSwap, which are both public and open source and are supported by thousands of users who actively participate in the evolution and development of these software and models.
Legal Gaps and Challenges
Multiple gaps and challenges exist in the legal space for deepfakes and their regulation. They are:
- The inadequate definitions governing AI-generated explicit content often lead to enforcement challenges.
- Jurisdictional challenges due to the cross-border nature of crimes and the difficulties caused by international cooperation measures are in the early stages for AI content.
- There is a gap between the current consent-based and harassment laws for AI-generated nudes.
- Providing evidence or providing proof for the intent and identification of perpetrators in digital crimes is a challenge that is yet to be overcome.
Policy Responses and Global Trends
Presently, the global response to deepfakes is developing. The UK has developed the Online Safety Bill, the EU has the AI Act, the US has some federal laws such as the National AI Initiative Act of 2020 and India is currently developing the India AI Act as the specific legislation dealing with AI and its correlating issues.
The IT Rules, 2021, and the DPDP Act, 2023, regulate digital platforms by mandating content governance, privacy policies, grievance redressal, and compliance with removal orders. Emphasising intermediary liability and safe harbour protections, these laws play a crucial role in tackling harmful content like AI-generated nudes, while the DPDP Act focuses on safeguarding privacy and personal data rights.
Bridging the Gap: CyberPeace Recommendations
- Initiate legislative reforms by advocating for clear and precise definitions for the consent frameworks and instituting high penalties for AI-based offences, particularly those which are aimed at sexually explicit material.
- Advocate for global cooperation and collaborations by setting up international standards and bilateral and multilateral treaties that address the cross-border nature of these offences.
- Platforms should push for accountability by pushing for stricter platform responsibility for the detection and removal of harmful AI-generated content. Platforms should introduce strong screening mechanisms to counter the huge influx of harmful content.
- Public campaigns which spread awareness and educate users about their rights and the resources available to them in case such an act takes place with them.
Conclusion
The rapid advancement of AI-generated explicit content demands immediate and decisive action. As this technology evolves, the gaps in existing legal frameworks become increasingly apparent, leaving individuals vulnerable to profound privacy violations and societal harm. Addressing this challenge requires adaptive, forward-thinking legislation that prioritises individual safety while fostering technological progress. Collaborative policymaking is essential and requires uniting governments, tech platforms, and civil society to develop globally harmonised standards. By striking a balance between innovation and societal well-being, we can ensure that the digital age is not only transformative but also secure and respectful of human dignity. Let’s act now to create a safer future!
References
- https://etedge-insights.com/technology/artificial-intelligence/deepfakes-and-the-future-of-digital-security-are-we-ready/
- https://odsc.medium.com/the-rise-of-deepfakes-understanding-the-challenges-and-opportunities-7724efb0d981
- https://insights.sei.cmu.edu/blog/how-easy-is-it-to-make-and-detect-a-deepfake/

Introduction
Netflix is no stranger to its subscribers being targeted by SMS and email-led phishing campaigns. But the most recent campaign has been deployed at a global scale, affecting paid users in as many as 23 countries according to cybersecurity firm Bitdefender. In this particular campaign, attackers are using the carrot-and-stick tactic of either creating a false sense of urgency or promising rewards to steal financial information and Netflix credentials. For example, users may be contacted via SMS and told that their account is being suspended due to payment failures. A fake website may be shared through a link, encouraging the individual to share sensitive information to restore their account. Once this information has been input, it is now accessible to the attackers. This can create significant stress and even financial loss for its users. Thus, they are encouraged to develop the necessary skills to recognize and respond to these threats effectively.
How The Netflix Scam Works
Users are typically contacted through SMS. Bitdefender reports that these messages may look something like this:
"NETFLIX: There was an issue processing your payment. To keep your services active, please sign in and confirm your details at: https://account-details[.]com"
On clicking the link, the victim is directed to a website designed to mimic an authentic user experience interface, containing Netflix’s logo, color scheme, and grammatically-correct text. The website uses this interface to encourage the victim to divulge sensitive personal information, such as account credentials and payment details. Since this is a phishing website, the user’s personal information becomes accessible to the attacker as soon as it is entered. This information is then sold individually or in bundles on the dark web.
Practical Steps to Stay Safe
- Know Netflix’s Customer Interface: According to Netflix, it will never ask users to share personal information including credit or debit card numbers, bank account details, and Netflix passwords. It will also never ask for payment through a third-party vendor or website.
- Verify Authenticity: Do not open links from unknown sources sent by email or sms. If unsure, access Netflix directly by typing the URL into the browser instead of clicking on links in emails or texts. If the link has been opened, do not enter any information.
- Use Netflix’s Official Support Channels: Confirm any suspicious communication through Netflix’s verified help page or app. Write to phishing@netflix.com with any complaints about such an issue.
- Contact Your Financial Institution: If you have entered your personal information into a phishing website, you should immediately reach out to your bank to block your card and change your Netflix password. Contact the authorities via www.cybercrime.gov.in or by calling the helpline at 1930 in case of loss of funds.
- Use Strong Passwords and Enable MFA/2FA: Users are advised to use a unique, strong password with multiple characters. Enable Multi-Factor Authentication or Two Factor Authentication to your accounts, if available, to add an extra level of security.
Conclusion
Phishing campaigns which are designed to gather customer data through fraudulent means often involve sending links to as many users as possible, with the aim of monetizing stolen information. Attackers exploit user trust in online platforms to steal sensitive personal information, making such campaigns more sophisticated as highlighted above. This underscores the need for users of online platforms to practice good cyber hygiene by verifying information, learning to detect suspicious information and ignoring it, and staying aware of the types of online fraud they may be exposed to.
Sources
- https://www.bitdefender.com/en-gb/blog/hotforsecurity/netflix-scam-stay-safe
- https://help.netflix.com/en/node/65674
- https://timesofindia.indiatimes.com/technology/tech-news/netflix-users-beware-this-netflix-subscription-scam-is-active-in-23-countries-how-to-spot-one-and-stay-safe/articleshow/115820070.cms

"Cybercriminals are unleashing a surprisingly high volume of new threats in this short period of time to take advantage of inadvertent security gaps as organizations are in a rush to ensure business continuity.”
Cyber security firm Fortinet on Monday announced that over the past several weeks, it has been monitoring a significant spike in COVID-19 related threats.
An unprecedented number of unprotected users and devices are now online with one or two people in every home connecting remotely to work through the internet. Simultaneously there are children at home engaged in remote learning and the entire family is engaged in multi-player games, chatting with friends as well as streaming music and video. The cybersec firm’s FortiGuard Labs is observing this perfect storm of opportunity being exploited by cybercriminals as the Threat Report on the Pandemic highlights:
A surge in Phishing Attacks: The research shows an average of about 600 new phishing campaigns every day. The content is designed to either prey on the fears and concerns of individuals or pretend to provide essential information on the current pandemic. The phishing attacks range from scams related to helping individuals deposit their stimulus for Covid-19 tests, to providing access to Chloroquine and other medicines or medical device, to providing helpdesk support for new teleworkers.
Phishing Scams Are Just the Start: While the attacks start with a phishing attack, their end goal is to steal personal information or even target businesses through teleworkers. Majority of the phishing attacks contain malicious payloads – including ransomware, viruses, remote access trojans (RATs) designed to provide criminals with remote access to endpoint systems, and even RDP (remote desktop protocol) exploits.
A Sudden Spike in Viruses: The first quarter of 2020 has documented a 17% increase in viruses for January, a 52% increase for February and an alarming 131% increase for March compared to the same period in 2019. The significant rise in viruses is mainly attributed to malicious phishing attachments. Multiple sites that are illegally streaming movies that were still in theatres secretly infect malware to anyone who logs on. Free game, free movie, and the attacker is on your network.
Risks for IoT Devices magnify: As users are all connected to the home network, attackers have multiple avenues of attack that can be exploited targeting devices including computers, tablets, gaming and entertainment systems and even online IoT devices such as digital cameras, smart appliances – with the ultimate goal of finding a way back into a corporate network and its valuable digital resources.
Ransomware like attack to disrupt business: If the device of a remote worker can be compromised, it can become a conduit back into the organization’s core network, enabling the spread of malware to other remote workers. The resulting business disruption can be just as effective as ransomware targeting internal network systems for taking a business offline. Since helpdesks are now remote, devices infected with ransomware or a virus can incapacitate workers for days while devices are mailed in for reimaging.
“Though organizations have completed the initial phase of transitioning their entire workforce to remote telework and employees are becoming increasingly comfortable with their new reality, CISOs continue to face new challenges presented by maintaining a secure teleworker business model. From redefining their security baseline, or supporting technology enablement for remote workers, to developing detailed policies for employees to have access to data, organizations must be nimble and adapt quickly to overcome these new problems that are arising”, said Derek Manky, Chief, Security Insights & Global Threat Alliances at Fortinet – Office of CISO.


