#FactCheck -AI-Generated Video Falsely Shows Car Stuck on Delhi–Jaipur Highway Signboard
Executive Summary
A shocking video showing a car hanging from a highway signboard is going viral on social media. The clip allegedly shows a black Mahindra Thar stuck on an overhead direction signboard on the Delhi–Jaipur Highway (NH-48). Social media users are widely sharing the video, claiming it shows a real road accident. However, a research by CyberPeace found the viral claim to be false. Our findings reveal that the circulating video is not real but AI-generated.
Claim
Social media users are sharing the clip as footage of an actual road accident. A viral post on X (formerly Twitter) claims that the incident took place on the Delhi–Jaipur Highway, showing a black Mahindra & Mahindra Thar lodged in a highway signboard.
- https://x.com/SenBaijnath/status/2024098520006029504
- https://archive.ph/cmr5e

Fact Check
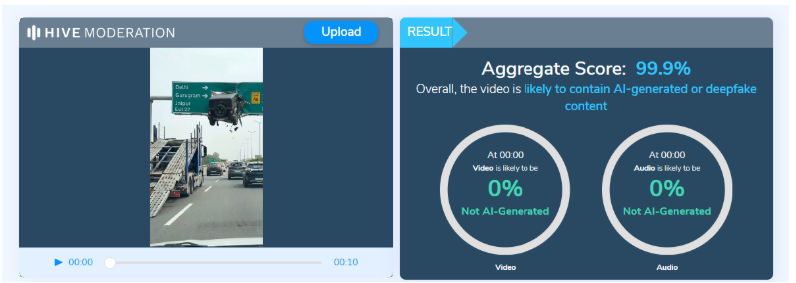
On closely examining the viral video, several inconsistencies were observed that are commonly associated with AI-generated content. For instance, it appears highly improbable for a heavy vehicle to get stuck precisely at the center of a signboard at such a height. Despite the scale of the alleged incident, traffic on the highway below continues moving normally without any disruption. Additionally, the text visible on the right side of the signboard appears distorted and unusually written. To further verify the authenticity of the video, we analysed it using the AI detection tool Hive Moderation, which indicated a 99.9% probability that the video was AI-generated.
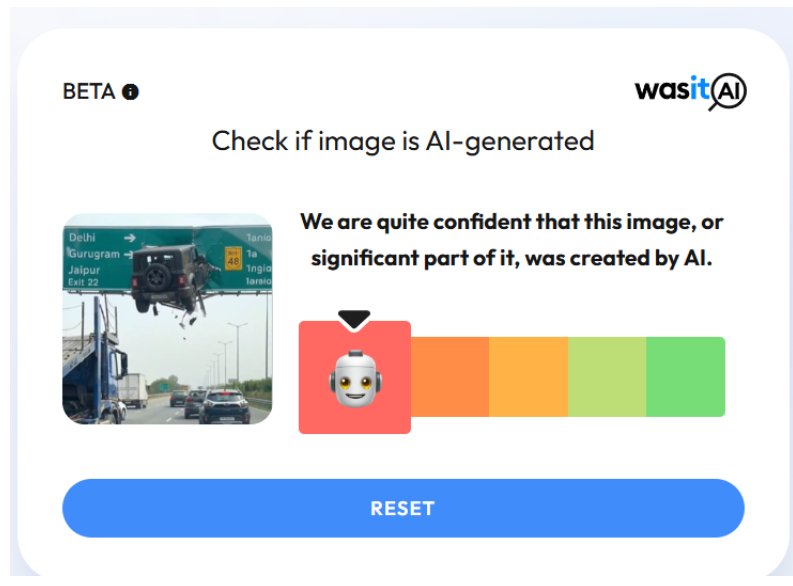
Another AI image detection tool, WasitAI, also found that the visuals in the viral clip were largely AI-generated.
Conclusion
Based on our research and available evidence, it is clear that the viral video showing a Mahindra Thar hanging from a highway signboard is not real but AI-generated.
Related Blogs

Executive Summary
A video showing a monkey dramatically rescuing a child hanging from a balcony is being widely shared on social media. In the clip, a small child appears to be on the verge of falling when a monkey suddenly arrives, grabs the child, and saves them from falling. Many users praised the monkey’s bravery, while some even described it as a miracle. Research by CyberPeace Research Wing found that the viral video is not real and was created using AI technology before being shared with misleading claims.
Claim
An X user shared the video claiming that a monkey saved a child from falling off a balcony just in time, astonishing onlookers with its intelligence and quick action. The post described the monkey’s act as heroic and compassionate.

Fact Check
To verify the claim, we extracted keyframes from the viral video and conducted a reverse image search using Google Lens. During this process, we found the same video uploaded on April 16, 2026 by an Instagram account named Instagram user mojilo_vandro. The caption described the scene as a “miracle of God.”

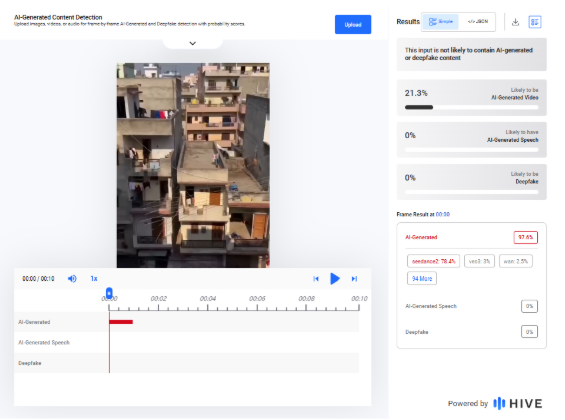
A closer review of the account revealed several similar monkey-themed videos. More importantly, the account bio clearly states that it creates AI-based fictional content. We also analyzed the clip using AI detection tool Hive Moderation, which assessed the video as having a 97.6% probability of being AI-generated
Conclusion
Our research confirms that the viral video of a monkey saving a child hanging from a balcony does not depict a real incident. It was digitally created using AI and shared online with misleading claims.

Introduction
As India moves full steam ahead towards a trillion-dollar digital economy, how user data is gathered, processed and safeguarded is under the spotlight. One of the most pervasive but least known technologies used to gather user data is the cookie. Cookies are inserted into every website and application to improve functionality, measure usage and customize content. But they also present enormous privacy threats, particularly when used without explicit user approval.
In 2023, India passed the Digital Personal Data Protection Act (DPDP) to give strong legal protection to data privacy. Though the act does not refer to cookies by name, its language leaves no doubt as to the inclusion of any technology that gathers or processes personal information and thus cookies regulation is at the centre of digital compliance in India. This blog covers what cookies are, how international legislation, such as the GDPR, has addressed them and how India's DPDP will regulate their use.
What Are Cookies and Why Do They Matter?
Cookies are simply small pieces of data that a website stores in the browser. They were originally designed to help websites remember useful information about users, such as your login session or what is in your shopping cart. Netscape initially built them in 1994 to make web surfing more efficient.
Cookies exist in various types. Session cookies are volatile and are deleted when the browser is shut down, whereas persistent cookies are stored on the device to monitor users over a period of time. First-party cookies are made by the site one is visiting, while third-party cookies are from other domains, usually utilised for advertisements or analytics. Special cookies, such as secure cookies, zombie cookies and tracking cookies, differ in intent and danger. They gather information such as IP addresses, device IDs and browsing history information associated with a person, thus making it personal data per the majority of data protection regulations.
A Brief Overview of the GDPR and Cookie Policy
The GDPR regulates how personal data can be processed in general. However, if a cookie collects personal data (like IP addresses or identifiers that can track a person), then GDPR applies as well, because it sets the rules on how that personal data may be processed, what lawful bases are required, and what rights the user has.
The ePrivacy Directive (also called the “Cookie Law”) specifically regulates how cookies and similar technologies can be used. Article 5(3) of the ePrivacy Directive says that storing or accessing information (such as cookies) on a user’s device requires prior, informed consent, unless the cookie is strictly necessary for providing the service requested by the user.
In the seminal Planet49 decision, the Court of Justice of the European Union held that pre-ticked boxes do not represent valid consent. Another prominent enforcement saw Amazon fined €35 million by France's CNIL for using tracking cookies without user consent.
Cookies and India’s Digital Personal Data Protection Act (DPDP), 2023
India's Digital Personal Data Protection Act, 2023 does not refer to cookies specifically but its provisions necessarily come into play when cookies harvest personal data like user activity, IP addresses, or device data. According to DPDP, personal data is to be processed for legitimate purposes with the individual's consent. The consent has to be free, informed, clear and unambiguous. The individuals have to be informed of what data is collected, how it will be processed.. The Act also forbids behavioural monitoring and targeted advertising in the case of children.
The Ministry of Electronics and IT released the Business Requirements Document for Consent Management Systems (BRDCMS) in June 2025. Although it is not binding by law, it provides operational advice on cookie consent. It recommends that websites use cookie banners with "Accept," "Reject," and "Customize" choices. Users must be able to withdraw or change their consent at any moment. Multi-language handling and automatic expiry of cookie preferences are also suggested to suit accessibility and privacy requirements.
The DPDP Act and the BRDCMS together create a robust user-rights model, even in the absence of a special cookie law.
What Should Indian Websites Do?
For the purposes of staying compliant, Indian websites and online platforms need to act promptly to harmonise their use of cookies with DPDP principles. This begins with a transparent and simple cookie banner providing users with an opportunity to accept or decline non-essential cookies. Consent needs to be meaningful; coercive tactics such as cookie walls must not be employed. Websites need to classify cookies (e.g., necessary, analytics and ads) and describe each category's function in plain terms under the privacy policy. Users must be given the option to modify cookie settings anytime using a Consent Management Platform (CMP). Monitoring children or their behavioural information must be strictly off-limits.
These are not only about being compliant with the law, they're about adhering to ethical data stewardship and user trust building.
What Should Users Do?
Cookies need to be understood and controlled by users to maintain online personal privacy. Begin by reading cookie notices thoroughly and declining unnecessary cookies, particularly those associated with tracking or advertising. The majority of browsers today support blocking third-party cookies altogether or deleting them periodically.
It is also recommended to check and modify privacy settings on websites and mobile applications. It is possible to minimise surveillance with the use of browser add-ons such as ad blockers or privacy extensions. Users are also recommended not to blindly accept "accept all" in cookie notices and instead choose "customise" or "reject" where not necessary for their use.
Finally, keeping abreast of data rights under Indian law, such as the right to withdraw consent or to have data deleted, will enable people to reclaim control over their online presence.
Conclusion
Cookies are a fundamental component of the modern web, but they raise significant concerns about individual privacy. India's DPDP Act, 2023, though not explicitly referring to cookies, contains an effective legal framework that regulates any data collection activity involving personal data, including those facilitated by cookies.
As India continues to make progress towards comprehensive rulemaking and regulation, companies need to implement privacy-first practices today. And so must the users, in an active role in their own digital lives. Collectively, compliance, transparency and awareness can build a more secure and ethical internet ecosystem where privacy is prioritised by design.
References
- https://prsindia.org/billtrack/digital-personal-data-protection-bill-2023
- https://gdpr-info.eu/
- https://d38ibwa0xdgwxx.cloudfront.net/create-edition/7c2e2271-6ddd-4161-a46c-c53b8609c09d.pdf
- https://oag.ca.gov/privacy/ccpa
- https://www.barandbench.com/columns/cookie-management-under-the-digital-personal-data-protection-act-2023#:~:text=The%20Business%20Requirements%20Document%20for,the%20DPDP%20Act%20and%20Rules.
- https://samistilegal.in/cookies-meaning-legal-regulations-and-implications/#
- https://secureprivacy.ai/blog/india-digital-personal-data-protection-act-dpdpa-cookie-consent-requirements
- https://law.asia/cookie-use-india/
- https://www.cookielawinfo.com/major-gdpr-fines-2020-2021/#:~:text=4.,French%20websites%20could%20refuse%20cookies.

Executive Summary
A video is being widely shared on social media claiming that a leopard dragged away a passenger from a moving train. Several users are circulating the clip as a real incident. However, CyberPeace Research Wing research found the claim to be false. Our research revealed that the viral video is not real and was generated using Artificial Intelligence (AI).
Claim
An X user (formerly Twitter) shared the viral clip with the caption:“A leopard snatched a man from a moving train.”The link, archived version, and screenshot of the post are provided below.

Fact Check
On closely examining the video, several visual inconsistencies were noticed. The leopard’s body appears distorted at multiple points in the clip. In some frames, parts of the animal’s body seem to merge into the background, while in others, sections appear incomplete or disappear entirely — something not typically seen in authentic footage. In the final part of the video, where the leopard is allegedly shown attacking a passenger, the person’s hands, limbs, and body also appear blurred and distorted. Additionally, unusual and selective blurring can be observed throughout the video, indicating possible editing or AI manipulation.
To further verify the clip, we scanned the viral video using the AI detection tool Sightengine. According to the results, the video showed an 86 percent probability of being AI-generated.

As part of the research , we also analysed the clip using another AI detection platform, UndetectableTM AI, which likewise indicated that the viral video was AI-generated.

Conclusion
Our research found that the viral video claiming to show a leopard dragging away a passenger from a moving train is fake. The clip is AI-generated and does not depict a real incident.


