#FactCheck- Viral Video Falsely Claims Iranian Strike Destroyed Israeli Army Headquarters
Executive Summary
A video is going viral on social media showing a massive building engulfed in flames and collapsing into debris. It is being widely claimed that Iran launched a powerful attack that destroyed Israel’s army headquarters. However, research by CyberPeace reveals that this claim is misleading. The viral video is AI-generated and has no connection to any real-world event.
Claim
An X (formerly Twitter) user shared the viral video with the caption: “Iran has targeted Israel’s army headquarters. It seems Israel’s dream of becoming ‘Greater Israel’ will remain unfulfilled.”
Post link:
- https://x.com/KAMESHKUMAR96/status/2039009484069368083
Archived version:
- https://archive.ph/HKXkK
- https://x.com/KAMESHKUMAR96/status/2039009484069368083
- https://archive.ph/HKXkK

Similar videos have also been shared by other users on social media:
Fact Check
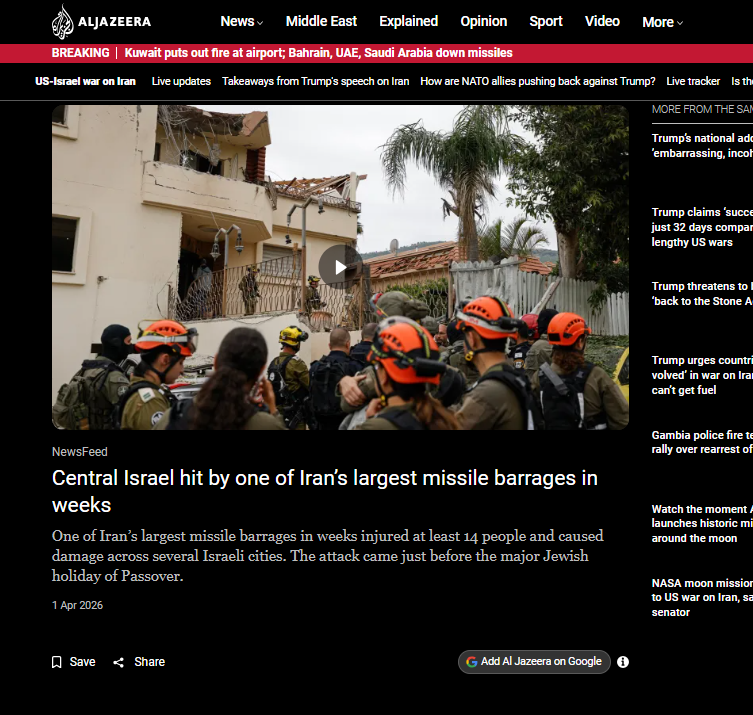
To verify the claim, we extracted keyframes from the viral video and conducted a reverse image search. During this process, we found several credible media reports confirming that Iran has carried out drone and missile attacks on Israel and the Gulf regions in recent times. However, none of these reports featured the viral video, indicating that it is not authentic footage.
- https://www.youtube.com/watch?v=fxDBX90bYng
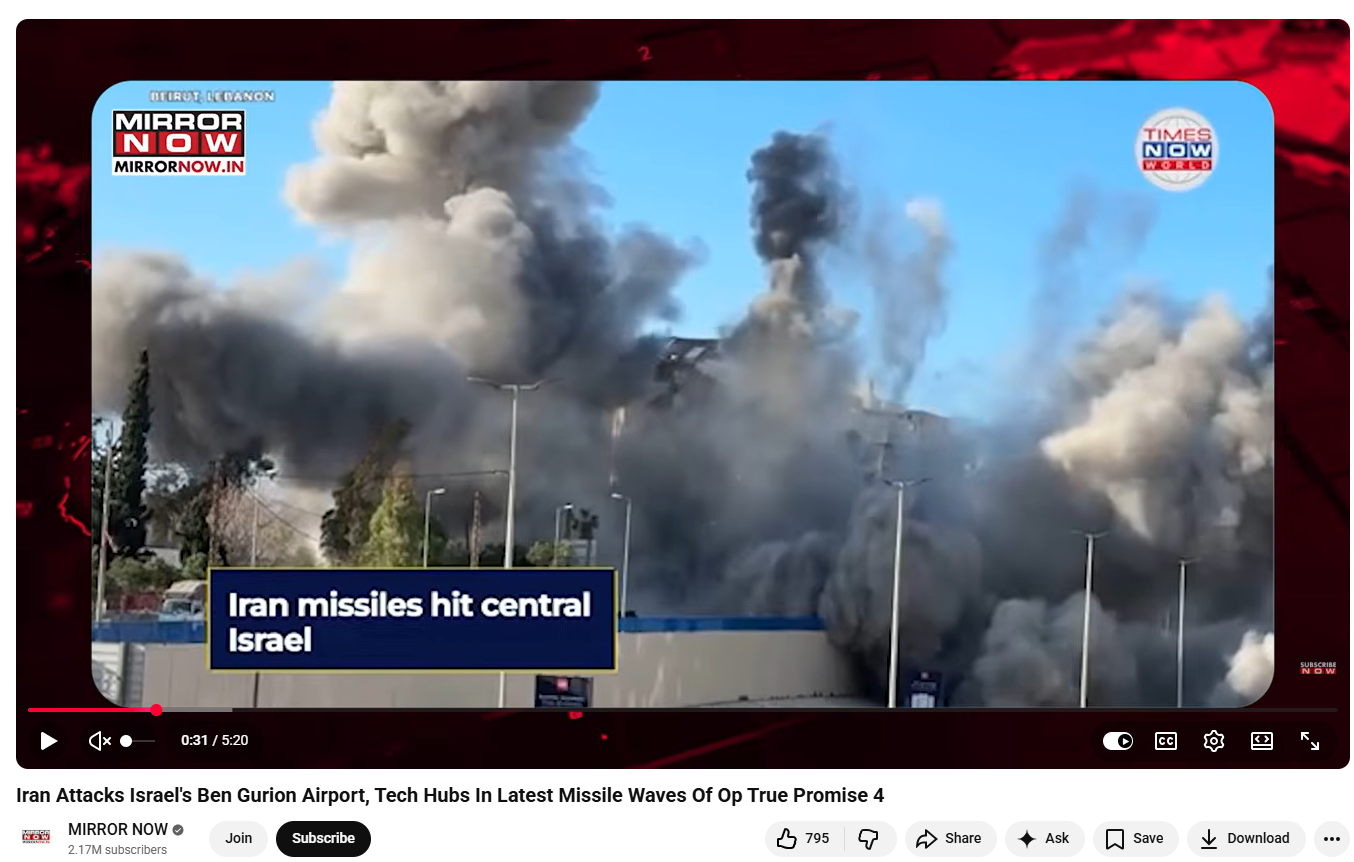
A closer examination of the video revealed multiple visual inconsistencies commonly associated with AI-generated content. For instance, a building on the left side appears to bend and collapse in a rubber-like manner—something that is physically unrealistic for structures made of concrete and steel. Additionally, the smoke and flames appear unnatural and lack realistic dynamics.
To further verify, we analyzed the video using the AI detection tool Hive Moderation, which classified it as 99.9% AI-generated.
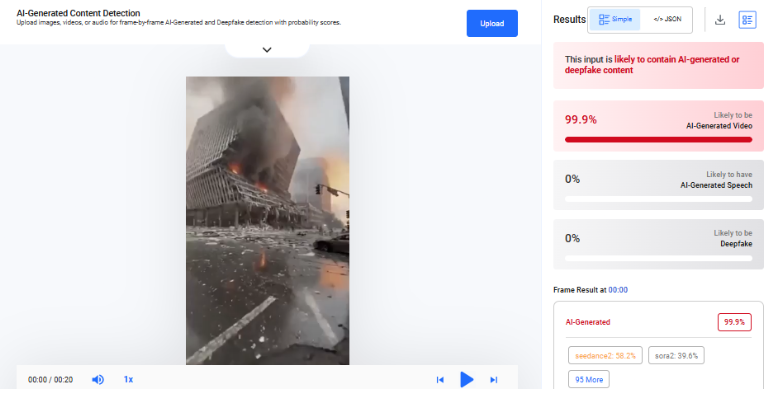
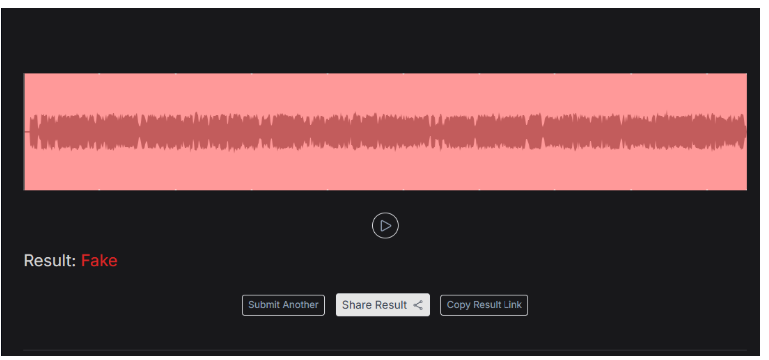
We also tested the video using the Deepfake-o-Meter platform.The AVSRDD (2025) model detected it as 99.5% AI-generated

Conclusion
Our research clearly establishes that the viral video claiming Iran destroyed Israel’s army headquarters is false and misleading. The footage does not appear in any credible news coverage of recent attacks, which strongly indicates that it is not real. Moreover, multiple AI detection tools consistently classify the video as artificially generated, with extremely high probability scores. Visual anomalies in the clip further support this finding.
Related Blogs

Executive Summary
A video allegedly showing Bollywood actor Shah Rukh Khan supporting and expressing his intention to join the so-called ‘Cockroach Janta Party’ (CJP) is being widely shared on social media.In the viral clip, Shah Rukh Khan can allegedly be heard saying:“Friends, the common people of this country are now fully awakened, and the storm of Cockroach Janta Party on social media has become so huge that its name is echoing everywhere… In just a few days, it has gained more than 15 million followers on Instagram… and honestly, I too will soon join the Cockroach Janta Party…”
However, CyberPeace Research Wing investigation found the claim to be false. The voice heard in the viral clip is AI-generated.
Claim
The viral video is being shared with the claim that actor Shah Rukh Khan publicly endorsed the ‘Cockroach Janta Party’ (CJP) and announced that he would soon join the movement.
- https://archive.is/wWueV

Fact Check
To verify the authenticity of the viral video, we first searched the internet using relevant keywords. However, we found no credible media reports, interviews, or posts from Shah Rukh Khan’s official social media accounts mentioning any support for the ‘Cockroach Janta Party’. Notably, if a major actor like Shah Rukh Khan had publicly supported any political or social media movement, it would have received widespread media coverage.
We then analysed key frames from the viral clip using Google Lens. During the investigation, we found an original video uploaded on September 10, 2023, on the YouTube channel of Sri Gokulam Movies. The footage was from the audio launch event of the film Jawan, where Shah Rukh Khan appeared in the same outfit seen in the viral clip.
वीडियो के डिस्क्रिप्शन में लिखा गया है, “शाहरुख़ In the original video, Shah Rukh Khan is seen speaking about the film, its cast, music, and his experience during the event. At no point does he mention the ‘Cockroach Janta Party’. The video description states that Shah Rukh Khan and the film’s team attended the audio launch event of Jawan in Chennai, where he praised music composer Anirudh Ravichander and thanked artists from the Tamil film industry. Additionally, the online trend related to the ‘Cockroach Janta Party’ emerged only in May 2026, whereas the original video is nearly three years old.
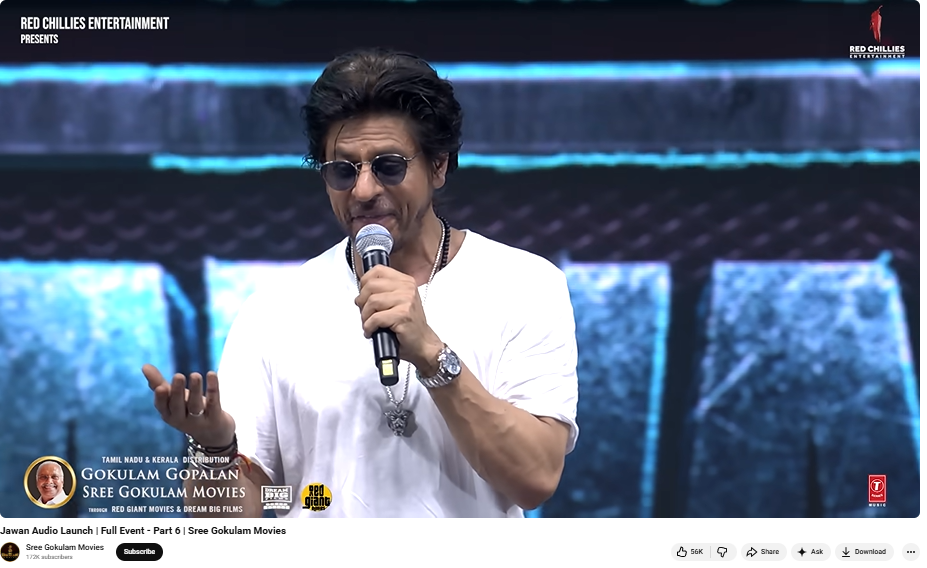
During the investigation, we also found several media reports covering the Jawan audio launch event, showing Shah Rukh Khan in the same attire as seen in the viral clip. For instance, a report published by Hindustan Times extensively covered the Chennai event, confirming that the viral footage was taken from the promotional event of the film.

To further examine the audio in the viral clip, we analysed it using the AI detection tool Resemble AI. The tool flagged the voice in the video as likely fake and AI-generated.
Conclusion
The investigation clearly shows that the claim about Shah Rukh Khan supporting or joining the ‘Cockroach Janta Party’ (CJP) is false. The viral video is actually from the 2023 audio launch event of the film Jawan, while the audio added to the clip has been generated using AI.

Introduction
In order to effectively deal with growing cyber crime and threats the Telangana police has taken initiative by launching Law Enforcement Chief Information Security Officers (CISO) Council, an innovative project launched in Telangana, India, which is a significant response to the growing cyber threat landscape. With cyber incidents increasing in the recent years and concerning statistics such as a tenfold rise in password-based attacks and an increase in ransomware attacks, the Council aims to strengthen the region's digital defenses. It primarily focuses on reducing vulnerability, improving resilience, and providing real-time threat intelligence. By promoting partnerships between the public and private sectors, offering legal and regulatory guidance, and facilitating networking and learning opportunities, this collaborative effort involving industry, academia, and law enforcement is a crucial move towards protecting critical infrastructure and businesses from cyber threats, the Telangana police in partnership with industry and academia, has launched the Law Enforcement CISO (Chief Information Security Officers) Council of India on 7th October 2023. Chief of the Central Crime Station Stephen Ravindra said that the forum is a path-breaking initiative and the Council represents an open platform for all the enforcement agencies in the country. The upcoming inititiative inculcate close association with different stakeholders, which includes government departments, startups, centers of excellence and international collaborations, carving a nieche for a sturdy cybersecurity envirnoment.
Enhancing Cybersecurity is the Need of the Hour:
The recent launch of the Law Enforcement CISO Council in Hyderabad, India emphasized the need for government organizations and industries to prioritize the protection of their digital space. Cyber incidents, ransomware attacks, and threats to critical infrastructure have been on the rise, making it essential to take proactive cybersecurity measures. Disturbing statistics regarding cyber threats, such as password-based attacks, BEC (Business Email Compromise) attempts, and vulnerabilities in the supply chain, highlight the importance of addressing these issues urgently. This initiative aims to provide real-time threat intelligence, legal guidance, and encourages collaboration between public and private organizations in order to combat cybercrime. Given that every cyber attack has criminal elements, the establishment of these councils is a crucial step towards minimizing vulnerabilities, enhancing resilience, and ensuring the security of our digital world.
International Issue & Domestic Issue:
The announcement by the Telangana State Police, is a proactive step to form a first-of-its-kind Law Enforcement CISO Council (LECC), as part of an initiative from the State government to give a further impetus to cyber security. Jointly with its law enforcement partners, the Telangana Police has decided to make cyber cops more efficient and shape them on par with the technology advancements. The Telangana police have proved its commitment for a secure cyber environment by recovering INR 2.2 crore and INR 6.8 crore lost by people in cyber frauds which is industry’s highest rate of helping the victims.
The Police department complemented efforts by corporate executives for their personal interest in the subject and mentioned police officers’ expertise and inputs from professionals from the industry need to work cohesively to prevent further increase in the number of cyber crime cases. Data indicates that the exponential increase in cyber threats in recent times necessitates an informed and prudent action with the cooperation and collaboration of the IT Department of Telangana, centers of excellence, start-ups, white hats or ethical hackers, and international associations.
A report from Telangana commissioner states the trend of a surge in the number of cyber incidents and vulnerabilities of Government organizations, Critical Infrastructure and MSMEs and stressed that every cyber security breaches have an element of criminality in it. The Law Enforcement CISO Council is a progressive step in this direction which ensures a reduced cyber attacks, enhanced resilience, actionable strategic and tactical real-time threat intelligence, legal guidance, opportunities for public private partnerships, networking, learning and much more.
The Secretary of SCSC, shared some alarming statistics on the threats that are currently rampant across the digital world. To combat it in today’s era of widespread digital dependence, the program launched by the Telangana Police stands as a commendable step or an initiative that offers a glimmer of aspiration. It brings together all the heroes who want to protect the digital spaces and counter the growing number of threats.
Contribution of Telangana Police for carving a niche to be followed:
The launch of the Law Enforcement CISO Council in Telangana represents a pivotal step in addressing the pressing challenges posed by escalating cyber threats. As highlighted by the Director General of Police, the initiative recognizes the critical need to combat cybercrime, which is growing at an alarming rate. The Council not only acknowledges the casual approach often taken towards cybersecurity but also aims to rectify it by fostering collaboration between law enforcement, industry, and academia.
One of the most significant positive aspects of this initiative is its commitment to sharing intelligence, ensuring that the hard-earned lessons from cyber fraud victims are translated into protective measures for others. By collaborating with the IT Department of Telangana, centers of excellence, startups, and ethical hackers, the Council is poised to develop robust Standard Operating Protocols (SOPs) and innovative tools to counter cyber threats effectively.
Moreover, the Council's emphasis on Public-Private Partnerships (PPPs) underscores its proactive approach in dealing with the evolving landscape of cyber threats. It offers a platform for networking and learning, enabling information sharing, and will contribute to reducing the attack surface, enhancing resilience, and providing real-time threat intelligence. Additionally, the Council will provide legal and regulatory guidance, which is crucial in navigating the complex realm of cybercrime. This collective effort represents a promising way forward in safeguarding digital spaces, critical infrastructure, and industries against cyber threats and ensuring a safer digital future for all.
Conclusion:
The Law Enforcement CISO Council in Telangana is an innovative effort to strengthen cybersecurity in the state. With the rise in cybercrimes and vulnerabilities, the council brings together expertise from various sectors to establish a strong defense against digital threats. Its goals include reducing vulnerabilities, improving resilience, and ensuring timely threat intelligence. Additionally, the council provides guidance on legal and regulatory matters, promotes collaborations between the public and private sectors, and creates opportunities for networking and knowledge-sharing. Through these important initiatives, the CISO Council will play a crucial role in establishing digital security and protecting the state from cyber threats.
References:
- http://www.uniindia.com/telangana-police-launches-india-s-first-law-enforcement-ciso-council/south/news/3065497.html
- https://indtoday.com/telangana-police-launched-indias-first-law-enforcement-ciso-council/
- https://www.technologyforyou.org/telangana-police-launched-indias-first-law-enforcement-ciso-council/
- https://timesofindia.indiatimes.com/city/hyderabad/victims-of-cyber-fraud-get-back-rs-2-2-cr-lost-money-in-bank-a/cs/articleshow/104226477.cms?from=mdr
Introduction
India is seeing a major change due to the introduction of Artificial Intelligence (AI) across all sectors of government, business, and the digital economy with regard to areas such as governance, healthcare, finance, and the infrastructure. The large scale and rapid pace of AI implementation are expected to lead to efficiency gains, innovations in products and services, and to drive economic growth; however, the growth of AI also creates many serious concerns regarding ethics, legality, and societal ramifications. Issues such as algorithmic bias in the use of algorithms by AI, a lack of transparency in decision-making algorithms, data protection risks resulting from AI employments, and unclear frameworks for determining accountability for AI-related action; bring issues of how we will govern AI in a responsible manner to the forefront of public policy discourse.
India wants to become an AI superpower and leader in technology on the world stage. As such, India has a dual responsibility to fuel innovation without discounting democratic ideals, human rights, and public trust. UNESCO's AI Readiness Assessment Methodology (RAM) is a global tool for AI governance, created to provide concrete policy guidance on how to make ethical AI a reality. The India AI RAM Report is set to be formally released by UNESCO during the India AI Impact Summit 2026, taking place in New Delhi, as a major milestone in India's developing AI governance journey.
What is UNESCO’s AI Readiness Assessment Methodology (RAM)?
UNESCO has created a simple yet effective tool, called the AI Readiness Assessment Methodology (RAM), that can assist governments in determining how well they are prepared to develop, deploy and manage Artificial Intelligence ethically, responsibly and trustworthily. RAM provides a framework for diagnosing and self-assessing the state of a country’s ability to govern AI on the basis of evidence-based decision making rather than serving as a regulatory framework or ranking system.
The most important goal of RAM is to assess a country’s overall state of readiness to govern AI based on four dimensions: institutionally, legally, socially and technologically. In doing so, RAM examines how institutions function, their maturity level and the extent to which various policies align with one another; thereby giving governments an overview of strengths, weaknesses and priorities for reform.
Unlike other frameworks, RAM does not prescribe any one-size-fits-all solutions; instead, it uses a context sensitive approach when implementing the concepts of AI governance due to differing national realities, developmental priorities and social/economic conditions. Using the ethical principles established by UNESCO, RAM converts these principles into practical actions that can guide countries in their transition from abstract commitments to concrete strategies for governing AI.
Key Dimensions Assessed Under RAM
UNESCO's AI Readiness Assessment Methodology (RAM) is a tool used to assess a country's readiness to implement ethical Artificial Intelligence through five interconnected dimensions. These include: the legal and regulatory dimension (which looks at the laws, rules, and safeguards that are currently in place related to AI), the social and cultural dimension (which looks at whether the public is aware of AI, whether it trusts AI, whether AI is an inclusive experience for all people who use AI and whether AI has affected society in various ways), and the economic dimension (which looks at innovation, participation from industry, and readiness of the market for AI).
Also included in the framework/functionality of the RAM are: scientific and educational dimension (which examines a country’s capacity to conduct serious scientific research, including research activities that prepare persons to be employable in AI jobs); and technological and infrastructure dimension (which examines the availability of data, digital infrastructure, and computing capabilities for AI projects in a country).
All five of these dimensions consider the entirety of the scope of an AI readiness evaluation to ensure that AI Governance is more than just a technical issue; rather, it is a condition of a country’s capacity to generate laws, create policy and maintain social equality in relation to all forms of Artificial Intelligence.
Methodology and Nationwide Consultative Process
RAM takes both qualitative and quantitative characteristics together to create an overall understanding of how ready any nation is for AI capabilities. It is designed with flexibility so nations can define their assessments with respect to their own institutional capabilities and development agenda.
Normally, RAM is implemented by an independent expert who is assisted by a national team consisting of various stakeholders. With respect to the RAM process used in India, it was conducted as a national consultation where representatives from across all sectors of society (government, private sector, academia, civil society, and young people) participated in the assessment's creation. This consultation process made sure there were many different viewpoints present, which increased the legitimacy of the assessment results and how relevant they are in each country. The consultation process also yields policy recommendations based on real life governing situations or challenges that are specific to different sectors.
Institutional Partnerships Behind India’s RAM
The India RAM Initiative was developed by the UNESCO South Asia Regional Office (as a partner of IndiaAI Mission and the Indian Ministry of Electronics and Information Technology) and implemented by Ikigai Law with the help of The Patrick J. McGovern Foundation. This demonstrated the need for and importance of partnership in developing governance frameworks for Artificial Intelligence (AI). The result of the RAM process is a collaborative effort that includes evidence-based international norm-setting capabilities from around the world; government policies under the guidance of national political leadership; independent legal-technical implementation; input from civil society; all with the goal of empowering (increasing) India's ability to establish and implement both a consistent (i.e., coherent) and comprehensive (i.e., inclusive) AI Governance Framework.
Significance of the India AI RAM Report and Its Launch
The India AI RAM Report provides a complete initial assessment of India’s AI ecosystem and includes key insights into AI readiness, governance strengths/weaknesses, and potential opportunities across multiple sectors. It identifies priority areas to promote a responsible and trustworthy AI ecosystem in India.
The report will be officially released during the India AI Impact Summit (February 16, 2026 at Bharat Mandapam, New Delhi) where Mr. Abhishek Venkateswaran (National Project Officer-Social and Human Sciences at UNESCO South Asia) offered additional insight into the consultative process and the overall importance of this launch on India's future AI policy path.
Policy Relevance and the Road Ahead
The RAM Framework gives the government a structure and roadmap for developing and implementing AI Governance. In doing this, RAM reinforces the alignment of IndiaAI Mission, which includes safety and trust in AI as one of the pillars. However, the results from this Assessment will not automatically translate to reforming institutions, issuing guidelines specific to sectors, or developing a mechanism for continued evaluation. Implementation will require strong and sustained commitment from political leaders, as well as the commitment of institutions involved in the reforms made possible by RAM's implementation.
Conclusion
UNESCO has developed an AI Readiness Assessment Methodology (AI-RAM) that can greatly advance the way India approaches governance with respect to artificial intelligence (AI). By focusing on "readiness" (doing what needs to be done), "responsibility" (being or having good moral principles) and "inclusivity" (including everyone), the AI-RAM will enable India to become an active participant in discussions around ethical use of AI at a global level. India is now positioned to take on a leadership role in the world by adopting this methodology, which provides a platform for establishing global standards for AI development. The real benefit of the AI-RAM will come from policy measures that will ensure future AI development in India is 'human-centered', 'trustworthy' and 'aligns with democratic values'.
References
- https://icaire.org/files/UNESCORam-en.pdf
- https://www.pib.gov.in/PressReleasePage.aspx?PRID=2134492®=3&lang=2
- https://www.facebook.com/unesconewdelhi/videos/unesco-is-set-to-launch-the-india-ai-readiness-assessment-methodology-ram-report/25955631820699516/
- https://www.unesco.org/ethics-ai/en/ram
- https://www.hindustantimes.com/india-news/unesco-meity-launch-exercise-to-assess-india-s-ai-readiness-101749188341803.html#
- https://www.manoramayearbook.in/current-affairs/india/2025/06/09/unesco-ai-readiness-assessment-methodology-ram.html


