#FactCheck -AI-Generated Image Falsely Claims Mukesh and Nita Ambani Gifted Luxury Car to Suryakumar Yadav
Executive Summary
A picture circulating on social media allegedly shows Reliance Industries chairman Mukesh Ambani and Nita Ambani presenting a luxury car to India’s T20 team captain Suryakumar Yadav. The image is being widely shared with the claim that the Ambani family gifted the cricketer a luxury car in recognition of his outstanding performance. However, research conducted by the CyberPeace found the viral claim to be false. The research revealed that the image being circulated online is not authentic but generated using artificial intelligence (AI).
Claim
On February 8, 2025, a Facebook user shared the viral image claiming that Mukesh Ambani and Nita Ambani gifted a luxury car to Suryakumar Yadav following his brilliant innings. The post has been widely circulated across social media platforms. In another instance, a user shared a collage in which one image shows Suryakumar Yadav receiving an award, while another depicts him with Nita Ambani, further amplifying the claim.
- https://www.facebook.com/61559815349585/posts/122207061746327178/?rdid=0MukeT6c7WK1uB8m#
- https://archive.ph/wip/UH9Xh

Fact Check:
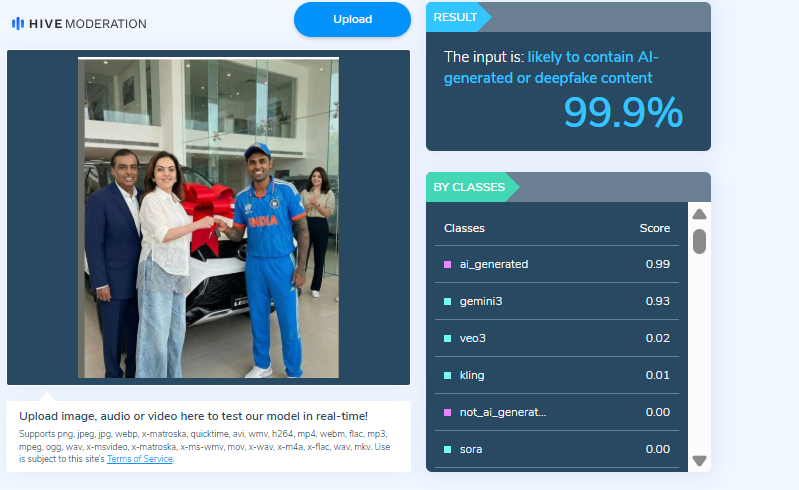
Upon closely examining the viral image, certain visual inconsistencies raised suspicion that it might be AI-generated. To verify its authenticity, the image was analysed using the AI detection tool Hive Moderation, which indicated a 99 percent probability that the image was AI-generated.
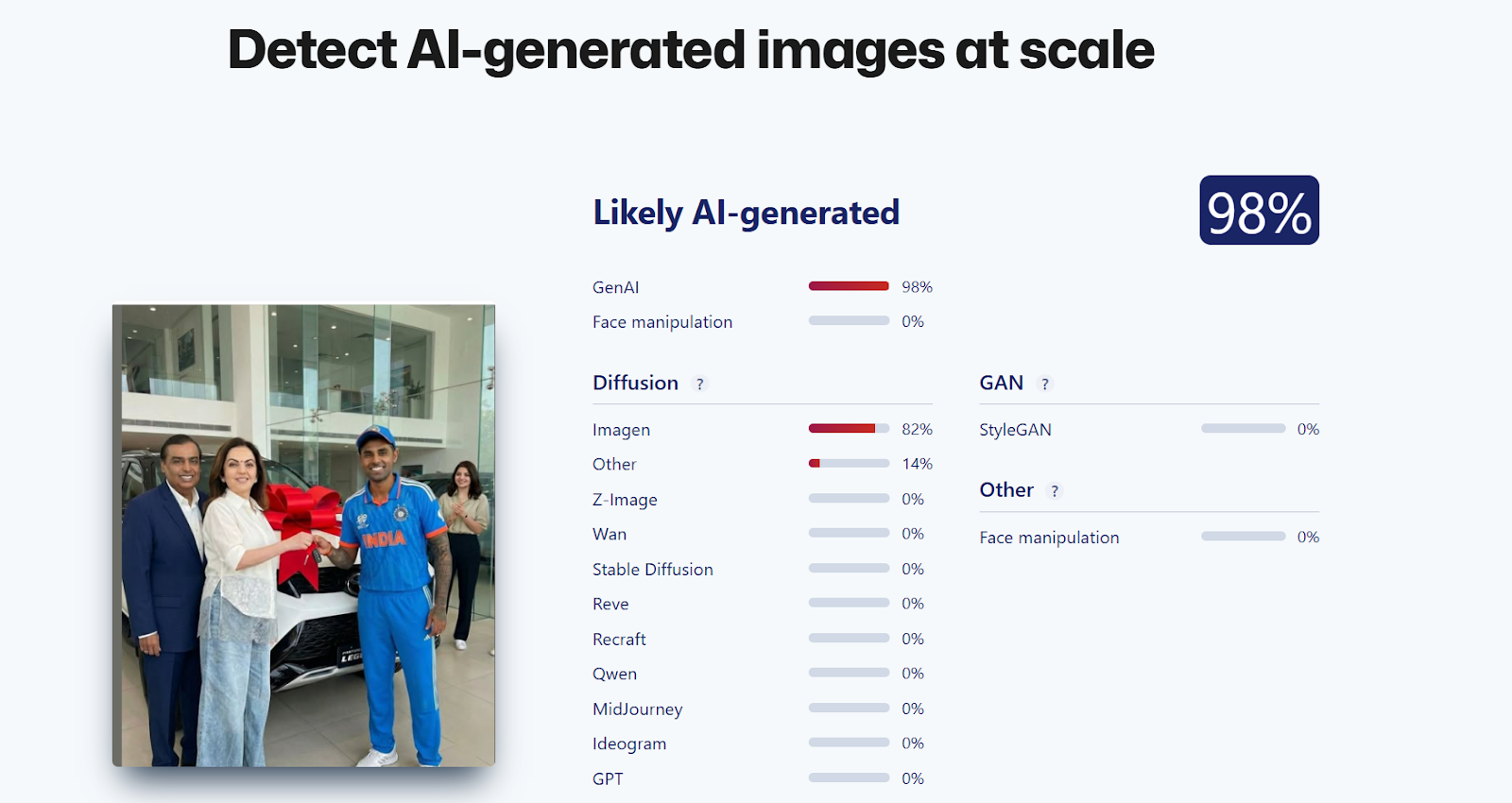
In the next step of the research, the image was also analysed using another AI detection tool, Sightengine, which found a 98 percent likelihood that the image was created using artificial intelligence.
Conclusion
The research clearly establishes that the viral image claiming Mukesh Ambani and Nita Ambani gifted a luxury car to Suryakumar Yadav is misleading. The picture is not real and has been generated using AI.
Related Blogs

Executive Summary:
A viral post currently circulating on various social media platforms claims that Reliance Jio is offering a ₹700 Holi gift to its users, accompanied by a link for individuals to claim the offer. This post has gained significant traction, with many users engaging in it in good faith, believing it to be a legitimate promotional offer. However, after careful investigation, it has been confirmed that this post is, in fact, a phishing scam designed to steal personal and financial information from unsuspecting users. This report seeks to examine the facts surrounding the viral claim, confirm its fraudulent nature, and provide recommendations to minimize the risk of falling victim to such scams.
Claim:
Reliance Jio is offering a ₹700 reward as part of a Holi promotional campaign, accessible through a shared link.

Fact Check:
Upon review, it has been verified that this claim is misleading. Reliance Jio has not provided any promo deal for Holi at this time. The Link being forwarded is considered a phishing scam to steal personal and financial user details. There are no reports of this promo offer on Jio’s official website or verified social media accounts. The URL included in the message does not end in the official Jio domain, indicating a fake website. The website requests for the personal information of individuals so that it could be used for unethical cyber crime activities. Additionally, we checked the link with the ScamAdviser website, which flagged it as suspicious and unsafe.


Conclusion:
The viral post claiming that Reliance Jio is offering a ₹700 Holi gift is a phishing scam. There is no legitimate offer from Jio, and the link provided leads to a fraudulent website designed to steal personal and financial information. Users are advised not to click on the link and to report any suspicious content. Always verify promotions through official channels to protect personal data from cybercriminal activities.
- Claim: Users can claim ₹700 by participating in Jio's Holi offer.
- Claimed On: Social Media
- Fact Check: False and Misleading

Introduction
Social media is the new platform for free speech and expressing one’s opinions. The latest news breaks out on social media and is often used by political parties to propagate their parties during the elections. Hashtag (#)is the new weapon, a powerful hashtag that goes a long way in making an impact in society that so at a global level. Various hashtags have gained popularity in the last years, such as – #blacklivesmatter, #metoo, #pride, #cybersecurity, and many more, which were influential in spreading awareness among the people regarding various social issues and taboos, which then were removed from multiple cultures. Social media is strengthened by social media influencers who are famous personalities with a massive following as they create regular content that the users consume and share with their friends. Social media is all about the message and its speed, and hence issues like misinformation and disinformation are widespread on nearly all social media platforms, so the influencers play a keen role in making sure the content on social media is in compliance with its community and privacy guidelines.
The Know-How
The Department of Consumer Affairs under the Ministry of Consumer Affairs, Food and Public Distribution released a guide, ‘Endorsements Know-hows!’ for celebrities, influencers, and virtual influencers on social media platforms, The guide aims to ensure that individuals do not mislead their audiences when endorsing products or services and that they are in compliance with the Consumer Protection Act and any associated rules or guidelines. Advertisements are no longer limited to traditional media like print, television, or radio, with the increasing reach of digital platforms and social media, such as Facebook, Twitter, and Instagram, there has been a rise in the influence of virtual influencers, celebrities, and social media influencers. This has led to an increased risk of consumers being misled by advertisements and unfair trade practices by these individuals on social media platforms. Endorsements must be made in simple, clear language, and terms such as “advertisement,” “sponsored,” or “paid promotion” can be used. They should not endorse any product or service and service in which they have done due diligence or that they have not personally used or experienced. The Act established guidelines for protecting consumers from unfair trade practices and misleading advertisements. The Department of Consumer Affairs published Guidelines for prevention of Misleading Advertisements and Endorsements for Misleading Advertisements, 2022, on 9th June 2022. These guidelines outline the criteria for valid advertisements and the responsibilities of manufacturers, service providers, advertisers, and advertising agencies. These guidelines also touched upon celebrities and endorsers. It states that misleading advertisements in any form, format, or medium are prohibited by law.
The guidelines apply to social media influencers as well as virtual avatars promoting products and services online. The disclosures should be easy to notice in post descriptions, where you can usually find hashtags or links. It should also be prominent enough to be noticeable in the content,
Changes Expected
The new guidelines will bring about uniformity in social media content in respect of privacy and the opinions of different people. The primary issue being addressed is misinformation, which was at its peak during the Covid-19 pandemic and impacted millions of people worldwide. The aspect of digital literacy and digital etiquette is a fundamental art of social media ethics, and hence social media influencers and celebrities can go a long way in spreading awareness about the same among common people and regular social media users. The increasing threats of cybercrimes and various exploitations over cyberspace can be eradicated with the help of efficient awareness and education among the youth and the vulnerable population, and the influencers can easily do the same, so its time that the influencers understand their responsibility of leading the masses online and create a healthy secure cyber ecosystem. Failing to follow the guidelines will make social media influencers liable for a fine of up to Rs 10 lakh. In the case of repeated offenders, the penalty can go up to Rs 50 lakh.
Conclusion
The size of the social media influencer market in India in 2022 was $157 million. It could reach as much as $345 million by 2025. Indian advertising industry’s self-regulatory body Advertising Standards Council of India (ASCI), shared that Influencer violations comprise almost 30% of ads taken up by ASCI, hence this legal backing for disclosure requirements is a welcome step. The Ministry of Consumer Affairs had been in touch with ASCI to review the various global guidelines on influencers. The social media guidelines from Clairfirnia and San Fransisco share the same basis, and hence guidelines inspired by different countries will allow the user and the influencer to understand the global perspective and work towards securing the bigger picture. As we know that cyberspace has no geographical boundaries and limitations; hence now is the time to think beyond conventional borders and start contributing towards securing and safeguarding global cyberspace.

Introduction
The recent advisory issued by CERT, issued on April 26th, 2026, titled “Defending Against Frontier AI-Driven Cyber Risks”, on AI-driven cyber threats does not merely add to the list of routine cybersecurity warnings. Instead, it marks a shift in how cyber risk itself is understood. The concern, here, is not just that attacks are increasing, but also that their nature is changing. Artificial intelligence is no longer assisting cyber operations- whether legitimate or malicious, in fragments; it is beginning to organise and execute them at scale.
What is emerging is a situation where capability is no longer tied to human skill alone. Systems can now identify vulnerabilities, generate exploits, and carry out coordinated attacks with limited intervention. This alters the baseline assumption of cybersecurity, that attacks require effort, time, and expertise.
The Essence: Automation and Capability
At the core of the advisory lies the recognition that AI has introduced speed and autonomy into cyber operations. Tasks such as analysing code, identifying vulnerabilities, or crafting phishing content are no longer sequential processes. They can happen almost simultaneously and at scale.
This is not simply a matter of efficiency. It changes the structure of the threat itself. When attacks can be automated, they become repeatable and less dependent on specialised actors. The advisory also points to the ability of AI systems to conduct multi-stage attacks, moving across networks and adapting strategies in real time.
In a way, the threat is no longer just external. It is embedded within the logics of the technology being used.
Significance: Lower Barriers, Wider Exposure
One of the more important aspects of the advisory is its emphasis on ‘accessibility’. AI lowers the barrier of complexity in the commission of cybercrimes. Activities that once required coordinated teams can now be performed by individuals with access to advanced tools.
This has two consequences. First, the number of potential attackers increases. Second, the scale at which attacks can be carried out expands significantly. Systems that were previously considered low risk may become viable targets simply because automated tools can scan, test, and exploit them rapidly.
There is also a broader anxiety reflected in what is being described as “Mythos concerns”, a shorthand for uncertainty around frontier AI systems and their unpredictable capabilities. This signals that the risk is not fully mapped yet and that regulatory responses are still catching up.
Element of Continuous Risk
The advisory outlines impacts such as unauthorised access, data breaches, identity theft, and financial fraud. These are familiar categories. What is less explicit, but more important, is the shift in how these harms occur.
When AI enables rapid and repeated exploitation, risk becomes continuous. Systems are not attacked once and then secured. They are exposed to ongoing attempts. This creates pressure not only on technical infrastructure but also on legal frameworks that are designed around discrete incidents.
For instance, obligations under the Information Technology Act, 2000 or even emerging data protection frameworks often assume identifiable breaches and reportable events. Continuous probing complicates that model!
Response Framework: From Compliance to Vigilance
CERT-In’s recommendations reflect this change in threat perception. There is a clear emphasis on vigilance rather than mere compliance. Organisations are advised to adopt zero-trust approaches, reduce exposure surfaces, and treat vulnerabilities as immediately exploitable.
The insistence on rapid patching within short timeframes is particularly telling. It acknowledges that the window between vulnerability disclosure and exploitation is shrinking.
There is also a noticeable expansion of responsibility. The advisory does not limit itself to large organisations. It extends guidance to the MSMEs and individuals, recognising that cyber risk is now distributed across the entire digital ecosystem.
A Subtle Legal Shift
Although the advisory itself is not binding in law, it operates within the framework of Section 70B of the Information Technology Act, 2000, which empowers CERT-In to issue directions on cybersecurity best practices and guidelines.
So, while the advisory does not create liability directly, it influences what may later be considered ‘reasonable security practice’. In that sense, it serves as soft law, gradually informing standards of due diligence.
At the same time, there remains a gap. The advisory focuses on defensive measures, but it does not fully address attribution and accountability in AI driven attacks. When actions are automated and anonymised, identifying responsibility and imposing liability becomes more complex.
Conclusion
The CERT In advisory is not just a warning about new threats. It is an acknowledgement of a transition. Cyber risk is moving from being occasional and targeted to being constant and scalable. AI is not simply adding to existing threats; it is restructuring and advancing them.
For cyber vigilance frameworks, this suggests a need to rethink priorities. Static compliance measures are no longer sufficient. It has become necessary to adopt continuous monitoring, adaptive responses, and a clearer understanding of how technology is reshaping risk.
While the advisory does not resolve these questions, it does bring them into focus. And that, in itself, is significant.
References
- CERT-In issues advisory against AI driven cyber attacks for MSMEs, organisations and individuals, Moneycontrol (Apr. 27, 2026), https://www.moneycontrol.com/technology/cert-in-issues-advisory-against-ai-driven-cyber-attacks-for-msmes-organisations-and-individuals-article-13899942.html.
- CERT-In warns of rising AI driven cyber threats amid Mythos concerns, Ommcom News (2026), https://ommcomnews.com/science-tech/cert-in-warns-of-rising-ai-driven-cyber-threats-amid-mythos-concerns/.
- Indian Computer Emergency Response Team (CERT-In), Defending Against Frontier AI Driven Cyber Risks, Advisory No. CIAD-2026-0020 (Apr. 26, 2026)
- Information Technology Act, 2000, § 70B (India).


