#FactCheck - AI-Generated Video Falsely Shared as ‘Multi-Hooded Snake’ Sighting in Vrindavan
A video is being widely shared on social media showing devotees seated in a boat appearing stunned as a massive, multi-hooded snake—resembling the mythical Sheshnag—suddenly emerges from the middle of a water body.
The video captures visible panic and astonishment among the devotees. Social media users are sharing the clip claiming that it is from Vrindavan, with some portraying the sight as a divine or supernatural event. However, research conducted by the Cyber Peace Foundation found the viral claim to be false. Our research revealed that the video is not authentic and has been generated using artificial intelligence (AI).
Claim
On January 17, 2026, a user shared the viral video on Instagram with the caption suggesting that God had appeared again in the age of Kalyug. The post claims that a terrifying video from Vrindavan has surfaced in which devotees sitting in a boat were shocked to see a massive multi-hooded snake emerge from the water. The caption further states that devotees are hailing the creature as an incarnation of Sheshnag or Vasuki Nag, raising religious slogans and questioning whether the sight represents a divine sign. (The link to the post, its archive link, and screenshots are available.)
- https://www.instagram.com/reel/DTngN9FkoX0/?igsh=MTZvdTN1enI2NnFydA%3D%3D
- https://archive.ph/UuAqB
Fact Check:
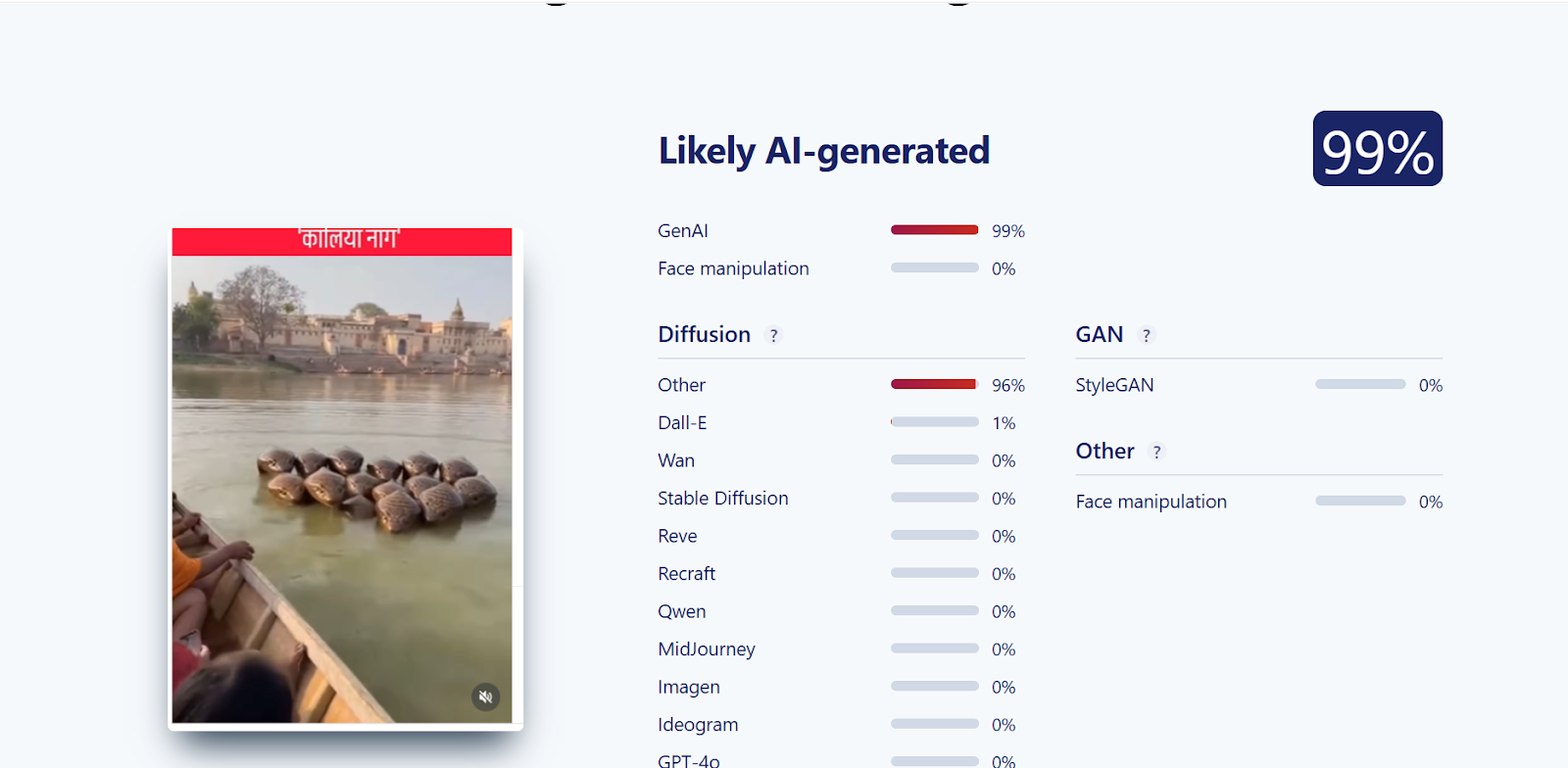
Upon closely examining the viral video, we suspected that it might be AI-generated. To verify this, the video was scanned using the AI detection tool SIGHTENGINE, which indicated that the visual is 99 per cent AI-generated.
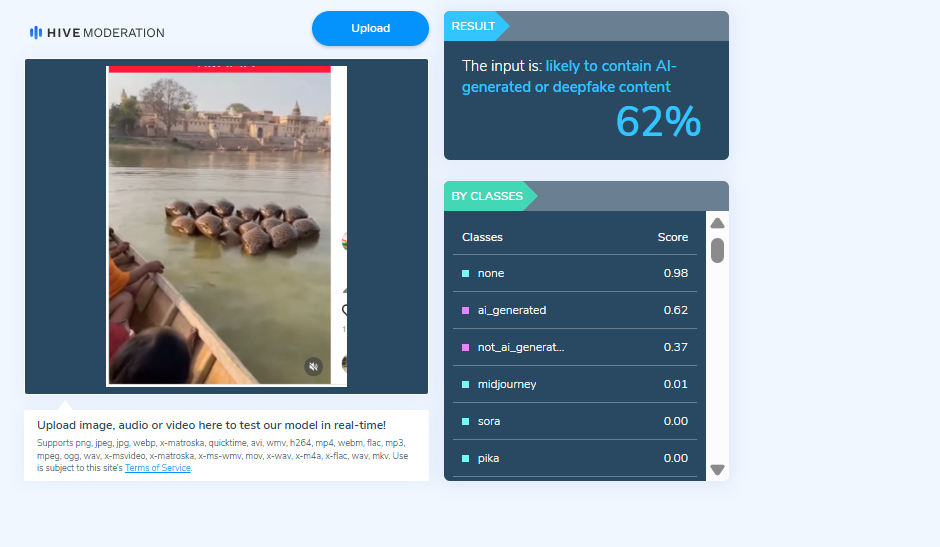
In the next step of the research , the video was analysed using another AI detection tool, HIVE Moderation. According to the results obtained, the video was found to be 62 per cent AI-generated.
Conclusion
Our research clearly establishes that the viral video claiming to show a multi-hooded snake in Vrindavan is not real. The clip has been created using artificial intelligence and is being falsely shared on social media with religious and sensational claims.
Related Blogs

The Illusion of Digital Serenity
In the age of technology, our email accounts have turned into overcrowded spaces, full of newsletters, special offers, and unwanted updates. To most, the presence of an "unsubscribe" link brings a minor feeling of empowerment, a chance to declutter and restore digital serenity. Yet behind this harmless-seeming tool lurks a developing cybersecurity threat. Recent research and expert discussions indicate that the "unsubscribe" button is being used by cybercriminals to carry out phishing campaigns, confirm active email accounts, and distribute malware. This new threat not only undermines individual users but also has wider implications for trust, behaviour, and governance in cyberspace.
Exploiting User Behaviour
The main challenge is the manipulation of user behaviour. Cyber thieves have learned to analyse typical user habits, most notably the instinctive process of unsubscribing from spam mail. Taking advantage of this, they now place criminal codes in emails that pose as real subscription programs. These codes may redirect traffic to fake websites that attempt to steal credentials, force the installation of malicious code, or merely count the click as verification that the recipient's email address is valid. Once confirmed, these addresses tend to be resold on the dark web or included in additional spam lists, further elevating the threat of subsequent attacks.
A Social Engineering Trap
This type of cyber deception is a prime example of social engineering, where the weakest link in the security chain ends up being the human factor. In the same way, misinformation campaigns take advantage of cognitive biases such as confirmation or familiarity, and these unsubscribe traps exploit user convenience and habits. The bait is so simple, and that is exactly what makes it work. Someone attempting to combat spam may unknowingly walk into a sophisticated cyber threat. Unlike phishing messages impersonating banks or government agencies, which tend to elicit suspicion, spoofed unsubscribe links are integrated into regular digital habits, making them more difficult to recognise and resist.
Professional Disguise, Malicious Intent
Technical analysis determines that most of these messages come from suspicious domains or spoofed versions of valid ones, like "@offers-zomato.ru" in place of the authentic "@zomato.com." The appearance of the email looks professional, complete with logos and styling copied from reputable businesses. But behind the HTML styling lies redirection code and obfuscated scripts with a very different agenda. At times, users are redirected to sites that mimic login pages or questionnaire forms, capturing sensitive information under the guise of email preference management.
Beyond the Inbox: Broader Consequences
The consequences of this attack go beyond the individual user. The compromise of a personal email account can be used to carry out more extensive spamming campaigns, engage in botnets, or even execute identity theft. Furthermore, the compromised devices may become entry points for ransomware attacks or espionage campaigns, particularly if the individual works within sensitive sectors such as finance, defence, or healthcare. In this context, what appears to be a personal lapse becomes a national security risk. This is why the issue posed by the weaponised unsubscribe button must be considered not just as a cybersecurity risk but also as a policy and public awareness issue.
Platform Responsibility
Platform responsibility is yet another important aspect. Email service providers such as Gmail, Outlook, and ProtonMail do have native unsubscribe capabilities, under the List-Unsubscribe header mechanism. These tools enable users to remove themselves from valid mailing lists safely without engaging with the original email content. Yet many users do not know about these safer options and instead resort to in-body unsubscribe links that are easier to find but risky. To that extent, email platforms need to do more not only to enhance backend security but also to steer user actions through simple interfaces, safety messages, and digital hygiene alerts.
Education as a Defence
Education plays a central role in mitigation. Just as cyber hygiene campaigns have been launched to teach users not to click on suspicious links or download unknown attachments, similar efforts are needed to highlight the risks associated with casual unsubscribing. Cybersecurity literacy must evolve to match changing threat patterns. Rather than only targeting clearly malicious activity, awareness campaigns should start tackling deceptive tactics that disguise themselves as beneficial, including unsubscribe traps or simulated customer support conversations. Partnerships between public and private institutions might be vital in helping with this by leveraging their resources for mass digital education.
Practical Safeguards for Users
Users are advised to always check the sender's domain before clicking any link, avoid unknown promotional emails, and hover over any link to preview its true destination. Rather than clicking "unsubscribe," users can simply mark such emails as spam or junk so that their email providers can automatically filter similar messages in the future. For enhanced security, embracing mechanisms such as mail client sandboxing, two-factor authentication (2FA) support, and alias email addresses for sign-ups can also help create layered defences.
Policy and Regulatory Implications
Policy implications are also significant. Governments and data protection regulators must study the increasing misuse of misleading unsubscribe hyperlinks under electronic communication and consent laws. In India, the new Digital Personal Data Protection Act, 2023 (DPDPA), provides a legislative framework to counter such deceptive practices, especially under the principles of legitimate processing and purpose limitation. The law requires that the processing of data should be transparent and fair, a requirement that malicious emails obviously breach. Regulatory agencies like CERT-In can also release periodic notifications warning users against such trends as part of their charter to encourage secure digital practices.
The Trust Deficit
The vulnerability also relates to broader issues of trust in digital infrastructure. When widely used tools such as an unsubscribe feature become points of exploitation, user trust in digital platforms erodes. Such a trust deficit can lead to generalised distrust of email systems, digital communication, and even legitimate marketing. Restoring and maintaining such trust demands a unified response that includes technical measures, user education, and regulatory action.
Conclusion: Inbox Hygiene with Caution
The "unsubscribe button trap" is a parable of the modern age. It illustrates how mundane digital interactions, when manipulated, can do great damage not only to individual users but also to the larger ecosystem of online security and trust. As cyber-attacks grow increasingly psychologically advanced and behaviorally focused, our response must similarly become more sophisticated, interdisciplinary, and user-driven. Getting your inbox in order should never involve putting yourself in cyber danger. But as things stand, even that basic task requires caution, context, and clear thinking.
Executive Summary
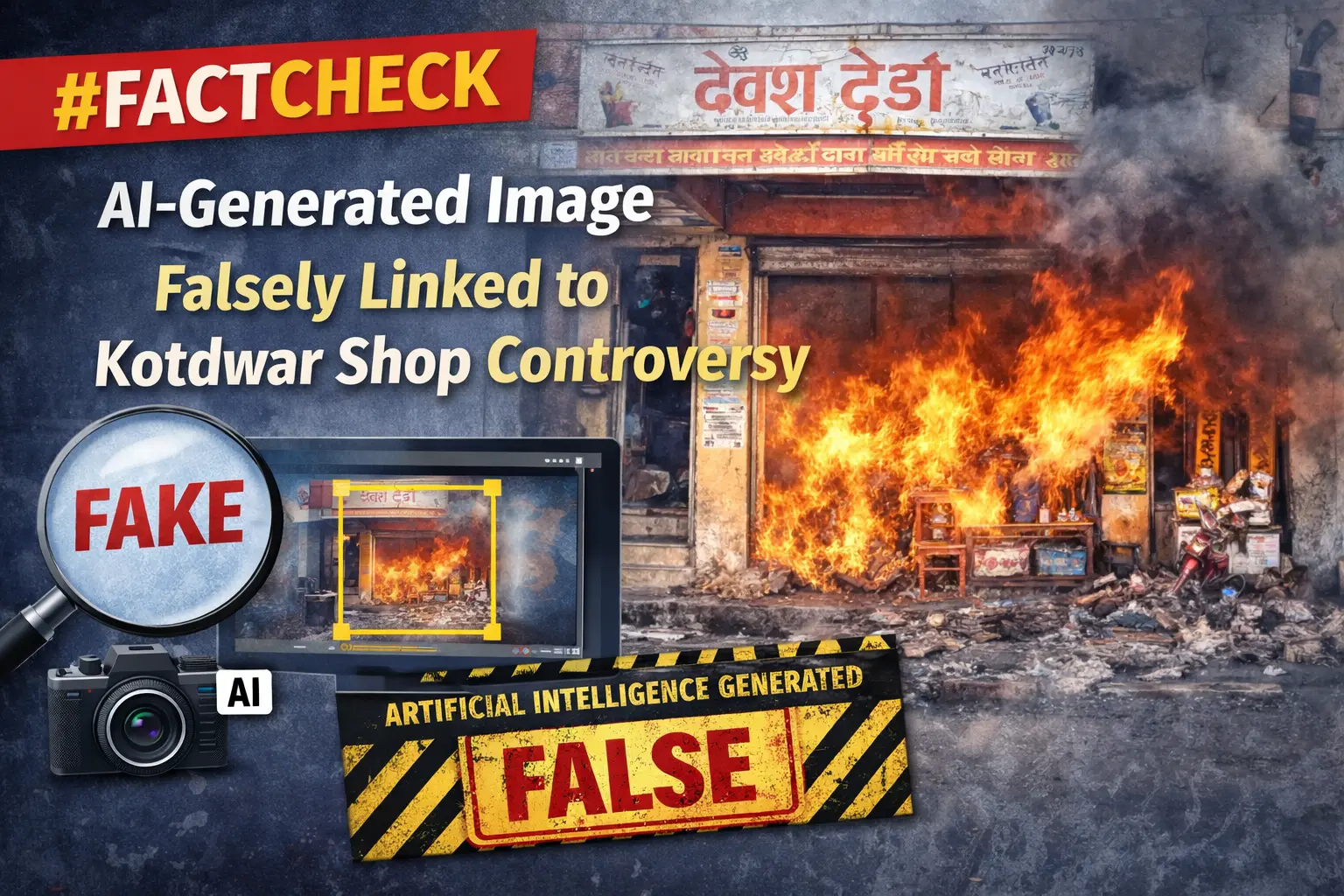
A dispute had recently emerged in Kotdwar, Uttarakhand, over the name of a shop. During the controversy, a local youth, Deepak Kumar, came forward in support of the shopkeeper. The incident subsequently became a subject of discussion on social media, with users expressing varied reactions. Meanwhile, a photo began circulating on social media showing a burqa-clad woman presenting a bouquet to Deepak Kumar. The image is being shared with the claim that All India Majlis-e-Ittehadul Muslimeen (AIMIM)’s women’s president, Rubina, welcomed “Mohammad Deepak Kumar” by presenting him with a bouquet. However, research conducted by the CyberPeace found the viral claim to be false. The research revealed that users are sharing an AI-generated image with a misleading claim.
Claim:
On social media platform Instagram, a user shared the viral image claiming that AIMIM’s women’s president Rubina welcomed “Mohammad Deepak Kumar” by presenting him with a bouquet. The link to the post, its archived version, and a screenshot are provided below.

Fact Check:
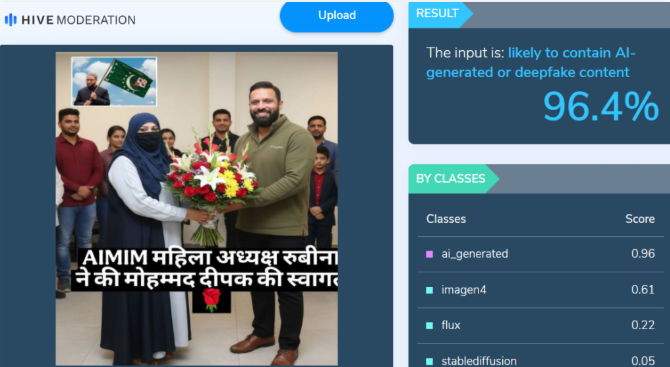
Upon closely examining the viral image, certain inconsistencies raised suspicion that it could be AI-generated. To verify its authenticity, the image was analysed using the AI detection tool Hive Moderation, which indicated a 96 percent probability that the image was AI-generated.
In the next stage of the research , the image was also analysed using another AI detection tool, Wasit AI, which likewise identified the image as AI-generated.
Conclusion
The research establishes that users are circulating an AI-generated image with a misleading claim linking it to the Kotdwar controversy.

Introduction:
Welcome to the second edition of our blog on Digital forensics series. In our previous blog we discussed what digital forensics is, the process followed by the tools, and the subsequent challenges faced in the field. Further, we looked at how the future of Digital Forensics will hold in the current scenario. Today, we will explore differences between 3 particular similar sounding terms that vary significantly in functionality when implemented: Copying, Cloning and Imaging.
In Digital Forensics, the preservation and analysis of electronic evidence are important for investigations and legal proceedings. Replication of the data and devices is one of the fundamental tasks in this domain, without compromising the integrity of the original evidence.
Three primary techniques -- copying, cloning, and imaging -- are used for this purpose. Each technique has its own strengths and is applied according to the needs of the investigation.
In this blog, we will examine the differences between copying, cloning and imaging. We will talk about the importance of each technique, their applications and why imaging is considered the best for forensic investigations.
Copying
Copying means duplicating data or files from one location to another. When one does copying, it implies that one is using standard copy commands. However, when dealing with evidence, it might be hard to use copy only. It is because the standard copy can alter the metadata and change the hidden or deleted data .
The characteristics of copying include:
- Speed: copying is simpler and faster,compared to cloning or imaging.
- Risk: The risk involved in copying is that the metadata might be altered and all the data might be captured.
Cloning
It is the process where the transfer of the entire contents of a hard drive or a storage device is done on another storage device. This process is known as cloning . This way, the cloning process captures both the active data and the unallocated space and hidden partitions, thus containing the whole structure of the original device. Cloning is generally used at the sector level of the device. Clones can be used as the working copy of a device .
Characteristics of cloning:
- bit-for-bit replication: cloning keeps the exact content and the whole structure of the original device.
- Use cases: cloning is used when it is needed to keep the original device intact for further examination or a legal affair.
- Time consuming: Cloning is usually longer in comparison to simple copying since it involves the whole detailed replication. Though it depends on various factors like the size of the storage device, the speed of the devices involved, and the method of cloning.
Imaging:
It is the process of creating a forensic image of a storage device. A forensic image is a replica copy of every bit of data that was on the source device, this including the allocated, unallocated, and the available slack space .
The image is then used for analysis and investigation, and the original evidence is left untouched. Images can’t be used as the working copies of a device. Unlike cloning, which produces working copies, forensic images are typically used for analysis and investigation purposes and are not intended for regular use as working copies.
Characteristics of Imaging:
- Integrity: Imaging ensures the integrity and authenticity of the evidence produced
- Flexibility: Forensic image replicas can be mounted as a virtual drive to create image-specific mode for analysis of data without affecting the original evidence .
- Metadata: Imaging captures metadata associated with the data, thus promoting forensic analysis.
Key Differences
- Purpose: Copying is for everyday use but not good for forensic investigations requiring data integrity. Cloning and imaging are made for forensic preservation.
- Depth of Replication: Cloning and imaging captures the entire storage device including hidden, unallocated, and deleted data whereas copying may miss crucial forensic data.
- Data Integrity: Imaging and cloning keep the integrity of the original evidence thus making them suitable for legal and forensic use. Which is a critical aspect of forensic investigations.
- Forensic Soundness: Imaging is considered the best in digital forensics due to its comprehensive and non-invasive nature.
- Cloning is generally from one hard disk to another, where as imaging creates a compressed file that contains a snapshot of the entire hard drive or a specific partitions
Conclusion
Therefore, copying, cloning, and imaging all deal with duplication of data or storage devices with significant variations, especially in digital forensic. However, for forensic investigations, imaging is the most selected approach due to the correct preservation of the evidence state for any analysis or legal use . Therefore, it is essential for forensic investigators to understand these rigorous differences to avail of real and uncontaminated digital evidence for their investigation and legal argument.


