#FactCheck-Air Taxi is a prototype and is not launched to commercial public
Executive Summary:
Recent reports circulating on various social media platforms have falsely claimed that an air taxi prototype is operational and providing services between Amritsar, Chandigarh, Delhi, and Jaipur. These claims, accompanied by images and videos, have been widely shared, leading to significant public attention. However, upon conducting a thorough examination using reverse image search, it has been determined that the information is misleading and inaccurate. These assertions do not reflect the current reality and are not substantiated by credible sources

Claim:
The claim suggests that an air taxi prototype is already operational, servicing routes between Amritsar, Chandigarh, Delhi, and Jaipur. This assertion is accompanied by images of a futuristic aircraft, implying that such technology is currently being used to transport commercial passengers.

Fact Check:
The claim of air taxi and routes between Amritsar, Chandigarh, Delhi, and Jaipur has been found to be misleading. Also, so far, neither the Indian government nor the respective aviation authorities have issued any sort of public declarations nor industry insiders to claim any launch of any air taxi service. Further research followed a keyword-based search that directed us to a news report published in The Times of India on January 20, 2025. A similar post to the one seen in the viral video accompanied the report. It stated that Bengaluru-based aerospace startup Sarla Aviation launched its prototype air taxi called “Shunya” during the Bharat Mobility Global Expo. Under this plan, it looks to initiate electric flying taxis in Bangalore by 2028. This urban air transport program for India will be similar to what they are posting in this regard.

Conclusion:
The viral claim saying that there is an air taxi service in India between Amritsar, Chandigarh, Delhi, and Jaipur is entirely false. The pictures and information going viral are misleading and do not relate to any progress or implementation of air taxi technology in India. To date, there is no official confirmation or credible evidence that supports such a service. Information must be verified from reliable sources before it is believed or shared in order to prevent the spread of misinformation.
- Claim: A viral post claims an air taxi is operational between Amritsar, Chandigarh, Delhi, and Jaipur.
- Claimed On: Social Media
- Fact Check: False and Misleading
Related Blogs
.webp)
Introduction
The judiciary as an institution has always been kept on a pedestal and is often seen as the embodiment of justice. From Dictatorship to Democracy, the judiciary plays a central role; even where the judiciary is controlled, the legitimacy of the policies, in one sense or another, is derived from it. In democracies around the world, the independence and well-being of the judiciary are seen as the barometer of democracy’s strength. In this global age, where technology is omnipresent, it seems the judiciary is no exception. Now more than ever, when the judiciary is at the centre of evaluative focus, it becomes imperative to make the judiciary transparent. Digitisation of the judiciary is not just an administrative reform; it is an extension of constitutionalism into the technological realm, an effort to ensure that justice is accessible, transparent, and efficient. On July 25, which is the International Day on Judicial Well-being, is commemorated every year with a clear message that judicial well-being supports “anti-corruption, access to justice, and sustainable peace.”
Digitisation by Design: Justice in the Age of Transformation
The Prime Minister of India envisioned the future of the Indian legal system in alignment with the digitised world, as when he said, “Technology will integrate police, forensics, jails, and courts, and will speed up their work as well. We are moving towards a justice system that will be fully future-ready,” he said, almost predicting the future. Although there are many challenges in the face of this future, there are various initiatives that ease the transition. To clarify, India is streamlining operations, reducing delays, and enhancing access to justice for all by integrating AI into legal research, case management, judicial procedures, and law enforcement. Machine Learning (ML), Natural Language Processing (NLP), Optical Character Recognition (OCR), and predictive analytics are just a few of the AI-powered technologies that are currently being used to increase crime prevention, automate administrative duties, and improve case monitoring.
The digitisation of Indian courts is a structural necessity rather than just a question of contemporary convenience. Miscarriages of justice have frequently resulted from the growing backlog of cases, challenges with maintaining records, and the loss of physical files. In the seminal case of State of U.P. v. Abhay Raj Singh, the courts acknowledged that a conviction could be overturned by missing records alone. With millions of legal documents at risk, digitisation becomes a shield against such a collapse and a tool for preserving judicial memory.
Judicial Digitalisation in India: Institutional Initiatives and Infrastructural Advancements
For centuries, towering bundles of courtroom files stood as dusty monuments to knowledge, sacred, chaotic, and accessible to a select few. But as we now stand in 2025, the physical boundaries of a traditional courtroom have blurred, and the Indian government is actively working towards transforming the legal system. The e-Courts Mission Mode Project is a flagship initiative that aims to utilise Information and Communication Technology (ICT) to modernise and advance the Indian judiciary. This groundbreaking effort, led by the Department of Justice, Government of India, is being carried out in close coordination with the Supreme Court of India’s e-Committee. As a news report suggests, the Supreme Court (SC) held 7.5 lakh hearings through video conferencing between 2020 and 2024, as stated by the Ministry of Law and Justice, responding to a query in the Rajya Sabha on Thursday. Technological tools such as the Supreme Court Vidhik Anuvaad Software (SUVAS), the Case Information Software (CIS), and the Supreme Court Portal for Assistance in Court’s Efficiency (SUPACE) were established to make all pertinent case facts easily available. In another move, the Registry, SC, in close coordination with IIT, Madras, has created and implemented AI and ML-based technologies that are integrated with the Registry’s electronic filing software. This serves as a statement to the fact that cybersecurity and digital infrastructure are no longer administrative add-ons but essential building blocks for ensuring judicial transparency, efficiency, and resilience.
E-Governance and Integrity: The Judiciary in Transition
The United Nations recognises the fundamentals of the judiciary’s well-being and how corruption acts like water to the rust and taints the integrity of not a single judge in general but creates a perception of the whole institution. This threat of corruption is recognised by the United Nations Convention against Corruption (UNCAC), particularly Article 11, which urges the protection of the judiciary’s independence and integrity. Digitisation, while it cannot operate in a vacuum, acts as a structural antidote to corruption by embedding transparency into the fabric of justice delivery as automated registry systems, e-filing, and real-time access to case data drastically reduce discretionary power and the potential for behind-the-scenes manipulation. However, digital systems are only as ethical as the people who design, maintain, and oversee them, bringing their own limitations.
Conclusion: CyberPeace and the Future of Ethical Digital Justice
The potential of digitalisation resides not just in efficiency but also in equity, as India’s judiciary balances tradition and change. A robust democracy, where justice is lit by code rather than hidden under files, is built on a foundation of an open, accessible, and technologically advanced court. This change is not risk-free, though. Secure justice must also be a component of digital justice. The very values that digitisation seeks to preserve are at risk from algorithmic opacity, data breaches, and insecure technologies.
Our vision is not just of a digitalised court system but of a digitally just society, one where judicial data is protected, legal processes are democratised, and innovation upholds constitutionalism. Therefore, as a step forward, CyberPeace resolves to support AI upskilling for legal professionals, advocate for secure-by-design court infrastructure, and facilitate dialogue between technologists and judicial actors to build trust in the digital justice ecosystem. CyberPeace is dedicated to cyber transparency, privacy protection, and ethical AI.
References
- https://www.un.org/en/observances/judicial-well-being
- https://www.pib.gov.in/PressReleasePage.aspx?PRID=2106239
- https://www.pib.gov.in/PressReleasePage.aspx?PRID=2106239
- https://www.barandbench.com/view-point/facilitating-legal-access-digitalization-of-supreme-court-high-court-records
- https://www.pib.gov.in/PressReleaseIframePage.aspx?PRID=2085127
- https://www.medianama.com/2024/12/223-supreme-court-seven-lakh-video-conferences-four-year-rajya-sabha/
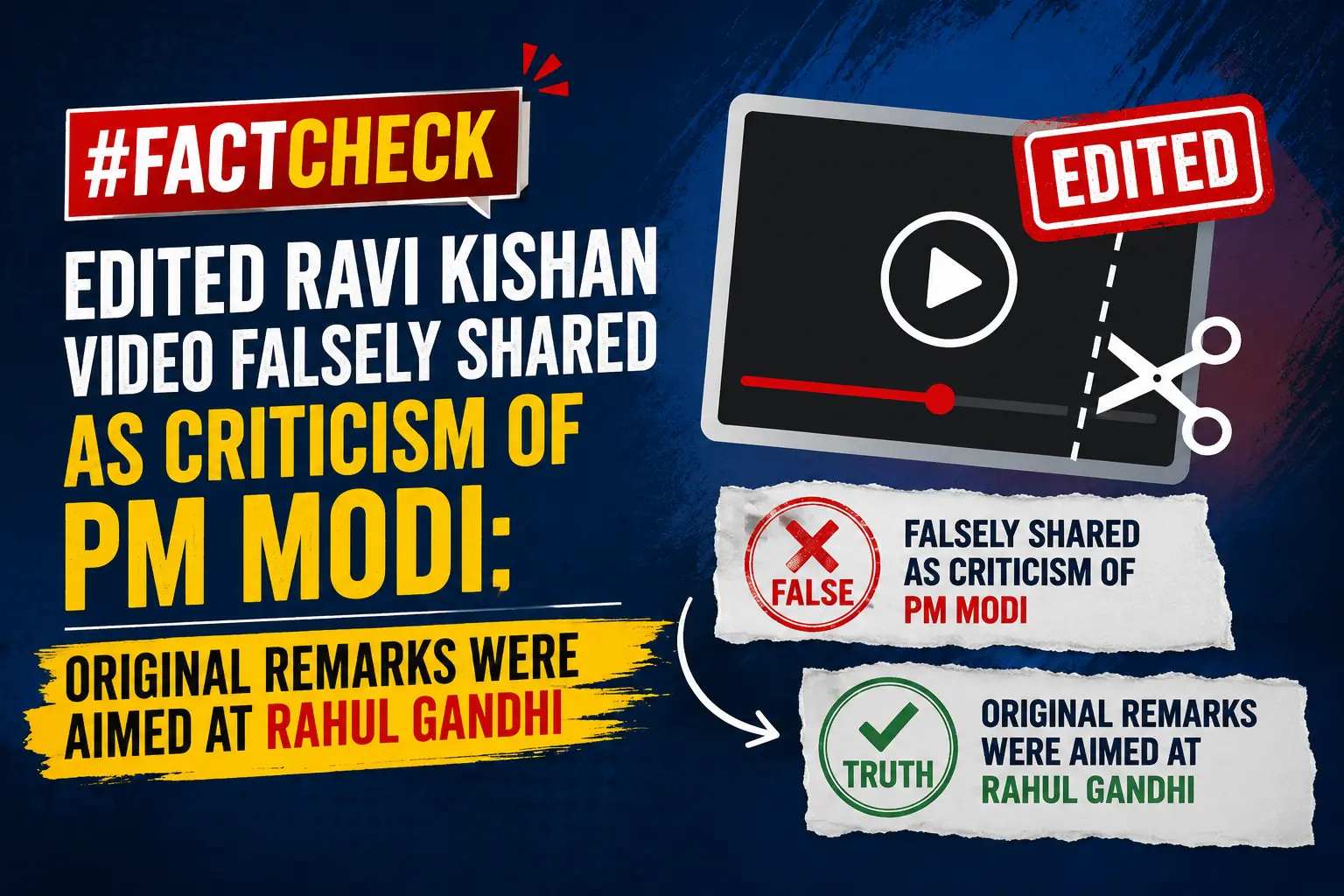
Executive Summary
A video of BJP MP Ravi Kishan is being widely circulated on social media with the claim that the Gorakhpur MP was mocking Prime Minister Narendra Modi and criticizing his working style and frequent foreign visits.In the viral clip, Ravi Kishan can be heard saying that “he likes to travel,” “comes to Parliament only for a few minutes,” and does not like pressure or responsibility. The clip also features him using phrases such as “azad panchhi” (free bird) and “azad parinda.” However, CyberPeace Research Wingresearch found the claim to be misleading. The research revealed that in the original video, Ravi Kishan was actually criticizing Congress leader Rahul Gandhi. A cropped portion of his statement is being shared out of context with a false claim.
Claim
An X (formerly Twitter) user shared the viral clip and wrote that Ravi Kishan was referring to Prime Minister Narendra Modi, alleging that Modi enjoys travelling abroad, spends little time in Parliament, and feels uncomfortable under pressure.
- https://x.com/Aarti202/status/2058523226305900586
- https://archive.ph/j5MaV

Fact Check
To verify the viral claim, we performed a reverse search using key frames from the video. During the research, we found the original video uploaded on the Facebook page of ANI on May 13, 2026.
The caption of the post read:“War does not seem to be ending…” Ravi Kishan warns the country about the ongoing conflict in the Middle East.At around the 4-minute-40-second timestamp, an ANI reporter asks Ravi Kishan about Rahul Gandhi distancing himself from the CBI Director selection process. Responding to that question, Ravi Kishan makes the remarks that later went viral.
This clearly establishes that Ravi Kishan was not referring to Prime Minister Narendra Modi, but was commenting on Rahul Gandhi. In his response, he says that “it is good that he has freed himself” and refers to Rahul Gandhi as an “azad parinda” (free bird).
During the research, we also found the same video posted on Ravi Kishan’s official X account on May 23. The caption of the post stated:“Congress should now free its prince Rahul Gandhi.”This further confirms that the viral clip has been misleadingly edited and shared out of context

Conclusion
The research found that Ravi Kishan’s remarks in the original video were directed at Rahul Gandhi, not Prime Minister Narendra Modi. An edited portion of the video has been falsely shared with a misleading claim.

Introduction
The enactment of the Online Gaming (Promotion and Regulation) Act, 2025 has a significant impact, resulting in considerable changes to the structure of the Indian gaming industry. The ban on Real-Money Games (RMG), including fantasy sports, rummy, and poker, aims to curb addiction, illegal betting and most importantly, financial exploitation.
However, this decision sent ripples throughout the industry, resulting in players, companies and their investors re-strategising their plans to move forward. This approach, however, is a sharp contrast to how other nations, including the UK, Singapore and others, regulate online gaming. This, as a result, has also raised doubts about the ban and calls into question whether this is the right move.
Industry in Flux - The resultant Fallout
- MPL’s Layoffs: The Mobile Premiere League has so far laid off nearly 60 per cent of its workforce, with the CEO of the company openly admitting that the company is no longer able to make money in India.
- Dream11’s Lost Revenue: Having seen a position of being a market leader, the company has now witnessed its 95 per cent revenue wiped out, resulting in raised alarms among investors.
- A23’s Legal Move: The company chose to move the Karnataka High Court under the argument that the ban also ends up unfairly criminalising skill-based games that were earlier classified differently from gambling by the courts.
The new face of eSports: With RMGs outlawed, the focus is now on esports, including casual mobile gaming, console/PC gaming, and creating new opportunities and also leaving a void for RMG revenue companies.
Regulations Around the World - & India
India has adopted a prohibition model, whereas many other countries have developed regulatory frameworks that allow sectoral expansion under monitoring.
United Kingdom:
- Online gaming is regulated by the UK Gambling Commission.
- RMGs are legal but subject to strict licensing, age verification and advertising rules.
- Self-exclusion schemes are a must, offered by operators along with tools to prevent gambling addictions.
United States
- State-driven regulations that vary from state to state.
- States including Nevada and New Jersey allow casinos both online and offline, while other states prohibit them completely.
- Regulation for skill-based fantasy games is fragmented but generally legal.
China
- Great focus on controlling and restricting gaming addictions among minors.
- Time limits are enforced for players under 18 (usually as little as 3 hours per week).
- Gambling has been deemed illegal; however, esports and casual gaming operate within China’s regulated gaming ecosystem, subject to certain compliance.
Singapore
- The Remote Gambling Act regulates chance-based games, while other eSports and skill-based games operate out of its jurisdiction and are regulated separately.
- Online gambling isn't completely banned, but is operated under restrictions.
- Only Licensed operators under strict controls are allowed by the government to operate to avoid and prevent black-market alternatives.
Australia
- Regulates under the Interactive Gambling Act.
- Sports betting and certain licensed operators are allowed, while most of the other online gambling services are prohibited.
- Restrictions on advertising and real-time interventions allow emphasis on harm minimisation.
India’s Approach - Comparison
The Online Gaming (Promotion and Regulation) Act, 2025 introduces a prohibition model for real money games. This differs from jurisdictions such as the UK and US, which have implemented regulatory frameworks to oversee the sector. In India, earlier legal interpretations distinguished between games of skill and games of chance. The new legislation provides a single treatment for both categories, which marks a departure from previous judicial pronouncements.
Conclusion
At present, India’s gaming sector is navigating layoffs, court cases, and a pivot towards esports post the RMG ban. Keeping in mind that the intent of said ban is the protection of citizens, the industry also argues that regulation, instead of prohibition, offers a sustainable approach to the issues. On the other hand, on the global scale, most nations prefer controlled and licensed models that ensure consumer safety and work on preserving both jobs and revenues. However, India’s step is diverging from such a model. The lack of safeguards and engagement in the real money gaming industry led to a prohibition model, underscoring that in sensitive digital sectors, early regulatory alignment is essential.
References
- India online gaming ban: Global rules & regulation bill 2025
- Level up or game over? Decoding India’s gaming industry post RMG ban
- MPL lays off 350 employees after GST rules, RMG crackdown
- India’s Dream11 hit by online gaming ban, revenue slumps
- Online gaming ban: A23 moves Karnataka HC against government decision
- UK Gambling Commission – Licensing and Regulations
- Fantasy Sports & Gambling Law – State by State
- China’s gaming restrictions for minors
- Singapore Remote Gambling Act – Ministry of Home Affairs
- Australian Communications and Media Authority – Interactive Gambling Act


