#Fact Check: Old Photo Misused to Claim Israeli Helicopter Downed in Lebanon!
Executive Summary
A viral image claims that an Israeli helicopter shot down in South Lebanon. This investigation evaluates the possible authenticity of the picture, concluding that it was an old photograph, taken out of context for a more modern setting.

Claims
The viral image circulating online claims to depict an Israeli helicopter recently shot down in South Lebanon during the ongoing conflict between Israel and militant groups in the region.


Factcheck:
Upon Reverse Image Searching, we found a post from 2019 on Arab48.com with the exact viral picture.



Thus, reverse image searches led fact-checkers to the original source of the image, thus putting an end to the false claim.
There are no official reports from the main news agencies and the Israeli Defense Forces that confirm a helicopter shot down in southern Lebanon during the current hostilities.
Conclusion
Cyber Peace Research Team has concluded that the viral image claiming an Israeli helicopter shot down in South Lebanon is misleading and has no relevance to the ongoing news. It is an old photograph which has been widely shared using a different context, fueling the conflict. It is advised to verify claims from credible sources and not spread false narratives.
- Claim: Israeli helicopter recently shot down in South Lebanon
- Claimed On: Facebook
- Fact Check: Misleading, Original Image found by Google Reverse Image Search
Related Blogs

Executive Summary:
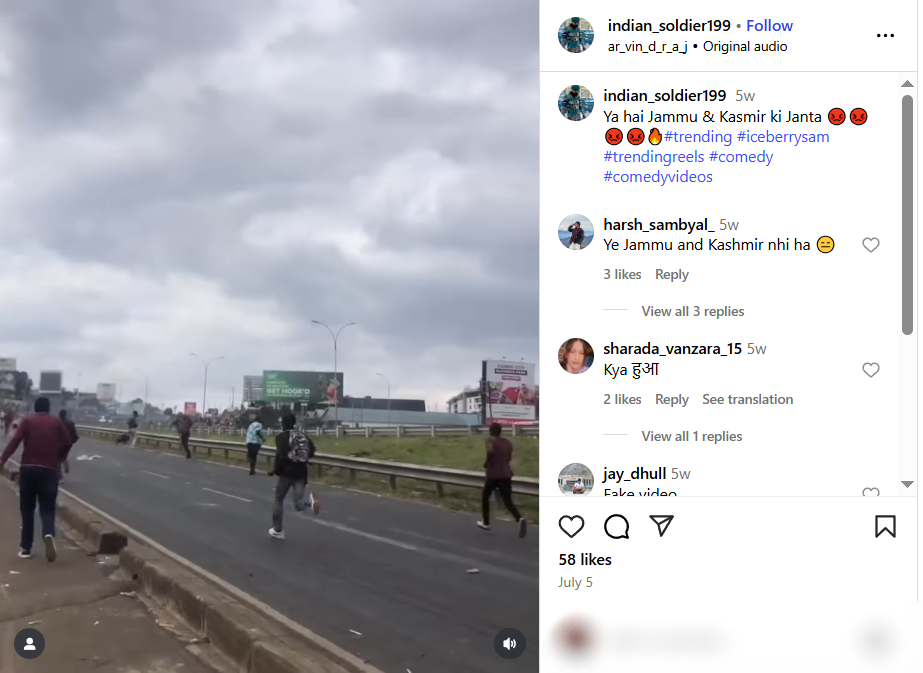
A video of people throwing rocks at vehicles is being shared widely on social media, claiming an incident of unrest in Jammu and Kashmir, India. However, our thorough research has revealed that the video is not from India, but from a protest in Kenya on 25 June 2025. Therefore, the video is misattributed and shared out of context to promote false information.

Claim:
The viral video shows people hurling stones at army or police vehicles and is claimed to be from Jammu and Kashmir, implying ongoing unrest and anti-government sentiment in the region.
Fact Check:
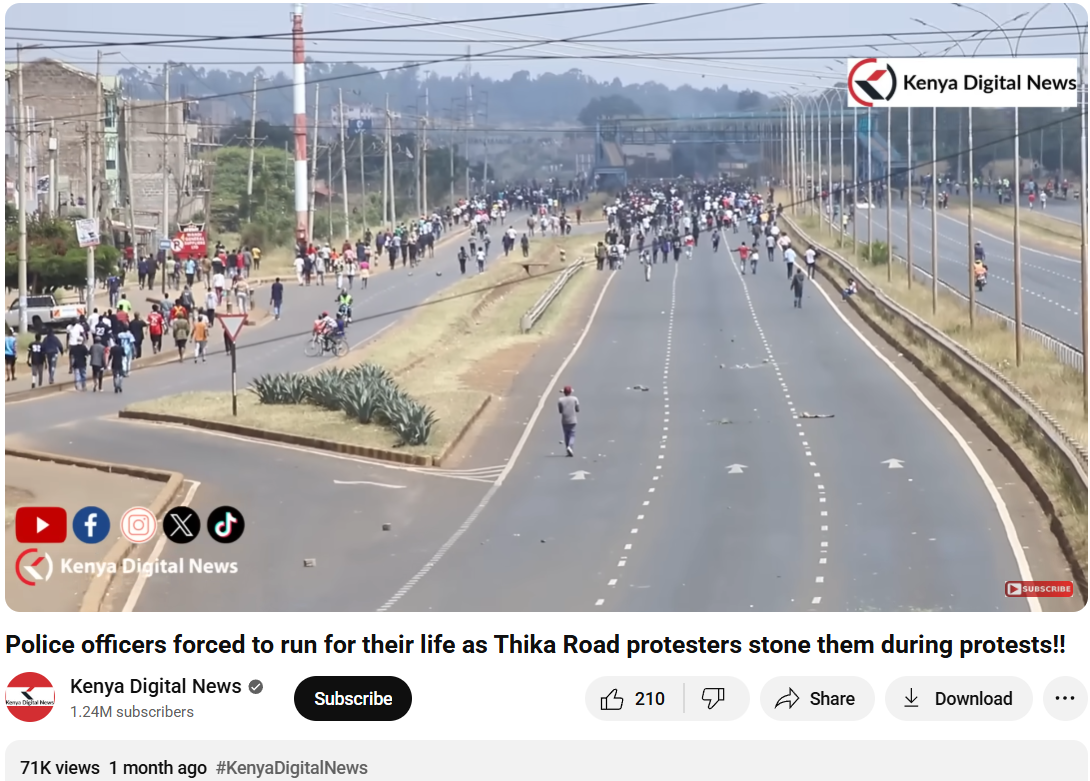
To verify the validity of the viral statement, we did a reverse image search by taking key frames from the video. The results clearly demonstrated that the video was not sourced from Jammu and Kashmir as claimed, but rather it was consistent with footage from Nairobi, Kenya, where a significant protest took place on 25 June 2025. Protesters in Kenya had congregated to express their outrage against police brutality and government action, which ultimately led to violent clashes with police.

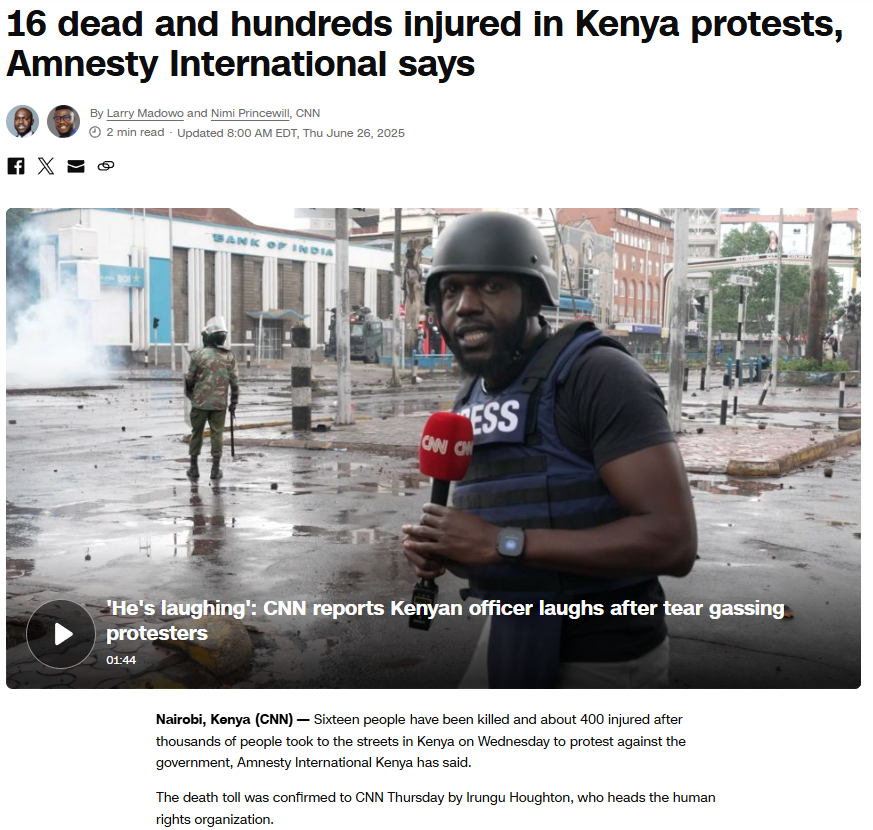
We also came across a YouTube video with similar news and frames. The protests were part of a broader anti-government movement to mark its one-year time period.
To support the context, we did a keyword search of any mob violence or recent unrest in J&K on a reputable Indian news source, But our search did not turn up any mention of protests or similar events in J&K around the relevant time. Based on this evidence, it is clear that the video has been intentionally misrepresented and is being circulated with false context to mislead viewers.
Conclusion:
The assertion that the viral video shows a protest in Jammu and Kashmir is incorrect. The video appears to be taken from a protest in Nairobi, Kenya, in June 2025. Labeling the video incorrectly only serves to spread misinformation and stir up uncalled for political emotions. Always be sure to verify where content is sourced from before you believe it or share it.
- Claim: Army faces heavy resistance from Kashmiri youth — the valley is in chaos.
- Claimed On: Social Media
- Fact Check: False and Misleading
.webp)
Introduction
The digital communication landscape in India is set to change significantly as the Department of Telecommunications is preparing to implement new rules for messaging apps that operate using SIM cards. This step is part of the government’s effort to tackle cybercrime at its roots by enforcing stricter verification and reducing the number of communication platforms that can be misused. One clear change that users will notice is that WhatsApp Web sessions will now be automatically logged out every six hours, disrupting the previously uninterrupted use across multiple devices. Although this may appear to be a simple inconvenience, the measure is part of a broader plan to address the growing problem of cyber fraud. Cybercriminals exploit messaging apps like WhatsApp without keeping the registered SIM in the device, making it difficult to trace fraud. These efforts are surely gonna address these challenges at the root.
The Incident: What Has Changed?
The new regulations will make it mandatory for messaging platforms to create a direct link between user accounts and verified SIM identities. By this method, every account in the network can be associated with a valid and traceable mobile number. Because of this requirement, it is expected that WhatsApp is going to tighten the management of device sessions. The six-hour logout cycle for WhatsApp Web is implemented to prevent long-lived and unmonitored sessions that are sometimes taken advantage of in account takeovers, device-based breaches, and remote access scams. This change significantly affects the user experience. WhatsApp Web, often used for communication, customer support, and coordination, will now require more frequent authentication through mobile devices. Though mobile access remains uninterrupted, desktop and browser-linked sessions will be subjected to tighter security controls.
Why Identity-Linked Messaging Matters
India is facing a rapidly evolving cybercrime ecosystem in which messaging applications play a central role. Scammers often rely on fake, unverified, or illegally obtained SIM cards to create temporary accounts that can be used for various illegal activities, such as sending phishing messages, impersonating government officials, and deceiving victims through call centres set up for scams.
The new rules take into consideration the following main issues:
- Anonymity of accounts makes large-scale fraud possible: Criminals operate bulk scams using hundreds of SIM-linked accounts.
- Freedom to drop identities: Illegal SIMs are discarded after fraud, making it difficult for the police to trace the criminals.
- Multi-device vulnerabilities that last for a long time: Access without permission to WhatsApp Web sessions that last for a long time is seen as the main reason for OTP theft, account hijacking, and on-device social engineering.
The government wants to disrupt these foundations by enforcing stricter traceability.
A Sector Under Strain: Misuse of Messaging Platforms
Messaging apps have turned out to be the most important thing in India's digital life, from communication to enterprise. This very widespread use of messaging apps has made them an easy target for cybercriminals.
The scams that are frequently visible are:
- WhatsApp groupsare used for job and loan scams
- False communication from banks, government departments, and payment applications
- Sextortion and blackmail through unverified accounts
- Remote-access fraud with attackers who are watching WhatsApp Web sessions
- Coordinated spread of false information and distribution of deepfake videos
The employment of AI-generated personas and "SIM farms" has made it harder to secure the systems even more. Unless there is a very strict linking of users to authenticated SIM credentials, the platforms might degenerate into uncontrollable rafts of cybercrime.
Government and Regulatory Response
The Department of Telecommunications is initiating a process of stricter compliance measures and cooperating with the Ministry of Home Affairs, along with the Indian Cyber Crime Coordination Centre. The main points of the directions include the following:
- Identity verification linked to a SIM is mandatory for the creation of messaging accounts
- Device re-authentication on platforms often starts with WhatsApp Web
- Coordination with the telecom operators to the extent of getting suspicious login patterns
- Protocols for the sharing of data with law enforcement in the course of cybercrime investigations
- Compliance checks of digital platforms to verify adherence to national safety guidelines
This coordinated effort reflects the understanding that the security of communication platforms is the responsibility of both the regulators and the service providers.
The Bigger Picture: Strengthening India’s Digital Trust
The fresh regulations are in step with the worldwide trend where the platforms of messaging have to be more responsible, as governments are demanding more and more from them. The same discussions are going on in the EU, UK, and certain Southeast Asian regions.
For India, it is imperative to enhance identity management because:
- The nation has the largest base of messaging users in the whole world
- Cybercrime is increasing at a rate quicker than that of traditional crime
- Digital government services rely on communications that are secure
- Identity integrity is the basis for trust in online transactions and digital payments
The six-hour logout policy for WhatsApp Web is a small action, but it is an indication of a bigger transformation towards a regulation that is active rather than just policing that is reactive.
What Needs to Happen Next?
The implementation of SIM-linked regulations must involve several subsequent measures to make them effective.
- Strengthening Digital Literacy: It is necessary to educate users about the benefits of frequent logouts and security improvements.
- Ensuring Privacy Protections: The DPDP Act should create a strong barrier against the misuse of personal data in identity-linked messaging that will be implemented.
- Collaboration with Platforms: Messaging services should seek to secure authentication under the compromise of safety checks.
- Monitoring SIM fraud at the source: Illicit SIM provisioning enforcement is the main source of criminals, not just changing their methods.
- Continuous Review and Feedback: Policymaking needs to keep pace with real-life difficulties and new inventions in technology.
Conclusion
India's announcement to impose regulations on messaging apps with SIM linkage is a major step forward in preventing cybercrime from occurring in the first place. Although the immediate effect, like the six-hour logout requirement for WhatsApp Web, may annoy users, it is nevertheless part of a bigger goal: to develop a more secure and trustworthy digital communication environment.
Securing the communication that links millions of people is vital as India becomes more and more digital. Through a combination of regulatory measures, technological protection, and user education, the country is headed toward a time when criminals in the cyber world will find it very difficult to operate and where consumers will be able to interact online with much more confidence and safety.
References
- https://thehackernews.com/2025/12/india-orders-messaging-apps-to-work.html
- https://indianexpress.com/article/explained/explained-sci-tech/whatsapp-web-automatic-log-out-six-hourse-reason-10394142/
- https://www.ndtv.com/india-news/explained-how-will-new-sim-binding-rule-affect-whatsapp-signal-telegram-9728710
- https://www.hindustantimes.com/india-news/no-whatsapp-without-active-sim-centre-issues-new-rules-dot-sim-binding-prevent-cyber-crimes-101764495810135.html

A video clip of journalist Palki Sharma is being widely shared on social media. Along with the video, it is being claimed that during Prime Minister Narendra Modi’s recent Middle East visit, she questioned Jordan’s diplomatic protocol.
In the viral clip, Palki Sharma is allegedly seen asking why Jordan’s King Abdullah II did not come to the airport to receive Prime Minister Modi, and whether this indicated a downgrade in the level of welcome.
However, an investigation by the Cyber Peace Foundation found this claim to be misleading. The probe revealed that while the visuals in the viral video are genuine, the audio has been altered using Artificial Intelligence (AI).
On the social media platform ‘X’, a user named “Ammar Solangi” shared this video on 18 December. The post claimed that the video was related to questions raised about Jordan’s diplomatic protocol during Prime Minister Modi’s visit. According to the post, Palki Sharma questioned why King Abdullah II did not receive Prime Minister Modi at the airport. The archive link of the viral post can be seen here: https://ghostarchive.org/archive/26aK0
Verification
During the investigation, the fact-check desk noticed the ‘Firstpost’ logo in the top-left corner of the viral video. Based on this clue, a customized Google search was conducted, which led to the original news report.
The investigation revealed that the viral video was taken from an episode of journalist Palki Sharma’s show “Vantage with Palki Sharma”, which aired on 17 December.
Analysis of the video showed that the visuals appearing at the 33 minutes 30 seconds timestamp in the original report exactly match those used in the viral clip. However, in the original broadcast, Palki Sharma neither questioned Jordan’s protocol nor made any comment about King Abdullah II not being present at the airport.
In the original video, Palki Sharma says:
“Prime Minister Modi was on a diplomatic tour of Jordan, Ethiopia, and Oman, and in Jordan he was received at the airport by the country’s Prime Minister…” The link to the original report can be seen here: https://www.youtube.com/watch?v=-VYZYe9l6Bs
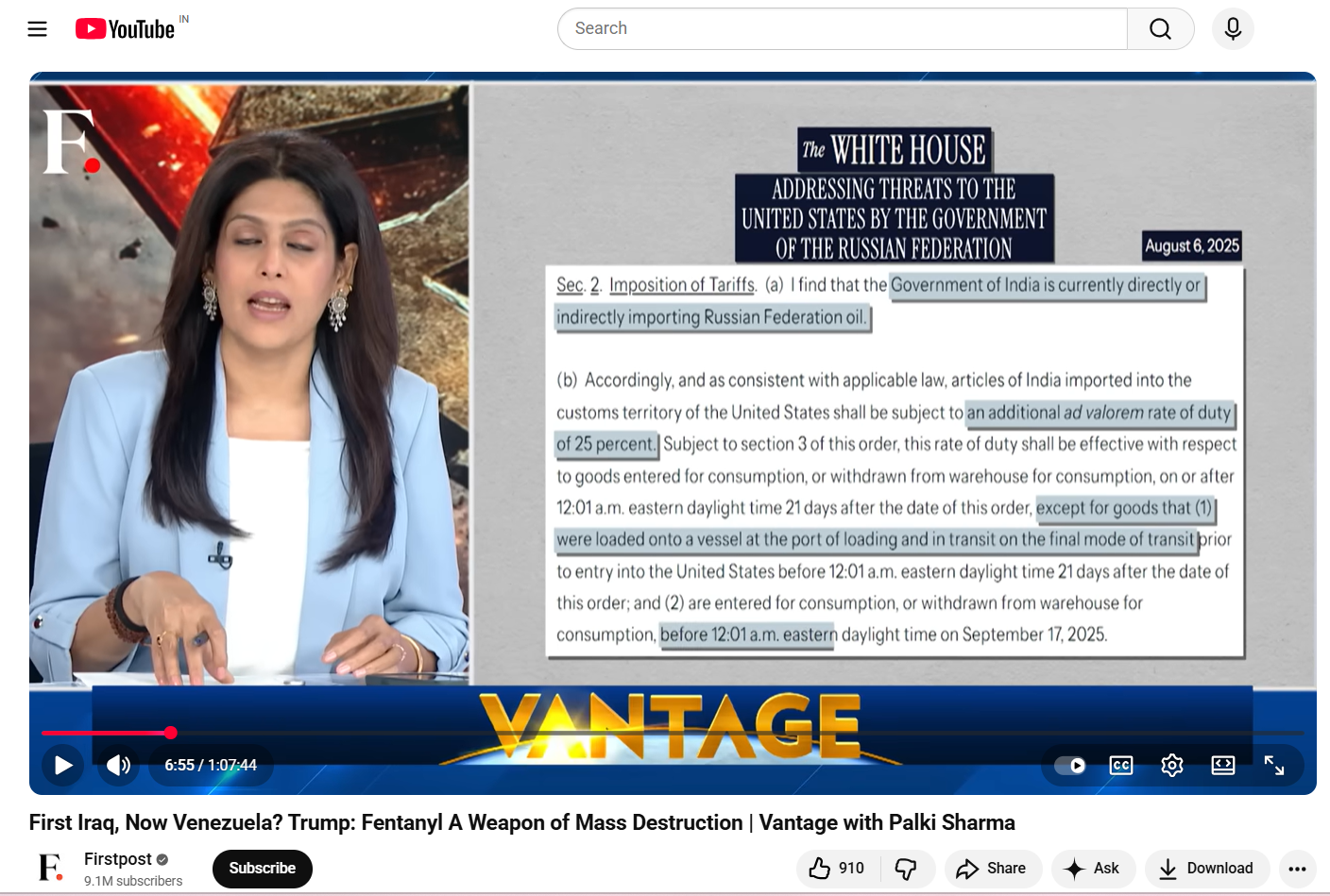
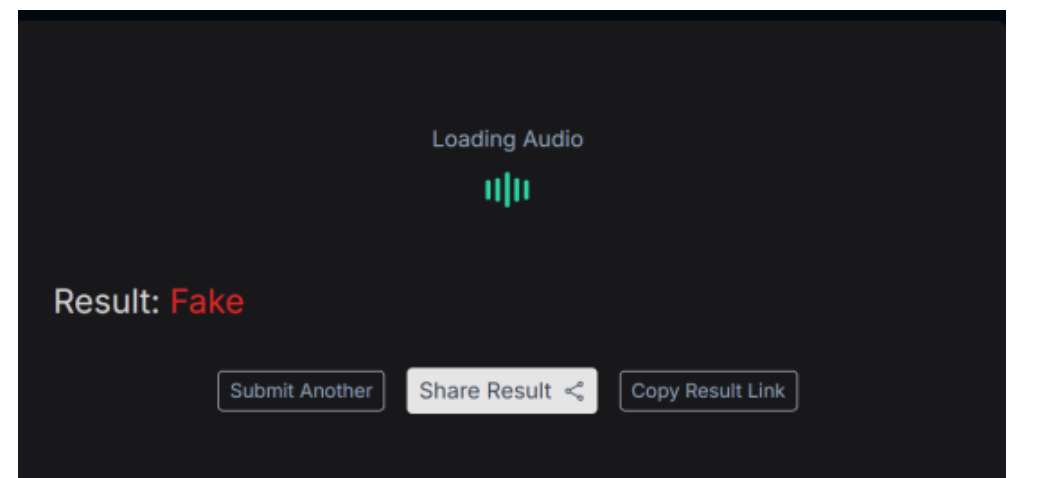
AI Audio Examination
Further investigation involved separating the audio from the viral video and analyzing it using the AI voice detection tool ‘Resemble AI’. The tool’s results confirmed that fake, AI-generated audio had been added over the real footage in the viral clip to spread a misleading claim. A screenshot of the results from this examination can be seen below.
Conclusion
The video being circulated in the name of journalist Palki Sharma has been tampered with. Her voice has been altered using AI technology, and the claim made regarding the Jordan visit is completely misleading.


