Best Practices for Citizens to Withstand Misinformation and Fake News Campaigns in the Aftermath of the Red Fort Blast
Introduction
After the tragic bomb blast at RedFort on November 10, 2025, there is a trail of misinformation and false narratives spread rapidly across social media platforms, messaging and news channels. It can not only unfold into a public misunderstanding but can also incite panic, communal tensions and endanger lives. To prevent all of these from happening, we, as responsible citizens, can play a critical role by verifying information before sharing it with friends, family, or colleagues. This article provides guidance on practical, evidence-based strategies to navigate the information landscape and protect yourself and your community from the harm caused by misinformation and disinformation.
Digital Scams in the Aftermath of the Blast
Cybercriminals increased their activity in the hours after the Red Fort explosion, using the country’s sorrow as a chance to take advantage of fear.
Numerous allegations surfaced of residents receiving threatening calls that falsely claimed they were “digitally arrested” or that their phones, bank accounts, or Aadhaar were being “seized for investigation”, accusing them of being involved in the explosion. These fictitious intimidation calls sent innocent people into worry, anxiety, and doubt spirals.
The pattern is common after major national crises:
- Fear rises.
- People seek urgent answers.
- Cybercriminals exploit the confusion.
Knowing this makes it easier for us to remain watchful. No law enforcement organisation uses phone conversations, WhatsApp communications, or threats of “digital detention” to make arrests or conduct investigations.
Verify breaking news from trusted official channels
Whenever a crisis like bomb blasts occurs, people look for information on social media, news channels, and YouTube channels to stay fully informed about the situation. This is a very chaotic moment, and due to the lack of government verification of the initial information, false news spread rapidly.
Where to seek verified information:
a. Press Information Bureau (PIB): The official government news agency that, from time to time, clarifies viral news.
b. Delhi Police Official Channels: Check social media handles of Delhi Police.
c. Ministry of Home Affairs (MHA): MHA is responsible for internal security, and gives information about this information through official press releases and notifications.
d. Major Credible news outlets: Some news channels can be trusted with news, as they typically verify information before publishing, like The Hindu, Indian Express.
What to do:
Cross-check every unverified social media post and news that you come across from credible news channels and official government press releases.
Verify Images and videos using reverse search tools
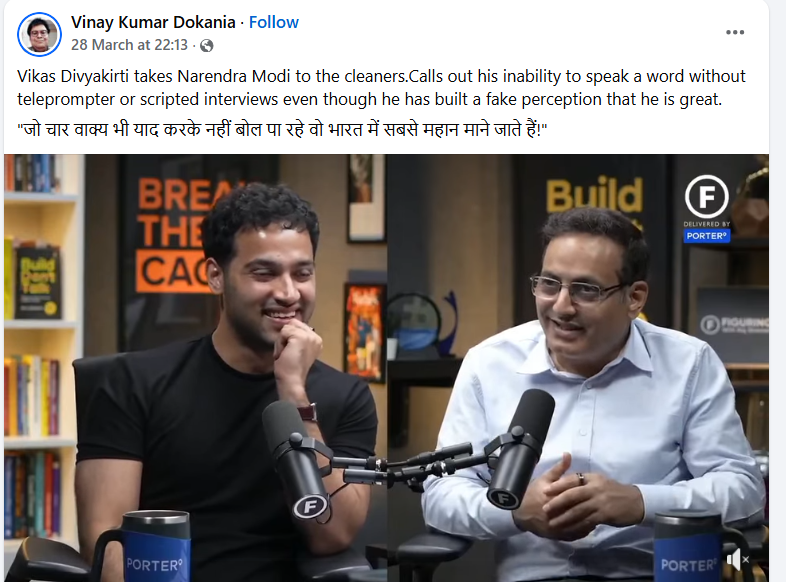
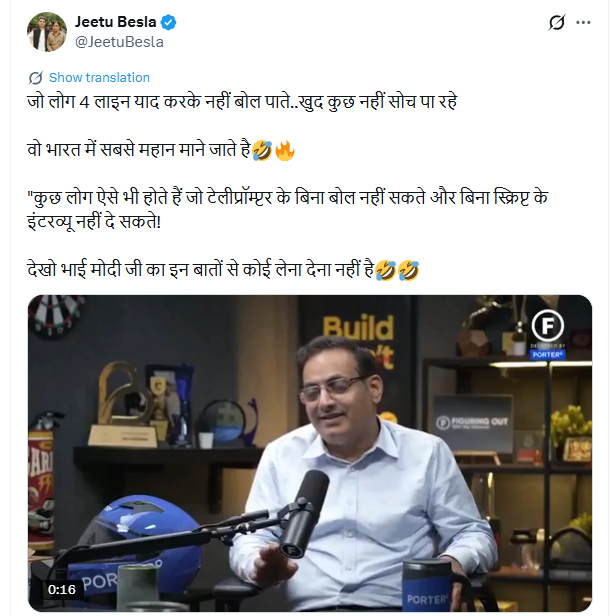
Recently, many social media handles have been sharing old photos of different bomb blasts from Ukraine, Israel, and Palestine in the name of the Red Fort blasts. While it can create a false narrative, the same should be verified before sharing.
Reliable fact-checking resources and how to use them.
Every country has dedicated fact-checking organisations that systematically verify viral claims.
Fact-checking organisations based in India:
a. PIB Fact Check (https://factcheck.pib.gov.in/ )
· It is the official fact-checking unit of the PIB, which focuses on demystifying government-related misinformation.
· email: socialmedia@pib.gov.in
· Telegram: http://t.me/PIB_FactCheck
· Follow it on: Twitter (@PIBFactCheck), Facebook, Instagram, Telegram and WhatsApp.
How to use these resources:
· Whenever you come across any viral post, use exact keywords or quotes to find those on these resources.
· Look for the verdict (true, false, misleading), then share the verified fact-checks with your network to debunk false narratives.
Practice Digital Hygiene and Be Cautious When Sharing
Digital hygiene refers to the practices and habits individuals adopt to maintain a healthy and secure digital lifestyle. Simple digital practices can restrict the spread of misinformation. A vigilant individual can reduce the spread of misinformation. It can be done by below steps
i. Check URLs and Links: We can verify the URLs and links of any news and websites using different tools to check the credibility of any news
ii. How to Evaluate the Trustworthiness of Sources:
· Verify if the account sharing the information has a blue checkmark on most platforms.
· Examine the account's background, whether it is a recognised media source, an official government profile, or a newly created anonymous account?
· Approach posts featuring intense emotional language ("URGENT!", "SHOCKING!", "MUST SHARE!") with scepticism.
· Refrain from posting screenshots of tweets or posts while providing a link to the source, allowing others to confirm its validity.
iii. Before You Distribute:
· Question yourself: "Am I certain this is accurate based on a reliable source?"
· Avoid the temptation to share breaking news immediately; hold off until it has been confirmed by government sources.
· If you're uncertain, include a comment such as "I haven't confirmed this yet; please consult reliable sources" instead of sharing unverified information.
· Reflect on the consequences, as it might lead to panic, provoke communal violence, or damage an individual's reputation
6. How to report misinformation to platforms and authorities?
While it is important to verify news before sharing it to prevent fake news, it is also important to report it to reduce misinformation and the violence caused due to it. On social media like Facebook, Instagram, Twitter/X, WhatsApp, and Telegram, anyone can report the same on the platform.
Reporting to the Government Authorities:
a. PIB Fact Check WhatsApp (+91 8799711259):
Send Screenshots or texts of suspected government-related misinformation for verification, and then an automated acknowledgement is generated.
b. Delhi Police Cyber Crime Unit
Cyber Crimes such as Email Frauds, Social Media Crimes, Mobile App-related crimes, Business Email Compromise, Data Theft, Ransomware, Net Banking/ ATM Frauds and fake calls frauds, insurance frauds, lottery scam, bitcoin, cheating scams, online transactions frauds can be reported to the Delhi Police Cyber Crime Unit.
7. Quick checklist: What to do When You See Breaking News
· Wait before sharing any breaking news.
· Go through official channels like PIB and other official channels like MHA.
· If not available there, then cross-reference it from 2-3 credible news sources for the same information.
· Check timestamps and metadata, and compare metadata dates with claims about when events occurred.
· In case you find any information, news or any social media posts as misleading, then report the same.
CyberPeace Resolves: Pause. Reflect. Then Respond
Misinformation becomes the infection that spreads the fastest when people are confused and afraid. Every citizen is urged by CyberPeace to remain composed, stand tall, and not panic, particularly in times of national emergency.
Prior to experiencing an emotional response to any concerning call, message, or widely shared news:
Pause. Reflect. Acknowledge.
- Pause before sharing or responding.
- Reflect on whether the information is from a credible source.
- Acknowledge what you know—and what is just rumour.
CyberPeace is still dedicated to helping people and communities deal with online dangers, safeguard mental health, and dispel false information with clarity and truth.