#FactCheck - AI-Generated Video of Monkey Falsely Linked to Hanuman Devotion
A video is being widely shared on social media showing a monkey, with users claiming that the animal is immersed in devotion to Lord Hanuman. The clip is being circulated with assertions that the monkey was seen participating in Hanuman Aarti. Cyber Peace Foundation’s research found that the viral claim is fake. Our investigation revealed that the video is not real and has been generated using artificial intelligence tools.
Claim
On January 6, 2026, Facebook users shared the viral video claiming, “A monkey was seen immersed in devotion during Hanuman Aarti.”
- Post link: https://www.facebook.com/reel/1261813845766976
- Archived link: https://archive.ph/anid5
Screenshots of the post can be seen below.

FactCheck:
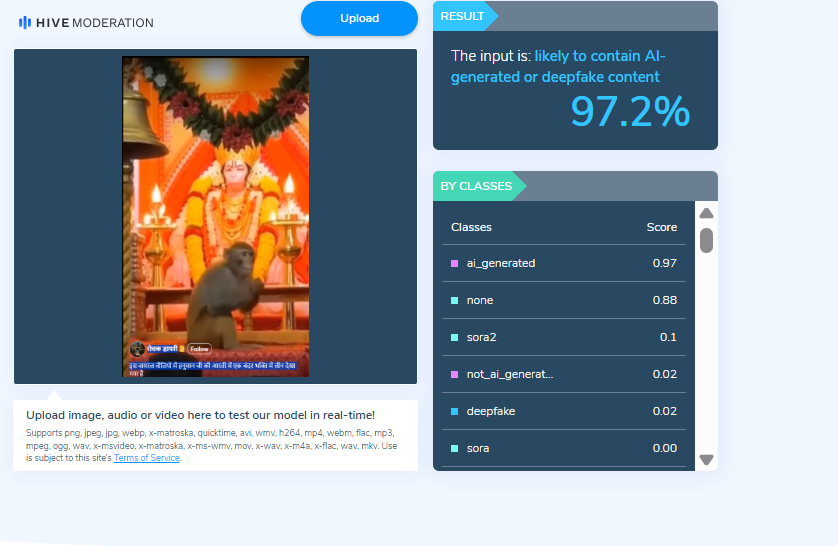
When we closely examined the viral video, we noticed several visual inconsistencies. These anomalies raised suspicion that the video might be AI-generated. To verify this, we scanned the video using the AI detection tool Hive Moderation. According to the results, the video was found to be 97 percent AI-generated.
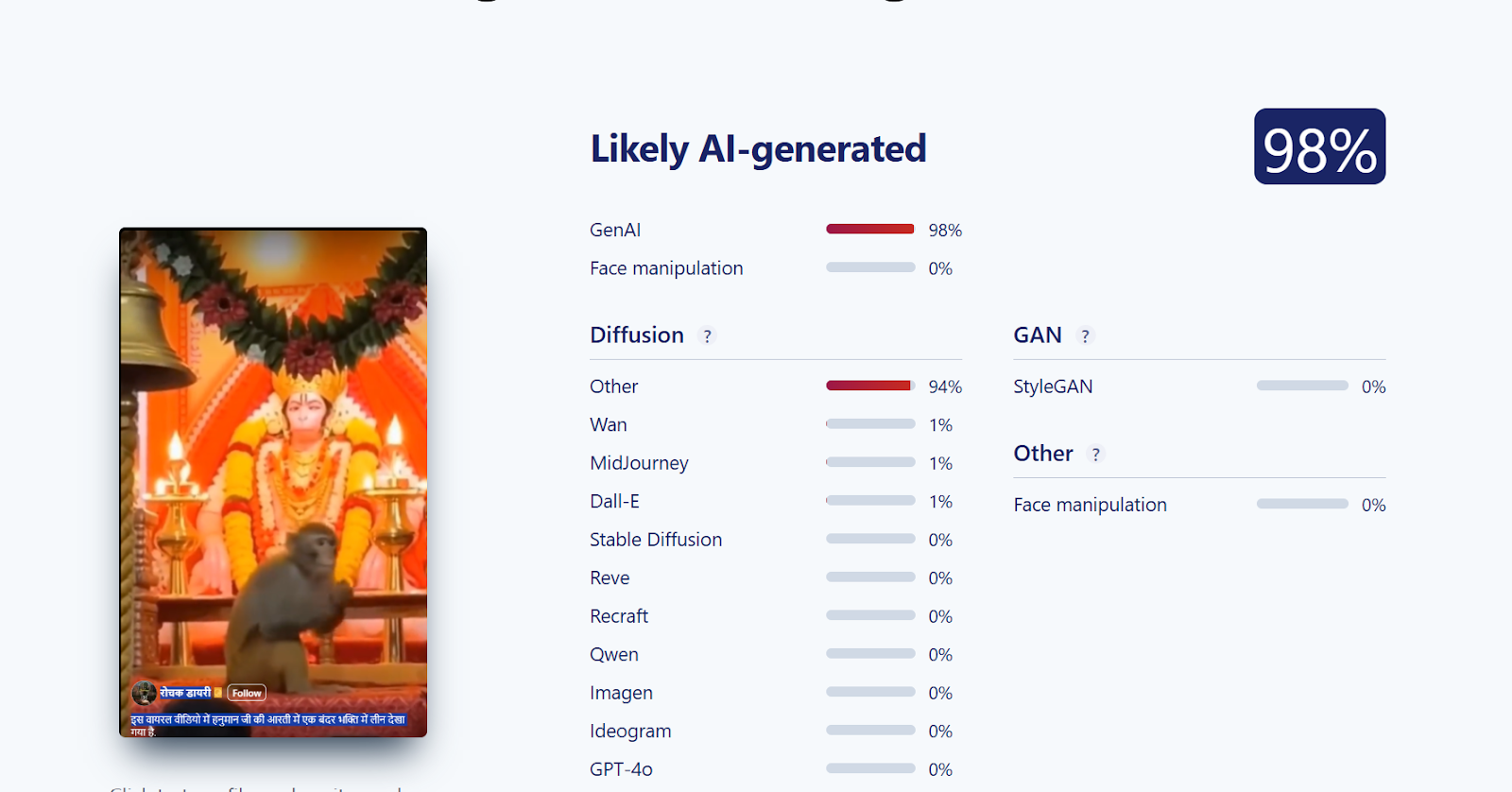
Further, we analysed the video using another AI detection tool, Sightengine. The tool’s assessment indicated that the viral video is 98 percent AI-generated.
Conclusion
Our investigation confirms that the viral video claiming to show a monkey immersed in devotion to Lord Hanuman is AI-generated and not real. The claim circulating on social media is false and misleading.
Related Blogs

Introduction
Social media has become integral to our lives and livelihood in today’s digital world. Influencers are now strong people who shape trends, views, and consumer behaviour. Influencers have become targets for bad actors aiming to abuse their fame due to their significant internet presence. Unfortunately, account hacking has grown frequently, with significant ramifications for influencers and their followers. Furthermore, the emergence of social media platforms in recent years has opened the way for influencer culture. Influencers exert power over their followers’ ideas, lifestyle choices, and purchase decisions. Influencers and brands frequently collaborate to exploit their reach, resulting in a mutually beneficial environment. As a result, the value of influencer accounts has risen dramatically, attracting the attention of hackers trying to abuse their potential for financial gain or personal advantage.
Instances of recent attacks
Places of worship
The hackers have targeted renowned temples for fulfilling their malicious activities the recent attack happened on The Khautji Shyam Temple, a famous religious institution with enormous cultural and spiritual value for its adherents. It serves as a place of worship, community events, and numerous religious activities. However, since technology has invaded all sectors of life, the temple’s online presence has developed, giving worshippers access to information, virtual darshans (holy viewings), and interactive forums. Unfortunately, this digital growth has also rendered the shrine vulnerable to cyber threats. The hackers hacked the Facebook page twice in the month, demanded donations and hacked the cheques the devotes gave to the trust. The second event happened by posting objectional images on the page and hurting the sentiments of the devotees. The Committee of the temple has filed an FIR under various charges and is also seeking help from the cyber cell.
Social media Influencers
Influencers enjoy a vast online following worldwide, but their presence is limited to the digital space. Hence every video, photo is of importance to them. An incident took place with leading news anchor and reporter Barkha Dutt, where in her youtube channel was hacked into, and all the posts made from the channel were deleted. The hackers also replaced the channel’s logo with Tesla and were streaming a live video on the channel featuring Elon Musk. A similar incident was reported by influencer Tanmay Bhatt, who also lost all the content e had posted on his channel. The hackers use the following methods to con social media influencers:
- Social engineering
- Phishing
- Brute Force Attacks
Such attacks on influencers can cause harm to their reputation, can also cause financial loss, and even lose the trust of the viewers or the followers who follow them, thus further impacting the collaborations.

Safeguards
Social media influencers need to be very careful about their cyber security as their prominent presence is in the online world. The influencers from different platforms should practice the following safeguards to protect themselves and their content better online
Secure your accounts
Protecting your accounts with passphrases or strong passwords is the first step. The best strategy for doing this is to create a passphrase, a phrase only you know. We advise choosing a passphrase with at least four words and 15 characters.
To further secure your accounts, you must enable multi-factor authentication in the second step.
To access your account, a hacker must guess your password and provide a second authentication factor (such as a face scan or fingerprint) that matches yours.
Be careful about who has access
Many social media influencers collaborate with a team to help generate and post content while building their personal brands.
This entails using team members who can write and produce material that influencers can share themselves, according to some of them. In these situations, the influencer is the only person who still has access to the account.
There are more potential weak spots when more people have access. Additionally, it increases the number of ways a password or account access could fall into the hands of a cybercriminal. Only some staff members will be as cautious about password security as you may be.
Stay up-to-date on the threats
What’s the most significant way to combat threats to computer security? Information.
Cybercriminals constantly adapt their methods. It’s crucial to stay informed about these threats and how they can be utilised against you.
But it’s not just threats. Social media platforms and other service providers are likewise changing their offerings to avoid these challenges.
Educate yourself to protect yourself. You can keep one step ahead of the hazards that cybercriminals offer by continuously educating yourself.
Preach cybersecurity
As influencers, cyber security should be preached, no matter your agenda.
This will also enable users to inculcate best practices for digital hygiene.
This will also boost the reporting numbers and increase population awareness, thus eradicating such bad actors from our cyberspace.
Acknowledge the risks
Keeping a blind eye will always hurt the safety aspects, as ignorance always causes issues.
Risks should be kept in mind while creating the digital routine and netiquette
Always inform your users of risk existing and potential risks
Monitor threats
After the acknowledgement, it is essential to monitor threats.
Active lookout for threats will allow you to understand the modus Operandi and the vulnerabilities to avoid criminals
Threats monitoring is also a basic netizens’ responsibility to ensure that the threats are reported as they emerge.
Interpret the data
All cyber nodal agencies release data and trends of cybercrimes, understand the trends and protect your vulnerabilities.
Data interpretation can lead to an early flagging of threats and issues, thus protecting the cyber ecosystem by and large.
Create risk profiles
All influencers should create risk profiles and backup profiles.
This will also help protect one’s data as it can be stored on different profiles.
Risk profiles and having a private profile are essential to safeguard the basic cyber interests of an influencer.

Conclusion
As we go deeper into the digital age, we see more technologies emerging, but along with them, we see a new generation of cyber threats and challenges. The physical, as well as the cyberspace, is now inter twinned and interdependent. Practising basic cyber security practices, hygiene, netiquette, and monitoring best practices will go a long way in protecting the online interests of the Influencers and will impact their followers to engage in best practices thus safeguarding the cyber ecosystem at large.

Introduction
Emerging technologies in the digital era have made their inroads in manifold domains and locations, including the “Aviation industry”. A 2022 Cranfield University and Inmarsat report has made the point for digitalization powering a reviving age for the aviation industry. Several airport authorities are presently mobilizing power of emerging technologies such as Artificial Intelligence (AI) across the airport bedrock to provide travelers with a plain sailing and expeditious air travel experience.
The Perils of Juice-Jacking
Today, Universal Serial Bus (USB) charging ports are ubiquitous and a convenient way for travelers to keep their devices powered up. In their busy, mundane lives, people use the public charging facility while travelling. However, cybersecurity experts have warned that charging in public areas could wipe off data from an electronic device or install malware, and they have urged people to stay away from USB charging ports at airports and other public areas. This leads to the possibility that fraudsters may manipulate susceptible users via juice jacking.
Investigative journalist Brian Krebs in 2011 coined the term "Juice Jacking". It isa form of cyber attack where a public USB charging port is fiddled with and infected using hardware and software changes to pocket data or install malware on devices connected to it. The term “juice jacking” is a slang representation for electric power or energy, and “hijacking” indicates an unauthorized key toa device.
While the preliminary purpose of juice jacking is usually to pilfer sensitive information from corresponding devices, such as passwords and payment card details, attackers can exploit this stolen information to attain unauthorized to your financial accounts. If the adversary attacker installs malware in the electronic device during the juice jacking strategy, the attacker may further observe the individual's movements even after one has disconnected the device from the USB port. However, the hazards of Juice Jacking include malware infection, data heist, economic loss and damage to the reputation of an individual.
RedFlags from Agencies
In2023, the Federal Bureau of Investigation (FBI) forewarned travelers against using charging stations in public zones such as hotels, airports, and shopping malls due to malicious actors attempting to use the public USB to introduce monitoring software and malware into devices. The U.S. Federal Communications Commission (FCC) has also administered a new advisory regarding “juice jacking "and its possibility of launching a hushed cyber attack against a mobile gadget while one is charging the phone with a USB cord. Similarly, according to new research from International Business Machines (IBM) Security, many nation-state hackers are currently training their eyes on travelers.
RBI Advisory
Recently in 2024, The Reserve Bank of India (RBI) has likewise administered a warning statement to mobile phone users urging them against charging their devices using public ports. RBI has additionally accentuated the importance of safeguarding private and financial data while using mobile devices. Juice jacking is further cited as one of the scams in the RBI booklet on the modus operandi of financial fraudsters in the financial space.
Preventing juice jacking attacks
The routes to avoid Juice Jacking are to keep a tab on the USB devices, not use the public charging ports, update the phone software regularly, enable and utilize the software security measures of the device, use a USB pass-through device, a wall outlet, or a backup battery; never use unknown charging cables and use only the trusted security apps. It is further important to avoid using cables that are left behind by other travelers in any public space. Users can correspondingly turn off their devices before connecting to a wary charging port. Nevertheless, the absence of documented cases does not necessarily imply that users cannot be a target of such an attack and a warning is still recommended when securing personal gadgets with susceptible user data while using standard cables. Also, using a virtual private network (VPN) and assuring that devices have the updated security updates established can aid in mitigating the danger of cyber attacks. It is equally important to utilize the security features of your device, such as passcodes, fingerprints, or facial recognition, enabled to count as a supplementary layer of safeguard.
Conclusion
In the contemporary digital age, individuals, on the whole, need to be vigilant about “Cybersecurity hygiene” and avoid accessing susceptible data or conducting financial transactions on unsecured networks. Mobile phones or devices should run on the latest operating system, and antivirus software should be revamped to mitigate conceivable security susceptibilities.
References
- https://www.forbes.com/sites/suzannerowankelleher/2023/04/20/juice-jacking-malware-phone-airports-hotels/?sh=47adab7e82ed
- https://www.businessairportinternational.com/features/how-ai-is-improving-business-aviation-operations.html
- https://www.news18.com/business/juice-jacking-attack-scam-bank-frauds-india-8412037.html
- https://www.comparitech.com/blog/information-security/juice-jacking/
- https://blogs.blackberry.com/en/2023/04/juice-jacking-advisory
- https://www.thehindubusinessline.com/info-tech/juice-jacking-rbi-issues-warning-against-charging-mobile-phones-using-public-ports/article67895091.ece
- https://www.thehindu.com/sci-tech/technology/juice-jacking-how-hackers-target-smartphones-tethered-to-public-charging-points/article67026433.ece
- https://www.forbes.com/sites/suzannerowankelleher/2019/05/21/why-you-should-never-use-airport-usb-charging-stations/?sh=630f026a5955
- https://edition.cnn.com/2023/04/12/tech/fbi-public-charging-port-warning/index.html
- https://social-innovation.hitachi/en-in/knowledge-hub/hitachi-voice/digital-transformation/
- https://www.inmarsat.com/en/insights/aviation/2022/future-aviation-connectivity.html
Introduction
We live in a time where technological change is no longer slow or subtle. Robotics, automation, artificial intelligence, and digital systems are transforming the way we work, think, and even imagine the future. This is often celebrated as great progress. But a deeper question quietly waits behind the noise. Is every advancement truly an uplift when seen through the lens of scriptures, culture, and Indian philosophical thought? Are we creating for the good of humanity, or are we only chasing convenience and speed? And what kind of future are we actually preparing, not just for ourselves, but for those who will be born into this world shaped by these tools from the very beginning?
India has long been seen as a land that values balance, purity, and harmony with nature. Its rivers, mountains, forests, and traditions are not just geography or history, they are part of a civilizational way of thinking that connects life, duty, and responsibility. In this context, it becomes important to ask what the long-term cost of our technological appetite might be. Every invention has a footprint. Industries change landscapes. Energy demands reshape ecosystems. Convenience today often hides consequences that only appear years later. Progress, when measured only in speed and output, forgets to ask what it takes away in silence.
There is also a quieter change happening inside the human mind. As tools become smarter, humans begin to feel more powerful. The thought slowly shifts from “I can use this” to “I control this.” With artificial intelligence, the language becomes even bolder. We start hearing phrases like “we can create worlds, faces, voices, even minds.” But history have always warned us about ‘overreach’. Not because power is evil, but because pride blinds judgment. When ability grows faster than wisdom, imbalance follows. We can already see early signs of this in concerns about shrinking attention spans, weakening cognitive habits, and a growing dependence on systems that think for us before we learn to think for ourselves deeply.
None of this is an argument to reject innovation. The idea is not to blacklist technology or romanticise the past. The real question is about direction and responsibility. Advancements are not only for the comfort of the present generation. They shape the mental, moral, and emotional world of future generations who will grow up surrounded by these systems as something normal and unavoidable. What values will guide that world? What habits will it encourage? What will it quietly take away?
This is where the richness of Indian thought becomes relevant, not as nostalgia, but as guidance. Ideas of dharma, restraint, balance, and ethical action were never anti-progress. They were reminders that power without responsibility becomes dangerous, and that ability without humility leads to decline. In modern terms, we talk about safety by design, ethical innovation, and human-centred technology. In older language, we talked about duty, limits, and the consequences of unchecked desire. The words have changed, but the concern is the same.
Perhaps the real question is not whether we are becoming creators, but whether we remember that we are also caretakers. We do not bring existence out of nothing. We reshape what already exists. And in that reshaping, the line between wisdom and arrogance, between progress and pride, becomes the most important line of all.
The futuristic impact of AI, robotics, and technologies
In every yuga, humans have extended the limits of what they can do. What changes is not the desire, but the form it takes. Our ancient history speak of extraordinary abilities, not as fantasies, but as reminders of how power tests character. Figures like Naradmuni (a prominent divine sage (Rishiraja) in Hinduism) are described as moving from one place to another in moments. Others gained immense strength, knowledge, or influence through years of discipline and tapasya. Ravana (Figure from Ramayana) himself was learned and powerful, far beyond ordinary human measure. Sanjaya (the charioteer and advisor of King Dhritarashtra in the Mahabharata) receives the gift of divya drishti and narrates the events of the battlefield without being physically present there, seeing and speaking across distance in a way that still feels remarkable even today.
In this yuga, that ancient search for power and reach has not disappeared, it has only changed its language, and today it speaks through robotics, artificial intelligence, and advanced technologies, making us ask whether we are truly creators or only very advanced arrangers of what already exists.
In this age, science and technology are attempting something similar in a different language. We may not travel like Naradmuni, but we send our voices, images, and thoughts across the world in seconds. We build machines that can see, listen, respond, and even imitate human thinking. Artificial intelligence and robotics promise comfort, speed, and efficiency, and in many ways, they truly improve human life. Yet the old question remains. Not just what can we do, but how far should we go, and at what cost.
When we primarily build for human convenience, we often fail to thoroughly examine the long-term consequences. The environmental impact of large-scale technology is already visible in the pressure on resources, the growth of waste, and the slow damage to air, water, and soil. Nature does not recover at the pace of human ambition. What feels like small compromises today can become heavy burdens for tomorrow.
There is also the impact on the human mind. As systems become more capable, humans risk becoming more dependent. When answers arrive instantly, patience weakens. When machines start deciding for us, the habit of deep thinking slowly fades. Over time, this can affect attention, memory, and judgment. Knowledge becomes easier to reach, but wisdom becomes harder to build. Just as in old stories, the danger is not in having power, but in losing clarity while using it.
Future generations will not encounter these technologies as new inventions. They will be born into them. What we treat today as tools, they will experience as the normal environment of life. This makes responsibility unavoidable. The real question is not only whether these systems work, but what kind of humans they will shape.
The purpose of this reflection is not to reject progress. It is to ask for balance. Building for human comfort is important, but building without studying long-term impact is risky. If this age has the power to create intelligent systems, it must also have the wisdom to protect the environment, care for future generations, and preserve the depth of the human mind. Otherwise, advancement becomes speed without direction, and power without responsibility.
The Acceleration of the Technological Age
The current era has reached a state where technological progress now occurs through instantaneous changes which transform our methods of working and decision-making and future planning. People often view robotics and automation and artificial intelligence as signs of progress yet a less audible inquiry persists through time which asks whether every technological advancement enhances human existence or whether we merely pursue efficient and easy solutions without thinking about their implications. Indian philosophical thought offers a useful lens here, one that does not reject progress but asks whether it aligns with balance, responsibility, and long-term harmony. The definition of intelligence according to this perspective extends beyond computational skills and pattern imitation because it requires people to achieve awareness and intent and their complete understanding. Current machines possess the ability to mimic human reasoning and produce language while they can replicate decision-making processes, but they lack both consciousness and personal experience.
Power, Responsibility, and Ethical Imbalance
The development of new technological capabilities brings with it ethical responsibilities which every society must handle. Human beings must take on new ethical duties which match their increasing capabilities according to historical evidence. The current situation shows that people create new things at a speed which exceeds their ability to think about those innovations. Systems exist to enhance operational performance while they determine human actions and extend their power but they do not always evaluate their complete impact. Indian traditions emphasize dharma, the principle of balance and rightful action, which shows that power without ethical grounding creates destructive human force. The state of imbalance exists without showing its presence at all times. The process of imbalance development takes place through three channels: environmental degradation, social inequalities, and the gradual decline of human control.
The current society demonstrates this transformation through its existing results. The algorithms now determine our consumption choices and our methods of understanding everything around us. The system provides users with personalized comfort, but it also creates hidden patterns that determine their preferences. The process starts with decision assistance before it progresses to decision influence which eventually leads to decision conditioning. The concept of swatantrata as inner freedom becomes more complicated within such an environment. People stop making freedom choices when they find it easier to select between things that exist in their surroundings because they lose their ability to choose. People start to measure their work activities and personal identity through systems that use optimization techniques and digital validation systems, which leads to a decrease of space that exists for individuals to think and consider matters independently.
Technology, Ecology, and Civilizational Values
The environmental impact of technological demand exists together with social transformations. All systems need power while all infrastructure creates environmental effects and all products, we use contain unknown expenses which become apparent after many years. India's civilizational values maintain their dedication to nature because people see rivers and forests and ecosystems as essential parts of existence. Success in modern society measures output as the main achievement while actual value disappears through the evaluation process. The future requires us to create new things but we must also decide which things to keep intact.
The current situation requires progress to be defined differently because it needs to be measured through precise management instead of continuous rapid development. The question now extends beyond technological advancement to include the need for technologies to be operated through intelligent guidance. The increasing abilities of machines create a greater need for people to maintain their essential human characteristics. Human beings must actively maintain their capacity to make ethical decisions and understand their life's meaning and purpose. The future depends on two factors: the “innovations that will emerge and the values that will guide their development.”
Conclusion
It is high time we pause and honestly examine the path we are taking. The question is not whether technology should grow, but whether its overreach should be allowed to shape the future without restraint. We are building faster than ever, developing systems that touch every part of life. That makes it even more important to study their long-term impact, not only on markets or productivity, but on nature, on the human mind, and on the generations who will inherit this tech-driven world.
Progress should benefit those who come after us, not quietly weaken them. A future where people are born into pure convenience, surrounded by tools that think, decide, and act for them, may look comfortable, but comfort alone does not build strong, aware, or responsible human beings. Growth without effort and ease without discipline slowly takes away depth, resilience, and clarity. Technology should support human potential, not replace it.
This is why morality, ethics, and balance cannot be treated as optional ideas. They must guide innovation, not follow it. We do not need to overcreate. We need to create ‘wisely’. We need to build systems that remain under human control, not systems that slowly train humans to surrender their judgment, attention, and responsibility. Tools should remain tools. They should serve life, not define it.
Indian thought has always placed intention at the centre of action. Karma is not judged only by outcome, but by the spirit in which an act is performed. A tool in itself is neither pure nor impure. It becomes one or the other through the hand that uses it. This is a lens through which modern technology can also be examined. Artificial intelligence can help doctors read scans faster, help farmers predict weather patterns, and help students in remote areas access knowledge. At the same time, it can be used to watch, to sort, to exclude, and to reduce human beings to data points that fit neatly into a system. The difference lies not in the machine, but in the values of those who design and deploy it.
The purpose of this reflection is simple. We should build, but we should build with responsibility. We should innovate, but with awareness of consequences. True progress is not just about what is possible today. It is about what remains healthy, meaningful, and sustainable tomorrow. If this age can combine intelligence with humility, and power with restraint, then technology will not become a symbol of overreach. It will become a sign of maturity.


