#FactCheck - Stunning 'Mount Kailash' Video Exposed as AI-Generated Illusion!
EXECUTIVE SUMMARY:
A viral video is surfacing claiming to capture an aerial view of Mount Kailash that has breathtaking scenery apparently providing a rare real-life shot of Tibet's sacred mountain. Its authenticity was investigated, and authenticity versus digitally manipulative features were analyzed.
CLAIMS:
The viral video claims to reveal the real aerial shot of Mount Kailash, as if exposing us to the natural beauty of such a hallowed mountain. The video was circulated widely in social media, with users crediting it to be the actual footage of Mount Kailash.


FACTS:
The viral video that was circulated through social media was not real footage of Mount Kailash. The reverse image search revealed that it is an AI-generated video created by Sonam and Namgyal, two Tibet based graphic artists on Midjourney. The advanced digital techniques used helped to provide a realistic lifelike scene in the video.
No media or geographical source has reported or published the video as authentic footage of Mount Kailash. Besides, several visual aspects, including lighting and environmental features, indicate that it is computer-generated.
For further verification, we used Hive Moderation, a deep fake detection tool to conclude whether the video is AI-Generated or Real. It was found to be AI generated.

CONCLUSION:
The viral video claiming to show an aerial view of Mount Kailash is an AI-manipulated creation, not authentic footage of the sacred mountain. This incident highlights the growing influence of AI and CGI in creating realistic but misleading content, emphasizing the need for viewers to verify such visuals through trusted sources before sharing.
- Claim: Digitally Morphed Video of Mt. Kailash, Showcasing Stunning White Clouds
- Claimed On: X (Formerly Known As Twitter), Instagram
- Fact Check: AI-Generated (Checked using Hive Moderation).
Related Blogs
.webp)
Executive Summary
A video showing a monkey allegedly saving the life of a sleeping child is rapidly going viral on social media. In the clip, a monkey can be seen picking up a child sleeping on a mat under a tree and moving the child away moments before a heavy tree branch falls at the same spot. Social media users are sharing the video as a “miracle of nature” and praising the emotional sensitivity and instincts of animals. However, research conducted by CyberPeace Research Wing found that the viral video is not real and was created using artificial intelligence tools.
Claim
The caption accompanying the viral post states:“In a shocking incident, a monkey was seen stepping in to save an innocent child sleeping under a tree from imminent danger. People nearby were stunned by the scene. It is being claimed that the monkey sensed the danger around the child and tried to protect him. The unusual incident has now gone viral on social media, with many saying that emotions and compassion are not limited to humans, animals can also understand feelings.”
The video has been widely shared across social media platforms
- https://www.instagram.com/reels/DYMvhRPTcCA/
- https://archive.ph/https://www.instagram.com/reels/DYMvhRPTcCA/

Fact Check
To verify the authenticity of the video, we extracted keyframes from the clip and conducted a reverse image search. During the research, we found the same video uploaded on May 8, 2026, on an Instagram page named Instagram user “mojilo_vandro.” The caption of the original upload did not provide any factual context and presented the video in a dramatic, miracle-like manner.

We further examined the Instagram account and found that it regularly posts several AI-generated videos featuring monkeys performing heroic or emotional acts. Importantly, the account owner has also identified themselves as an “AI video creator” in the bio section.
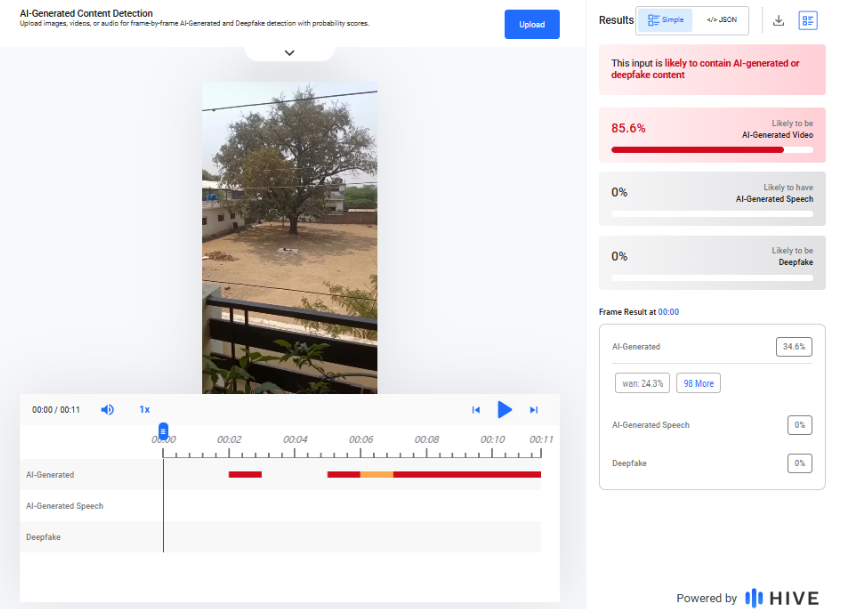
To further analyze the clip, we tested it using the AI detection tool Hive Moderation. The tool’s analysis classified the viral video as 85.6% likely to be AI-generated. We also checked the clip using another AI detection platform, Deepfake-o-meter. Its AVSRDD (2025) detection model flagged the video as potentially AI-generated with a 100% confidence score.

Conclusion
The evidence gathered during our research clearly shows that the viral video claiming to show a monkey saving a sleeping child from a falling tree branch is not authentic. The clip was created using AI-generated visual techniques and does not depict a real incident.

Introduction
The Data Protection Data Privacy Act 2023 is the most essential step towards protecting, prioritising, and promoting the users’ privacy and data protection. The Act is designed to prioritize user consent in data processing while assuring uninterrupted services like online shopping, intermediaries, etc. The Act specifies that once a user provides consent to the following intermediary platforms, the platforms can process the data until the user withdraws the rights of it. This policy assures that the user has the entire control over their data and is accountable for its usage.
A keen Outlook
The Following Act also provides highlights for user-specific purpose, which is limited to data processing. This step prevents the misuse of data and also ensures that the processed data is being for the purpose for which it was obtained at the initial stage from the user.
- Data Fudiary and Processing of Online Shopping Platforms: The Act Emphasises More on Users’ Consent. Once provided, the Data Fudiary can constantly process the data until it is specifically withdrawn by the Data Principal.
- Detailed Analysis
- Consent as a Foundation: The Act places the user's consent as a backbone to the data processing. It sets clear boundaries for data processing. It can be Collecting, Processing, and Storing, and must comply with users’ consent before being used.
- Uninterrupted Data processing: With the given user consent, the intermediaries are not time-restrained. As long as the user does not obligate their consent, the process will be ongoing.
- Consent and Order Fulfillment: Consent, once provided, encloses all the activities related to the specific purpose for which it was meant to the data it was given for subsequent actions such as order fulfilment.
- Detailed Analysis
- Purpose-Limited Consent: The consent given is purpose-limited. The platform cannot misuse the obtained data for its personal use.
- Seamless User Experience: By ensuring that the user consent covers the full transactions, spared from the unwanted annoyance of repeated consent requests from the actual ongoing activities.
- Data Retention and Rub Out on Online Platforms: Platforms must ensure data minimisation post its utilisation period. This extends to any kind of third-party processors they might take on.
- Detailed Analysis
- Minimization and Security Assurance: By compulsory data removal on post ultization,This step helps to reduce the volume of data platforms hold, which leads to minimizing the risk to data.
- Third-Party Accountability, User Privacy Protection.
Influence from Global frameworks
The impactful changes based on global trends and similar legislation( European Union’s GDPR) here are some fruitful changes in intermediaries and social media platforms experienced after the implementation of the DPDP Act 2023.
- Solidified Consent Mechanism: Platforms and intermediatries need to ensure the users’ consent is categorically given, and informed, and should be specific to which the data is obtained. This step may lead to user-friendly consent forms activities and prompts.
- Data Minimizations: Platforms that tend to need to collect the only data necessary for the specific purpose mentioned and not retain information beyond its utility.
- Transparency and Accountability: Data collecting Platforms need to ensure transparency in data collecting, data processing, and sharing practices. This involves more detailed policy and regular audits.
- Data Portability: Users have the right to request for a copy of their own data used in format, allowing them to switch platforms effectively.
- Right to Obligation: Users can have the request right to deletion of their data, also referred to as the “Right to be forgotten”.
- Prescribed Reporting: Under circumstances of data breaches, intermediary platforms are required to report the issues and instability to the regulatory authorities within a specific timeline.
- Data Protection Authorities: Due to the increase in data breaches, Large platforms indeed appoint data protection officers, which are responsible for the right compliance with data protection guidelines.
- Disciplined Policies: Non-compliance might lead to a huge amount of fines, making it indispensable to invest in data protection measures.
- Third-Party Audits: Intermediaries have to undergo security audits by external auditors to ensure they are meeting the expeditions of the following compliances.
- Third-Party Information Sharing Restrictions: Sharing personal information and users’ data with third parties (such as advertisers) come with more detailed and disciplined guideline and user consent.
Conclusion
The Data Protection Data Privacy Act 2023 prioritises user consent, ensuring uninterrupted services and purpose-limited data processing. It aims to prevent data misuse, emphasising seamless user experiences and data minimisation. Drawing inspiration from global frameworks like the EU's GDPR, it introduces solidified consent mechanisms, transparency, and accountability. Users gain rights such as data portability and data deletion requests. Non-compliance results in significant fines. This legislation sets a new standard for user privacy and data protection, empowering users and holding platforms accountable. In an evolving digital landscape, it plays a crucial role in ensuring data security and responsible data handling.
References:
- https://www.meity.gov.in/writereaddata/files/Digital%20Personal%20Data%20Protection%20Act%202023.pdf
- https://www.mondaq.com/india/privacy-protection/1355068/data-protection-law-in-india-analysis-of-dpdp-act-2023-for-businesses--part-i
- https://www.hindustantimes.com/technology/explained-indias-new-digital-personal-data-protection-framework-101691912775654.html
%20(1).webp)
Introduction
Bumble’s launch of its ‘Opening Move’ feature has sparked a new narrative on safety and privacy within the digital dating sphere and has garnered mixed reactions from users. It was launched against the backdrop of women stating that the ‘message first’ policy of Bumble was proving to be tedious. Addressing the large-scale review, Bumble launched its ‘Opening Move’ feature, whereby users can either craft or select from pre-set questions which potential matches may choose to answer to start the conversation at first glance. These questions are a segue into meaningful and insightful conversation from the get-go and overstep the traditional effort to start engaging chats between matched users. This feature is an optional feature that users may enable and as such does not prevent a user from exercising the autonomy previously in place.
Innovative Approach to Conversation Starters
Many users consider this feature as innovative; not only does it act as a catalyst for fluid conversation but also cultivates insightful dialogue, fostering meaningful interactions that are devoid of the constraint of superficial small talk. The ‘Opening Moves’ feature may also be aligned with unique scientific research indicating that individuals form their initial attractions within 3-seconds of intimate interaction, thereby proving to be a catalyst to the decision-making process of an individual in the attraction time frame.
Organizational Benefits and Data Insights
From an organisational standpoint, the feature is a unique solution towards localisation challenges faced by apps; the option of writing a personalised ‘Opening Move’ implies setting prompts that are culturally relevant and appropriate in a specific area. Moreover, it is anticipated that Bumble may enhance and improve user experience within the platform through data analysis. Data from responses to an ‘Opening Move’ may provide valuable insights into user preferences and patterns by analysing which pre-set prompts garner more responses over others and how often is a user-written ‘Opening Move’ successful in obtaining a response in comparison with Bumble’s pre-set prompts. A quick glance at Bumble’s privacy policy[1] shows that data storing and transferring of chats between users are not shared with third parties, further safeguarding personal privacy. However, Bumble does use the chat data for its own internal purposes after removing personally identifiable information from chats. The manner of such review and removal of data has not been specified, which may raise challenges depending upon whether the reviewer is a human or an algorithm.
However, some users perceive the feature as counterproductive to the company’s principle of ‘women make the first move’. While Bumble aims to market the feature as a neutral ground for matched users based on the exercise of choice, users see it as a step back into the heteronormative gender expectations that most dating apps conform to, putting the onus of the ‘first move’ on men. Many male users have complained that the feature acts as a catalyst for men to opt out of the dating app and would most likely refrain from interacting with profiles enabled with the ‘Opening Move’ feature, since the pressure to answer in a creative manner is disproportionate with the likelihood their response actually being entertained.[2] Coupled with the female users terming the original protocol as ‘too much effort’, the preset questions of the ‘Opening Move’ feature may actively invite users to categorise potential matches according to arbitrary questions that undermine real-life experiences, perspectives and backgrounds of each individual.[3]
Additionally, complications are likely to arise when a notorious user sets a question that indirectly gleans personal or sensitive, identifiable information. The individual responding may be bullied or be subjected to hateful slurs when they respond to such carefully crafted conversation prompts.
Safety and Privacy Concerns
On the corollary, the appearance of choice may translate into more challenges for women on the platform. The feature may spark an increase in the number of unsolicited, undesirable messages and images from a potential match. The most vulnerable groups at present remain individuals who identify as females and other sexual minorities.[4] At present, there appears to be no mechanism in place to proactively monitor the content of responses, relying instead on user reporting. This approach may prove to be impractical given the potential volume of objectionable messages, necessitating a more efficient solution to address this issue. It is to be noted that in spite of a user reporting, the current redressal systems of online platforms remain lax, largely inadequate and demonstrate ineffectiveness in addressing user concerns or grievances. This lack of proactiveness is violative of the right to redressal provided under the Digital Personal Data Protection Act, 2023. It is thought that the feature may actually take away user autonomy that Bumble originally aimed to grant since Individuals who identify as introverted, shy, soft-spoken, or non-assertive may refrain from reporting harassing messages altogether, potentially due to discomfort or reluctance to engage in confrontation. Resultantly, it is anticipated that there would be a sharp uptake in cases pertaining to cyberbullying, harassment and hate speech (especially vulgar communications) towards both the user and the potential match.
From an Indian legal perspective, dating apps have to adhere to the Information Technology Act, 2000 [5], the Information Technology (Intermediary and Digital Media Ethics) Rules 2021 [6] and the Digital Personal Data Protection Act, 2023, that regulates a person’s digital privacy and set standards on the kind of content an intermediary may host. An obligation is cast upon an intermediary to uprise its users on what content is not allowed on its platform in addition to mandating intimation of the user’s digital rights. The lack of automated checks, as mentioned above, is likely to make Bumble non-compliant with the ethical guidelines.
The optional nature of the ‘Opening Move’ grants users some autonomy. However, some technical updates may enhance the user experience of this feature. Technologies like AI are an effective aid in behavioural and predictive analysis. An upgraded ‘matching’ algorithm can analyse the number of un-matches a profile receives, thereby identifying and flagging a profile having multiple lapsed matches. Additionally, the design interface of the application bearing a filter option to filter out flagged profiles would enable a user to be cautious while navigating through the matches. Another possible method of weeding out notorious profiles is by deploying a peer-review system of profiles whereby a user has a singular check-box that enables them to flag a profile. Such a checkbox would ideally be devoid of any option for writing personal comments and would bear a check box stating whether the profile is most or least likely to bully/harass. This would ensure that a binary, precise response is recorded and any coloured remarks are avoided. [7]
Governance and Monitoring Mechanisms
From a governance point of view, a monitoring mechanism on the manner of crafting questions is critical. Systems should be designed to detect certain words/sentences and a specific manner of framing sentences to disallow questions contrary to the national legal framework. An onscreen notification having instructions on generally acceptable manner of conversations as a reminder to users to maintain cyber hygiene while conversing is also proposed as a mandated requirement for platforms. The notification/notice may also include guidelines on what information is safe to share in order to safeguard user privacy. Lastly, a revised privacy policy should establish the legal basis for processing responses to ‘Opening Moves’, thereby bringing it in compliance with national legislations such as the Digital Personal Data Protection Act, 2023.
Conclusion
Bumble's 'Opening Move' feature marks the company’s ‘statement’ step to address user concerns regarding initiating conversations on the platform. While it has been praised for fostering more meaningful interactions, it also raises not only ethical concerns but also concerns over user safety. While the 'Opening Move' feature can potentially enhance user experience, its success is largely dependent on Bumble's ability to effectively navigate the complex issues associated with this feature. A more robust monitoring mechanism that utilises newer technology is critical to address user concerns and to ensure compliance with national laws on data privacy.
Endnotes:
- [1] Bumble’s privacy policy https://bumble.com/en-us/privacy
- [2] Discussion thread, r/bumble, Reddit https://www.reddit.com/r/Bumble/comments/1cgrs0d/women_on_bumble_no_longer_have_to_make_the_first/?share_id=idm6DK7e0lgkD7ZQ2TiTq&utm_content=2&utm_medium=ios_app&utm_name=ioscss&utm_source=share&utm_term=1&rdt=65068
- [3] Mcrea-Hedley, Olivia, “Love on the Apps: When did Dating Become so Political?”, 8 February 2024 https://www.service95.com/the-politics-of-dating-apps/
- [4] Gewirtz-Meydan, A., Volman-Pampanel, D., Opuda, E., & Tarshish, N. (2024). ‘Dating Apps: A New Emerging Platform for Sexual Harassment? A Scoping Review. Trauma, Violence, & Abuse, 25(1), 752-763. https://doi.org/10.1177/15248380231162969
- [5] Information Technology Act, 2000 https://www.indiacode.nic.in/bitstream/123456789/13116/1/it_act_2000_updated.pdf
- [6] Information Technology (Intermediary Guidelines and Digital Media Ethics) Rules 2021 https://www.meity.gov.in/writereaddata/files/Information%20Technology%20%28Intermediary%20Guidelines%20and%20Digital%20Media%20Ethics%20Code%29%20Rules%2C%202021%20%28updated%2006.04.2023%29-.pdf
- [7] Date Confidently: Engaging Features in a Dating App (Use Cases), Consaguous, 10 July 2023 https://www.consagous.co/blog/date-confidently-engaging-features-in-a-dating-app-use-cases


